
1. Definition
Data transmission security is the safe management of data transmission over the network. This is an important stage of data security and also Data security incidents, such as data leakage, theft, and tampering, occur frequently, so the importance of this stage is self-evident.
This process contains four process areas, namely: data transmission encryption and network availability management.
1.1 Data transmission encryption
The official description is to adopt appropriate encryption protection measures according to the internal and external data transmission requirements of the organization to ensure that transmission channels, transmission nodes and The security of transmitted data prevents data leakage caused by interception of data during transmission.
When data is transmitted through untrusted or low-security networks, security risks such as data theft, forgery, and tampering are prone to occur. Therefore, relevant security protection measures need to be established to ensure that data is transmitted during the transmission process. security, and encryption is a common means to ensure data security.
The DSMM standard requires the following at the fully defined level:
Organizational construction
The organization has established positions and personnel to manage data encryption and key management. , responsible for the overall encryption principles and technical work, and the technical teams of each business are responsible for implementing data transmission encryption in specific scenarios.
The requirements of DSMM are almost the same. Each process area needs to designate a dedicated person and post to be responsible for the work and be competent for the work. In actual work, all process areas may have the same one or more people in this dimension, who can be appointed individually or explained in the corresponding system chapter.
System process:
Establish data transmission security management specifications and clarify data transmission security requirements (such as transmission channel encryption, data content encryption, signature verification, identity authentication, Data transmission interface security, etc.) to determine the scenarios where data transmission encryption is required.
Establish key management security specifications and clarify the processes and requirements for key generation, distribution, access, update, backup and destruction.
Technical tools:
There are technical solutions and tools for subject identity identification and authentication at both ends of the transmission channel.
There are technical solutions and tools for encrypting transmitted data, including uniformly deploying transmission channel encryption solutions for key data transmission channels (such as using TLS/SSL), and encrypting the content of transmitted data.
There are technical solutions and tools to detect the integrity of transmitted data and perform recovery control.
There are technical solutions and tools to review and monitor changes in data transmission security policies, and technical tools have been deployed to review and monitor protection measures such as channel security configuration, password algorithm configuration, and key management.
The established key management system provides functions such as data encryption and decryption, signature verification, etc., and implements secure management of the entire life cycle of keys (generation, storage, use, distribution, update, and destruction).
Personnel capabilities:
Understand the mainstream secure channel and trusted channel establishment solutions, identity identification and authentication technologies, data encryption algorithms and nationally recommended data encryption algorithms, Choose an appropriate data transmission security management method based on specific business scenarios.
The personnel responsible for this work understand the data encryption algorithm and can choose the appropriate encryption technology based on specific business scenarios.

#The following are the specific contents that should be paid attention to during the data transmission encryption process.
1. Establish data transmission security management specifications, clarify data transmission security requirements (such as transmission channel encryption, data content encryption, signature verification, identity authentication, data transmission interface security, etc.), and determine the need for data transmission encryption scene.
2. Scenarios that require encryption should be based on national laws and regulations, industry regulatory department requirements, and the confidentiality and integrity requirements of the unit's own business data. Content combined with data classification and grading usually includes but is not limited to system management data, identification information, important business data, important personal privacy and other data with high integrity and confidentiality requirements.
3. Since the implementation of encryption technology relies on keys, it is necessary to establish key management security specifications and a key management system to clarify the key generation, distribution, access, update, backup and destruction processes. . That is, what security level of data should be used, what encryption algorithm should be used (national encryption algorithm or international algorithm, symmetric encryption algorithm, asymmetric encryption algorithm or hash algorithm) and how many bits of strength key should be used, how long is the validity period of the key, and how Backup keys, how to delete keys, etc.
4. When selecting the encryption type and key strength, you need to consider the business type and network status, and selectively implement encryption to avoid impact on the business.
5. For those responsible for encryption policy configuration and key management, there must be an audit and supervision mechanism to ensure that the configuration and changes of their encryption algorithms are authorized and recognized. At present, bastion machines are usually used for supervision and management. .
1.2 Network availability management
The official description is to achieve high availability of the network through the backup construction of basic network links and key network equipment, thereby ensuring the reliability of the data transmission process. stability.
Data relies on the availability of the network during network transmission. Once a network failure or paralysis occurs, data transmission will be affected or even interrupted.
The DSMM standard requires the following at the fully defined level:
Institutional process:
The availability construction requirements of the network should be considered in the critical business network architecture, Implement redundant construction of key network transmission links and network equipment nodes.
Technical tools:
Deploy load balancing, anti-intrusion attack and other equipment to further strengthen the prevention of network availability risks
Personnel capabilities:
The personnel responsible for this work have network security management capabilities, understand the security requirements for availability in network security, and can formulate effective availability security protection plans based on the network performance requirements of different businesses.

The following are the specific contents that should be focused on during the data collection security management stage:
1. Transmission links and network equipment of key business networks Nodes are constructed redundantly. Including: hardware redundancy (power redundancy, engine redundancy, module redundancy, device stacking, link redundancy, device redundancy, load balancing), software redundancy (link bundling technology) and routing redundancy (VRRP, dynamic routing protocol).
2. Use security devices such as load balancing and anti-intrusion attacks to reduce network availability risks.
2. Summary
The data transmission security of DSMM is actually to ensure the security of the data transmission process from the front-end collection to the business processing system. The main goal is To achieve data confidentiality, tamper resistance and high availability, network security requirements are also based on data encryption and network redundancy.
Although many systems and technical tools are described separately in the article, they may be mixed together in actual work. At the same time, many specific implementation parts are not only applied in one process area or one life cycle stage. It can even be applied throughout the entire life cycle. For example, it requires encrypted storage and transmission of important or sensitive data, which applies to all stages of the life cycle.
The above is the detailed content of Detailed introduction to data transmission security of DSMM. For more information, please follow other related articles on the PHP Chinese website!
 两个iphone怎么传输所有数据 详细讲解:迁移旧手机数据 的方法Mar 18, 2024 pm 06:31 PM
两个iphone怎么传输所有数据 详细讲解:迁移旧手机数据 的方法Mar 18, 2024 pm 06:31 PM很多朋友朋友在更换苹果手机时,想把旧手机内的所有数据全部导入到新手机里,理论上是完全可行的,但在实际操作中是无法做到“转移所有”数据的,本期文章列举几种“转移部分数据”的方法。一、iTunesiTunes是苹果手机预装的软件,可用于迁移旧手机中的所有数据,但需要与电脑配合使用。可通过在电脑上安装iTunes,然后通过数据线连接手机和电脑,使用iTunes进行备份手机内的应用和数据,最后将备份恢复到新的苹果手机上来完成迁移。二、iCloudiCloud是苹果专属的“云空间”工具,可以先在旧手机内登
 React API调用指南:如何与后端API进行交互和数据传输Sep 26, 2023 am 10:19 AM
React API调用指南:如何与后端API进行交互和数据传输Sep 26, 2023 am 10:19 AMReactAPI调用指南:如何与后端API进行交互和数据传输概述:在现代的Web开发中,与后端API进行交互和数据传输是一个常见的需求。React作为一个流行的前端框架,提供了一些强大的工具和功能来简化这一过程。本文将介绍如何使用React来调用后端API,包括基本的GET和POST请求,并提供具体的代码示例。安装所需的依赖:首先,确保在项目中安装了Axi
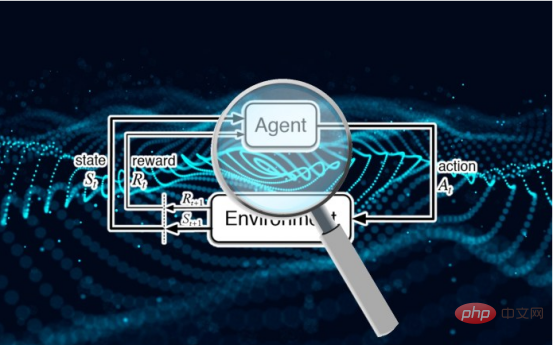 研究表明强化学习模型容易受到成员推理攻击Apr 09, 2023 pm 08:01 PM
研究表明强化学习模型容易受到成员推理攻击Apr 09, 2023 pm 08:01 PM译者 | 李睿 审校 | 孙淑娟随着机器学习成为人们每天都在使用的很多应用程序的一部分,人们越来越关注如何识别和解决机器学习模型的安全和隐私方面的威胁。 然而,不同机器学习范式面临的安全威胁各不相同,机器学习安全的某些领域仍未得到充分研究。尤其是强化学习算法的安全性近年来并未受到太多关注。 加拿大的麦吉尔大学、机器学习实验室(MILA)和滑铁卢大学的研究人员开展了一项新研究,主要侧重于深度强化学习算法的隐私威胁。研究人员提出了一个框架,用于测试强化学习模型对成员推理攻击的脆弱性。 研究
 Java API 开发中使用 Https 进行数据传输Jun 18, 2023 pm 10:43 PM
Java API 开发中使用 Https 进行数据传输Jun 18, 2023 pm 10:43 PM随着科技的发展,网络通信已经成为了现代社会信息传输的重要工具之一。但同时,网络上的信息传输面临着被恶意攻击和窃取的风险,因此安全性显得尤为重要。基于此,HTTPS协议就应运而生。它是在HTTP协议上加入SSL/TLS加密的方式来保证网络传输安全性的一种协议。Java作为一门广泛应用于网络开发的语言,自然也提供了丰富的API来支持HTTPS协议。本文将
 深入聊聊前端限制用户截图的脑洞Nov 07, 2022 pm 04:56 PM
深入聊聊前端限制用户截图的脑洞Nov 07, 2022 pm 04:56 PM做后台系统,或者版权比较重视的项目时,产品经常会提出这样的需求:能不能禁止用户截图?有经验的开发不会直接拒绝产品,而是进行引导。
 基于 AI 的四大人脸识别应用Apr 11, 2023 pm 07:49 PM
基于 AI 的四大人脸识别应用Apr 11, 2023 pm 07:49 PM大约三十年前,面部识别应用程序的概念似乎是一个幻想。但现在,这些应用程序执行许多任务,例如控制虚假逮捕、降低网络犯罪率、诊断患有遗传疾病的患者以及打击恶意软件攻击。2019 年全球脸型分析仪市场价值 32 亿美元,预计到 2024 年底将以 16.6% 的复合年增长率增长。人脸识别软件有增长趋势,这一领域将提升整个数字和技术领域。如果您打算开发一款脸型应用程序以保持竞争优势,这里有一些最好的人脸识别应用程序的简要列表。优秀的人脸识别应用列表Luxand:Luxand人脸识别不仅仅是一个应用程序;
 PHP trait DTO:优化数据传输过程的关键工具Oct 12, 2023 pm 02:33 PM
PHP trait DTO:优化数据传输过程的关键工具Oct 12, 2023 pm 02:33 PMPHPtraitDTO:优化数据传输过程的关键工具,需要具体代码示例概述:在PHP开发中,数据传输是一项非常常见的任务,例如将数据从控制器传递给视图、将数据从接口传递给前端等。然而,在传输数据的过程中,往往需要对数据进行处理、转换和封装,这可能会导致代码冗余和不易维护。为了解决这个问题,我们可以使用PHPtraitDTO(DataTransfer
 PHP trait DTO:优化数据传输过程的关键利器Oct 12, 2023 pm 03:10 PM
PHP trait DTO:优化数据传输过程的关键利器Oct 12, 2023 pm 03:10 PMPHPtraitDTO:优化数据传输过程的关键利器,需要具体代码示例简介:在开发过程中,数据传输是一个非常常见的需求,尤其是在不同层级之间传递数据时。在传输这些数据过程中,我们常常需要对数据进行处理、验证或者转换,以满足不同的业务需求。为了提高代码的可读性和可维护性,我们可以使用PHPtraitDTO(DataTransferObject)来优化


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 English version
Recommended: Win version, supports code prompts!

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

Zend Studio 13.0.1
Powerful PHP integrated development environment

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),






