This article is reprinted from the WeChat public account "Living in the Information Age". The author lives in the information age. To reprint this article, please contact the Living in the Information Age public account.
Convolutional Neural Network (CNN) is a special deep feed-forward network, which generally includes a data input layer, a convolution layer, an activation layer, and a downsampling layer. and fully connected layers.

The convolutional layer is an important unit in the convolutional neural network. It consists of a series of filtering data The essence of the convolution kernel is the linear superposition process of the weighted sum of the local area of the image and the weight of the convolution kernel. Image I is used as input, and a two-dimensional convolution kernel K is used for convolution. The convolution process can be expressed as:

Among them, I(i,j) is the value of the image at the position (i,j), and S(i,j) is the feature map obtained after the convolution operation.
The activation convolution operation is linear, can only perform linear mapping, and has limited expression ability. Therefore, to deal with nonlinear mapping problems, it is necessary to introduce a nonlinear activation function. To deal with different nonlinear problems, the activation functions introduced are also different. The commonly used ones are sigmoid, tanh, relu, etc.
The Sigmoid function expression is:

##The expression of Tanh function is:

Expression of Relu function The formula is:

The downsampling layer is also called the pooling layer, and is usually placed after several convolutional layers. to reduce the size of feature images. The pooling function uses the overall statistical characteristics of neighboring outputs at a certain position to replace the network's output at that position. Generally, the pooling layer has three functions: First, it reduces the feature dimension. The pooling operation is equivalent to another feature extraction process, which can remove redundant information and reduce the data processing volume of the next layer. The second is to prevent overfitting, and the pooling operation obtains more abstract information and improves generalization. The third is to maintain feature invariance, and the pooling operation retains the most important features.
The fully connected layer is usually placed at the end of the convolutional neural network, and all neurons between layers have weighted connections. The purpose is to map all the features learned in the network to the label space of the sample to make category judgments. The Softmax function is usually used in the last layer of the neural network as the output of the classifier. Each value output by the softmax function ranges between (0, 1).
There are some classic and efficient CNN models, such as: VGGNet, ResNet, AlexNet, etc., which have been widely used in the field of image recognition.
The above is the detailed content of Image Recognition: Convolutional Neural Network. For more information, please follow other related articles on the PHP Chinese website!
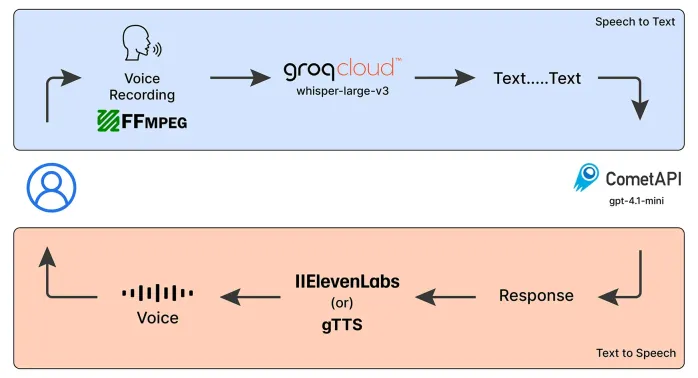 Emergency Operator Voice Chatbot: Empowering AssistanceMay 07, 2025 am 09:48 AM
Emergency Operator Voice Chatbot: Empowering AssistanceMay 07, 2025 am 09:48 AMLanguage models have been rapidly evolving in the world. Now, with Multimodal LLMs taking up the forefront of this Language Models race, it is important to understand how we can leverage the capabilities of these Multimodal model
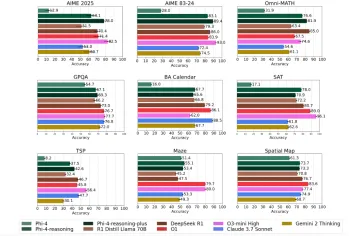 Microsoft's Phi-4 Reasoning Models Explained SimplyMay 07, 2025 am 09:45 AM
Microsoft's Phi-4 Reasoning Models Explained SimplyMay 07, 2025 am 09:45 AMMicrosoft isn’t like OpenAI, Google, and Meta; especially not when it comes to large language models. While other tech giants prefer to launch multiple models almost overwhelming the users with choices; Microsoft launches a few,
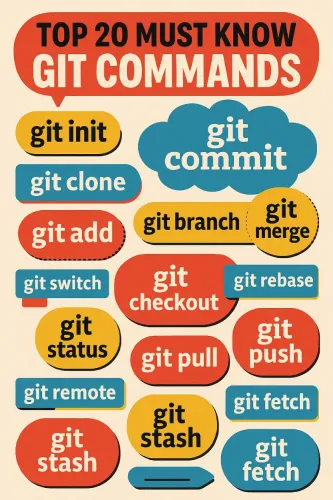 Top 20 Git Commands Every Developer Should Know - Analytics VidhyaMay 07, 2025 am 09:44 AM
Top 20 Git Commands Every Developer Should Know - Analytics VidhyaMay 07, 2025 am 09:44 AMGit can feel like a puzzle until you learn the key moves. In this guide, you’ll find the top 20 Git commands, ordered by how often they are used. Each entry starts with a quick “What it does” summary, followed by an image display
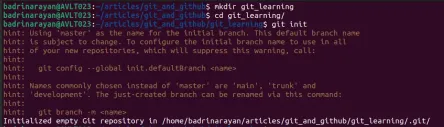 Git Tutorial for BeginnersMay 07, 2025 am 09:36 AM
Git Tutorial for BeginnersMay 07, 2025 am 09:36 AMIn software development, managing code across multiple contributors can get messy fast. Imagine several people editing the same document at the same time, each adding new ideas, fixing bugs, or tweaking features. Without a struct
 Top 5 PDF to Markdown Converter for Effortless Formatting - Analytics VidhyaMay 07, 2025 am 09:21 AM
Top 5 PDF to Markdown Converter for Effortless Formatting - Analytics VidhyaMay 07, 2025 am 09:21 AMDifferent formats, such as PPTX, DOCX, or PDF, to Markdown converter is an essential tool for content writers, developers, and documentation specialists. Having the right tools makes all the difference when converting any type of
 Qwen3 Models: How to Access, Features, Applications, and MoreMay 07, 2025 am 09:18 AM
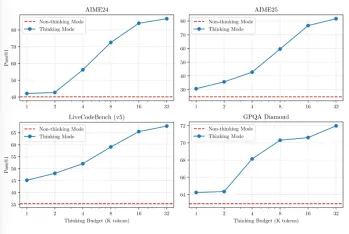
Qwen3 Models: How to Access, Features, Applications, and MoreMay 07, 2025 am 09:18 AMQwen has been silently adding one model after the other. Each of its models comes packed with features so big and sizes so quantized that they are just impossible to ignore. After QvQ, Qwen2.5-VL, and Qwen2.5-Omni this year, the
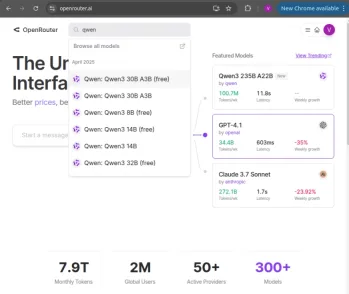 How to Build RAG Systems and AI Agents with Qwen3May 07, 2025 am 09:10 AM
How to Build RAG Systems and AI Agents with Qwen3May 07, 2025 am 09:10 AMQwen just released 8 new models as part of its latest family – Qwen3, showcasing promising capabilities. The flagship model, Qwen3-235B-A22B, outperformed most other models including DeepSeek-R1, OpenAI’s o1, o3-mini,
 Why Sam Altman And Others Are Now Using Vibes As A New Gauge For The Latest Progress In AIMay 06, 2025 am 11:12 AM
Why Sam Altman And Others Are Now Using Vibes As A New Gauge For The Latest Progress In AIMay 06, 2025 am 11:12 AMLet's discuss the rising use of "vibes" as an evaluation metric in the AI field. This analysis is part of my ongoing Forbes column on AI advancements, exploring complex aspects of AI development (see link here). Vibes in AI Assessment Tradi


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

SublimeText3 Chinese version
Chinese version, very easy to use

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software






