1. Background of Write Once
In computer technology, people have always attached great importance to the integrity and security of data. In order to effectively protect data security and avoid damage caused by malicious tampering and misuse, the feature "WriteOnce" (WriteOnce) was born.
2. Implementation principle of Write Once
The core technology of Linux is to achieve the "write once" function by adopting the read-only file system mode. This file system only allows reading and prohibits writing, thus ensuring the uniqueness and immutability of data.
3. The impact of Write Once on system stability
The "write once" feature is crucial to ensuring system stability. Since the data cannot be changed or deleted, it can prevent various possible misoperations or malicious attacks and avoid data loss. At the same time, the linux kernel writes once, which can also effectively prevent the system from being invaded by viruses or malware.
4. Write Once guarantees data security
The "cannot be changed after writing" feature fully demonstrates its powerful advantages in data security. Even if it encounters malicious network attacks or even virus attacks, the data will remain safe and sound. This is significant in protecting some core data.

5. Limitations of Write Once
Although the "Write Once" feature has many benefits, it still has its shortcomings. Because data cannot be changed or deleted, updates or repairs may be frustrated in some cases. To avoid possible problems, it is recommended that you think carefully about the inherent stability of your data and potential future needs.
6. Practical application cases of Write Once
The "Write Once" feature is used in many industries. For example, key data in the financial field, such as transaction records and account information, can use this technology to ensure its security. Similarly, in the medical industry, this feature also plays a role in protecting important data such as patient medical records and diagnostic results.
7. How to use the Write Once feature correctly
In order to make the system more stable and data fully protected Linux web server, we need to correctly set the Write Once function. First, please carefully weigh the practicality required and then choose the most appropriate technical strategy. Next, while practicing this function, you must pay attention to designing appropriate backup and recovery measures to deal with possible problems at any time.
Through the above detailed interpretation of the Linux kernel Write Once featurelinux kernel write onceThis is how Linux should be learned. I believe you have a more comprehensive understanding of it. This feature has a profound impact on ensuring the robustness and security of data, so it is widely used in practice. During use, we must pay attention to the stability of the data itself and take into account possible diverse needs in the future to ensure that our equipment runs smoothly and the data is safe.
The above is the detailed content of Ensure permanent information security: Write Once technology revealed. For more information, please follow other related articles on the PHP Chinese website!
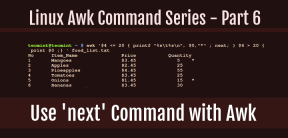 How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AM
How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AMIn this sixth installment of our Awk series, we will explore the next command, which is instrumental in enhancing the efficiency of your script executions by skipping redundant processing steps.What is the next Command?The next command in awk instruc
 How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AM
How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AMTransferring files in Linux systems is a common task that every system administrator should master, especially when it comes to network transmission between local or remote systems. Linux provides two commonly used tools to accomplish this task: SCP (Secure Replication) and Rsync. Both provide a safe and convenient way to transfer files between local or remote machines. This article will explain in detail how to use SCP and Rsync commands to transfer files, including local and remote file transfers. Understand the scp (Secure Copy Protocol) in Linux scp command is a command line program used to securely copy files and directories between two hosts via SSH (Secure Shell), which means that when files are transferred over the Internet, the number of
 10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AM
10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AMOne fascinating feature of Linux, in contrast to Windows and Mac OS X, is its support for a variety of desktop environments. This allows desktop users to select the most suitable and fitting desktop environment based on their computing requirements.A
 How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AM
How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AMLibreOffice stands out as a robust and open-source office suite, tailored for Linux, Windows, and Mac platforms. It boasts an array of advanced features for handling word documents, spreadsheets, presentations, drawings, calculations, and mathematica
 How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AM
How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AMLinux users who manage PDF files have a wide array of programs at their disposal. Specifically, there are numerous specialized PDF tools designed for various functions.For instance, you might opt to install a PDF viewer for reading files or a PDF edi
 How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AM
How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AMIn the earlier segments of the Awk command series, our focus was primarily on reading input from files. However, what if you need to read input from STDIN?In Part 7 of the Awk series, we will explore several examples where you can use the output of o
 Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AM
Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AMClifm stands out as a distinctive and incredibly swift command-line file manager, designed on the foundation of a shell-like interface. This means that users can engage with their file system using commands they are already familiar with.The choice o
 How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AM
How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AMIf you prefer not to perform a new installation of Linux Mint 22 Wilma, you have the option to upgrade from a previous version.In this guide, we will detail the process to upgrade from Linux Mint 21.3 (the most recent minor release of the 21.x series


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

Notepad++7.3.1
Easy-to-use and free code editor

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

SublimeText3 Mac version
God-level code editing software (SublimeText3)

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment






