The sudo command allows users to run commands with root privileges. This can be a powerful tool, but it can also be a security risk if not used carefully. One way to mitigate this risk is to allow sudo users to run particular authorized commands. In this guide, we will show you how to restrict sudo users to run specific commands with sudo privileges in Linux. We will also show you how to revert sudoers file back to the original configuration.
Table of Contents
Restrict Sudo Users to Run Authorized Commands
To restrict sudo users to ONLY run authorized commands, you can use the sudoers configuration file. On most Linux distributions, the sudoers file is located at /etc/sudoers file or /etc/sudoers.d/ directory.
Heads Up: Before making changes to the sudoers file, it's crucial to use caution, as incorrect configurations can lead to system issues. Always use the visudo command to edit the sudoers file, as it performs syntax checks before saving changes.
Here's how you can restrict sudo users to run specific commands:
1. It's highly recommended to backup the sudoers file before making any changes or edits to it. To backup sudoers file, run:
$ sudo cp /etc/sudoers /etc/sudoers.bak
By backing up the sudoers file, you can easily revert to a known-working configuration if errors occur during editing or in case of security incidents.
2. Open the sudoers file for editing using visudo command:
$ sudo visudo
3. Scroll down to the line where it says:
# Allow members of group sudo to execute any command %sudo ALL=(ALL:ALL) ALL
The above line means that members of the "sudo" group are allowed to execute any command with sudo privileges on any host and as any user or group. Essentially, it grants full sudo access to the users in the "sudo" group.
4. To allow the sudo users to execute only a specific command, for example apt, modify the line as shown below.
%sudo ALL=(ALL:ALL) /bin/apt

You can also specify multiple allowed commands for a user by separating them with commas:
%sudo ALL=(ALL:ALL) /path/to/allowed/command1,/path/to/allowed/command2
5. If you want to allow the user to run the allowed commands without entering a password, you can append NOPASSWD: before the command path. However, be cautious when using this option, as it might reduce the security of your system.
%sudo ALL=(ALL) NOPASSWD: /path/to/allowed/command
6. Once you've made the necessary changes, save and close the sudoers file.
7. Verify the syntax of your sudoers file before exiting visudo. If there are any syntax errors, visudo will prompt you to correct them.
After following these steps, all the members of the sudo group will only be able to execute the allowed commands with sudo privileges. Running all other commands with sudo privilege will be denied, even if the user is a member of sudo group.
Let us verify it by running the cat command with sudo privilege.
$ sudo cat /etc/sudoers
Sample Output:
[sudo] password for ostechnix: Sorry, user ostechnix is not allowed to execute '/usr/bin/cat /etc/sudoers' as root on debian12.ostechnix.lan.

Even though, the user 'ostechnix' is a member of sudo group, he can't run sudo cat /etc/sudoers command. Because, we restricted him to run only the apt command with sudo privilege.
Let us list all of the commands that the user ostechnix is allowed to run with sudo privileges.
$ sudo -lU ostechnix
[sudo] password for ostechnix:
Matching Defaults entries for ostechnix on debian12:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, use_pty
User ostechnix may run the following commands on debian12:
<strong><mark>(ALL : ALL) /bin/apt</mark></strong>

As you can see in the above output, the user ostechnix can run only apt command with sudo privilege.
Let us check if he can able to the apt command with sudo privilege.
$ sudo apt update

Yes, he has no problem on running the allowed command, which is apt in this case, with sudo rights. The user can also run all the sub-commands of apt, for example apt upgrade, apt full-upgrade etc.
Please note that this is applicable only for the commands run with sudo privilege. Executing any other commands without sudo will normally work.
Restoring Original sudoers File Configuration
If you want to revert the sudoers file back to the original configuration, you need to change it to the correct syntax that was originally present in the file. To do that, follow these steps:
1. Login as root user or switch to another sudo user who has full sudo privilege.
2. If you already have the backup, restore the sudoers file from the backup using the following command (assuming the backup file is in /etc directory).
$ sudo cp /etc/sudoers.bak /etc/sudoers
If you don't have backup, follow the subsequent steps.
3. Open the sudoers file for editing using visudo command. Make sure you're logged in as root or other sudo user.
$ sudo visudo
4. Locate the line that you want to modify. In our case, it's the line that grants sudo privileges to the sudo group and allows them to run /bin/apt.
5. Replace the current line with the original configuration that you want to restore. For example, if the current line is:
%sudo ALL=(ALL:ALL) /bin/apt
and you want to revert it back to the default configuration that grants full sudo privileges to the sudo group, it should be:
%sudo ALL=(ALL:ALL) ALL
6. Save and close the sudoers file.
7. Verify the syntax of your sudoers file before exiting visudo. If there are no syntax errors, the changes will be applied.
After making these changes, the sudo configuration will be modified back to the original settings, and the users will have the sudo privileges as they had before the changes were made.
Remember to be careful when modifying the sudoers file, as incorrect configurations can lead to issues with sudo access on your system. Always use visudo to edit the file to avoid syntax errors.
Conclusion
Restricting sudo users to run specific commands is a good way to improve the security of your Linux system. By limiting the commands that sudo users can run, you can reduce the risk of unauthorized access and system damage.
Related Read:
- How To Run Particular Commands Without Sudo Password In Linux
- How To Allow Or Deny Sudo Access To A Group In Linux
- How To Restrict Su Command To Authorized Users In Linux
- Run Commands As Another User Via Sudo In Linux
- How To Prevent Command Arguments With Sudo In Linux
- How To Run All Programs In A Directory Via Sudo In Linux
- How To Restore Sudo Privileges To A User
以上是如何限制sudo用戶在Linux中運行特定的授權命令的詳細內容。更多資訊請關注PHP中文網其他相關文章!
 如何在Linux中自動重新啟動失敗的服務Apr 28, 2025 am 09:39 AM
如何在Linux中自動重新啟動失敗的服務Apr 28, 2025 am 09:39 AM本指南詳細介紹瞭如何使用SystemD配置自動服務在Linux中重新啟動,從而增強了系統的可靠性並最大程度地減少停機時間。 系統管理員通常依靠此功能來確保關鍵服務,例如Web服務器(APA
 10個隱藏的Linux命令每個系統都應該知道Apr 28, 2025 am 09:35 AM
10個隱藏的Linux命令每個系統都應該知道Apr 28, 2025 am 09:35 AM作為Linux用戶,我們經常依賴常用的命令ls、grep、awk、sed和find來完成工作。但Linux擁有大量鮮為人知的命令,可以節省時間、自動化任務並簡化工作流程。 本文將探討一些被低估但卻功能強大的Linux命令,它們值得更多關注。 rename – 高效批量重命名文件 當您需要一次重命名多個文件時,rename命令是救星。無需使用包含mv的循環,rename允許您輕鬆應用複雜的重命名模式。 將所有.txt文件更改為.log。 rename 's/\.txt$/\.log/' *
 如何在Linux中的SystemD下列出所有運行服務Apr 28, 2025 am 09:29 AM
如何在Linux中的SystemD下列出所有運行服務Apr 28, 2025 am 09:29 AMLinux 系統提供各種系統服務(例如進程管理、登錄、syslog、cron 等)和網絡服務(例如遠程登錄、電子郵件、打印機、Web 託管、數據存儲、文件傳輸、域名解析(使用 DNS)、動態 IP 地址分配(使用 DHCP)等等)。 從技術上講,服務是在後台持續運行的進程或進程組(通常稱為 守護進程),等待傳入請求(尤其來自客戶端)。 Linux 支持不同的方式來管理(啟動、停止、重啟、啟用系統啟動時的自動啟動等)服務,通常通過進程或服務管理器。幾乎所有現代 Linux 發行版現在都使用相同的進
 Crossover 25:在Linux上運行Windows軟件和遊戲Apr 28, 2025 am 09:27 AM
Crossover 25:在Linux上運行Windows軟件和遊戲Apr 28, 2025 am 09:27 AM使用Crossover 25運行Windows軟件和遊戲 由於CodeWeavers的Crossover 25,在Linux上運行Windows應用程序和遊戲現在比以往任何時候都容易。 這個商業軟件解決方案讓Linux用戶運行各種各樣的風
![PCLOUD-最安全的雲存儲[優惠50%]](https://img.php.cn/upload/article/001/242/473/174580357418126.jpg?x-oss-process=image/resize,p_40) PCLOUD-最安全的雲存儲[優惠50%]Apr 28, 2025 am 09:26 AM
PCLOUD-最安全的雲存儲[優惠50%]Apr 28, 2025 am 09:26 AM使用PCLOUD保護數據:Linux安裝的綜合指南 領先的安全雲存儲服務PCloud提供了一個可靠的平台來管理您的文件和數據。本指南詳細介紹了Linux系統上的安裝過程。 關於
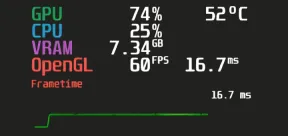 MANGOHUD-監視FPS,Linux遊戲中的CPU和GPU使用情況Apr 28, 2025 am 09:25 AM
MANGOHUD-監視FPS,Linux遊戲中的CPU和GPU使用情況Apr 28, 2025 am 09:25 AMMangoHud:實時監控Linux遊戲性能的利器 MangoHud是一款功能強大且輕量級的工具,專為遊戲玩家、開發者以及任何希望實時監控系統性能的用戶而設計。它作為Vulkan和OpenGL應用程序的疊加層,顯示FPS、CPU和GPU使用率、溫度等重要信息。本文將探討MangoHud的功能、工作原理以及使用方法,並提供在Linux系統上安裝和配置MangoHud的分步說明。 MangoHud是什麼? MangoHud是一個開源項目,可在GitHub上獲取,旨在提供一種簡單且可自定義的方式來監
 5必不可少的Linux命令行檔案工具 - 第1部分Apr 28, 2025 am 09:23 AM
5必不可少的Linux命令行檔案工具 - 第1部分Apr 28, 2025 am 09:23 AM管理存檔文件是Linux中的常見任務。本文是兩部分系列中的第一篇,探討了五種強大的命令行檔案工具,詳細介紹了他們的功能和示例的用法。 1。焦油命令:多功能存檔實用程序 t
 在Linux中比較文件的前7個工具(示例)Apr 28, 2025 am 09:21 AM
在Linux中比較文件的前7個工具(示例)Apr 28, 2025 am 09:21 AM本指南探討了用於比較Linux中文本文件的各種方法,Linux是系統管理員和開發人員的關鍵任務。 我們將介紹命令行工具和視覺差異工具,突出顯示其優勢和適當的用例。 假設


熱AI工具

Undresser.AI Undress
人工智慧驅動的應用程序,用於創建逼真的裸體照片

AI Clothes Remover
用於從照片中去除衣服的線上人工智慧工具。

Undress AI Tool
免費脫衣圖片

Clothoff.io
AI脫衣器

Video Face Swap
使用我們完全免費的人工智慧換臉工具,輕鬆在任何影片中換臉!

熱門文章

熱工具

MantisBT
Mantis是一個易於部署的基於Web的缺陷追蹤工具,用於幫助產品缺陷追蹤。它需要PHP、MySQL和一個Web伺服器。請查看我們的演示和託管服務。

SecLists
SecLists是最終安全測試人員的伙伴。它是一個包含各種類型清單的集合,這些清單在安全評估過程中經常使用,而且都在一個地方。 SecLists透過方便地提供安全測試人員可能需要的所有列表,幫助提高安全測試的效率和生產力。清單類型包括使用者名稱、密碼、URL、模糊測試有效載荷、敏感資料模式、Web shell等等。測試人員只需將此儲存庫拉到新的測試機上,他就可以存取所需的每種類型的清單。

mPDF
mPDF是一個PHP庫,可以從UTF-8編碼的HTML產生PDF檔案。原作者Ian Back編寫mPDF以從他的網站上「即時」輸出PDF文件,並處理不同的語言。與原始腳本如HTML2FPDF相比,它的速度較慢,並且在使用Unicode字體時產生的檔案較大,但支援CSS樣式等,並進行了大量增強。支援幾乎所有語言,包括RTL(阿拉伯語和希伯來語)和CJK(中日韓)。支援嵌套的區塊級元素(如P、DIV),

Atom編輯器mac版下載
最受歡迎的的開源編輯器

SublimeText3 Mac版
神級程式碼編輯軟體(SublimeText3)






