 Technology peripherals
Technology peripherals AI
AI Internet of Things 'botnet DDos attacks' are growing alarmingly, threatening global telecommunications networks
Internet of Things 'botnet DDos attacks' are growing alarmingly, threatening global telecommunications networksInternet of Things 'botnet DDos attacks' are growing alarmingly, threatening global telecommunications networks
Recently, as Nokia’s 2023 Threat Intelligence Report reveals, a surge in malicious activity was first observed during the Russia-Ukraine conflict and has now spread to various regions around the world.
In addition to the increase in botnet-driven DDoS attacks, the threat intelligence report also highlights that the number of Trojans targeting personal banking information on mobile devices has doubled and now accounts for 9% of all infections.
A recent report released by the Nokia Threat Intelligence Center shows an alarming increase in IoT botnet DDoS attacks targeting telecommunications networks around the world. The study shows that such attacks have increased fivefold in the past year, with cybercriminals taking advantage of insecure IoT devices and profit-driven hacking collectives.
This surge in malicious activity, first observed during the Russia-Ukraine conflict, has now spread to various regions around the world, compromising critical infrastructure and services beyond telecommunications networks.
The escalation of DDoS attacks is driven hugely by the proliferation of IoT devices among consumers. The number of compromised IoT devices used in these attacks has surged from 200,000 to approximately 1 million and now accounts for more than 40% of all DDoS traffic.

The report highlights that the increase in attacks stems from an increasing number of profit-driven hacking groups taking advantage of the Ukraine crisis.
A popular form of malware in telecom networks is bot malware, which scans for vulnerable devices – a tactic associated with multiple IoT botnets. With lax security measures prevalent in billions of IoT devices around the world, including everything from smart refrigerators to medical sensors and smartwatches, cybercriminals have found ample targets to exploit.
In addition to the increase in botnet-driven DDoS attacks, the threat intelligence report also highlights that the number of Trojans targeting personal banking information on mobile devices has doubled and now accounts for 9% of all infections. This puts millions of users around the world at higher risk of having their financial and credit card details compromised. Trojan horses are malicious software code disguised as legitimate applications.
The report shows that the trend of malware infections in home networks is showing a downward trend, looking at it from a positive perspective. After peaking at 3% during the Covid-19 pandemic, the infection rate has dropped to 1.5%, close to the pre-pandemic level of 1%. This decrease has been driven by a decrease in malware activity targeting remote workers as people return to office environments.
The findings in the report are based on data collected from more than 200 million devices worldwide that leverage Nokia's NetGuard Endpoint Security product to monitor network traffic.
Canada’s Threat Intelligence Center, France’s Nokia Cyber Security Center, India’s Nokia Security Operations Center and Nokia Deepfield, which specializes in network analytics and DDoS security, contributed their expertise to compile this comprehensive report.
Speaking on the report’s findings, Nokia Senior Vice President of Business Applications Hamdy Farid emphasized the urgent need for robust security measures in 5G networks. Farid emphasized the importance of telecom-centric threat detection and response, as well as the importance of implementing rigorous security practices and awareness at all levels of the organization, including service providers, vendors and regulators.
The alarming surge in IoT botnet attacks is a wake-up call for the global telecommunications industry, requiring them to strengthen security measures and work closely to protect network integrity and ensure the safety of millions of users around the world.
Scan the QR code to enter the community and get the original report!
Wonderful recommendation
Ukrainian hackers shut down Russian bank service provider
2023.06.12
Zellis data breach has affected British Airways, BBC
2023.06.09
NASA website vulnerability that has not been fixed so far
2022 .06.08
Note: This article was compiled and reported by E Security. Please contact us for authorization and indicate the source for reprinting.
The above is the detailed content of Internet of Things 'botnet DDos attacks' are growing alarmingly, threatening global telecommunications networks. For more information, please follow other related articles on the PHP Chinese website!
 The AI Skills Gap Is Slowing Down Supply ChainsApr 26, 2025 am 11:13 AM
The AI Skills Gap Is Slowing Down Supply ChainsApr 26, 2025 am 11:13 AMThe term "AI-ready workforce" is frequently used, but what does it truly mean in the supply chain industry? According to Abe Eshkenazi, CEO of the Association for Supply Chain Management (ASCM), it signifies professionals capable of critic
 How One Company Is Quietly Working To Transform AI ForeverApr 26, 2025 am 11:12 AM
How One Company Is Quietly Working To Transform AI ForeverApr 26, 2025 am 11:12 AMThe decentralized AI revolution is quietly gaining momentum. This Friday in Austin, Texas, the Bittensor Endgame Summit marks a pivotal moment, transitioning decentralized AI (DeAI) from theory to practical application. Unlike the glitzy commercial
 Nvidia Releases NeMo Microservices To Streamline AI Agent DevelopmentApr 26, 2025 am 11:11 AM
Nvidia Releases NeMo Microservices To Streamline AI Agent DevelopmentApr 26, 2025 am 11:11 AMEnterprise AI faces data integration challenges The application of enterprise AI faces a major challenge: building systems that can maintain accuracy and practicality by continuously learning business data. NeMo microservices solve this problem by creating what Nvidia describes as "data flywheel", allowing AI systems to remain relevant through continuous exposure to enterprise information and user interaction. This newly launched toolkit contains five key microservices: NeMo Customizer handles fine-tuning of large language models with higher training throughput. NeMo Evaluator provides simplified evaluation of AI models for custom benchmarks. NeMo Guardrails implements security controls to maintain compliance and appropriateness
 AI Paints A New Picture For The Future Of Art And DesignApr 26, 2025 am 11:10 AM
AI Paints A New Picture For The Future Of Art And DesignApr 26, 2025 am 11:10 AMAI: The Future of Art and Design Artificial intelligence (AI) is changing the field of art and design in unprecedented ways, and its impact is no longer limited to amateurs, but more profoundly affecting professionals. Artwork and design schemes generated by AI are rapidly replacing traditional material images and designers in many transactional design activities such as advertising, social media image generation and web design. However, professional artists and designers also find the practical value of AI. They use AI as an auxiliary tool to explore new aesthetic possibilities, blend different styles, and create novel visual effects. AI helps artists and designers automate repetitive tasks, propose different design elements and provide creative input. AI supports style transfer, which is to apply a style of image
 How Zoom Is Revolutionizing Work With Agentic AI: From Meetings To MilestonesApr 26, 2025 am 11:09 AM
How Zoom Is Revolutionizing Work With Agentic AI: From Meetings To MilestonesApr 26, 2025 am 11:09 AMZoom, initially known for its video conferencing platform, is leading a workplace revolution with its innovative use of agentic AI. A recent conversation with Zoom's CTO, XD Huang, revealed the company's ambitious vision. Defining Agentic AI Huang d
 The Existential Threat To UniversitiesApr 26, 2025 am 11:08 AM
The Existential Threat To UniversitiesApr 26, 2025 am 11:08 AMWill AI revolutionize education? This question is prompting serious reflection among educators and stakeholders. The integration of AI into education presents both opportunities and challenges. As Matthew Lynch of The Tech Edvocate notes, universit
 The Prototype: American Scientists Are Looking For Jobs AbroadApr 26, 2025 am 11:07 AM
The Prototype: American Scientists Are Looking For Jobs AbroadApr 26, 2025 am 11:07 AMThe development of scientific research and technology in the United States may face challenges, perhaps due to budget cuts. According to Nature, the number of American scientists applying for overseas jobs increased by 32% from January to March 2025 compared with the same period in 2024. A previous poll showed that 75% of the researchers surveyed were considering searching for jobs in Europe and Canada. Hundreds of NIH and NSF grants have been terminated in the past few months, with NIH’s new grants down by about $2.3 billion this year, a drop of nearly one-third. The leaked budget proposal shows that the Trump administration is considering sharply cutting budgets for scientific institutions, with a possible reduction of up to 50%. The turmoil in the field of basic research has also affected one of the major advantages of the United States: attracting overseas talents. 35
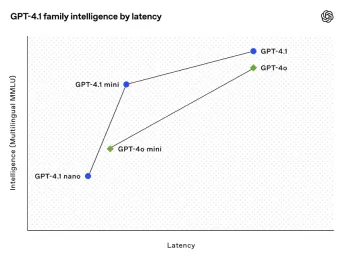 All About Open AI's Latest GPT 4.1 Family - Analytics VidhyaApr 26, 2025 am 10:19 AM
All About Open AI's Latest GPT 4.1 Family - Analytics VidhyaApr 26, 2025 am 10:19 AMOpenAI unveils the powerful GPT-4.1 series: a family of three advanced language models designed for real-world applications. This significant leap forward offers faster response times, enhanced comprehension, and drastically reduced costs compared t


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

WebStorm Mac version
Useful JavaScript development tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

SublimeText3 English version
Recommended: Win version, supports code prompts!





