 Technology peripherals
Technology peripherals It Industry
It Industry Cyberspace Administration of China: Accounts such as 'Wang Wukong Talking Cars' were shut down for publishing false and untrue information
Cyberspace Administration of China: Accounts such as 'Wang Wukong Talking Cars' were shut down for publishing false and untrue informationCyberspace Administration of China: Accounts such as 'Wang Wukong Talking Cars' were shut down for publishing false and untrue information

1. Publishing false and untrue information to slander corporate image and reputation
- Douyin account "Wang Wukong Talks about Cars" "
- Xigua Video Account "Wang Wukong"
- Little Red Book Account "It's Me, Wang Wukong"
2. In the name of publishing negative information, blackmailing companies to carry out business cooperation
- NetEase Account "Lil" Moss”
- Douyin account “Lil Moss・Business Detective”
- WeChat public account “Electric Vehicle Hotspot”
3. Publish “clickbait” articles to maliciously smear the company
- WeChat public
- WeChat video account "Jin Merchants Zongheng"
4. Publish false information and interfere with the normal operation of enterprises
- Douyin account "International Energy Network"
- Kuaishou account "International Energy "Net"
- Zhihu account "International Energy Network"
- Xiaohongshu account "International Energy Network"
5. Publish rumors and information to smear and slander the image of companies and entrepreneurs
- Xiaohongshu account "Run" Talk about Runyu”
- Weibo account “Shen Yixin”
- Oriental Fortune Network account “CelineFeng 风你偌”
The above is the detailed content of Cyberspace Administration of China: Accounts such as 'Wang Wukong Talking Cars' were shut down for publishing false and untrue information. For more information, please follow other related articles on the PHP Chinese website!
 Serverless Image Processing Pipeline with AWS ECS and LambdaApr 18, 2025 am 08:28 AM
Serverless Image Processing Pipeline with AWS ECS and LambdaApr 18, 2025 am 08:28 AMThis tutorial guides you through building a serverless image processing pipeline using AWS services. We'll create a Next.js frontend deployed on an ECS Fargate cluster, interacting with an API Gateway, Lambda functions, S3 buckets, and DynamoDB. Th
 CNCF Arm64 Pilot: Impact and InsightsApr 15, 2025 am 08:27 AM
CNCF Arm64 Pilot: Impact and InsightsApr 15, 2025 am 08:27 AMThis pilot program, a collaboration between the CNCF (Cloud Native Computing Foundation), Ampere Computing, Equinix Metal, and Actuated, streamlines arm64 CI/CD for CNCF GitHub projects. The initiative addresses security concerns and performance lim
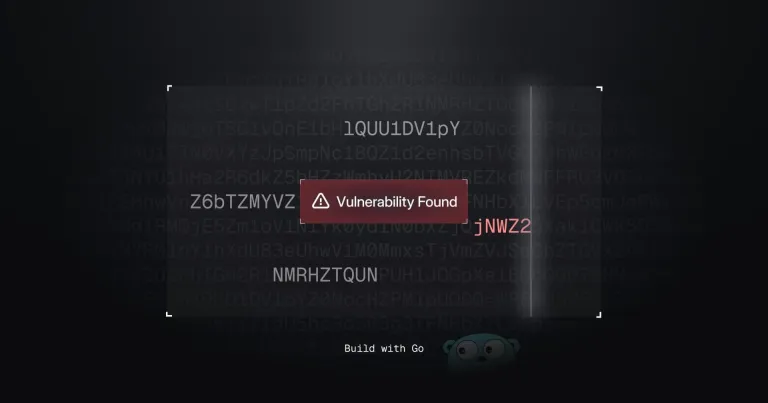 Building a Network Vulnerability Scanner with GoApr 01, 2025 am 08:27 AM
Building a Network Vulnerability Scanner with GoApr 01, 2025 am 08:27 AMThis Go-based network vulnerability scanner efficiently identifies potential security weaknesses. It leverages Go's concurrency features for speed and includes service detection and vulnerability matching. Let's explore its capabilities and ethical


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

SublimeText3 Linux new version
SublimeText3 Linux latest version

Atom editor mac version download
The most popular open source editor

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

SublimeText3 Chinese version
Chinese version, very easy to use

SublimeText3 Mac version
God-level code editing software (SublimeText3)




