scanner.php
Copy the code The code is as follows:
/**************PHP Web Trojan Scanner***********************/
/* [+] Author: alibaba */
/* [+] QQ: 1499281192 */
/* [+] MSN: weeming21@hotmail.com */
/* [+] First published: t00ls.net, please indicate t00ls when reprinting */
/* [+] Version: v1.0 */
/* [+] Function: web version of php Trojan scanning tool*/
/* [+] Note: Scanned files are not necessarily backdoors, */
/* Please judge, review and compare the original files by yourself. */
/* If you are not sure whether the scanned file is a backdoor, */
/* You are welcome to send the file to me for analysis.*/
/*******************************************************/
ob_start();
set_time_limit(0);
$username = "t00ls"; //设置用户名
$password = "t00ls"; //设置密码
$md5 = md5(md5($username).md5($password));
$version = "PHP Web木马扫描器 v1.0";
$realpath = realpath('./');
$selfpath = $_SERVER['PHP_SELF'];
$selfpath = substr($selfpath, 0, strrpos($selfpath,'/'));
define('REALPATH', str_replace('//','/',str_replace('\','/',substr($realpath, 0, strlen($realpath) - strlen($selfpath)))));
define('MYFILE', basename(__FILE__));
define('MYPATH', str_replace('\', '/', dirname(__FILE__)).'/');
define('MYFULLPATH', str_replace('\', '/', (__FILE__)));
define('HOST', "http://".$_SERVER['HTTP_HOST']);
?>
if(!(isset($_COOKIE['t00ls']) && $_COOKIE['t00ls'] == $md5) && !(isset($_POST['username']) && isset($_POST['password']) && (md5(md5($_POST['username']).md5($_POST['password']))==$md5)))
{
echo '';
}
elseif(isset($_POST['username']) && isset($_POST['password']) && (md5(md5($_POST['username']).md5($_POST['password']))==$md5))
{
setcookie("t00ls", $md5, time()+60*60*24*365,"/");
echo "登陆成功!";
header( 'refresh: 1; url='.MYFILE.'?action=scan' );
exit();
}
else
{
setcookie("t00ls", $md5, time()+60*60*24*365,"/");
$setting = getSetting();
$action = isset($_GET['action'])?$_GET['action']:"";
if($action=="logout")
{
setcookie ("t00ls", "", time() - 3600);
Header("Location: ".MYFILE);
exit();
}
if($action=="download" && isset($_GET['file']) && trim($_GET['file'])!="")
{
$file = $_GET['file'];
ob_clean();
if (@file_exists($file)) {
header("Content-type: application/octet-stream");
header("Content-Disposition: filename="".basename($file).""");
echo file_get_contents($file);
}
exit();
}
?>
| $version"?> |
|
=date("Y-m-d H:i:s",mktime())?> 扫描 | 设定 | 登出 |
if($action=="setting")
{
if(isset($_POST['btnsetting']))
{
$Ssetting = array();
$Ssetting['user']=isset($_POST['checkuser'])?$_POST['checkuser']:"php | php? | phtml";
$Ssetting['all']=isset($_POST['checkall'])&&$_POST['checkall']=="on"?1:0;
$Ssetting['hta']=isset($_POST['checkhta'])&&$_POST['checkhta']=="on"?1:0;
setcookie("t00ls_s", base64_encode(serialize($Ssetting)), time()+60*60*24*365,"/");
echo "设置完成!";
header( 'refresh: 1; url='.MYFILE.'?action=setting' );
exit();
}
?>
}
else
{
$dir = isset($_POST['path'])?$_POST['path']:MYPATH;
$dir = substr($dir,-1)!="/"?$dir."/":$dir;
?>
if(isset($_POST['btnScan']))
{
$start=mktime();
$is_user = array();
$is_ext = "";
$list = "";
if(trim($setting['user'])!="")
{
$is_user = explode("|",$setting['user']);
if(count($is_user)>0)
{
foreach($is_user as $key=>$value)
$is_user[$key]=trim(str_replace("?","(.)",$value));
$is_ext = "(\.".implode("($|\.))|(\.",$is_user)."($|\.))";
}
}
if($setting['hta']==1)
{
$is_hta=1;
$is_ext = strlen($is_ext)>0?$is_ext."|":$is_ext;
$is_ext.="(^\.htaccess$)";
}
if($setting['all']==1 || (strlen($is_ext)==0 && $setting['hta']==0))
{
$is_ext="(.+)";
}
$php_code = getCode();
if(!is_readable($dir))
$dir = MYPATH;
$count=$scanned=0;
scan($dir,$is_ext);
$end=mktime();
$spent = ($end - $start);
?>
| No. | 文件 | 更新时间 | 原因 | 特征 | 动作 |
}
}
}
ob_flush();
?>
function scan($path = '.',$is_ext){
global $php_code,$count,$scanned,$list;
$ignore = array('.', '..' );
$replace=array(" ","n","r","t");
$dh = @opendir( $path );
while(false!==($file=readdir($dh))){
if( !in_array( $file, $ignore ) ){
if( is_dir( "$path$file" ) ){
scan("$path$file/",$is_ext);
} else {
$current = $path.$file;
if(MYFULLPATH==$current) continue;
if(!preg_match("/$is_ext/i",$file)) continue;
if(is_readable($current))
{
$scanned++;
$c
$c
foreach($php_code as $key => $value)
{
if(preg_match("/$value/i",$content))
{
$count++;
$j = $count % 2 + 1;
$filetime = date('Y-m-d H:i:s',filemtime($current));
$reason = explode("->",$key);
$url = str_replace(REALPATH,HOST,$current);
preg_match("/$value/i",$content,$arr);
$list.="
//echo $key . "-" . $path . $file ."(" . $arr[0] . ")" ."
";
//echo $path . $file ."
";
break;
}
}
}
}
}
}
closedir( $dh );
}
function getSetting()
{
$Ssetting = array();
if(isset($_COOKIE['t00ls_s']))
{
$Ssetting = unserialize(base64_decode($_COOKIE['t00ls_s']));
$Ssetting['user']=isset($Ssetting['user'])?$Ssetting['user']:"php | php? | phtml | shtml";
$Ssetting['all']=isset($Ssetting['all'])?intval($Ssetting['all']):0;
$Ssetting['hta']=isset($Ssetting['hta'])?intval($Ssetting['hta']):1;
}
else
{
$Ssetting['user']="php | php? | phtml | shtml";
$Ssetting['all']=0;
$Ssetting['hta']=1;
setcookie("t00ls_s", base64_encode(serialize($Ssetting)), time()+60*60*24*365,"/");
}
return $Ssetting;
}
function getCode()
{
return array(
'Backdoor characteristics->cha88.cn'=>'cha88.cn',
'Backdoor characteristics->c99shell'=>'c99shell',
'Backdoor Features->phpspy'=>'phpspy',
'Backdoor Features->Scanners'=>'Scanners',
'Backdoor Features->cmd.php'=>'cmd.php',
'Backdoor characteristics->str_rot13'=>'str_rot13',
'Backdoor characteristics->webshell'=>'webshell',
'Backdoor characteristics->EgY_SpIdEr'=>'EgY_SpIdEr',
'Backdoor Features->tools88.com'=>'tools88.com',
'Backdoor Feature->SECFORCE'=>'SECFORCE',
'Backdoor Feature->eval("?>'=> 'eval(('|")?>',
'Suspicious code characteristics->system('=>'system(',
'Suspicious code characteristics->passthru('=>'passthru(' ,
'Suspicious code characteristics->shell_exec('=>'shell_exec(',
'Suspicious code characteristics->exec('=>'exec(',
'Suspicious code characteristics->popen(' =>'popen(',
'Suspicious code characteristics->proc_open'=>'proc_open',
'Suspicious code characteristics->eval($'=>'eval(('|"|s* )\$',
'Suspicious code characteristics->assert($'=>'assert(('|"|s*)\$',
'Dangerous MYSQL code->returns string soname'=> 'returnsstringsoname',
'Dangerous MYSQL code->into outfile'=>'intooutfile',
'Dangerous MYSQL code->load_file'=>'select(s+)(.*)load_file',
'Encryption Backdoor characteristics->eval(gzinflate('=>'eval(gzinflate(',
'Encryption backdoor characteristics->eval(base64_decode('=>'eval(base64_decode(',
'Encryption backdoor characteristics-> ;eval(gzuncompress('=>'eval(gzuncompress(',
'Encryption backdoor characteristics->eval(gzdecode('=>'eval(gzdecode(',
'Encryption backdoor characteristics->eval(str_rot13 ('=>'eval(str_rot13(',
'Encryption backdoor characteristics->gzuncompress(base64_decode('=>'gzuncompress(base64_decode(',
'Encryption backdoor characteristics->base64_decode(gzuncompress('=> ;'base64_decode(gzuncompress(',
'One sentence backdoor characteristics->eval($_'=>'eval(('|"|s*)\$_(POST|GET|REQUEST|COOKIE)',
'One sentence backdoor characteristics->assert($_'=>'assert(('|"|s*)\$_(POST|GET|REQUEST|COOKIE)',
'One sentence backdoor characteristics-> ;require($_'=>'require(('|"|s*)\$_(POST|GET|REQUEST|COOKIE)',
'One sentence backdoor characteristics->require_once($_'=> ;'require_once(('|"|s*)\$_(POST|GET|REQUEST|COOKIE)',
'One sentence backdoor characteristics->include($_'=>'include(('|" |s*)\$_(POST|GET|REQUEST|COOKIE)',
'One sentence backdoor characteristics->include_once($_'=>'include_once(('|"|s*)\$_( POST|GET|REQUEST|COOKIE)',
'One sentence backdoor characteristics->call_user_func("assert"'=>'call_user_func(("|')assert("|')',
'One sentence backdoor characteristics ->call_user_func($_'=>'call_user_func(('|"|s*)\$_(POST|GET|REQUEST|COOKIE)',
'One sentence backdoor characteristics->$_POST/GET/ REQUEST/COOKIE[?]($_POST/GET/REQUEST/COOKIE[?]'=>'$_(POST|GET|REQUEST|COOKIE)[([^]]+)](('|"|s *)\$_(POST|GET|REQUEST|COOKIE)[',
'One sentence backdoor characteristics->echo(file_get_contents($_POST/GET/REQUEST/COOKIE'=>'echo(file_get_contents(('| "|s*)\$_(POST|GET|REQUEST|COOKIE)',
'Upload backdoor characteristics->file_put_contents($_POST/GET/REQUEST/COOKIE,$_POST/GET/REQUEST/COOKIE'=> 'file_put_contents(('|"|s*)\$_(POST|GET|REQUEST|COOKIE)[([^]]+)],('|"|s*)\$_(POST|GET|REQUEST |COOKIE)',
'Upload backdoor features->fputs(fopen("?","w"),$_POST/GET/REQUEST/COOKIE['=>'fputs(fopen((.+),( '|")w('|")),('|"|s*)\$_(POST|GET|REQUEST|COOKIE)[',
'.htaccess plug-in feature->SetHandler application/x- httpd-php'=>'SetHandlerapplication/x-httpd-php',
'.htaccess plug-in feature->php_value auto_prepend_file'=>'php_valueauto_prepend_file',
'.htaccess plug-in feature->php_value auto_append_file' =>'php_valueauto_append_file'
);
}
?>
A tool for scanning PHP Trojans in the PHP environment. Currently, the following feature codes can be scanned
Copy the code The code is as follows:
Feature codes:
Backdoor features->cha88.cn
Backdoor features->c99shell
Backdoor features->phpspy
Backdoor features->Scanners
Backdoor features->cmd.php
Backdoor features-> str_rot13
Backdoor characteristics->webshell
Backdoor characteristics->EgY_SpIdEr
Backdoor characteristics->tools88.com
Backdoor characteristics->SECFORCE
Backdoor characteristics->eval("?>
Suspicious code characteristics-> system(
Suspicious code characteristics->passthru(
Suspicious code characteristics->shell_exec(
Suspicious code characteristics->exec(
Suspicious code characteristics->popen(
Suspicious code characteristics->proc_open
Suspicious code characteristics ->eval($
Suspicious code signature->assert($
Dangerous MYSQL code->returns string soname
Dangerous MYSQL code->into outfile
Dangerous MYSQL code->load_file
Encryption backdoor signature-> eval(gzinflate(
Encryption backdoor characteristics->eval(base64_decode(
Encryption backdoor characteristics->eval(gzuncompress(
Encryption backdoor characteristics->gzuncompress(base64_decode(
Encryption backdoor characteristics->base64_decode(gzuncompress(
One sentence Backdoor features->eval($_
Backdoor features in one sentence->assert($_
Backdoor features in one sentence->require($_
Backdoor features in one sentence->require_once($_
Backdoor in one sentence) Features->include($_
One sentence backdoor feature->include_once($_
One sentence backdoor feature->call_user_func("assert"
One sentence backdoor feature->call_user_func($_
One sentence backdoor feature ->$_POST/GET/REQUEST/COOKIE[?]($_POST/GET/REQUEST/COOKIE[?]
Backdoor characteristics in one sentence->echo(file_get_contents($_POST/GET/REQUEST/COOKIE
Upload backdoor characteristics ->file_put_contents($_POST/GET/REQUEST/COOKIE,$_POST/GET/REQUEST/COOKIE
Upload backdoor features->fputs(fopen("?","w"),$_POST/GET/REQUEST/COOKIE [
.htaccess plug-in feature->SetHandler application/x-httpd-php
.htaccess plug-in feature->php_value auto_prepend_file
.htaccess plug-in feature->php_value auto_append_file
Lazy design, directly apply phpspy style
Note: The scanned files are not necessarily backdoors. Please judge, review and compare the original files by yourself.
The above introduces the PHP Web Trojan Scanner Code v10 security testing tool, including the relevant content. I hope it will be helpful to friends who are interested in PHP tutorials.
 华为GT3 Pro和GT4的差异是什么?Dec 29, 2023 pm 02:27 PM
华为GT3 Pro和GT4的差异是什么?Dec 29, 2023 pm 02:27 PM许多用户在选择智能手表的时候都会选择的华为的品牌,其中华为GT3pro和GT4都是非常热门的选择,不少用户都很好奇华为GT3pro和GT4有什么区别,下面就就给大家介绍一下二者。华为GT3pro和GT4有什么区别一、外观GT4:46mm和41mm,材质是玻璃表镜+不锈钢机身+高分纤维后壳。GT3pro:46.6mm和42.9mm,材质是蓝宝石玻璃表镜+钛金属机身/陶瓷机身+陶瓷后壳二、健康GT4:采用最新的华为Truseen5.5+算法,结果会更加的精准。GT3pro:多了ECG心电图和血管及安
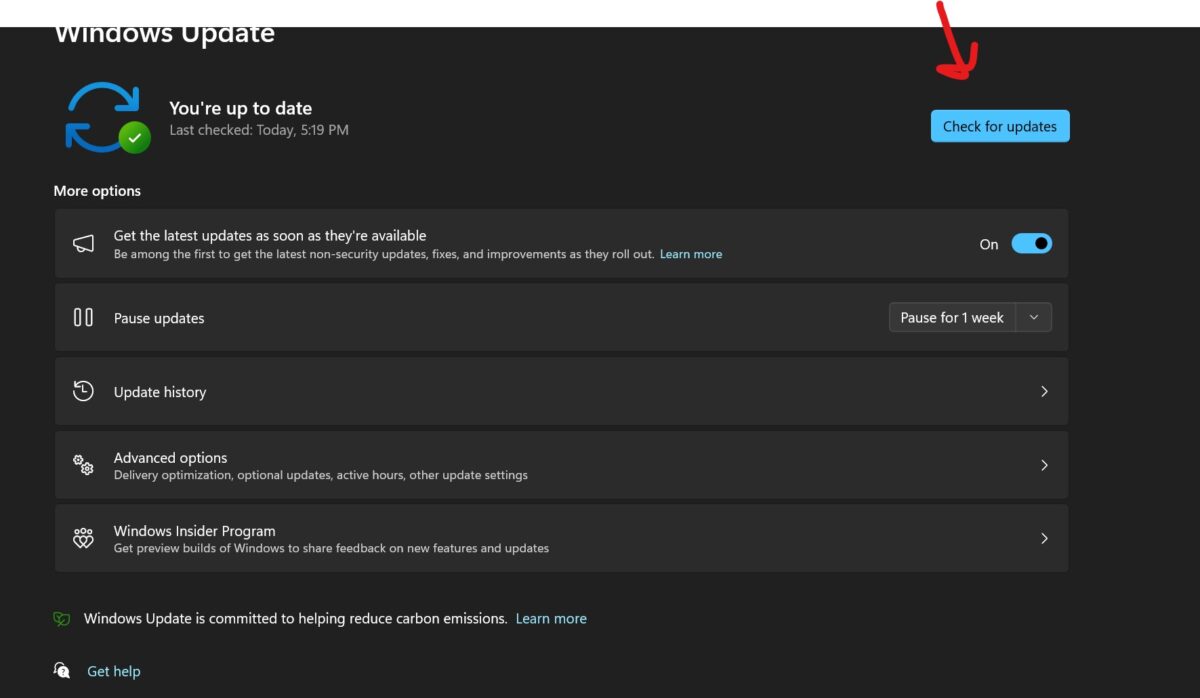 修复:截图工具在 Windows 11 中不起作用Aug 24, 2023 am 09:48 AM
修复:截图工具在 Windows 11 中不起作用Aug 24, 2023 am 09:48 AM为什么截图工具在Windows11上不起作用了解问题的根本原因有助于找到正确的解决方案。以下是截图工具可能无法正常工作的主要原因:对焦助手已打开:这可以防止截图工具打开。应用程序损坏:如果截图工具在启动时崩溃,则可能已损坏。过时的图形驱动程序:不兼容的驱动程序可能会干扰截图工具。来自其他应用程序的干扰:其他正在运行的应用程序可能与截图工具冲突。证书已过期:升级过程中的错误可能会导致此issu简单的解决方案这些适合大多数用户,不需要任何特殊的技术知识。1.更新窗口和Microsoft应用商店应用程
 浅析php中POST方法带参数跳转页面Mar 23, 2023 am 09:15 AM
浅析php中POST方法带参数跳转页面Mar 23, 2023 am 09:15 AM对于PHP开发者来说,使用POST带参数跳转页面是一项基本技能。POST是HTTP中一种发送数据的方法,它可以通过HTTP请求向服务器提交数据,跳转页面则是在服务器端进行页面的处理和跳转。在实际开发中,我们经常需要使用POST带参数来跳转页面,以达到一定的功能目的。
 php怎么判断post有没有提交Mar 21, 2023 pm 07:12 PM
php怎么判断post有没有提交Mar 21, 2023 pm 07:12 PMPHP是一种广泛使用的服务器端脚本语言,它可以用于创建交互式和动态的Web应用程序。在开发PHP应用时,我们通常需要通过表单将用户输入数据提交给服务器端处理。然而,有时候我们需要在PHP中判断是否有表单数据被提交,这篇文章将介绍如何进行这样的判断。
 python requests post如何使用Apr 29, 2023 pm 04:52 PM
python requests post如何使用Apr 29, 2023 pm 04:52 PMpython模拟浏览器发送post请求importrequests格式request.postrequest.post(url,data,json,kwargs)#post请求格式request.get(url,params,kwargs)#对比get请求发送post请求传参分为表单(x-www-form-urlencoded)json(application/json)data参数支持字典格式和字符串格式,字典格式用json.dumps()方法把data转换为合法的json格式字符串次方法需要
 如何修复无法连接到iPhone上的App Store错误Jul 29, 2023 am 08:22 AM
如何修复无法连接到iPhone上的App Store错误Jul 29, 2023 am 08:22 AM第1部分:初始故障排除步骤检查苹果的系统状态:在深入研究复杂的解决方案之前,让我们从基础知识开始。问题可能不在于您的设备;苹果的服务器可能会关闭。访问Apple的系统状态页面,查看AppStore是否正常工作。如果有问题,您所能做的就是等待Apple修复它。检查您的互联网连接:确保您拥有稳定的互联网连接,因为“无法连接到AppStore”问题有时可归因于连接不良。尝试在Wi-Fi和移动数据之间切换或重置网络设置(“常规”>“重置”>“重置网络设置”>设置)。更新您的iOS版本:
 java如何发起http请求调用post与get接口May 16, 2023 pm 07:53 PM
java如何发起http请求调用post与get接口May 16, 2023 pm 07:53 PM一、java调用post接口1、使用URLConnection或者HttpURLConnectionjava自带的,无需下载其他jar包URLConnection方式调用,如果接口响应码被服务端修改则无法接收到返回报文,只能当响应码正确时才能接收到返回publicstaticStringsendPost(Stringurl,Stringparam){OutputStreamWriterout=null;BufferedReaderin=null;StringBuilderresult=newSt
 NGINX反向代理对HTML页面的POST请求返回405怎么解决May 22, 2023 pm 07:49 PM
NGINX反向代理对HTML页面的POST请求返回405怎么解决May 22, 2023 pm 07:49 PM实现如下:server{listen80;listen443ssl;server_namenirvana.test-a.gogen;ssl_certificate/etc/nginx/ssl/nirvana.test-a.gogen.crt;ssl_certificate_key/etc/nginx/ssl/nirvana.test-a.gogen.key;proxy_connect_timeout600;proxy_read_timeout600;proxy_send_timeout600;c


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Chinese version
Chinese version, very easy to use

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

SublimeText3 Linux new version
SublimeText3 Linux latest version

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.






