Linux system transplantation: address mapping revealed

In the process of implementing Linux system migration, special attention needs to be paid to address-related matters. The following is a summary of relevant views:
1. The importance of address mapping
In the process of Linux system transplantation, accurate address mapping plays a decisive role. It determines how the operating system accesses and controls the flow of data in memory.
2. Physical address and virtual address
During the Linux migration process, there is a mapping relationship between physical addresses and virtual addresses. The physical address refers to the actual memory address of the hardware facility; correspondingly Do you need to pay attention to the address when transplanting Linuxlinux windows? The virtual address is the logical addressing method introduced by the operating system for the application.
3. Kernel space and user space
In the Linux environment, we divide the computer into two parts: kernel space and user space, which are respectively responsible for the operation of the operating system core code and the operation of application software.
4. Kernel mapping
During the running stage of the Linux system, physical address mapping and allocation of the kernel need to be performed to ensure the normal operation of the kernel and effective memory management and code reading and writing control.
5.Device driver
The device driver is a key part of Linux system transplantation, and its design must fully consider the correspondence between the device's physical address and virtual address.
6. Memory management
In the Linux system transplantation process, the improvement of memory management is crucial. We must ensure that it can properly coordinate memory allocation and release, and accurately map real addresses to virtual addresses.
7. Compilation options
During the Linux transplantation process, you need to pay attention to the selection of compilation optionsDo you need to pay attention to the address when transplanting Linux, because it is directly related to the memory layout of the generated executable file.
8. Debugging tools
In the analysis of specific problems, debugging tools play a decisive role. With the help of such tools, we can quickly and intuitively review and adjust the memory contents to quickly identify and resolve defects related to address issues.
Through the above eight key factors, we can deeply understand that the address issue is a crucial issue in the Linux transplantation process and requires special attention. Only by properly solving this issue can we ensure that the Linux operating system can run healthily on the corresponding hardware platform.
We hope this sharing can provide valuable guidance and reference for developers working on Linux porting projects. When it comes to address issues, be sure to treat them with caution and develop appropriate countermeasures based on the specific situation.
The above is the detailed content of Linux system transplantation: address mapping revealed. For more information, please follow other related articles on the PHP Chinese website!
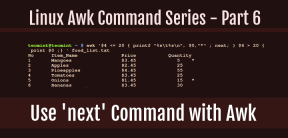 How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AM
How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AMIn this sixth installment of our Awk series, we will explore the next command, which is instrumental in enhancing the efficiency of your script executions by skipping redundant processing steps.What is the next Command?The next command in awk instruc
 How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AM
How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AMTransferring files in Linux systems is a common task that every system administrator should master, especially when it comes to network transmission between local or remote systems. Linux provides two commonly used tools to accomplish this task: SCP (Secure Replication) and Rsync. Both provide a safe and convenient way to transfer files between local or remote machines. This article will explain in detail how to use SCP and Rsync commands to transfer files, including local and remote file transfers. Understand the scp (Secure Copy Protocol) in Linux scp command is a command line program used to securely copy files and directories between two hosts via SSH (Secure Shell), which means that when files are transferred over the Internet, the number of
 10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AM
10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AMOne fascinating feature of Linux, in contrast to Windows and Mac OS X, is its support for a variety of desktop environments. This allows desktop users to select the most suitable and fitting desktop environment based on their computing requirements.A
 How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AM
How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AMLibreOffice stands out as a robust and open-source office suite, tailored for Linux, Windows, and Mac platforms. It boasts an array of advanced features for handling word documents, spreadsheets, presentations, drawings, calculations, and mathematica
 How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AM
How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AMLinux users who manage PDF files have a wide array of programs at their disposal. Specifically, there are numerous specialized PDF tools designed for various functions.For instance, you might opt to install a PDF viewer for reading files or a PDF edi
 How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AM
How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AMIn the earlier segments of the Awk command series, our focus was primarily on reading input from files. However, what if you need to read input from STDIN?In Part 7 of the Awk series, we will explore several examples where you can use the output of o
 Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AM
Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AMClifm stands out as a distinctive and incredibly swift command-line file manager, designed on the foundation of a shell-like interface. This means that users can engage with their file system using commands they are already familiar with.The choice o
 How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AM
How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AMIf you prefer not to perform a new installation of Linux Mint 22 Wilma, you have the option to upgrade from a previous version.In this guide, we will detail the process to upgrade from Linux Mint 21.3 (the most recent minor release of the 21.x series


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.






