Improving IT security: Five-step plan to plug loopholes
Enterprise IT security breaches can lead to catastrophic consequences, and giants like Google can be targeted. IBM data shows that the United States monitored 1.5 million cyber attacks last year, with an average of 16,856 attacks per organization each year, and many of them resulted in quantifiable data breaches. The average downtime cost per minute for a medium-sized attack is $38,065. In the face of increasingly complex cyber threats, IT security must be prioritized. However, many IT professionals don't understand the vulnerability that could allow hackers to access their systems and sank the organization. While it is usually easy to fix these vulnerabilities, the difficulty lies in discovering them.
The following are five steps to help you discover IT security vulnerabilities:
1. Implement external penetration test:
Hiring a white hat hacker for penetration testing can easily identify critical external security vulnerabilities than using security vulnerability scanning tools. Starting with your company name, these authorized hackers will use the latest attacks to collect as much information about your employees and infrastructure as possible. They will search for vulnerabilities in your website, applications, systems, and configurations and exploit them like malicious people. If the white hat hacker can't find any technical vulnerabilities, they will use social engineering techniques such as phishing to try to collect data from your users. Combining social engineering with penetration testing is essential to know whether your users are involved in dangerous behaviors. You should conduct penetration testing regularly, especially in regulated industries. This will keep your system safe and put you a few steps ahead of hackers.
2. Identify internal risks:
As the Snowden incident proves, your employees may be your greatest safety risk. Internal penetration tests can tell you exactly how much information an unhappy employee can steal and assess the risk of loss if the employee decides to engage in malicious behavior. During internal penetration testing, authorized hackers will work within your organization to exploit your internal vulnerabilities. They will look for weaknesses in IT systems, databases, networks, applications, access controls, and firewalls. This will reveal flaws in your infrastructure and help you identify data that is at risk. Internal penetration tests should be performed every time an external penetration test is conducted.
3. Perform risk assessment:
You should conduct a risk assessment based on the results of external and internal penetration tests. Analyze your risks and determine which risks pose the greatest threat to your organization. You may need to introduce your risks to your executives in your organization and convince them to invest in safety. Make suggestions on what needs to be fixed and how much to invest to reduce the risk of security vulnerabilities. New risk assessments are conducted annually to understand the latest technologies and threats. Risk assessment is also mandatory if you accept payment card transactions and must comply with PCI-DSS regulations.
4. Develop a data breach and security incident response plan:
Economist Intelligence Unit found that while 77% of companies have encountered security breaches in the past two years, 38% of them still have no incident response plans. Globally, only 17% of organizations are ready for security incidents. Incident response planning is critical to quickly recovering data and services after a vulnerability occurs. Your plan should specify:
- Members of the response team and the actions they should take in the event of a vulnerability or attack.
- Who should be invited to investigate the vulnerability and restore everything to normal operation.
- How will you communicate with employees, customers, and stakeholders after the vulnerability occurs.
- How you will implement lessons learned to avoid similar vulnerabilities in the future.
Practical testing of your incident response plan with your IT team and employees during your annual penetration testing period. Your IT team should be able to detect and respond to internal attacks. Actually test your plan and train your team to react and think proactively.
5. Test backup and recovery preparation:
Many companies failed to test their backups. Your backups may not be as reliable as you think, and if your data is lost or corrupted, you will become vulnerable. It is crucial to test your backups to ensure you can quickly recover your data after a vulnerability or other security incidents. You can also consider backing up your data in multiple data centers. You may need a local data center to quickly access your infrastructure, as well as another data center in another city or country. If a data center goes down, you can still use your data. Test how your team can react in a trial case. Let them compete with each other for the fastest time to put server backups into use.
Conclusion:
Perform each of these five steps to identify your IT security vulnerabilities and understand what you must do to protect yourself from threats. When was the last time you had a security check? What are your tips for staying safe?
(The picture remains the original format and position unchanged)

The above is the detailed content of 5 Steps to Uncovering Your IT Security Gaps. For more information, please follow other related articles on the PHP Chinese website!
 Behind the first Android access to DeepSeek: Seeing the power of womenMar 12, 2025 pm 12:27 PM
Behind the first Android access to DeepSeek: Seeing the power of womenMar 12, 2025 pm 12:27 PMThe rise of Chinese women's tech power in the field of AI: The story behind Honor's collaboration with DeepSeek women's contribution to the field of technology is becoming increasingly significant. Data from the Ministry of Science and Technology of China shows that the number of female science and technology workers is huge and shows unique social value sensitivity in the development of AI algorithms. This article will focus on Honor mobile phones and explore the strength of the female team behind it being the first to connect to the DeepSeek big model, showing how they can promote technological progress and reshape the value coordinate system of technological development. On February 8, 2024, Honor officially launched the DeepSeek-R1 full-blood version big model, becoming the first manufacturer in the Android camp to connect to DeepSeek, arousing enthusiastic response from users. Behind this success, female team members are making product decisions, technical breakthroughs and users
 DeepSeek's 'amazing' profit: the theoretical profit margin is as high as 545%!Mar 12, 2025 pm 12:21 PM
DeepSeek's 'amazing' profit: the theoretical profit margin is as high as 545%!Mar 12, 2025 pm 12:21 PMDeepSeek released a technical article on Zhihu, introducing its DeepSeek-V3/R1 inference system in detail, and disclosed key financial data for the first time, which attracted industry attention. The article shows that the system's daily cost profit margin is as high as 545%, setting a new high in global AI big model profit. DeepSeek's low-cost strategy gives it an advantage in market competition. The cost of its model training is only 1%-5% of similar products, and the cost of V3 model training is only US$5.576 million, far lower than that of its competitors. Meanwhile, R1's API pricing is only 1/7 to 1/2 of OpenAIo3-mini. These data prove the commercial feasibility of the DeepSeek technology route and also establish the efficient profitability of AI models.
 Top 10 Best Free Backlink Checker Tools in 2025Mar 21, 2025 am 08:28 AM
Top 10 Best Free Backlink Checker Tools in 2025Mar 21, 2025 am 08:28 AMWebsite construction is just the first step: the importance of SEO and backlinks Building a website is just the first step to converting it into a valuable marketing asset. You need to do SEO optimization to improve the visibility of your website in search engines and attract potential customers. Backlinks are the key to improving your website rankings, and it shows Google and other search engines the authority and credibility of your website. Not all backlinks are beneficial: Identify and avoid harmful links Not all backlinks are beneficial. Harmful links can harm your ranking. Excellent free backlink checking tool monitors the source of links to your website and reminds you of harmful links. In addition, you can also analyze your competitors’ link strategies and learn from them. Free backlink checking tool: Your SEO intelligence officer
 Midea launches its first DeepSeek air conditioner: AI voice interaction can achieve 400,000 commands!Mar 12, 2025 pm 12:18 PM
Midea launches its first DeepSeek air conditioner: AI voice interaction can achieve 400,000 commands!Mar 12, 2025 pm 12:18 PMMidea will soon release its first air conditioner equipped with a DeepSeek big model - Midea fresh and clean air machine T6. The press conference is scheduled to be held at 1:30 pm on March 1. This air conditioner is equipped with an advanced air intelligent driving system, which can intelligently adjust parameters such as temperature, humidity and wind speed according to the environment. More importantly, it integrates the DeepSeek big model and supports more than 400,000 AI voice commands. Midea's move has caused heated discussions in the industry, and is particularly concerned about the significance of combining white goods and large models. Unlike the simple temperature settings of traditional air conditioners, Midea fresh and clean air machine T6 can understand more complex and vague instructions and intelligently adjust humidity according to the home environment, significantly improving the user experience.
 Another national product from Baidu is connected to DeepSeek. Is it open or follow the trend?Mar 12, 2025 pm 01:48 PM
Another national product from Baidu is connected to DeepSeek. Is it open or follow the trend?Mar 12, 2025 pm 01:48 PMDeepSeek-R1 empowers Baidu Library and Netdisk: The perfect integration of deep thinking and action has quickly integrated into many platforms in just one month. With its bold strategic layout, Baidu integrates DeepSeek as a third-party model partner and integrates it into its ecosystem, which marks a major progress in its "big model search" ecological strategy. Baidu Search and Wenxin Intelligent Intelligent Platform are the first to connect to the deep search functions of DeepSeek and Wenxin big models, providing users with a free AI search experience. At the same time, the classic slogan of "You will know when you go to Baidu", and the new version of Baidu APP also integrates the capabilities of Wenxin's big model and DeepSeek, launching "AI search" and "wide network information refinement"
 Prompt Engineering for Web DevelopmentMar 09, 2025 am 08:27 AM
Prompt Engineering for Web DevelopmentMar 09, 2025 am 08:27 AMAI Prompt Engineering for Code Generation: A Developer's Guide The landscape of code development is poised for a significant shift. Mastering Large Language Models (LLMs) and prompt engineering will be crucial for developers in the coming years. Th
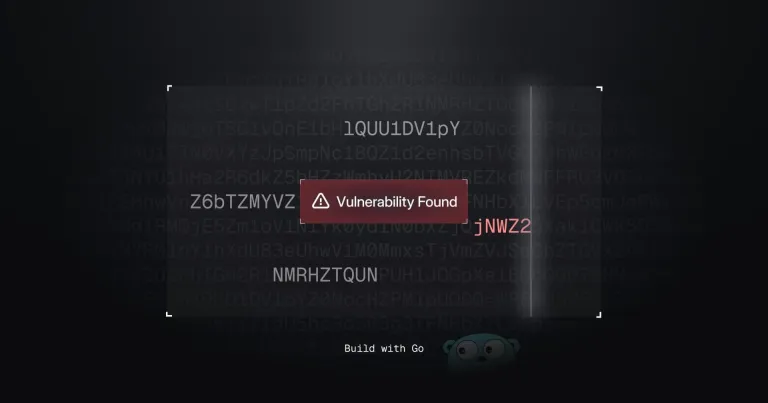 Building a Network Vulnerability Scanner with GoApr 01, 2025 am 08:27 AM
Building a Network Vulnerability Scanner with GoApr 01, 2025 am 08:27 AMThis Go-based network vulnerability scanner efficiently identifies potential security weaknesses. It leverages Go's concurrency features for speed and includes service detection and vulnerability matching. Let's explore its capabilities and ethical


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft







