No password required to run sudo commands in Linux
Assuming you are running a Linux system on a computer that you only use, such as a laptop, you will need to enter a password every time you call sudo, which will be tedious in the long run. Therefore, in this guide, we will describe how to configure the sudo command to run without entering a password.

This setting is done in the /etc/sudoers file, which is the default security policy using the sudo command; in the user permissions specification section.
IMPORTANT: In sudeors files, the authenticate parameter is turned on by default for authentication purposes. If it is set, the user must authenticate with a password (or other authentication method) before they can run a command using sudo.
However, this default can be overridden using the NOPASSWD (no password required when user calls sudo command) flag.
The syntax for configuring user permissions is as follows:user_list host_list=effective_user_list tag_list command_list
in:
- user_list - User list or user alias that has been set.
- host_list - A list of hosts or host aliases on which the user can run sudo.
- effective_user_list - List of users running as this user or alias
- tag_list - tag list, such as NOPASSWD.
- command_list - A list of commands or command aliases that the user runs using sudo.
To allow a user (aaronkilik in the example below) to run all commands using sudo without entering a password, open the sudoers file:
$ sudo visudoAdd the following lines:
aaronkilik ALL=(ALL) NOPASSWD: ALL
For groups, use the % characters before the group name; this means that all members of the sys group can use sudo without a password.
%sys ALL=(ALL) NOPASSWD: ALL
To allow users to run the specified command without a password using sudo (/bin/kill), add the following line:
aaronkilik ALL=(ALL) NOPASSWD: /bin/kill
下面的行会让 sys 组成员在使用 sudo 运行命令:/bin/kill 、/bin/rm 时不用输入密码:
%sys ALL=(ALL) NOPASSWD: /bin/kill, /bin/rm

不用密码运行 sudo
在本篇中,我们讨论了如何配置 sudo 命令来不用输入密码运行。不要忘记在评论栏中给我们提供你关于这份指导的想法和其他对于 Linux 系统管理员有用的 sudoers 配置。
The above is the detailed content of No password required to run sudo commands in Linux. For more information, please follow other related articles on the PHP Chinese website!
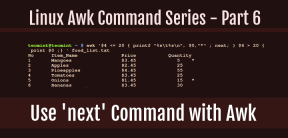 How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AM
How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AMIn this sixth installment of our Awk series, we will explore the next command, which is instrumental in enhancing the efficiency of your script executions by skipping redundant processing steps.What is the next Command?The next command in awk instruc
 How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AM
How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AMTransferring files in Linux systems is a common task that every system administrator should master, especially when it comes to network transmission between local or remote systems. Linux provides two commonly used tools to accomplish this task: SCP (Secure Replication) and Rsync. Both provide a safe and convenient way to transfer files between local or remote machines. This article will explain in detail how to use SCP and Rsync commands to transfer files, including local and remote file transfers. Understand the scp (Secure Copy Protocol) in Linux scp command is a command line program used to securely copy files and directories between two hosts via SSH (Secure Shell), which means that when files are transferred over the Internet, the number of
 10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AM
10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AMOne fascinating feature of Linux, in contrast to Windows and Mac OS X, is its support for a variety of desktop environments. This allows desktop users to select the most suitable and fitting desktop environment based on their computing requirements.A
 How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AM
How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AMLibreOffice stands out as a robust and open-source office suite, tailored for Linux, Windows, and Mac platforms. It boasts an array of advanced features for handling word documents, spreadsheets, presentations, drawings, calculations, and mathematica
 How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AM
How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AMLinux users who manage PDF files have a wide array of programs at their disposal. Specifically, there are numerous specialized PDF tools designed for various functions.For instance, you might opt to install a PDF viewer for reading files or a PDF edi
 How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AM
How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AMIn the earlier segments of the Awk command series, our focus was primarily on reading input from files. However, what if you need to read input from STDIN?In Part 7 of the Awk series, we will explore several examples where you can use the output of o
 Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AM
Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AMClifm stands out as a distinctive and incredibly swift command-line file manager, designed on the foundation of a shell-like interface. This means that users can engage with their file system using commands they are already familiar with.The choice o
 How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AM
How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AMIf you prefer not to perform a new installation of Linux Mint 22 Wilma, you have the option to upgrade from a previous version.In this guide, we will detail the process to upgrade from Linux Mint 21.3 (the most recent minor release of the 21.x series


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.






