What are Linux kernel space and user space?
Kernel space and user space
For a 32-bit operating system, its addressing space (also called virtual address space or linear address space) size is 4G (that is, 2 to the 32nd power). This means that a process can have a maximum address space of 4G.
The core of the operating system is the kernel, which is separated from ordinary applications and has permission to access protected memory space and underlying hardware devices. In order to ensure the security of the kernel, modern operating systems usually restrict user processes from directly operating the kernel.
Typically, this is achieved by dividing the virtual address space into two parts, kernel space and user space. As far as the Linux operating system is concerned, the highest 1G bytes (from virtual address 0xC0000000 to 0xFFFFFFFF) are used by the kernel and are called kernel space. The lower 3G bytes (from virtual address 0x00000000 to 0xBFFFFFFF) are used by individual processes and are called user space.
In other words, among the 4G address space of each process, the highest 1G is the same, that is, the kernel space. Only the remaining 3G is the available space for the process itself.
It can be understood like this: "The maximum 1G kernel space is shared among all processes!" The following figure shows the allocation of 4G address space for each process (picture comes from the Internet):

Why do we need to distinguish between kernel space and user space
Among all the instructions of the CPU, some are very dangerous and will cause the system to crash if used incorrectly, such as clearing memory, setting the clock, etc. If all programs are allowed to use these instructions, the probability of a system crash will be greatly increased.
So, the CPU divides instructions into privileged instructions and non-privileged instructions. For those dangerous instructions, only the operating system and its related modules are allowed to use them, and ordinary applications can only use those instructions that will not cause disaster.
For example, Intel's CPU divides the privilege level into 4 levels: Ring0~Ring3. In fact, Linux systems only use two run levels, Ring0 and Ring3 (the same is true for Windows systems).
When a process is running at Ring3 level, it is said to be running in user mode, and when it is running at Ring0 level, it is said to be running in kernel mode.
Kernel state and user state
Okay, now we need to explain what kernel mode and user mode are: "When a process runs in kernel space, it is in kernel mode, and when a process runs in user space, it is in user mode."
In kernel mode, the process runs in the kernel address space, and the CPU can execute any instructions at this time. The running code is not subject to any restrictions and can freely access any valid address or directly access the port.
In user mode, the process runs in the user address space. The executed code is subject to many checks by the CPU. They can only access pages that are accessible in user mode as specified in the page table entries mapping their address space. Virtual address, and can only directly access the accessible ports specified in the I/O Permission Bitmap in the Task Status Segment (TSS).
For the previous DOS operating system, there was no concept of kernel space, user space, kernel mode, and user mode. It can be considered that all code runs in the kernel mode, so user-written application code can easily crash the operating system.
For Linux, the design of distinguishing kernel space and user space isolates operating system code (operating system code is much more robust than application code) and application code.
Even if an error occurs in a single application, it will not affect the stability of the operating system, so that other programs can still run normally (Linux is a multi-tasking system!).
"So, distinguishing between kernel space and user space is essentially to improve the stability and availability of the operating system."
How to enter kernel space from user space
In fact, all system resource management is completed in the kernel space. For example, reading and writing disk files, allocating and recycling memory, reading and writing data from network interfaces, etc.
Our application cannot directly perform such operations. But we can accomplish such tasks through the interface provided by the kernel.
For example, if an application wants to read a file on the disk, it can initiate a "system call" to the kernel and tell the kernel: "I want to read a certain file on the disk."
In fact, a special instruction is used to allow the process to enter the kernel state (to the kernel space) from the user state. In the kernel space, the CPU can execute any instructions, including reading data from the disk. The specific process is to first read the data into the kernel space, then copy the data to the user space and switch from the kernel mode to the user mode.
At this point, the application has returned from the system call and obtained the desired data, and can happily continue execution. To put it simply, the application outsources high-tech things (reading files from disk) to the system kernel, and the system kernel does these things professionally and efficiently.
For a process, the process of entering kernel space from user space and finally returning to user space is very complicated. For example, the concept "stack" that we often come into contact with actually has a stack in the kernel mode and user mode.
When running in user space, the process uses the stack in user space, and when running in kernel space, the process uses the stack in kernel space. Therefore, each process in Linux has two stacks, one for user mode and one for kernel mode.
The following figure briefly describes the conversion between user mode and kernel mode:

Since the user mode process must switch to the kernel mode in order to use the system resources, let's take a look at how many ways the process can enter from the user mode to the kernel mode.
In summary, there are three ways: system call, software interrupt and hardware interrupt. Each of these three methods involves a lot of operating system knowledge, so they will not be expanded upon here.
the whole frame
Next, let’s take a look at the structure of the entire Linux system from the perspective of kernel space and user space. It can be roughly divided into three parts, from bottom to top: hardware -> kernel space -> user space. As shown in the picture below (this picture comes from the Internet):

On top of the hardware, the code in the kernel space controls the use of hardware resources. The code in the user space can only use the hardware resources in the system through the system call interface (System Call Interface) exposed by the kernel. . In fact, not only Linux, but also the design of Windows operating systems is similar.
In fact we can summarize the activity of each processor at any given point in time as one of the following three:
- Runs in user space and executes user processes.
- Runs in the kernel space, in the process context, and executes on behalf of a specific process.
- Runs in kernel space, is in interrupt context, has nothing to do with any process, and handles a specific interrupt.
The above three points include almost all situations. For example, when the CPU is idle, the kernel runs an empty process, which is in the process context but runs in the kernel space.
Note: The interrupt service routines of Linux systems are not executed in the context of the process. They are executed in a specialized interrupt context that is independent of all processes.
The reason why there is a special execution environment is to ensure that the interrupt service program can respond to and handle the interrupt request as soon as possible, and then exit quickly.
Подведем итог
Большинство современных операционных систем защищают безопасность и стабильность самой операционной системы за счет проектирования пространства ядра и пользовательского пространства. Поэтому, когда мы читаем информацию об операционных системах, мы часто сталкиваемся с такими понятиями, как пространство ядра, пространство пользователя, режим ядра и режим пользователя.Я надеюсь, что эта статья поможет вам понять эти основные понятия.
The above is the detailed content of What are Linux kernel space and user space?. For more information, please follow other related articles on the PHP Chinese website!
 How to Automatically Restart a Failed Service in LinuxApr 28, 2025 am 09:39 AM
How to Automatically Restart a Failed Service in LinuxApr 28, 2025 am 09:39 AMThis guide details how to configure automatic service restarts in Linux using systemd, enhancing system reliability and minimizing downtime. System administrators often rely on this functionality to ensure critical services, such as web servers (Apa
 10 Hidden Linux Commands Every Sysadmin Should KnowApr 28, 2025 am 09:35 AM
10 Hidden Linux Commands Every Sysadmin Should KnowApr 28, 2025 am 09:35 AMAs Linux users, we often rely on commonly used commands ls, grep, awk, sed and find to complete the work. But Linux has a large number of lesser-known commands that can save time, automate tasks and simplify workflows. This article will explore some underrated but powerful Linux commands that deserve more attention. rename – efficient batch rename files The rename command is the savior when you need to rename multiple files at once. Without using loops containing mv, rename allows you to easily apply complex renaming patterns. Change all .txt files to .log. rename 's/\.txt$/\.log/' *
 How to List All Running Services Under Systemd in LinuxApr 28, 2025 am 09:29 AM
How to List All Running Services Under Systemd in LinuxApr 28, 2025 am 09:29 AMLinux systems provide various system services (such as process management, login, syslog, cron, etc.) and network services (such as remote login, email, printer, web hosting, data storage, file transfer, domain name resolution (using DNS), dynamic IP address allocation (using DHCP), and so on). Technically, a service is a process or group of process (usually known as a daemon) that runs continuously in the background, waiting for incoming requests (especially from the client). Linux supports different ways to manage services (start, stop, restart, enable automatic startup at system startup, etc.), usually through a process or service manager. Almost all modern Linux distributions now use the same
 CrossOver 25: Run Windows Software and Games on LinuxApr 28, 2025 am 09:27 AM
CrossOver 25: Run Windows Software and Games on LinuxApr 28, 2025 am 09:27 AMRun Windows Software and Games on Linux with CrossOver 25 Running Windows applications and games on Linux is now easier than ever, thanks to CrossOver 25 from CodeWeavers. This commercial software solution lets Linux users run a wide variety of Wind
![pCloud - The Most Secure Cloud Storage [50% Off Offer]](https://img.php.cn/upload/article/001/242/473/174580357418126.jpg?x-oss-process=image/resize,p_40) pCloud - The Most Secure Cloud Storage [50% Off Offer]Apr 28, 2025 am 09:26 AM
pCloud - The Most Secure Cloud Storage [50% Off Offer]Apr 28, 2025 am 09:26 AMSecure Your Data with pCloud: A Comprehensive Guide to Linux Installation pCloud, a leading secure cloud storage service, provides a robust platform for managing your files and data. This guide details the installation process on Linux systems. About
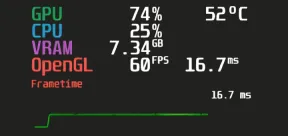 MangoHud - Monitor FPS, CPU & GPU Usage in Linux GamesApr 28, 2025 am 09:25 AM
MangoHud - Monitor FPS, CPU & GPU Usage in Linux GamesApr 28, 2025 am 09:25 AMMangoHud: A powerful tool for real-time monitoring of Linux gaming performance MangoHud is a powerful and lightweight tool designed for gamers, developers, and anyone who wants to monitor system performance in real time. It acts as an overlay for Vulkan and OpenGL applications, displaying important information such as FPS, CPU and GPU usage, temperature, etc. This article will explore the functions, working principles and usage of MangoHud, and provide step-by-step instructions for installing and configuring MangoHud on Linux systems. What is MangoHud? MangoHud is an open source project available on GitHub and aims to provide a simple and customizable way to monitor
 5 Must-Know Linux Command Line Archive Tools – Part 1Apr 28, 2025 am 09:23 AM
5 Must-Know Linux Command Line Archive Tools – Part 1Apr 28, 2025 am 09:23 AMManaging archived files is a common task in Linux. This article, the first of a two-part series, explores five powerful command-line archive tools, detailing their features and usage with examples. 1. The tar Command: A Versatile Archiving Utility t
 Top 7 Tools to Compare Files in Linux (with Examples)Apr 28, 2025 am 09:21 AM
Top 7 Tools to Compare Files in Linux (with Examples)Apr 28, 2025 am 09:21 AMThis guide explores various methods for comparing text files in Linux, a crucial task for system administrators and developers. We'll cover command-line tools and visual diff tools, highlighting their strengths and appropriate use cases. Let's assum


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Dreamweaver CS6
Visual web development tools

WebStorm Mac version
Useful JavaScript development tools

Atom editor mac version download
The most popular open source editor

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software







