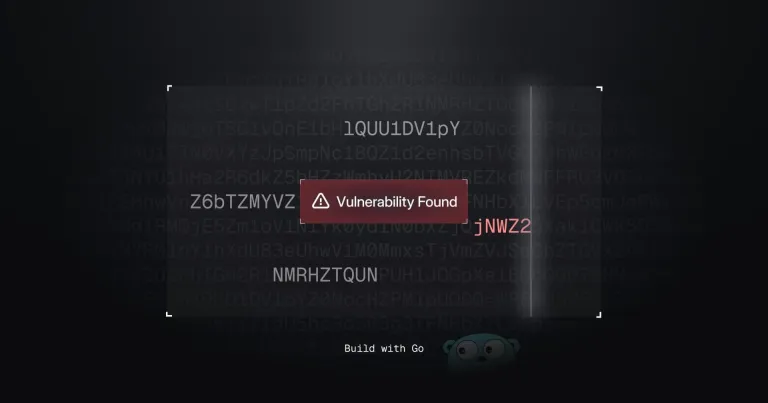
This Go-based network vulnerability scanner efficiently identifies potential security weaknesses. It leverages Go's concurrency features for speed and includes service detection and vulnerability matching. Let's explore its capabilities and ethical considerations.

Core Functionality:
The scanner functions as a command-line tool, designed to:
- Scan a network of hosts: It targets specified IP addresses or ranges, identifying open ports and running services.
- Detect open ports: It uses a multi-threaded approach to quickly check for open ports on a target host, overcoming the slowness of sequential scanning.
- Identify running services (banner grabbing): By analyzing the banner information received from open ports, the scanner identifies the services running (e.g., HTTP, SSH, MySQL) and their versions. This is crucial for vulnerability assessment.
- Match against known vulnerabilities: The scanner compares identified services and versions against a built-in database of known vulnerabilities (CVEs). This database could be expanded or replaced with an external database for a more comprehensive scan.
- Report findings: Results are presented in a clear, concise format, selectable as text, JSON, or CSV, allowing for easy analysis and integration with other security tools. A verbose option provides additional detail, including raw banner information.
Ethical Considerations and Responsible Use:
Before using this or any network scanning tool, it's crucial to understand and adhere to ethical and legal guidelines:
- Obtain explicit permission: Unauthorized network scanning is illegal in many jurisdictions. Always ensure you have permission from the owner of the network you're scanning.
- Define a clear scope: Limit your scan to the specifically authorized range of IP addresses and ports.
- Avoid aggressive scanning: Excessive scanning can disrupt services or trigger security alerts. The scanner includes rate-limiting mechanisms, but responsible usage is paramount.
- Report vulnerabilities responsibly: If you discover vulnerabilities, report them to the appropriate system owners in a constructive manner, allowing them to address the issues.
- Comply with all applicable laws and regulations: Understand and follow the legal framework governing network scanning in your location.
Enhancements and Future Development:
While this scanner provides a solid foundation, several enhancements could improve its capabilities:
- Expanded vulnerability database: Integrate with a regularly updated, external vulnerability database (like NVD) for more comprehensive vulnerability detection.
- Advanced vulnerability detection: Implement more sophisticated techniques for identifying vulnerabilities beyond simple version matching, including analyzing service configurations and checking for known exploits.
- Support for other protocols: Expand beyond TCP to include UDP and other network protocols.
- Improved service identification: Use more robust techniques for service fingerprinting, improving accuracy and handling of less common services.
- Network mapping: Incorporate network mapping capabilities to visualize the target network's topology.
- Reporting and visualization: Enhance reporting features with more advanced visualizations and summaries of findings.
This scanner offers a practical starting point for learning about network vulnerability scanning and the capabilities of the Go programming language. Remember that responsible and ethical use is paramount.
The above is the detailed content of Building a Network Vulnerability Scanner with Go. For more information, please follow other related articles on the PHP Chinese website!
 Top 21 Developer Newsletters to Subscribe To in 2025Apr 24, 2025 am 08:28 AM
Top 21 Developer Newsletters to Subscribe To in 2025Apr 24, 2025 am 08:28 AMStay informed about the latest tech trends with these top developer newsletters! This curated list offers something for everyone, from AI enthusiasts to seasoned backend and frontend developers. Choose your favorites and save time searching for rel
 Serverless Image Processing Pipeline with AWS ECS and LambdaApr 18, 2025 am 08:28 AM
Serverless Image Processing Pipeline with AWS ECS and LambdaApr 18, 2025 am 08:28 AMThis tutorial guides you through building a serverless image processing pipeline using AWS services. We'll create a Next.js frontend deployed on an ECS Fargate cluster, interacting with an API Gateway, Lambda functions, S3 buckets, and DynamoDB. Th
 CNCF Arm64 Pilot: Impact and InsightsApr 15, 2025 am 08:27 AM
CNCF Arm64 Pilot: Impact and InsightsApr 15, 2025 am 08:27 AMThis pilot program, a collaboration between the CNCF (Cloud Native Computing Foundation), Ampere Computing, Equinix Metal, and Actuated, streamlines arm64 CI/CD for CNCF GitHub projects. The initiative addresses security concerns and performance lim
 Building a Network Vulnerability Scanner with GoApr 01, 2025 am 08:27 AM
Building a Network Vulnerability Scanner with GoApr 01, 2025 am 08:27 AMThis Go-based network vulnerability scanner efficiently identifies potential security weaknesses. It leverages Go's concurrency features for speed and includes service detection and vulnerability matching. Let's explore its capabilities and ethical


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

Dreamweaver CS6
Visual web development tools

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

Atom editor mac version download
The most popular open source editor

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.






