Home >Operation and Maintenance >Safety >How to reproduce the RCE vulnerability of unauthorized access to the XXL-JOB API interface
How to reproduce the RCE vulnerability of unauthorized access to the XXL-JOB API interface
- WBOYWBOYWBOYWBOYWBOYWBOYWBOYWBOYWBOYWBOYWBOYWBOYWBforward
- 2023-05-12 09:37:055451browse
XXL-JOB Description
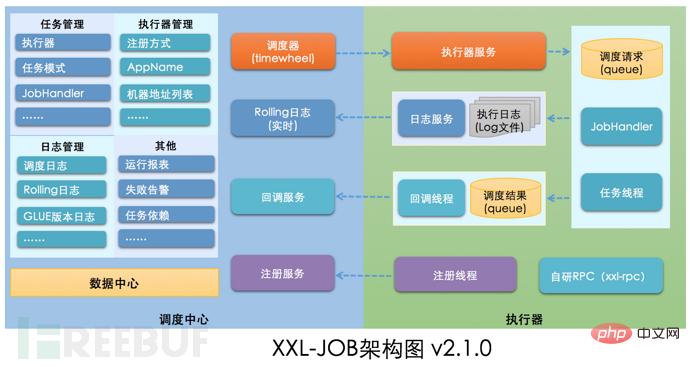
XXL-JOB is a lightweight distributed task scheduling platform. Its core design goals are rapid development, easy learning, lightweight, and easy expansion. The source code is now open and connected to the online product lines of many companies, ready to use out of the box.
1. Vulnerability details
The core issue of this vulnerability is GLUE mode. XXL-JOB supports multi-language and script tasks through "GLUE mode". The task features of this mode are as follows:
● Multi-language support: supports Java, Shell, Python, NodeJS, PHP, PowerShell...etc. type.
● Web IDE: Tasks are maintained in the dispatch center in source code form and support online development and maintenance through Web IDE.
● Dynamic effect: The task code developed by the user online through the Web IDE is pushed to the executor remotely and loaded in real time for execution.
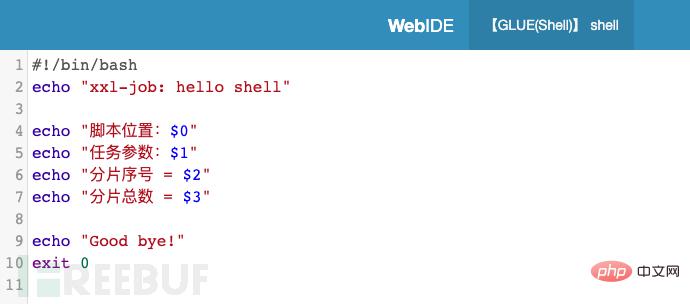
#As shown in the figure above, if you write attack code in the GLUE mode task code and push it to the executor for execution, you can cause remote attacks.
[Vulnerability Description]
The Restful API interface or RPC interface of XXL-JOB is not configured with authentication measures. Unauthorized attackers can construct malicious requests and cause remote execution. Command
[Vulnerability Rating]
High Risk
[Affected Version]
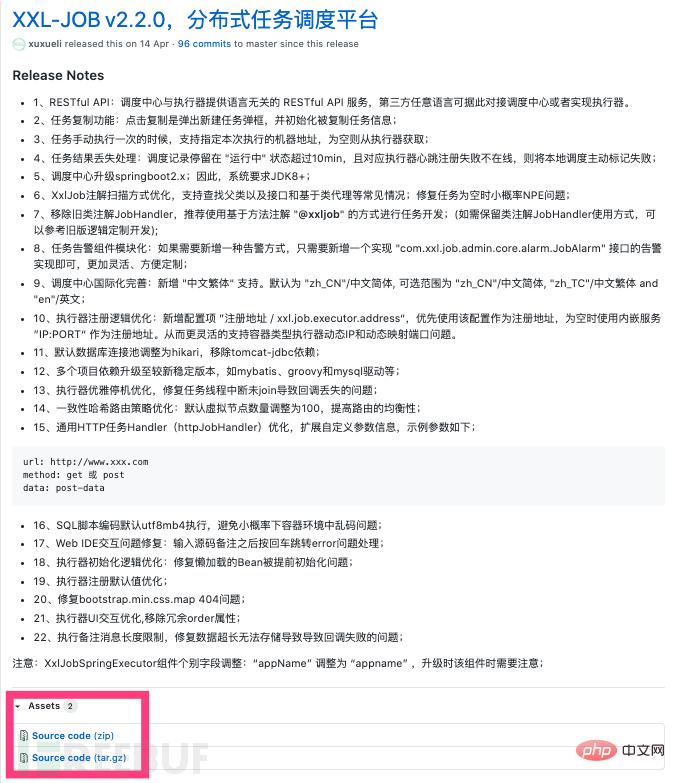
XXL-JOB <= 2.2.0
2. Environment setup
Overall idea: Source code download->Maven installation dependencies->Configuration and deployment "Scheduling Center"- >Configure deployment "executor project"->Complete deployment
Local development environment: Java8 Maven3.6
1. Github download source code
Address: https: //github.com/xuxueli/xxl-job/releases/tag/v2.2.0
2. Maven downloads the required dependencies
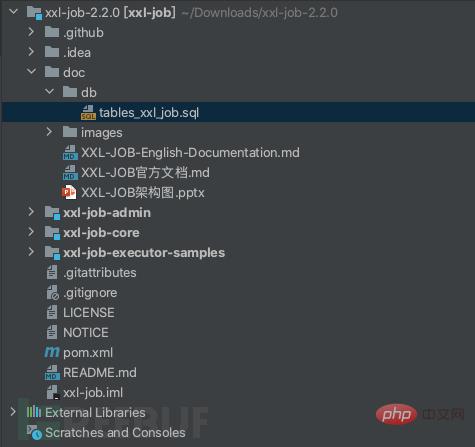
Idea opens the decompressed source code and automatically installs the relevant dependencies in the pom. You can also use the maven command in the terminal to download the required dependencies
3. Database configuration
The location of the scheduling database initialization SQL script is:
/xxl-job/doc/db/tables_xxl_job.sql
Because the local To install mysql, use docker to install it.
a) docker pull mysql:5.7
b) sudo docker run -p 3306:3306 --name mysql -e MYSQL_ROOT_PASSWORD=123456 -d mysql:5.7
This way We started the mysql container, the account is root, the password is 123456
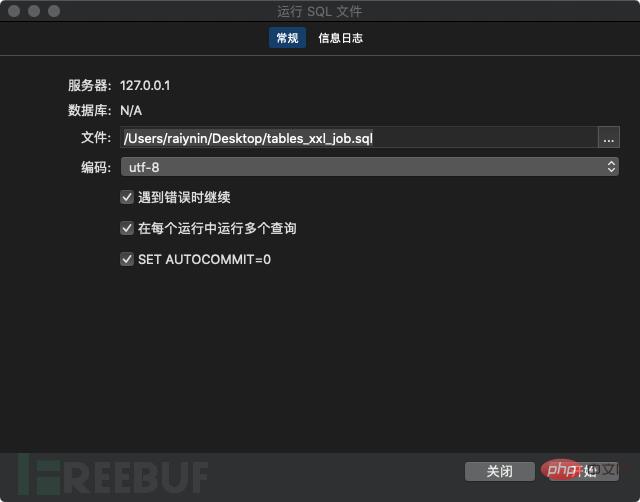
Use navicat to connect to the database
 You can click on the lower left corner to complete the test connection. Right-click the imported database, select Run SQL file, and click Start to complete the database import.
You can click on the lower left corner to complete the test connection. Right-click the imported database, select Run SQL file, and click Start to complete the database import.
4. Configure and deploy the "Scheduling Center"
Scheduling center project: xxl-job-admin
Function: Unified management of scheduling tasks on the task scheduling platform, responsible for triggering scheduling execution, and providing a task management platform. You can modify the database configuration in application.properties according to the actual situation
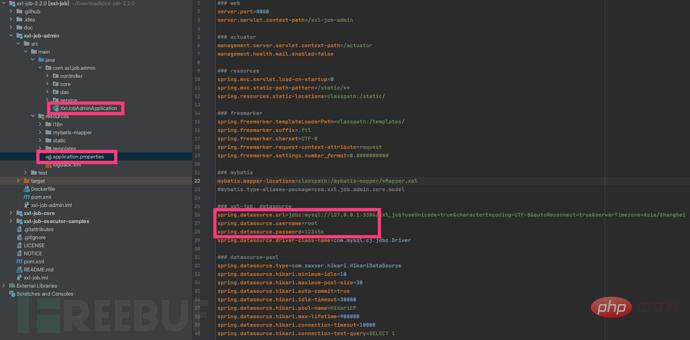
Execute XxlJobAdminApplication to start the dispatch center
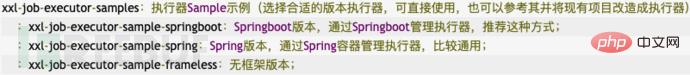 We use the recommended Springboot to manage execution Check the configuration file and find the xxl.job.executor.logpath parameter. We can create or modify the path to prevent problems with program execution. The data path does not exist in the new Mac system. It was found that using mkdir to create the path failed. This is because Sip is turned off in the Mac system. Use sudo mount -uw / to remove Sip restrictions. Run XxlJobExecutorApplication to start the executor. Open //localhost:8080/ in the browser and see the login interface. Make sure the startup is successful. The default login account is "admin/123456"
We use the recommended Springboot to manage execution Check the configuration file and find the xxl.job.executor.logpath parameter. We can create or modify the path to prevent problems with program execution. The data path does not exist in the new Mac system. It was found that using mkdir to create the path failed. This is because Sip is turned off in the Mac system. Use sudo mount -uw / to remove Sip restrictions. Run XxlJobExecutorApplication to start the executor. Open //localhost:8080/ in the browser and see the login interface. Make sure the startup is successful. The default login account is "admin/123456"
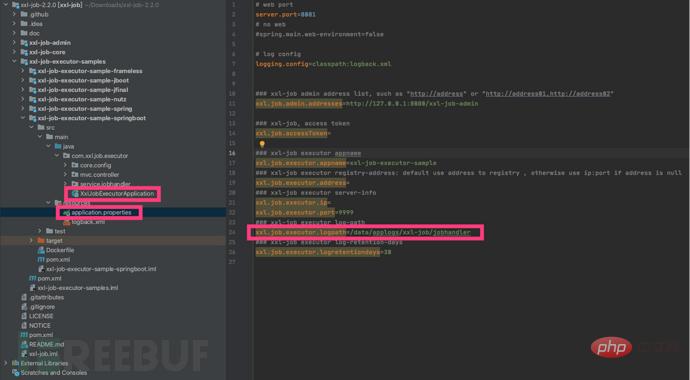
 It is recommended to create /data/applogs/xxl-job first, and use this path for many configuration files in the program
It is recommended to create /data/applogs/xxl-job first, and use this path for many configuration files in the program
Modify the dispatch center database configuration
Linux/Unix can use lsof to check the port occupancy , to prevent startup failure
The dispatch center and the executor can be deployed separately according to the actual situation
3. Vulnerability recurrence
View the official documentation and you can see the task triggered in the executor RESTful API Interface description
 The task running modes are as follows
The task running modes are as follows
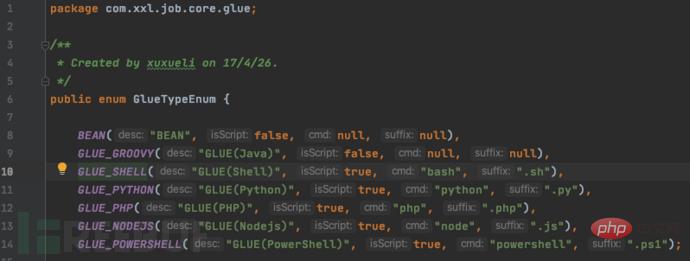
 View GulueTypeEnum source code
View GulueTypeEnum source code
 So we use Burpsuite to construct our POC
So we use Burpsuite to construct our POC
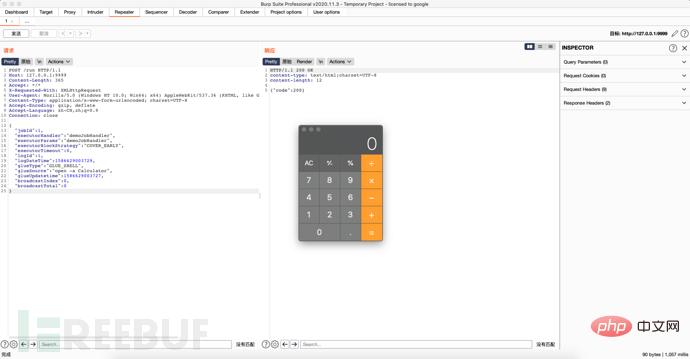
Tips:
When modifying glueSource, if the execution does not take effect, please modify the jobId
When restarting the project, it is found that the port startup exception is , please close BurpSuite
Since the official version of XXL-JOB comes with its own authentication component, it can ensure the security of the underlying communication of the system when turned on. The author of XXL-JOB stated that under normal circumstances, the underlying communication between the dispatch center and the executor is safe, and there is no remote command vulnerability. However, if the access token is not enabled on the executor, illegal scheduling requests cannot be identified and intercepted. Malicious requesters can use GLUE mode to push malicious attack code to achieve remote attacks. Therefore, the author of XXL-JOB believes that this problem is not a "vulnerability" in nature. The official website version provides an authentication component, which can be turned on for protection.
4. Repair suggestions
1. Turn on the authentication component that comes with XXL-JOB: Search for "xxl.job.accessToken" in the official documentation and follow the documentation instructions Just enable it.
2. Port access restrictions: By configuring security group restrictions, only specified IPs can access the port
The above is the detailed content of How to reproduce the RCE vulnerability of unauthorized access to the XXL-JOB API interface. For more information, please follow other related articles on the PHP Chinese website!

