How to operate PPT design Rubik's Cube renderings
php editor Strawberry will share with you an article today about how to use PPT to design Rubik's Cube renderings. In our daily work, we often need to make PPT to display work results or make reports. How to use Rubik's Cube renderings to enhance the visual effect of PPT and make the content more vivid and interesting is a question that many people are concerned about. Below, we will introduce in detail how to use Rubik's Cube renderings in PPT to make your presentation more attractive.
1. Open PPT and create a blank presentation.

2. Insert a square.

3. Copy multiple squares and combine them into a whole, which is also square as a whole.

4. Rotate the combined graphics three-dimensionally in an isometric upper-right direction.

5. Copy the combined shape and perform a three-dimensional rotation with the top of the same length facing upward.

6. Move the position of the combined graphics to get two sides of the Rubik's Cube.

7. Copy another combined shape and perform isometric lower-left three-dimensional rotation.

8. Similarly, if you move the position, you will get another side.

9. Finally, set the theme color for the combined shape of each face to get the final effect.

The above is the detailed content of How to operate PPT design Rubik's Cube renderings. For more information, please follow other related articles on the PHP Chinese website!
 Consolidate in Excel: Merge multiple sheets into oneApr 29, 2025 am 10:04 AM
Consolidate in Excel: Merge multiple sheets into oneApr 29, 2025 am 10:04 AMThis tutorial explores various methods for combining Excel sheets, catering to different needs: consolidating data, merging sheets via data copying, or merging spreadsheets based on key columns. Many Excel users face the challenge of merging multipl
 Calculate moving average in Excel: formulas and chartsApr 29, 2025 am 09:47 AM
Calculate moving average in Excel: formulas and chartsApr 29, 2025 am 09:47 AMThis tutorial shows you how to quickly calculate simple moving averages in Excel, using functions to determine moving averages over the last N days, weeks, months, or years, and how to add a moving average trendline to your charts. Previous articles
 How to calculate average in Excel: formula examplesApr 29, 2025 am 09:38 AM
How to calculate average in Excel: formula examplesApr 29, 2025 am 09:38 AMThis tutorial demonstrates various methods for calculating averages in Excel, including formula-based and formula-free approaches, with options for rounding results. Microsoft Excel offers several functions for averaging numerical data, and this gui
 How to calculate weighted average in Excel (SUM and SUMPRODUCT formulas)Apr 29, 2025 am 09:32 AM
How to calculate weighted average in Excel (SUM and SUMPRODUCT formulas)Apr 29, 2025 am 09:32 AMThis tutorial shows you two simple ways to calculate weighted averages in Excel: using the SUM or SUMPRODUCT function. Previous articles covered basic Excel averaging functions. But what if some values are more important than others, impacting the f
 Using Excel Find and Replace in the most efficient wayApr 29, 2025 am 09:07 AM
Using Excel Find and Replace in the most efficient wayApr 29, 2025 am 09:07 AMThis tutorial demonstrates how to efficiently locate and modify data within Excel spreadsheets using the Find and Replace function. We'll cover basic and advanced techniques, including wildcard searches and modifications across multiple workbooks. W
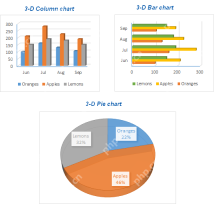 How to make a chart (graph) in Excel and save it as templateApr 28, 2025 am 09:31 AM
How to make a chart (graph) in Excel and save it as templateApr 28, 2025 am 09:31 AMThis Excel charting tutorial provides a comprehensive guide to creating and customizing graphs within Microsoft Excel. Learn to visualize data effectively, from basic chart creation to advanced techniques. Everyone uses Excel charts to visualize dat
 Excel charts: add title, customize chart axis, legend and data labelsApr 28, 2025 am 09:18 AM
Excel charts: add title, customize chart axis, legend and data labelsApr 28, 2025 am 09:18 AMAfter you have created a chart in Excel, what's the first thing you usually want to do with it? Make the graph look exactly the way you've pictured it in your mind! In modern versions of Excel, customizing charts is easy and fun. Microsof
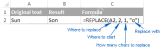 Using Excel REPLACE and SUBSTITUTE functions - formula examplesApr 28, 2025 am 09:16 AM
Using Excel REPLACE and SUBSTITUTE functions - formula examplesApr 28, 2025 am 09:16 AMThis tutorial demonstrates the Excel REPLACE and SUBSTITUTE functions with practical examples. Learn how to use REPLACE with text, numbers, and dates, and how to nest multiple REPLACE or SUBSTITUTE functions within a single formula. Last week, we ex


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Zend Studio 13.0.1
Powerful PHP integrated development environment

WebStorm Mac version
Useful JavaScript development tools

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),






