
Detailed explanation of SELinux policy management in CentOS system
In the Linux security field, SELinux (Security Enhanced Linux) is like a solid guardian. Although often misunderstood, it is crucial to protecting the system from potential threats. For CentOS administrators and users, mastering SELinux policy management is crucial to ensuring a strong security configuration. This article aims to clarify the secrets of SELinux policy management in CentOS and introduce its complexity and functionality.
In-depth understanding of SELinux
SELinux changes Linux security mode by enforcing mandatory access control (MAC) based on security policies. Unlike traditional autonomous access control (DAC) that relies on user permissions, SELinux assigns security contexts to system objects such as files, processes, and sockets. These contexts include tags representing object types, roles, and domains, allowing SELinux to perform fine-grained access control decisions.
SELinux mainly runs in two modes: mandatory mode and license mode. In forced mode, SELinux actively executes security policies and refuses unauthorized operations. Instead, the licensed model records policy violations without enforcing them, which facilitates policy development and troubleshooting.
SELinux Strategy Basics
SELinux policies define rules for access control decisions within the system. CentOS usually uses target policies to restrict SELinux enforcement to specific system services and processes. In contrast, MLS policies enforce mandatory access control based on sensitivity tags, which are suitable for high-security environments.
Key components of SELinux policies include type mandatory (TE), role-based access control (RBAC), and multi-level security (MLS). TE controls access based on the object type and its associated permissions to ensure that the process runs within defined constraints. RBAC assigns roles to users and domains, stating their access rights in the system. MLS extends access control to support multiple security levels, which is critical for systems that handle confidential information.
SELinux Policy Management on CentOS
Managing SELinux policies on CentOS involves the use of various tools and utilities to effectively configure and exclude security settings. Administrators can use the setenforce command to switch between mandatory and licensed modes to flexibly execute policies.
Using the SELinux policy module enables administrators to customize access controls for specific applications and services. CentOS provides tools like semodule to install, manage and create custom policy modules tailored to system needs. By encapsulating policy rules in modules, administrators can deploy targeted security configurations without modifying core SELinux policies.
Troubleshooting SELinux policy violations usually requires analyzing audit logs generated by auditd daemon. These logging policies deny, helping administrators identify and resolve security incidents. Common troubleshooting techniques include viewing audit logs, identifying policy violations, and applying policy adjustments to resolve security issues.
Best Practices for SELinux Policy Management
To maintain a secure and stable CentOS environment, it is crucial to comply with best practices for SELinux policy management. Regular updates to SELinux policies ensure compatibility with system updates and patches, mitigating potential security vulnerabilities. Additionally, regular review and review of SELinux policies can help proactively identify and correct misconfigurations or policy conflicts.
Loging SELinux policy changes helps in knowledge sharing and maintains a complete record of secure configurations. Detailed documentation enables administrators to track policy modifications, understand their fundamentals, and replicate configurations in similar environments.
Summary
In short, SELinux policy management on CentOS is a key aspect of Linux security and requires careful attention and expertise to navigate effectively. By understanding SELinux basics, mastering policy management tools, and following best practices, administrators can strengthen CentOS systems to protect against potential security threats. Using SELinux as a cornerstone of CentOS security enables organizations to maintain strong defense capabilities and protect sensitive assets in a changing threat environment.
The above is the detailed content of Understanding the Basics of SELinux Policy Management on CentOS. For more information, please follow other related articles on the PHP Chinese website!
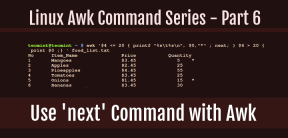 How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AM
How to Use 'next' Command with Awk in Linux - Part 6May 15, 2025 am 10:43 AMIn this sixth installment of our Awk series, we will explore the next command, which is instrumental in enhancing the efficiency of your script executions by skipping redundant processing steps.What is the next Command?The next command in awk instruc
 How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AM
How to Efficiently Transfer Files in LinuxMay 15, 2025 am 10:42 AMTransferring files in Linux systems is a common task that every system administrator should master, especially when it comes to network transmission between local or remote systems. Linux provides two commonly used tools to accomplish this task: SCP (Secure Replication) and Rsync. Both provide a safe and convenient way to transfer files between local or remote machines. This article will explain in detail how to use SCP and Rsync commands to transfer files, including local and remote file transfers. Understand the scp (Secure Copy Protocol) in Linux scp command is a command line program used to securely copy files and directories between two hosts via SSH (Secure Shell), which means that when files are transferred over the Internet, the number of
 10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AM
10 Most Popular Linux Desktop Environments of All TimeMay 15, 2025 am 10:35 AMOne fascinating feature of Linux, in contrast to Windows and Mac OS X, is its support for a variety of desktop environments. This allows desktop users to select the most suitable and fitting desktop environment based on their computing requirements.A
 How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AM
How to Install LibreOffice 24.8 in Linux DesktopMay 15, 2025 am 10:15 AMLibreOffice stands out as a robust and open-source office suite, tailored for Linux, Windows, and Mac platforms. It boasts an array of advanced features for handling word documents, spreadsheets, presentations, drawings, calculations, and mathematica
 How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AM
How to Work with PDF Files Using ONLYOFFICE Docs in LinuxMay 15, 2025 am 09:58 AMLinux users who manage PDF files have a wide array of programs at their disposal. Specifically, there are numerous specialized PDF tools designed for various functions.For instance, you might opt to install a PDF viewer for reading files or a PDF edi
 How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AM
How to Filter Command Output Using Awk and STDINMay 15, 2025 am 09:53 AMIn the earlier segments of the Awk command series, our focus was primarily on reading input from files. However, what if you need to read input from STDIN?In Part 7 of the Awk series, we will explore several examples where you can use the output of o
 Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AM
Clifm - Lightning-Fast Terminal File Manager for LinuxMay 15, 2025 am 09:45 AMClifm stands out as a distinctive and incredibly swift command-line file manager, designed on the foundation of a shell-like interface. This means that users can engage with their file system using commands they are already familiar with.The choice o
 How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AM
How to Upgrade from Linux Mint 21.3 to Linux Mint 22May 15, 2025 am 09:44 AMIf you prefer not to perform a new installation of Linux Mint 22 Wilma, you have the option to upgrade from a previous version.In this guide, we will detail the process to upgrade from Linux Mint 21.3 (the most recent minor release of the 21.x series


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

SublimeText3 English version
Recommended: Win version, supports code prompts!

SublimeText3 Linux new version
SublimeText3 Linux latest version

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

SublimeText3 Mac version
God-level code editing software (SublimeText3)






