The default system administrator account of Linux is the root account.

The default system administrator account in Linux is root.
Root is a user account with permissions in the Linux system, also known as the super user. It has full access to all files and configurations in the system and can make any modifications and operations to the system. When installing a Linux system, a root account will be manually created and the user will be asked to set a root password.
The root account has the following characteristics:
1. Full control permissions: root has full control permissions for all files and directories in the system, and can read, write and execute any file. This makes the root account the most important and powerful account for system administrators.

2. Key system operation and maintenance work: The root account is mainly used for key system operation and maintenance work, such as: installing, upgrading software, system configuration, managing users and groups, setting file permissions, managing processes, etc.
3. Security risk: Because of the powerful permissions of the root account, it also has greater security risks. Wrong command operations or the execution of malicious programs may cause the system to crash or be invaded. Therefore, you should be careful when using the root account, use it as little as possible, but adhere to the principle of safe operation.

4.sudo command: In order to reduce the risk of directly using the root account linux creates an administrator user Hongqi Linux system, the Linux system provides the sudo command. sudo allows ordinary users to run specified commands as administratorslinux Create administrator usersLinux server configuration and management without knowing the password of the root account. Administrators can configure sudo files to authorize ordinary users to use sudo commands.
In order to improve the security of the system, the following principles should be followed:

1. Try not to use the root account: Only use the root account when performing operations that require root permissions. Normally, you should use an ordinary user account.
2. Use the sudo command: For operations that require root permissions, use the sudo command for authorization. This can reduce the impact of misuse or malicious operations on the system.
3. Set a strong password: Set a strong password for the root account to prevent it from being guessed or violently cracked.
4. Use a firewall: Configure the firewall to restrict remote access to the root account and only allow access from specific IP addresses or networks.
In short, the root account is a privileged user account in the Linux system and has full control of the system. You need to be careful when using the root account and try to follow the principles of safe operation to protect the security and stability of the system.
The above is the detailed content of The default system administrator account of Linux is the root account.. For more information, please follow other related articles on the PHP Chinese website!
 How does performance differ between Linux and Windows for various tasks?May 14, 2025 am 12:03 AM
How does performance differ between Linux and Windows for various tasks?May 14, 2025 am 12:03 AMLinux performs well in servers and development environments, while Windows performs better in desktop and gaming. 1) Linux's file system performs well when dealing with large numbers of small files. 2) Linux performs excellently in high concurrency and high throughput network scenarios. 3) Linux memory management has more advantages in server environments. 4) Linux is efficient when executing command line and script tasks, while Windows performs better on graphical interfaces and multimedia applications.
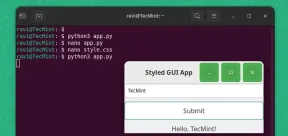 How to Create GUI Applications In Linux Using PyGObjectMay 13, 2025 am 11:09 AM
How to Create GUI Applications In Linux Using PyGObjectMay 13, 2025 am 11:09 AMCreating graphical user interface (GUI) applications is a fantastic way to bring your ideas to life and make your programs more user-friendly. PyGObject is a Python library that allows developers to create GUI applications on Linux desktops using the
 How to Install LAMP Stack with PhpMyAdmin in Arch LinuxMay 13, 2025 am 11:01 AM
How to Install LAMP Stack with PhpMyAdmin in Arch LinuxMay 13, 2025 am 11:01 AMArch Linux provides a flexible cutting-edge system environment and is a powerfully suited solution for developing web applications on small non-critical systems because is a completely open source and provides the latest up-to-date releases on kernel
 How to Install LEMP (Nginx, PHP, MariaDB) on Arch LinuxMay 13, 2025 am 10:43 AM
How to Install LEMP (Nginx, PHP, MariaDB) on Arch LinuxMay 13, 2025 am 10:43 AMDue to its Rolling Release model which embraces cutting-edge software Arch Linux was not designed and developed to run as a server to provide reliable network services because it requires extra time for maintenance, constant upgrades, and sensible fi
![12 Must-Have Linux Console [Terminal] File Managers](https://img.php.cn/upload/article/001/242/473/174710245395762.png?x-oss-process=image/resize,p_40) 12 Must-Have Linux Console [Terminal] File ManagersMay 13, 2025 am 10:14 AM
12 Must-Have Linux Console [Terminal] File ManagersMay 13, 2025 am 10:14 AMLinux console file managers can be very helpful in day-to-day tasks, when managing files on a local machine, or when connected to a remote one. The visual console representation of the directory helps us quickly perform file/folder operations and sav
 qBittorrent: A Powerful Open-Source BitTorrent ClientMay 13, 2025 am 10:12 AM
qBittorrent: A Powerful Open-Source BitTorrent ClientMay 13, 2025 am 10:12 AMqBittorrent is a popular open-source BitTorrent client that allows users to download and share files over the internet. The latest version, qBittorrent 5.0, was released recently and comes packed with new features and improvements. This article will
 Setup Nginx Virtual Hosts, phpMyAdmin, and SSL on Arch LinuxMay 13, 2025 am 10:03 AM
Setup Nginx Virtual Hosts, phpMyAdmin, and SSL on Arch LinuxMay 13, 2025 am 10:03 AMThe previous Arch Linux LEMP article just covered basic stuff, from installing network services (Nginx, PHP, MySQL, and PhpMyAdmin) and configuring minimal security required for MySQL server and PhpMyadmin. This topic is strictly related to the forme
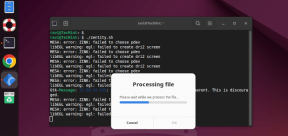 Zenity: Building GTK Dialogs in Shell ScriptsMay 13, 2025 am 09:38 AM
Zenity: Building GTK Dialogs in Shell ScriptsMay 13, 2025 am 09:38 AMZenity is a tool that allows you to create graphical dialog boxes in Linux using the command line. It uses GTK , a toolkit for creating graphical user interfaces (GUIs), making it easy to add visual elements to your scripts. Zenity can be extremely u


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

Zend Studio 13.0.1
Powerful PHP integrated development environment

SublimeText3 Chinese version
Chinese version, very easy to use

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software






