A brief discussion on file uploading methods for obtaining permissions
Overview
File upload vulnerabilities occur in applications with upload functions. If the application has no control over the user's uploaded files or has defects, an attacker can exploit the defects in the application's upload function to upload Trojans , viruses and other harmful files to the server and control the server.
Causes and hazards of the vulnerability
The main reason for the file upload vulnerability is that there is an upload function in the application, but the uploaded file has not undergone strict legality testing or the testing function is defective, resulting in Upload the Trojan file to the server. File upload vulnerabilities are extremely harmful because malicious code can be uploaded directly to the server, which may cause serious consequences such as tampering with the server's web page, hanging the website, remote controlling the server, and installing backdoors.
Below we will discuss several verification and bypass methods for file upload:
1. Local verification (front-end verification)
Front-end JS filtering bypasses the upload vulnerability because of the application The program is verified through JS code on the front end, rather than on the back end of the program. In this way, you can bypass upload filtering and upload Trojans by modifying the front-end JS code.
So how to judge whether it is front-end verification? Personally, I think we can check whether we can get the data packet when uploading and capturing the packet, whether there is data flowing through, or we can check whether the uploaded image page will display the uploaded image address, etc.
Bypass: Delete the filtering code, modify or disable Javascript.
2. Backend verification and bypass
Common verifications for file upload: suffix name (direct verification), file, file header (indirect verification).
2.1 Suffix name
2.1.1 Blacklist (script format suffixes that are explicitly not allowed to be uploaded)
The file name filtering bypass vulnerability is mainly Because the type of file upload is determined through the blacklist, and there is no complete filtering, attackers can upload files outside the blacklist type.
Blacklist judgment method: Upload files, the system prompts that uploading xxx format files is not allowed.
Bypass: Use other formats (php5, Phtml, php3) or file case, and you can also add some interference symbols to achieve bypass.
2.1.2 .htaccess (pseudo-static protocol) - rewrite analysis (only available in Apache and enable the pseudo-static module)
.htaccess file upload is done using .htaccess The file can configure the function of the Web server to realize the process of parsing files with suffixes such as jpg and png as PHP files.
.htaccess file (distributed configuration file) provides a way to make configuration changes on a per-directory basis. A file containing one or more configuration directives is placed in a specific document directory, and the The directive applies to this directory and all its subdirectories. .htaccess is a configuration file of the web server. You can use the .htaccess file to implement configurations such as the parsing method and redirection of the definition file in the web server.
Bypass method: First upload the 1.htaccess file. 2. Upload the picture again.
2.1.3 Space bypass
Bypass method: Add a space after the file suffix name in the data packet to achieve bypass.
2.1.4. Bypass
Bypass method: Similar to the space bypass method, add a . after the file suffix name in the data packet to achieve bypass.
2.1.5 ::$data bypass
This is a protocol unique to windows. In window, if the file name "::$DATA" will Treat the data after ::$DATA as a file stream, without checking the suffix name, and keep the file name before ::$DATA. Its purpose is not to check the suffix name.
2.1.6 Loop filtering
Bypass: The code replaces php in the string with nothing.
For example: a.pphphp will become ->a.
2.1.7 Whitelist: Clear the format suffix that can be uploaded (more secure)
3. File type verification
3.1 File header detection: file header content information (such as gif89a)
Different files have specific file header formats, and developers upload files by checking The file header detects the file type, but this detection method can also be bypassed. As long as the corresponding file header is added to the header of the Trojan file, this can bypass the detection without affecting the normal operation of the Trojan file.
Common file headers are as follows:
JPEG 0xFFD8FF
PNG0 x89504E470D0A1A0A
GIF 47 49 4638 39 61 (GIF89a)
Wrap Method:
- Change the header information to achieve deception. For example, adding the file header of an image file to the header file of the Trojan horse can bypass detection.
GIF89a
?>
- Make picture horse
Insert a sentence Trojan directly into the picture and upload it. ——Use the principle of file inclusion.
Use the cmd command to combine a normal picture 1.jpg and an a.txt file containing a one-sentence Trojan horse into a new test.php Trojan file.
cmd command: copy 1.jpg/b a.txt test.php.
3.2 Content-Type detection
Content-Type is used to define the type of network file and the encoding of the web page, and is used to tell the file receiver in what form and encoding it will read the file. Different files will correspond to different Content-Types. For example, the Content-Type of jpg files is image/jpeg, and the Content-Type of php files is application/octet-stream. Content-Type is in the request header of the data packet. Developers will use the Content-Type type to determine whether the file is allowed to be uploaded.
Bypass: The type of Content-Type can be tampered with through packet capture, so that the Content-Type of the data packet can be modified by capturing the packet to bypass the Content-Type judgment.
MIME: You can guess the file suffix name by judging the type, and use the packet capture tool to tamper with the Content-Type, such as changing it to image/pjpeg, image/jpeg, image/gif, image/png. One can bypass filtering.
4. Content and others
4.1 Logical safety: conditional competition (equivalent to system occupation)
Definition: Competition conditions refer to when multiple threads do not perform lock operations or Synchronous operations access the same shared code, variables, files, etc. at the same time. The results of the operation depend on the order in which different threads access data. First upload the file to the server, and the server selects whether to save or delete the image according to the rules. The vulnerability is that the file is not checked for legality before being saved to the server. Although the file is checked after saving, through the race condition vulnerability, the file is passed Upload a Trojan with the function of writing files, and access the uploaded Trojan before deleting it to write a new Trojan.
Bypass: After uploading the file to the server, we will continue to access the file path. Due to competing conditions, the purpose of uploading the Webshell will be achieved. The vulnerability is exploited by sending requests and continuously uploading content. Such access will Generate a new Trojan file and then send another request to continuously access this file. If the race condition exploit is successful, a new Trojan will be generated.
4.2 Directory naming
Bypass: Add the /. suffix to let the server recognize the file as a folder to achieve the purpose of uploading, such as -x.php/.
5. Other vulnerabilities
Script function vulnerability-cve
CVE-2017-12615
CVE-2015-5254
CVE-2019-2618
......
There are tutorials on how to exploit these vulnerabilities online. Interested masters can check the information.
6. Middleware parsing vulnerability
6.1 IIS 6.0 parsing vulnerability
Quickly judge the parsing vulnerability. Check /.php to see if there is any garbled code. If there is, it exists, if not, it does not exist. .
6.1.1 Execute as a folder
Normal file name: image/aa.jpg.
Bypass: image.asp/aa.jpg aa.jpg will be parsed as asp.
6.1.2 Execute as file
Normal file name: image.jpg.
Bypass: image.asp;.jpg or xxx.asp;xxx.jpg This file will be executed as asp.
asp can be changed to php. If you change php, it can be executed as php.
7.WAF Bypass
To bypass WAF, we need to know which parameters can be modified, such as:
- Content-Disposition: Generally can be modified.
- name: form parameter value, cannot be modified.
- filename: file name, can be modified.
- Content-Type (file’s own type): File MIME, change as appropriate.
- The core of waf bypass is to constantly modify the test after the parameter name that can be modified to try to bypass.
Common bypass methods:
7.1 Data overflow (junk data filling)
Use the WAF detection limit to add a large amount of junk data so that it cannot be matched. Similar to overflow vulnerabilities, interference data can generally be added after the upload parameters. Remember to add ; between the junk data and the parameters, otherwise the data packet will report an error.
7.2 Symbol mutation ('";)
Use program development vulnerabilities to replace, add, and delete symbols in the upload parameters in the data package to achieve the purpose of uploading. Such as
For example, x.jpg;.php The semicolon represents the end of a piece of data.
7.3 Data truncation (
The above is the detailed content of A brief discussion on file uploading methods for obtaining permissions. For more information, please follow other related articles on the PHP Chinese website!
 An easy-to-understand explanation of how to create a VBA macro in ChatGPT!May 14, 2025 am 02:40 AM
An easy-to-understand explanation of how to create a VBA macro in ChatGPT!May 14, 2025 am 02:40 AMFor beginners and those interested in business automation, writing VBA scripts, an extension to Microsoft Office, may find it difficult. However, ChatGPT makes it easy to streamline and automate business processes. This article explains in an easy-to-understand manner how to develop VBA scripts using ChatGPT. We will introduce in detail specific examples, from the basics of VBA to script implementation using ChatGPT integration, testing and debugging, and benefits and points to note. With the aim of improving programming skills and improving business efficiency,
 I can't use the ChatGPT plugin function! Explaining what to do in case of an errorMay 14, 2025 am 01:56 AM
I can't use the ChatGPT plugin function! Explaining what to do in case of an errorMay 14, 2025 am 01:56 AMChatGPT plugin cannot be used? This guide will help you solve your problem! Have you ever encountered a situation where the ChatGPT plugin is unavailable or suddenly fails? The ChatGPT plugin is a powerful tool to enhance the user experience, but sometimes it can fail. This article will analyze in detail the reasons why the ChatGPT plug-in cannot work properly and provide corresponding solutions. From user setup checks to server troubleshooting, we cover a variety of troubleshooting solutions to help you efficiently use plug-ins to complete daily tasks. OpenAI Deep Research, the latest AI agent released by OpenAI. For details, please click ⬇️ [ChatGPT] OpenAI Deep Research Detailed explanation:
 Does ChatGPT not follow the character count specification? A thorough explanation of how to deal with this!May 14, 2025 am 01:54 AM
Does ChatGPT not follow the character count specification? A thorough explanation of how to deal with this!May 14, 2025 am 01:54 AMWhen writing a sentence using ChatGPT, there are times when you want to specify the number of characters. However, it is difficult to accurately predict the length of sentences generated by AI, and it is not easy to match the specified number of characters. In this article, we will explain how to create a sentence with the number of characters in ChatGPT. We will introduce effective prompt writing, techniques for getting answers that suit your purpose, and teach you tips for dealing with character limits. In addition, we will explain why ChatGPT is not good at specifying the number of characters and how it works, as well as points to be careful about and countermeasures. This article
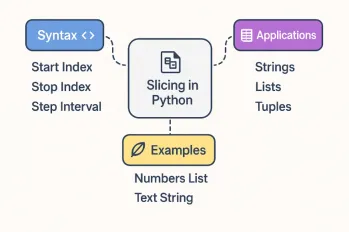 All About Slicing Operations in PythonMay 14, 2025 am 01:48 AM
All About Slicing Operations in PythonMay 14, 2025 am 01:48 AMFor every Python programmer, whether in the domain of data science and machine learning or software development, Python slicing operations are one of the most efficient, versatile, and powerful operations. Python slicing syntax a
 An easy-to-understand explanation of how to use ChatGPT to create quotes!May 14, 2025 am 01:44 AM
An easy-to-understand explanation of how to use ChatGPT to create quotes!May 14, 2025 am 01:44 AMThe evolution of AI technology has accelerated business efficiency. What's particularly attracting attention is the creation of estimates using AI. OpenAI's AI assistant, ChatGPT, contributes to improving the estimate creation process and improving accuracy. This article explains how to create a quote using ChatGPT. We will introduce efficiency improvements through collaboration with Excel VBA, specific examples of application to system development projects, benefits of AI implementation, and future prospects. Learn how to improve operational efficiency and productivity with ChatGPT. Op
 What is ChatGPT Pro (o1 Pro)? Explaining what you can do, the prices, and the differences between them from other plans!May 14, 2025 am 01:40 AM
What is ChatGPT Pro (o1 Pro)? Explaining what you can do, the prices, and the differences between them from other plans!May 14, 2025 am 01:40 AMOpenAI's latest subscription plan, ChatGPT Pro, provides advanced AI problem resolution! In December 2024, OpenAI announced its top-of-the-line plan, the ChatGPT Pro, which costs $200 a month. In this article, we will explain its features, particularly the performance of the "o1 pro mode" and new initiatives from OpenAI. This is a must-read for researchers, engineers, and professionals aiming to utilize advanced AI. ChatGPT Pro: Unleash advanced AI power ChatGPT Pro is the latest and most advanced product from OpenAI.
 We explain how to create and correct your motivation for applying using ChatGPT! Also introduce the promptMay 14, 2025 am 01:29 AM
We explain how to create and correct your motivation for applying using ChatGPT! Also introduce the promptMay 14, 2025 am 01:29 AMIt is well known that the importance of motivation for applying when looking for a job is well known, but I'm sure there are many job seekers who struggle to create it. In this article, we will introduce effective ways to create a motivation statement using the latest AI technology, ChatGPT. We will carefully explain the specific steps to complete your motivation, including the importance of self-analysis and corporate research, points to note when using AI, and how to match your experience and skills with company needs. Through this article, learn the skills to create compelling motivation and aim for successful job hunting! OpenAI's latest AI agent, "Open
 What's so amazing about ChatGPT? A thorough explanation of its features and strengths!May 14, 2025 am 01:26 AM
What's so amazing about ChatGPT? A thorough explanation of its features and strengths!May 14, 2025 am 01:26 AMChatGPT: Amazing Natural Language Processing AI and how to use it ChatGPT is an innovative natural language processing AI model developed by OpenAI. It is attracting attention around the world as an advanced tool that enables natural dialogue with humans and can be used in a variety of fields. Its excellent language comprehension, vast knowledge, learning ability and flexible operability have the potential to transform our lives and businesses. In this article, we will explain the main features of ChatGPT and specific examples of use, and explore the possibilities for the future that AI will unlock. Unraveling the possibilities and appeal of ChatGPT, and enjoying life and business


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

SublimeText3 Chinese version
Chinese version, very easy to use

WebStorm Mac version
Useful JavaScript development tools

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver Mac version
Visual web development tools







