Securing your Linux environment: Backup and recovery strategies

introduction
In the dynamic Linux environment, protecting your data is crucial. Whether for personal use or operating in a server setup, understanding the depth of your backup and recovery strategies can be a game-changer. This article will introduce some methods and explore the multi-faceted approach to Linux backup and recovery strategy, including the necessity and how to ensure data security and retrieval.
Understanding the Linux file system
Before delving into the intricacies of backup and recovery strategies, it is crucial to understand the Linux file system. Linux supports multiple file systems, such as ext4, XFS, and Btrfs, and each file system has its own unique functions and data storage methods. Understanding the nuances of these file systems can greatly influence the choice of backup and recovery strategies, making them more robust and tailored to your specific needs.
Backup Strategy
Protecting your data starts with having a proper backup strategy. Let’s explore some of the backup options available in Linux environments.
Manual backup
Using basic Linux commands
Linux provides powerful commands such as cp, tar and rsync for manual backup. These commands are very flexible and allow the user to specify exactly what to back up.
advantage
- Have full control over the backup process
- No additional software required
shortcoming
- Good knowledge of Linux commands required
- Time consuming and prone to human error
Automatic backup
Cron job
Cron jobs make it possible to schedule backups regularly, automate the backup process, and reduce the possibility of human error.
Linux backup solution
Bacula and Amanda are comprehensive solutions that offer a range of features for automated backups.
advantage
- Regular automatic backup
- Comprehensive solution providing detailed reporting
shortcoming
- Initial setup can be complicated
- May burden system resources
Recovery Strategy
Having backups is only half the journey; becoming proficient at recovery is complete. Let us elaborate on the various recovery strategies related to Linux environment.
Manual recovery
Restore using Linux commands
Using Linux commands for recovery has the same advantages and disadvantages as those used for backup, providing control but requiring expertise.
Automatic recovery
Script utilization
Scripts can automate the recovery process, working seamlessly with backup tools to restore data when needed.
Integrated solutions
Many backup tools offer integrated recovery features that facilitate a seamless recovery process.
advantage
- Faster recovery
- Less prone to human error
shortcoming
- Setting up and maintaining the system can be complex
- Depends on tools and scripts
Backup and recovery strategies in different Linux environments
Linux is suitable for a variety of environments, from individual users to large enterprises, and each environment requires a customized backup and recovery strategy.
personal computer
Personal Linux Backup Tool
For individual users, tools such as Deja Dup and Timeshift provide user-friendly interfaces for backing up and restoring data.
server
Enterprise Solutions
In the enterprise space, solutions like Bareos provide a solid option for large-scale environments and are in high demand.
Best Practices
safety
Encrypted backup
Encryption ensures data security, making backups inaccessible to unauthorized users.
maintain
Regular testing
Regularly testing your backup setup ensures you have a functional recovery system when needed.
Log monitoring
Track backup status to help detect and resolve errors in a timely manner.
case study
A deep dive into actual situations presents a range of situations where a sound backup and recovery strategy actually saved the day, providing practical insights into its necessity.
in conclusion
The Linux environment, with its versatility and open source nature, provides a rich foundation for data processing. However, this also brings with it a responsibility to protect data effectively. Establishing a solid backup and recovery strategy not only protects information, but also provides peace of mind, security, and ensures business continuity in an enterprise environment.
Understanding and implementing a well-designed backup and recovery strategy is like having a well-oiled safety net, ready to catch you when the unexpected happens. In the ever-evolving digital space, let's move forward with caution and equip our Linux environments with the best backup and recovery strategies available today.
The above is the detailed content of Securing your Linux environment: Backup and recovery strategies. For more information, please follow other related articles on the PHP Chinese website!
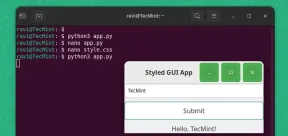 How to Create GUI Applications In Linux Using PyGObjectMay 13, 2025 am 11:09 AM
How to Create GUI Applications In Linux Using PyGObjectMay 13, 2025 am 11:09 AMCreating graphical user interface (GUI) applications is a fantastic way to bring your ideas to life and make your programs more user-friendly. PyGObject is a Python library that allows developers to create GUI applications on Linux desktops using the
 How to Install LAMP Stack with PhpMyAdmin in Arch LinuxMay 13, 2025 am 11:01 AM
How to Install LAMP Stack with PhpMyAdmin in Arch LinuxMay 13, 2025 am 11:01 AMArch Linux provides a flexible cutting-edge system environment and is a powerfully suited solution for developing web applications on small non-critical systems because is a completely open source and provides the latest up-to-date releases on kernel
 How to Install LEMP (Nginx, PHP, MariaDB) on Arch LinuxMay 13, 2025 am 10:43 AM
How to Install LEMP (Nginx, PHP, MariaDB) on Arch LinuxMay 13, 2025 am 10:43 AMDue to its Rolling Release model which embraces cutting-edge software Arch Linux was not designed and developed to run as a server to provide reliable network services because it requires extra time for maintenance, constant upgrades, and sensible fi
![12 Must-Have Linux Console [Terminal] File Managers](https://img.php.cn/upload/article/001/242/473/174710245395762.png?x-oss-process=image/resize,p_40) 12 Must-Have Linux Console [Terminal] File ManagersMay 13, 2025 am 10:14 AM
12 Must-Have Linux Console [Terminal] File ManagersMay 13, 2025 am 10:14 AMLinux console file managers can be very helpful in day-to-day tasks, when managing files on a local machine, or when connected to a remote one. The visual console representation of the directory helps us quickly perform file/folder operations and sav
 qBittorrent: A Powerful Open-Source BitTorrent ClientMay 13, 2025 am 10:12 AM
qBittorrent: A Powerful Open-Source BitTorrent ClientMay 13, 2025 am 10:12 AMqBittorrent is a popular open-source BitTorrent client that allows users to download and share files over the internet. The latest version, qBittorrent 5.0, was released recently and comes packed with new features and improvements. This article will
 Setup Nginx Virtual Hosts, phpMyAdmin, and SSL on Arch LinuxMay 13, 2025 am 10:03 AM
Setup Nginx Virtual Hosts, phpMyAdmin, and SSL on Arch LinuxMay 13, 2025 am 10:03 AMThe previous Arch Linux LEMP article just covered basic stuff, from installing network services (Nginx, PHP, MySQL, and PhpMyAdmin) and configuring minimal security required for MySQL server and PhpMyadmin. This topic is strictly related to the forme
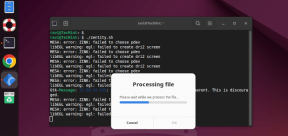 Zenity: Building GTK Dialogs in Shell ScriptsMay 13, 2025 am 09:38 AM
Zenity: Building GTK Dialogs in Shell ScriptsMay 13, 2025 am 09:38 AMZenity is a tool that allows you to create graphical dialog boxes in Linux using the command line. It uses GTK , a toolkit for creating graphical user interfaces (GUIs), making it easy to add visual elements to your scripts. Zenity can be extremely u
 Top 22 Best Music Players for LinuxMay 13, 2025 am 09:25 AM
Top 22 Best Music Players for LinuxMay 13, 2025 am 09:25 AMSome may describe it as their passion, while others may consider it a stress reliever or a part of their daily life. In every form, listening to music has become an inseparable part of our lives. Music plays different roles in our lives. Sometimes it


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

Dreamweaver Mac version
Visual web development tools

Dreamweaver CS6
Visual web development tools

SublimeText3 Chinese version
Chinese version, very easy to use







