Cybersecurity will be revolutionized by machine learning operations
Machine Learning Operations (MLOps) refers to the practices and tools used to simplify the deployment, management, and monitoring of machine learning models in production environments.
While MLOps is typically associated with data science and machine learning workflows, its integration with cybersecurity brings new capabilities for detecting and responding to threats in real-time. It involves simplifying the deployment and management of machine learning models, enabling organizations to gain insights from large amounts of data and improve their overall security posture.

Definition MLOps
MLOps is a relatively new field that combines machine learning and software engineering. It focuses on developing and deploying machine learning services in a more efficient and automated way. This enables organizations to accelerate the use of machine learning in their security programs, improve detection and response times, and ultimately reduce risk.
Collaboration
MLOps requires collaboration between data scientists, developers, and operations teams. Together they manage the entire machine learning lifecycle from data preparation to model deployment.
Automation
Automation is the core of MLOps. By automating model training, deployment, and management, organizations can deploy models faster and reduce errors
Scalability
MLOps helps organizations scale machine learning across multiple teams and projects application, making it easier to manage and maintain machine learning models
There are many benefits to using MLOps in cybersecurity
MLOps enables organizations to run faster and more efficiently than ever Accurately detect and respond to threats, potentially changing the game for cybersecurity. Machine learning models can help organizations detect and respond to cyber threats faster and more accurately than traditional methods. Additionally, MLOps tools can help organizations manage and maintain machine learning models at scale, thereby improving their overall security posture.
There are several benefits of using MLOps in cybersecurity:
- Faster detection and response times: MLOps enables organizations to detect and respond faster and more accurately than traditional methods threaten.
- Improving accuracy: Machine learning models can analyze large amounts of data and identify patterns that are difficult or impossible for humans to detect.
- Improve efficiency: By automating machine learning processes, MLOps helps organizations accelerate time to market for new models and save costs associated with manual processes.
Here are some real-world examples:
- A South African fintech company uses MLOps to detect and defend against online banking fraud
- Cloud security solution Provider uses MLOps to identify and contain cloud-based security threats
- U.S. government agencies use MLOps for airport security threat detection.
Challenges When Integrating MLOps into Cybersecurity
While MLOps has many benefits, there are still many challenges that need to be faced when integrating it into an organization’s cybersecurity practices Challenges:
- Lack of expertise: Training and hiring data scientists and machine learning engineers can be challenging, especially for organizations with limited budgets.
- Data quality: Machine learning models rely on large amounts of data to accurately detect threats. Ensuring the quality of this data can be difficult, especially when dealing with unstructured data sources.
- Model Transparency: The complexity of machine learning models can make model interpretation and transparency difficult, making it difficult to identify false positives and negatives and hold the model accountable.
MLOps and the future of cybersecurity
The role of MLOps in cybersecurity will continue to grow in the coming years. As machine learning technology advances and organizations become more data-driven, MLOps is expected to become an important part of every organization’s cybersecurity toolkit.
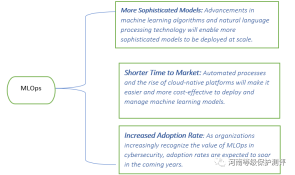
In the real world of cybersecurity, MLOps are expected to evolve as new concepts and methodologies are developed to enhance threat detection, Incident response and overall security operations. Here are some future MLOps concepts specific to cybersecurity
Adaptive and self-learning security systems
The future of MLOps concepts will focus on developing adaptive and self-learning security systems to cope with constant changes threats. These systems will leverage continuous learning technology to update their models in real time based on new threat intelligence and attack patterns to proactively defend and quickly respond to emerging cyber threats
zero-day threat detection
rewritten What: Zero-day threats are vulnerabilities or attack vectors unknown to the security community. Future MLOps concepts will explore advanced machine learning algorithms and techniques to detect and mitigate zero-day threats. By analyzing network traffic, system behavior and anomaly detection, machine learning models can identify unknown patterns and suspicious activity associated with zero-day attacks
Behavior-based anomaly detection
MLOps will continue to improve and advance behavior-based anomaly detection technology. Machine learning models will be trained to understand normal patterns of user and system behavior and identify deviations that may indicate malicious activity. These models will be integrated into security systems to provide real-time alerts and responses to anomalous behavior.
Threat Hunting and Intelligence-Driven Defense
MLOps will leverage advanced threat hunting technology to proactively search for potential threats and vulnerabilities within an organization’s networks and systems. Machine learning models will analyze large amounts of data, including log files, network traffic, and threat intelligence feeds, to identify hidden threats, suspicious activity, and potential attack vectors.
Real-time Threat Intelligence Analysis
MLOps will focus on enhancing the capabilities of threat intelligence analysis by leveraging machine learning models. These models will process and analyze real-time threat intelligence data from a variety of sources, including open source intelligence, dark web surveillance, and security sources. By integrating these models into security systems, organizations can more effectively identify and respond to emerging threats.
Adaptive and resilient defense mechanisms
Future concepts for MLOps will focus on developing adaptive and resilient defense mechanisms that can dynamically adjust security controls based on real-time threat intelligence. Machine learning models will continuously monitor and analyze security events, system vulnerabilities and attack patterns to optimize security configurations, deploy policies and respond to threats in real time
Enhanced User and Entity Behavior Analysis (UEBA)
UEBA systems leverage machine learning models to detect and respond to anomalous user and entity behavior that may indicate insider threats or account compromise. Future MLOps concepts will focus on improving the accuracy and effectiveness of UEBA systems through advanced machine learning algorithms, improved feature engineering, and integration with other security systems to enable comprehensive threat detection and response
These future concepts in cybersecurity within MLOps are designed to strengthen defenses against complex and ever-changing cyber threats, enabling organizations to detect, respond, and mitigate security incidents in a more proactive and efficient manner.
The important role of machine learning
MLOps is a powerful framework that can significantly enhance cybersecurity defenses. By leveraging the power of machine learning models, organizations can improve threat detection, real-time monitoring, malware analysis, and user behavior analysis. MLOps enable security teams to respond quickly to emerging threats, reduce the likelihood of data breaches and minimize the impact of cyberattacks.
As the cybersecurity landscape continues to evolve, the integration of MLOps will play a vital role in protecting our digital ecosystem.
The above is the detailed content of Cybersecurity will be revolutionized by machine learning operations. For more information, please follow other related articles on the PHP Chinese website!
 You Must Build Workplace AI Behind A Veil Of IgnoranceApr 29, 2025 am 11:15 AM
You Must Build Workplace AI Behind A Veil Of IgnoranceApr 29, 2025 am 11:15 AMIn John Rawls' seminal 1971 book The Theory of Justice, he proposed a thought experiment that we should take as the core of today's AI design and use decision-making: the veil of ignorance. This philosophy provides a simple tool for understanding equity and also provides a blueprint for leaders to use this understanding to design and implement AI equitably. Imagine that you are making rules for a new society. But there is a premise: you don’t know in advance what role you will play in this society. You may end up being rich or poor, healthy or disabled, belonging to a majority or marginal minority. Operating under this "veil of ignorance" prevents rule makers from making decisions that benefit themselves. On the contrary, people will be more motivated to formulate public
 Decisions, Decisions… Next Steps For Practical Applied AIApr 29, 2025 am 11:14 AM
Decisions, Decisions… Next Steps For Practical Applied AIApr 29, 2025 am 11:14 AMNumerous companies specialize in robotic process automation (RPA), offering bots to automate repetitive tasks—UiPath, Automation Anywhere, Blue Prism, and others. Meanwhile, process mining, orchestration, and intelligent document processing speciali
 The Agents Are Coming – More On What We Will Do Next To AI PartnersApr 29, 2025 am 11:13 AM
The Agents Are Coming – More On What We Will Do Next To AI PartnersApr 29, 2025 am 11:13 AMThe future of AI is moving beyond simple word prediction and conversational simulation; AI agents are emerging, capable of independent action and task completion. This shift is already evident in tools like Anthropic's Claude. AI Agents: Research a
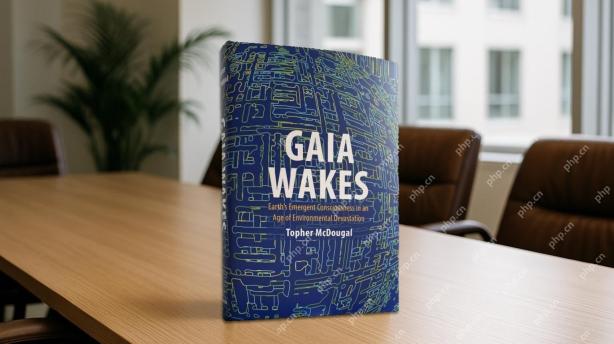 Why Empathy Is More Important Than Control For Leaders In An AI-Driven FutureApr 29, 2025 am 11:12 AM
Why Empathy Is More Important Than Control For Leaders In An AI-Driven FutureApr 29, 2025 am 11:12 AMRapid technological advancements necessitate a forward-looking perspective on the future of work. What happens when AI transcends mere productivity enhancement and begins shaping our societal structures? Topher McDougal's upcoming book, Gaia Wakes:
 AI For Product Classification: Can Machines Master Tax Law?Apr 29, 2025 am 11:11 AM
AI For Product Classification: Can Machines Master Tax Law?Apr 29, 2025 am 11:11 AMProduct classification, often involving complex codes like "HS 8471.30" from systems such as the Harmonized System (HS), is crucial for international trade and domestic sales. These codes ensure correct tax application, impacting every inv
 Could Data Center Demand Spark A Climate Tech Rebound?Apr 29, 2025 am 11:10 AM
Could Data Center Demand Spark A Climate Tech Rebound?Apr 29, 2025 am 11:10 AMThe future of energy consumption in data centers and climate technology investment This article explores the surge in energy consumption in AI-driven data centers and its impact on climate change, and analyzes innovative solutions and policy recommendations to address this challenge. Challenges of energy demand: Large and ultra-large-scale data centers consume huge power, comparable to the sum of hundreds of thousands of ordinary North American families, and emerging AI ultra-large-scale centers consume dozens of times more power than this. In the first eight months of 2024, Microsoft, Meta, Google and Amazon have invested approximately US$125 billion in the construction and operation of AI data centers (JP Morgan, 2024) (Table 1). Growing energy demand is both a challenge and an opportunity. According to Canary Media, the looming electricity
 AI And Hollywood's Next Golden AgeApr 29, 2025 am 11:09 AM
AI And Hollywood's Next Golden AgeApr 29, 2025 am 11:09 AMGenerative AI is revolutionizing film and television production. Luma's Ray 2 model, as well as Runway's Gen-4, OpenAI's Sora, Google's Veo and other new models, are improving the quality of generated videos at an unprecedented speed. These models can easily create complex special effects and realistic scenes, even short video clips and camera-perceived motion effects have been achieved. While the manipulation and consistency of these tools still need to be improved, the speed of progress is amazing. Generative video is becoming an independent medium. Some models are good at animation production, while others are good at live-action images. It is worth noting that Adobe's Firefly and Moonvalley's Ma
 Is ChatGPT Slowly Becoming AI's Biggest Yes-Man?Apr 29, 2025 am 11:08 AM
Is ChatGPT Slowly Becoming AI's Biggest Yes-Man?Apr 29, 2025 am 11:08 AMChatGPT user experience declines: is it a model degradation or user expectations? Recently, a large number of ChatGPT paid users have complained about their performance degradation, which has attracted widespread attention. Users reported slower responses to models, shorter answers, lack of help, and even more hallucinations. Some users expressed dissatisfaction on social media, pointing out that ChatGPT has become “too flattering” and tends to verify user views rather than provide critical feedback. This not only affects the user experience, but also brings actual losses to corporate customers, such as reduced productivity and waste of computing resources. Evidence of performance degradation Many users have reported significant degradation in ChatGPT performance, especially in older models such as GPT-4 (which will soon be discontinued from service at the end of this month). this


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

WebStorm Mac version
Useful JavaScript development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

Dreamweaver CS6
Visual web development tools

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.







