How to delete thumbs.db file?
In our daily use of computers, in some cases we may encounter an unfamiliar file: thumbs.db. Many friends want to delete it because they don't know what this component is. So as far as the editor knows, this file is a file responsible for Microsoft system thumbnails, and we don’t need to delete it. If you must delete it, let’s take a look at how the editor did it~ I hope it can help you.
What is thumbs.db
1. Thumbs.db is a file used by Microsoft Windows systems to cache Windows Explorer thumbnails.
2. Thumbs.db is saved in every directory containing pictures or photos.
3. The Thumbs.db file can cache image file formats including: jpeg, bmp, gif, tif, pdf and htm.
4. The Thumbs.db file is a database that stores the thumbnails of all image files in this directory (the format is jpeg).
5. When viewing as a thumbnail (displaying a picture or movie film), a Thumbs.db file will be generated.
6. Thumbs.db is not a virus, but a database file. It can generally be found in a folder with pictures,
and its size increases with the number of pictures in the folder. increase by increasing.
Thumbs.db deletion steps:
1. Press win r to enter the run window and enter gpedit.msc.

2. In the Local Group Policy Editor window, click on User Configuration - Administrative Templates - Windows Components, and then Find and open the file manager on the right

3. Find and open the thumbnail cache in the hidden thumbs.db file

4. In the window, click Enabled-Apply-OK.
The above is the detailed content of How to delete thumbs.db file?. For more information, please follow other related articles on the PHP Chinese website!
 6 Tasks You Should Do Regularly on Your Windows ComputerApr 19, 2025 am 03:01 AM
6 Tasks You Should Do Regularly on Your Windows ComputerApr 19, 2025 am 03:01 AMMaintaining a Windows computer requires regular upkeep to ensure smooth operation and prevent performance issues, security risks, and unnoticed hardware problems. Here's a routine maintenance checklist to keep your computer running smoothly: 1. Run
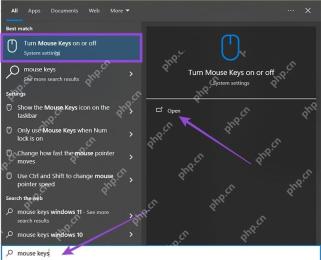 How to Right-Click With No MouseApr 18, 2025 pm 12:03 PM
How to Right-Click With No MouseApr 18, 2025 pm 12:03 PMThe mouse is a vital component to getting work done on your PC. But when you’re stuck with a faulty mouse, you can run into a few problems including the inability to right-click. But the good news is that there are definitely ways t
 5 Mistakes That Can Ruin Your Windows ExperienceApr 18, 2025 am 06:01 AM
5 Mistakes That Can Ruin Your Windows ExperienceApr 18, 2025 am 06:01 AMMaintaining a clean and efficient Windows experience is crucial for optimal performance. Here are some common pitfalls to avoid: 1. Overloading Startup Apps: Too many startup applications significantly slow down boot times and overall system perfor
 Your Keyboard Needs a Big Ol' Volume KnobApr 18, 2025 am 03:04 AM
Your Keyboard Needs a Big Ol' Volume KnobApr 18, 2025 am 03:04 AMIn today's touchscreen world, the satisfying tactile feedback of physical controls is a welcome change. That's why a keyboard with a large volume knob is surprisingly appealing. I recently experienced this firsthand, and it's been a revelation. For
 Windows 11 Will Let You Copy Any Text on Your ScreenApr 18, 2025 am 03:01 AM
Windows 11 Will Let You Copy Any Text on Your ScreenApr 18, 2025 am 03:01 AMWindows 11 Snipping Tool Gains Powerful New OCR Feature: Say Goodbye to Manual Text Selection! Windows 11's Snipping Tool just received a major upgrade, adding Optical Character Recognition (OCR) capabilities. This allows users to select text from v
 How and Why to Change Default File Explorer FolderApr 17, 2025 pm 10:01 PM
How and Why to Change Default File Explorer FolderApr 17, 2025 pm 10:01 PMThis guide explains how to change the default opening location of File Explorer in Windows 11 and 10. The default "Home" view, while convenient for some, may compromise privacy or workflow efficiency. This tutorial offers three methods to
 This Acer Desktop PC Has Laptop Specs, For Some ReasonApr 17, 2025 am 06:03 AM
This Acer Desktop PC Has Laptop Specs, For Some ReasonApr 17, 2025 am 06:03 AMAcer's latest gaming laptop series is stunning, but the company has also launched a desktop computer that is awkward in Acer's product line and has its own advantages and disadvantages compared to other small desktop computers. Acer today added four new laptops and a redesigned compact desktop to its popular Nitro gaming lineup. However, let's talk about desktop computers first, because it's the most unique. What makes it unique is that it uses laptop specifications. The Nitro 20 N20-100 uses an AMD Ryzen AI 9 365 processor, or the Intel Core i5-13420H desktop processor is also available. Graphics card can be equipped with up to
 This Limited-Edition 'DOOM' Release Comes In a Box That Runs 'DOOM'Apr 17, 2025 am 06:02 AM
This Limited-Edition 'DOOM' Release Comes In a Box That Runs 'DOOM'Apr 17, 2025 am 06:02 AMLimited Run Games is releasing a limited-edition DOOM DOOM II: Will It Run Edition box set, a playful nod to the enduring "Can it run DOOM?" meme. This extravagant set includes remastered versions of the first two DOOM games, playable ac


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.

WebStorm Mac version
Useful JavaScript development tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.






