
ARP defense under Linux
There are 2 ways of ARP attack
The first is to mislead your serverlinux anti-arp attack, telling you that the MAC of the network segment is another.
The second is to mislead the network segment linux video, telling the network segment that the MAC of your server is another one.
For the first type, you can use the arp-s network segment IP network segment MAC command to set up static arp record defense
For the second method, you can use the following method
Linux security hardening, since it is source code compilation, I won’t talk about it later. Go check out the specific software packages required for ubuntu source code installation
tarzxvf-
cd-/
sudo./configure

sudomake
If you are prompted that the command is insufficient, you can use apt-getinstallmake to install it
sudomakeinstall
During the compilation processLinux anti-arp attack, some warnings will be prompted, it doesn't matter. In short, after installation, just have /usr/lib/.a
Install arpoison afterwards
tarxvfarpoison-
cdarpoison/
sudogcc/usr/lib/.a-oarpoison

There may be a prompt that the file does not exist, which can be solved by replacing /usr/lib with /usr/local/lib
sudomvarpoison/usr/sbin
sudogcc/usr/lib/.a-oarpoison
sudomvarpoison/usr/sbin
After the installation is complete, you can use the following command
sudoarpoisonUsage:-i-d-s-t-r[-a][-wtimebetweenpackets][-nnumbertosend]
Parameter description
-i specifies the network card socket eth0 that sends arp packets
-d
-s
The above is the detailed content of Two forms of ARP attacks and defense methods, detailed analysis. For more information, please follow other related articles on the PHP Chinese website!
 Mastering Text Manipulation With the Sed CommandMar 16, 2025 am 09:48 AM
Mastering Text Manipulation With the Sed CommandMar 16, 2025 am 09:48 AMThe Linux command line interface provides a wealth of text processing tools, one of the most powerful tools is the sed command. sed is the abbreviation of Stream EDitor, a multi-functional tool that allows complex processing of text files and streams. What is Sed? sed is a non-interactive text editor that operates on pipeline inputs or text files. By providing directives, you can let it modify and process text in a file or stream. The most common use cases of sed include selecting text, replacing text, modifying original files, adding lines to text, or removing lines from text. It can be used from the command line in Bash and other command line shells. Sed command syntax sed
 How To Count Files And Directories In Linux: A Beginner's GuideMar 19, 2025 am 10:48 AM
How To Count Files And Directories In Linux: A Beginner's GuideMar 19, 2025 am 10:48 AMEfficiently Counting Files and Folders in Linux: A Comprehensive Guide Knowing how to quickly count files and directories in Linux is crucial for system administrators and anyone managing large datasets. This guide demonstrates using simple command-l
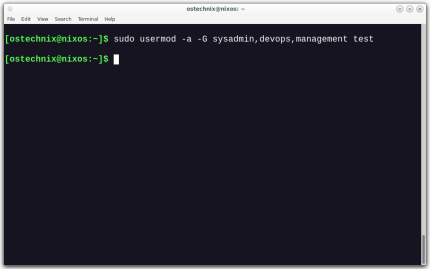 How To Add A User To Multiple Groups In LinuxMar 18, 2025 am 11:44 AM
How To Add A User To Multiple Groups In LinuxMar 18, 2025 am 11:44 AMEfficiently managing user accounts and group memberships is crucial for Linux/Unix system administration. This ensures proper resource and data access control. This tutorial details how to add a user to multiple groups in Linux and Unix systems. We
 The Secret Weapon to Supercharge Your Linux System With Liquorix KernelMar 08, 2025 pm 12:12 PM
The Secret Weapon to Supercharge Your Linux System With Liquorix KernelMar 08, 2025 pm 12:12 PMLiquorix kernel: a powerful tool to improve Linux system performance Linux is known for its flexibility, security and high performance, becoming the operating system of choice for developers, system administrators, and advanced users. However, the universal Linux kernel is not always meeting the needs of users seeking maximum performance and responsiveness. This is where the Liquorix kernel comes into play—a performance-optimized alternative that promises to enhance your Linux system. This article will explore what the Liquorix kernel is, why you might want to use it, and how to install and configure it to get the most out of your system. Liquorix kernel detailed explanation Liquorix kernel is a precompiled Linux kernel designed for
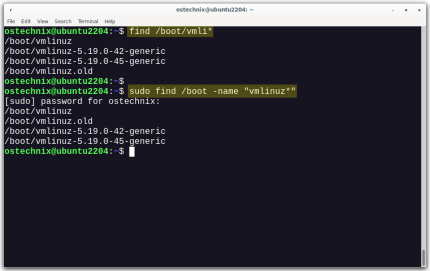 How To List Or Check All Installed Linux Kernels From CommandlineMar 23, 2025 am 10:43 AM
How To List Or Check All Installed Linux Kernels From CommandlineMar 23, 2025 am 10:43 AMLinux Kernel is the core component of a GNU/Linux operating system. Developed by Linus Torvalds in 1991, it is a free, open-source, monolithic, modular, and multitasking Unix-like kernel. In Linux, it is possible to install multiple kernels on a sing
 How To Type Indian Rupee Symbol In Ubuntu LinuxMar 22, 2025 am 10:39 AM
How To Type Indian Rupee Symbol In Ubuntu LinuxMar 22, 2025 am 10:39 AMThis brief guide explains how to type Indian Rupee symbol in Linux operating systems. The other day, I wanted to type "Indian Rupee Symbol (₹)" in a word document. My keyboard has a rupee symbol on it, but I don't know how to type it. After
 Locating Leviathan Files in LinuxMar 13, 2025 pm 12:11 PM
Locating Leviathan Files in LinuxMar 13, 2025 pm 12:11 PMIntroduction In the realm of Linux, where the command line is often the compass by which we navigate, the efficient management of disk space is crucial. Whether you’re sailing through personal projects or steering the ship o
![Install Fedora Linux 41 Workstation [Step-by-Step Guide]](https://img.php.cn/upload/article/001/242/473/174149047084567.png?x-oss-process=image/resize,p_40) Install Fedora Linux 41 Workstation [Step-by-Step Guide]Mar 09, 2025 am 11:21 AM
Install Fedora Linux 41 Workstation [Step-by-Step Guide]Mar 09, 2025 am 11:21 AMThis guide provides a comprehensive walkthrough for installing Fedora Linux 41 Workstation Edition. Let's get started! Table of Contents - Step 1: Prepare Your Fedora 41 Installation Media Step 2: Boot from the Fedora 41 Installation Media Step 3:


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.






