Application of downsampling in convolutional neural networks

Downsampling is a key technology in convolutional neural networks, which is used to reduce the amount of calculation, prevent overfitting and improve the generalization ability of the model. It is usually implemented in a pooling layer after a convolutional layer.
The purpose of downsampling is to reduce the dimension of the output. Commonly used methods include maximum pooling, average pooling and other operations. These methods select parts of the information from the input data to operate on to reduce the dimensionality of the output. In convolutional neural networks, downsampling is usually implemented through pooling operations.
Max pooling is a common pooling operation that works by selecting the maximum value in a specific window of the input image as the output. The effect of this operation is to reduce the size of the output feature map, thereby reducing the complexity of the model. For example, if the original input is a 4x4 image, after 2x2 max pooling, the output feature map size will become 2x2. This pooling operation is commonly used in convolutional neural networks and can help extract key features in images and reduce the amount of calculations.
Average pooling is to average the pixel values in the pooling window as the output, so as to obtain a smoother feature map, reduce the sensitivity of the model to details, and improve the generalization of the model. ization ability.
In addition to max pooling and average pooling, there are other types of pooling operations, such as LSTM pooling and adaptive average pooling. Additionally, there are many other methods for downsampling. One of the common methods is to use a 2x2 convolution kernel and a convolutional layer with a stride of 2. This convolutional layer slides on the input feature map, moving 2 pixels at a time, and performs a convolution operation on the covered area to obtain a smaller output feature map.
Another approach is to use separable convolutions. This convolution method can perform convolution operations separately along the two dimensions of the input feature map, and then merge the results. Since separable convolution can reduce the amount of calculation, it can be used as an alternative to downsampling in some scenarios.
In addition, there are some more complex model structures that can achieve downsampling, such as residual networks and attention mechanisms. These model structures can learn more complex feature representations by introducing additional layers or modules, while also enabling downsampling.
The role of downsampling in convolutional neural networks:
1. Reduce the amount of calculation: Through downsampling, model needs can be significantly reduced The amount of input data processed thereby reduces computational complexity. This allows models to be run on smaller hardware devices or enables more complex models.
2. Improve generalization ability: Downsampling reduces the sensitivity of the model to specific details by downsampling and dimensionality reduction of the input data, allowing the model to better generalize. to new, unseen data.
3. Prevent overfitting: Through downsampling, the degree of freedom of the model can be reduced, thereby preventing overfitting. This makes the model perform better on the training data and also perform better on the test data.
4. Feature compression: Downsampling can compress features by selecting the most important features (as in max pooling) or the average features (as in average pooling) . This helps reduce the storage requirements of the model, while also protecting the performance of the model to a certain extent.
In short, convolutional neural networks usually use downsampling operations to reduce the size of feature maps, thereby reducing the amount of calculation and number of parameters, while increasing the robustness and generalization of the model. ability.
The above is the detailed content of Application of downsampling in convolutional neural networks. For more information, please follow other related articles on the PHP Chinese website!
 The Hidden Dangers Of AI Internal Deployment: Governance Gaps And Catastrophic RisksApr 28, 2025 am 11:12 AM
The Hidden Dangers Of AI Internal Deployment: Governance Gaps And Catastrophic RisksApr 28, 2025 am 11:12 AMThe unchecked internal deployment of advanced AI systems poses significant risks, according to a new report from Apollo Research. This lack of oversight, prevalent among major AI firms, allows for potential catastrophic outcomes, ranging from uncont
 Building The AI PolygraphApr 28, 2025 am 11:11 AM
Building The AI PolygraphApr 28, 2025 am 11:11 AMTraditional lie detectors are outdated. Relying on the pointer connected by the wristband, a lie detector that prints out the subject's vital signs and physical reactions is not accurate in identifying lies. This is why lie detection results are not usually adopted by the court, although it has led to many innocent people being jailed. In contrast, artificial intelligence is a powerful data engine, and its working principle is to observe all aspects. This means that scientists can apply artificial intelligence to applications seeking truth through a variety of ways. One approach is to analyze the vital sign responses of the person being interrogated like a lie detector, but with a more detailed and precise comparative analysis. Another approach is to use linguistic markup to analyze what people actually say and use logic and reasoning. As the saying goes, one lie breeds another lie, and eventually
 Is AI Cleared For Takeoff In The Aerospace Industry?Apr 28, 2025 am 11:10 AM
Is AI Cleared For Takeoff In The Aerospace Industry?Apr 28, 2025 am 11:10 AMThe aerospace industry, a pioneer of innovation, is leveraging AI to tackle its most intricate challenges. Modern aviation's increasing complexity necessitates AI's automation and real-time intelligence capabilities for enhanced safety, reduced oper
 Watching Beijing's Spring Robot RaceApr 28, 2025 am 11:09 AM
Watching Beijing's Spring Robot RaceApr 28, 2025 am 11:09 AMThe rapid development of robotics has brought us a fascinating case study. The N2 robot from Noetix weighs over 40 pounds and is 3 feet tall and is said to be able to backflip. Unitree's G1 robot weighs about twice the size of the N2 and is about 4 feet tall. There are also many smaller humanoid robots participating in the competition, and there is even a robot that is driven forward by a fan. Data interpretation The half marathon attracted more than 12,000 spectators, but only 21 humanoid robots participated. Although the government pointed out that the participating robots conducted "intensive training" before the competition, not all robots completed the entire competition. Champion - Tiangong Ult developed by Beijing Humanoid Robot Innovation Center
 The Mirror Trap: AI Ethics And The Collapse Of Human ImaginationApr 28, 2025 am 11:08 AM
The Mirror Trap: AI Ethics And The Collapse Of Human ImaginationApr 28, 2025 am 11:08 AMArtificial intelligence, in its current form, isn't truly intelligent; it's adept at mimicking and refining existing data. We're not creating artificial intelligence, but rather artificial inference—machines that process information, while humans su
 New Google Leak Reveals Handy Google Photos Feature UpdateApr 28, 2025 am 11:07 AM
New Google Leak Reveals Handy Google Photos Feature UpdateApr 28, 2025 am 11:07 AMA report found that an updated interface was hidden in the code for Google Photos Android version 7.26, and each time you view a photo, a row of newly detected face thumbnails are displayed at the bottom of the screen. The new facial thumbnails are missing name tags, so I suspect you need to click on them individually to see more information about each detected person. For now, this feature provides no information other than those people that Google Photos has found in your images. This feature is not available yet, so we don't know how Google will use it accurately. Google can use thumbnails to speed up finding more photos of selected people, or may be used for other purposes, such as selecting the individual to edit. Let's wait and see. As for now
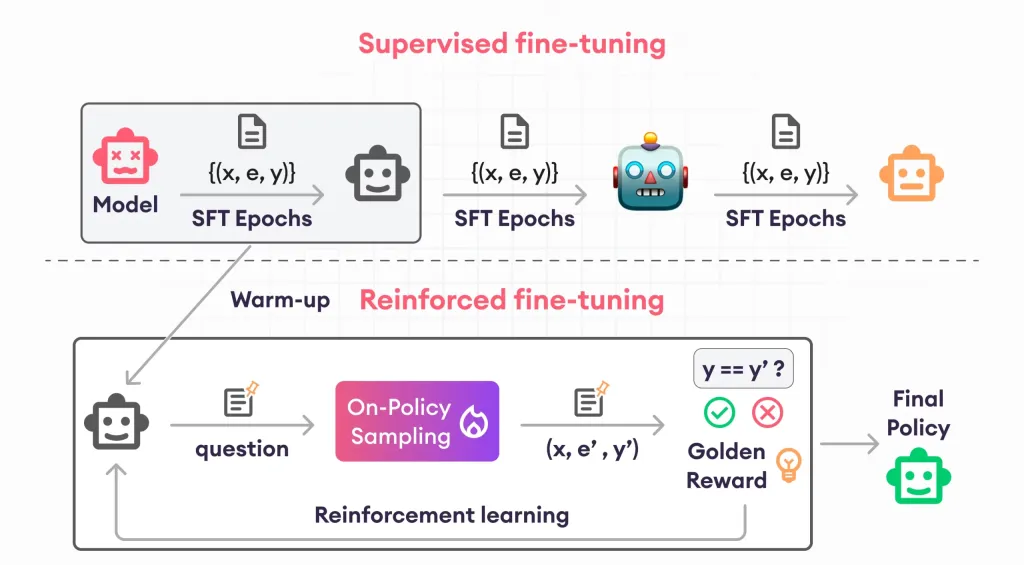 Guide to Reinforcement Finetuning - Analytics VidhyaApr 28, 2025 am 09:30 AM
Guide to Reinforcement Finetuning - Analytics VidhyaApr 28, 2025 am 09:30 AMReinforcement finetuning has shaken up AI development by teaching models to adjust based on human feedback. It blends supervised learning foundations with reward-based updates to make them safer, more accurate, and genuinely help
 Let's Dance: Structured Movement To Fine-Tune Our Human Neural NetsApr 27, 2025 am 11:09 AM
Let's Dance: Structured Movement To Fine-Tune Our Human Neural NetsApr 27, 2025 am 11:09 AMScientists have extensively studied human and simpler neural networks (like those in C. elegans) to understand their functionality. However, a crucial question arises: how do we adapt our own neural networks to work effectively alongside novel AI s


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

SublimeText3 Chinese version
Chinese version, very easy to use

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.






