How to solve redis cache penetration
- 步履不停Original
- 2019-06-22 17:52:4010641browse

Caching technology can be used to reduce the pressure on the database and improve access efficiency. Currently, caching is being paid more and more attention in enterprise projects. But caching doesn’t mean just adding projects casually. Integrating caching into the project is the first step. The penetration problem caused by the cache and the resulting snow bounce problem are all issues that we urgently need to solve. This article will share with you the solutions I use in my daily projects for your reference.
1. The principle of cache penetration
The normal use of cache is as shown in the figure:
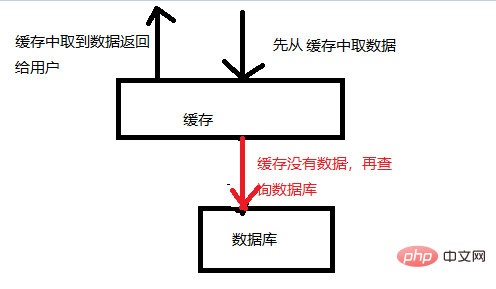
As shown in the figure, the cache usage process :
1. First get the data from the cache. If it can be obtained, return the data directly to the user. This eliminates the need to access the database and reduces the pressure on the database.
2. If there is no data in the cache, the database will be accessed.
There will be a BUG here, as shown in the picture:
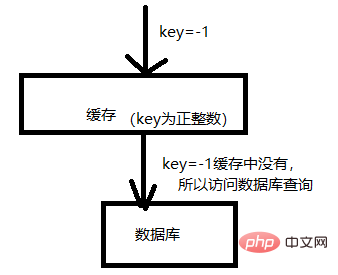
As shown in the picture, the cache is like a firewall for the database, which will request more frequently data. Put it in the cache to reduce the pressure on the database. But if someone attacks maliciously, they can easily penetrate your cache and put all the pressure on the database. For example, in the picture above, the keys in your cache are all positive integers, but I use negative numbers as keys to access your cache. This will cause the cache to be penetrated and put pressure directly on the database.
2. Reasons for cache penetration
The problem of cache penetration must be under no matter how large the concurrency is. Based on this premise, we analyze the reasons for cache penetration as follows:
1. Malicious attack, guess your key naming method, and then estimate to use a key that is not in your cache to access.
2. For the first data access, if there is no data in the cache yet, in a concurrent scenario, all requests will be pushed to the database.
3. The data in the database is also empty, so even if the database is accessed, the data cannot be obtained, so there must be no corresponding data in the cache. This can also lead to penetration.
3. Solving cache penetration
Cache penetration lies in avoiding the reasons for penetration step by step, as shown in the figure:
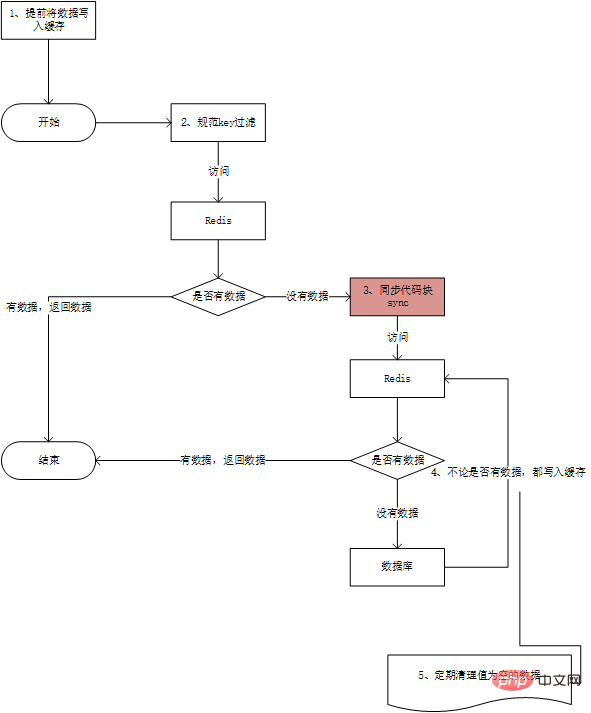
As shown above As shown, the solution steps are as follows:
1. When the web server starts, write data that may be frequently accessed concurrently into the cache in advance. —This avoids queuing and blocking of a large number of requests in step 3.
2. Standardize the naming of keys and unify cache query and write entries. In this way, at the entrance, the specification of the key is detected. – In this way, malicious keys are saved and intercepted.
-
3. Synchronized double detection mechanism. At this time, we need to use the synchronization (Synchronized) mechanism to check whether the corresponding key exists in the cache before the synchronization code block, and then synchronize the code block Check again whether the cache contains the key to be queried. The purpose of this "double detection" is to avoid meaningless database access caused by concurrent scenarios (it is also a solution that strictly avoids penetration).
This step will cause queuing, but as we said in the first step, in order to avoid a large number of queuing, a large number of predictable requests can be written to the cache in advance.
4. Regardless of whether there is data in the database, the corresponding key is saved in the cache. The value is empty. – This is to avoid ordinary cache-penetrating access to the database due to the absence of this data in the database.
5. If there are too many null values in step 4, it will also cause memory exhaustion. Causes unnecessary memory consumption. In this way, the keys with empty values must be cleaned regularly. Prevent the memory from being maliciously occupied. As a result, normal functions cannot cache data.
For more Redis-related technical articles, please visit the Redis Tutorial column to learn !
The above is the detailed content of How to solve redis cache penetration. For more information, please follow other related articles on the PHP Chinese website!

