In Debian, managing user privileges and administrative access is crucial for maintaining a secure and efficient system. By granting users the ability to execute administrative tasks without relying on the root account, you can enhance security, control access to sensitive operations, and maintain an audit trail of user activity. This detailed guide walks you through the steps to add, delete, and grant sudo privileges to users in Debian Linux.
Whether you're setting up a new Debian system or need to manage user accounts on an existing installation, this step-by-step tutorial is designed to provide clear instructions and explanations that even beginners can follow.
By the end of this guide, you'll have a solid understanding of how to create new user accounts, grant them sudo access, and remove users when necessary.
Before getting into the topic of adding, deleting, and granting sudo privileges to users in Debian, it's essential to understand what sudo is and the advantages it offers.
Table of Contents
1. What is Sudo?
The sudo (Superuser Do) command in Linux and Unix-like systems allows authorized users to execute commands with the privileges of the superuser or another user. It enables users to perform administrative tasks without logging in as the root user permanently.
The primary purpose of sudo is to provide a safer and more controlled approach to system administration. Instead of granting full root access to users, sudo enables privilege separation, limiting the scope of elevated privileges to specific commands or operations.
2. Advantages of Sudo Users
Here are some key aspects regarding sudo and the advantages of having a sudo user:
1. Privilege Separation
By default, Linux systems have a root user account with full administrative privileges. However, logging in as the root user can be risky because any command executed has unrestricted access to the entire system.
Sudo provides a way to separate regular user accounts from privileged tasks, allowing users to perform administrative actions only when needed.
2. Limited Privilege Escalation
Sudo allows specific users or groups to execute specific commands with elevated privileges. This provides a controlled and auditable way to grant temporary administrative access to trusted users.
Users can execute individual commands or a series of commands with sudo by authenticating themselves with their own password, rather than the root password.
3. Auditing and Accountability
Sudo logs all executed commands, providing an audit trail for system administrators. This audit trail helps track who executed which commands and when, enhancing system security and accountability.
The logs generated by sudo can be analyzed to investigate security incidents, troubleshoot issues, and monitor user activity.
4. Fine-Grained Access Control
With sudo, system administrators can define granular access control policies for different users or groups. This allows them to specify precisely which commands or operations each user can perform with elevated privileges.
Access control can be customized based on factors such as user roles, specific systems or services, and even specific command options.
5. Reduced Risk of Accidental Damage
Using sudo helps mitigate the risk of accidental damage caused by executing privileged commands. With sudo, users need to deliberately prefix a command with sudo to run it with elevated privileges, reducing the likelihood of unintentional system modifications or deletions.
It provides an extra layer of safety by prompting users for authentication before executing privileged operations, ensuring they are aware of the consequences of their actions.
6. Collaboration and Delegation
Sudo facilitates collaboration among system administrators by allowing them to delegate specific administrative tasks to other users without sharing the root password.
By assigning sudo privileges to trusted users, the workload can be distributed, and routine administrative tasks can be performed by designated individuals without requiring full root access.
In summary, having a sudo user provides a more secure and controlled approach to system administration. It enhances security, accountability, and flexibility by enabling limited privilege escalation, fine-grained access control, auditing, and delegation of administrative tasks.
3. Add a New User in Debian
To create a new sudo user in Debian, you need to have either an existing sudo user or root access to the system. This requirement ensures that only authorized users can grant sudo privileges to others.
In order to add a new user, follow these steps:
Log in to your Debian system using an existing sudo user account or as the root user. Open a terminal or connect to your Debian system via SSH.
If you have an existing sudo user:
Run the following command to create a new user:
$ sudo adduser senthil
Replace "senthil" with the desired username for the new sudo user.
Enter a strong password for the new user when prompted.
Provide any additional information requested during the user creation process.
If you have root access:
If the currently logged-in user does not have sudo rights, you will need to switch to the root account in order to create new sudo users.
Use any one of the following commands to switch to root user.
$ su -l
Or
$ su -
By using su -l or su -, the root shell is initialized with an environment similar to a normal 'login' shell. This means that the root user's $PATH variable is correctly initialized, ensuring that system directories such as /sbin are included.
Next, run the following command to create a new user:
# adduser senthil
Again, replace "senthil" with your own username.
You will be prompted to set a password for the new user. Enter a strong password and confirm it.
Additional information about the new user, such as their full name, phone number, etc., may be requested. You can enter the information or leave it blank by pressing Enter.
Adding user `senthil' ... Adding new group `senthil' (1001) ... Adding new user `senthil' (1001) with group `senthil (1001)' ... Creating home directory `/home/senthil' ... Copying files from `/etc/skel' ... New password: Retype new password: passwd: password updated successfully Changing the user information for senthil Enter the new value, or press ENTER for the default Full Name []: Room Number []: Work Phone []: Home Phone []: Other []: Is the information correct? [Y/n] y Adding new user `senthil' to supplemental / extra groups `users' ... Adding user `senthil' to group `users' ...

3.1. Check Sudo Privileges for a Specific User
After creating a new user named "senthil", it's important to note that this user does not have sudo access by default. Without sudo privileges, the user won't be able to perform administrative tasks.
To verify whether a user has sudo access or not, you can use the following command:
# sudo -l -U senthil
Replace "senthil" with the actual username you want to check.
Sample output:
User senthil is not allowed to run sudo on debian12.

As you can see, the user "senthil" has not been granted sudo privileges yet. If the user "senthil" has sudo access, the output will show the allowed commands and their associated restrictions, if any.
In the next steps, we will cover how to grant sudo privileges to the user "senthil" so they can perform administrative tasks.
4. Grant Sudo Privileges to Users in Debian
Add the newly created user to sudo group using the following command:
If you have an existing sudo user:
$ sudo adduser senthil sudo
If you have root access:
# adduser senthil sudo
Sample output:
Adding user `senthil' to group `sudo' ... Done.

We granted sudo permission to the user "senthil".
You can also the following command to add a user to sudo group.
# sudo usermod -aG sudo senthil
Now verify if the user is added in the sudo group, using command
# sudo -l -U senthil
Sample output:
Matching Defaults entries for senthil on debian12:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
use_pty
User senthil may run the following commands on debian12:
<strong><mark>(ALL : ALL) ALL</mark></strong>

Here, the line (ALL : ALL) ALL in the above output indicates that the user "senthil" can run any command (ALL) as any user (ALL) with all available privileges.
The output confirms that the user "senthil" has been granted unrestricted sudo privileges on the Debian 12 system, allowing him to run any command as any user with full administrative capabilities.
If you view the contents of the sudoers file;
$ sudo cat /etc/sudoers
You would see some lines like below.
# User privilege specification root ALL=(ALL:ALL) ALL # Members of the admin group may gain root privileges %admin ALL=(ALL) ALL # Allow members of group sudo to execute any command <strong><mark>%sudo ALL=(ALL:ALL) ALL</mark></strong> # See sudoers(5) for more information on "@include" directives: @includedir /etc/sudoers.d
The directive %sudo ALL=(ALL:ALL) ALL in the /etc/sudoers file is a rule that specifies the sudo privileges for members of the "sudo" group. Let's break down what each part of the directive means:
- %sudo: This signifies that the rule applies to all users who are members of the "sudo" group. The % character denotes a group name.
- ALL=(ALL:ALL): This portion defines the scope of the sudo rule. It indicates that the rule applies to any host (ALL) and allows users in the "sudo" group to run commands as any user and any group.
- The first "ALL" represents the hosts or machines on which the sudo rule is applicable. In this case, "ALL" means the rule applies to any host. It allows members of the "sudo" group to execute commands with sudo privileges from any machine.
- The second "ALL" represents the users or accounts as whom the commands can be executed. "ALL" means the members of the "sudo" group can run commands as any user on the system.
- The third "ALL" represents the groups that the sudo commands can be executed as. Again, "ALL" means that the members of the "sudo" group can execute commands as any group on the system.
- ALL: This specifies that the members of the "sudo" group can run any command.
In summary, the directive %sudo ALL=(ALL:ALL) ALL allows any user who is a member of the "sudo" group to execute any command with full administrative privileges. It grants broad sudo access to the users in the "sudo" group, enabling them to perform a wide range of administrative tasks on the system.
Since the user "senthil" is a member of "sudo" group, he can now run any command on any host. To put this in other word, he is one of the administrator.
5. Verify Sudo Privilege of Users
To verify if a user has the ability to perform administrative tasks with sudo, Log out from the current user session. On the login screen, select the new user you created. Enter the password for the new user and log in.
Alternatively, you can quickly switch to the new user using the following command:
# sudo -i -u senthil
This command will instantly switch you to the specified user, in this case, "senthil".
Once you are switched to the user, run any commands with the sudo prefix to perform administrative tasks. For example:
$ sudo apt update

As you witnessed in the above output, the user "senthil" has the ability to run administrative tasks with sudo privilege.
6. Remove Sudo Access from Users
Removing sudo access from a user in Debian systems is a delicate process that requires caution. It's important to ensure that you do not remove the real administrator from the "sudo" group, as there should always be at least one sudo user in the system.
To revoke sudo permissions from a user, follow these steps:
Make sure you are logged out from the user's session ("senthil") and logged in as another user with sudo privileges.
To remove the user "senthil" from the "sudo" group, use the following command:
$ sudo deluser senthil sudo
This command will revoke the user's sudo permissions by removing them from the "sudo" group. Note that this action does not permanently delete the user from the system.
Sample output:
Removing user `senthil' from group `sudo' ... Done.
Alternatively, you can use the following command to revoke sudo permissions:
$ sudo gpasswd -d senthil sudo
Running this command will have the same effect of removing the user "senthil" from the "sudo" group.
After executing either of these commands, the user "senthil" will no longer have sudo access and will be considered a regular user without administrative privileges.
To verify if the user has indeed been removed from the "sudo" group, you can run the following command:
$ sudo -l -U senthil
This command will display the user's sudo privileges. If the user is no longer listed as having sudo access, it confirms that the sudo permissions have been successfully revoked.
User senthil is not allowed to run sudo on debian12.

The user "senthil" is now removed from sudoer list.
7. Remove Users Permanently
Please exercise caution when permanently deleting users from the system, as this action is not reversible. Double-check that you are removing the correct user, and ensure that you have taken appropriate backups or precautions to prevent any unintended data loss.
To permanently delete users from a Linux system, including their home directory and mail spool, follow these steps:
Ensure that you are logged in as the root user or a user with sudo privileges.
To delete a user, use the following command:
$ sudo deluser senthil
Replace "senthil" with the actual username of the user you want to remove.
This command will remove the specified user from the system, including their user account details. However, their home directory and mail spool will remain intact.
If you want to remove the user's home directory and mail spool along with their account, use the --remove-home option:
$ sudo deluser --remove-home senthil
This command ensures that not only the user account but also their home directory and mail spool are deleted.
Conclusion
Managing user privileges and granting sudo access in Debian systems is an essential aspect of maintaining system security and controlling administrative tasks. By following the step-by-step instructions provided, even beginners can successfully add, grant sudo access, and manage users in Debian systems.
Remember to exercise caution when using sudo, grant privileges only to trusted users, and regularly review sudo logs to monitor user activity and identify any potential security issues.
Related Read:
- Add, Delete And Grant Sudo Privileges To Users In Alpine Linux
- Add, Delete And Grant Sudo Privileges To Users In Arch Linux
- Add, Delete And Grant Sudo Privileges To Users In CentOS
- Add, Delete And Grant Sudo Privileges To Users In Fedora
- Add, Delete And Grant Sudo Privileges To Users In Ubuntu
- How To Allow Or Deny Sudo Access To A Group In Linux
以上是如何向Debian 12中的用戶添加,刪除和授予Sudo特權的詳細內容。更多資訊請關注PHP中文網其他相關文章!
 對於各種任務,Linux和Windows之間的性能有何不同?May 14, 2025 am 12:03 AM
對於各種任務,Linux和Windows之間的性能有何不同?May 14, 2025 am 12:03 AMLinux在服務器和開發環境中性能優異,而Windows在桌面和遊戲領域表現更好。 1)Linux的文件系統在處理大量小文件時表現出色。 2)Linux在高並發和高吞吐量網絡場景中表現優異。 3)Linux的內存管理在服務器環境中更具優勢。 4)Linux在執行命令行和腳本任務時效率高,而Windows在圖形界面和多媒體應用上表現更好。
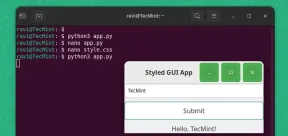 如何使用Pygobject在Linux中創建GUI應用程序May 13, 2025 am 11:09 AM
如何使用Pygobject在Linux中創建GUI應用程序May 13, 2025 am 11:09 AM創建圖形用戶界面(GUI)應用程序是使您的想法栩栩如生並使您的程序更加用戶友好的絕佳方法。 PygoBject是一個Python庫,允許開發人員使用Linux桌面上創建GUI應用程序
 如何在Arch Linux中使用PhpMyAdmin安裝燈泡May 13, 2025 am 11:01 AM
如何在Arch Linux中使用PhpMyAdmin安裝燈泡May 13, 2025 am 11:01 AMArch Linux提供了靈活的尖端系統環境,是一種非常適合在小型非關鍵系統上開發Web應用程序的解決方案,因為是完全開源的,並且在內核上提供了最新的最新版本
 如何在Arch Linux上安裝LEMP(NGINX,PHP,MARIADB)May 13, 2025 am 10:43 AM
如何在Arch Linux上安裝LEMP(NGINX,PHP,MARIADB)May 13, 2025 am 10:43 AM由於其滾動釋放模型,該模型包含尖端軟件Arch Linux的設計和開發以作為服務器運行以提供可靠的網絡服務,因為它需要額外的時間進行維護,持續的升級和明智的FI
![12必備Linux控制台[終端]文件管理器](https://img.php.cn/upload/article/001/242/473/174710245395762.png?x-oss-process=image/resize,p_40) 12必備Linux控制台[終端]文件管理器May 13, 2025 am 10:14 AM
12必備Linux控制台[終端]文件管理器May 13, 2025 am 10:14 AMLinux控制台文件管理器在日常任務,在本地計算機上管理文件時或連接到遠程時,可能非常有幫助。目錄的視覺控制台表示可以幫助我們快速執行文件/文件夾操作和SAV
 Qbittorrent:強大的開源Bittorrent客戶端May 13, 2025 am 10:12 AM
Qbittorrent:強大的開源Bittorrent客戶端May 13, 2025 am 10:12 AMQbittorrent是一個受歡迎的開源Bittorrent客戶端,允許用戶通過Internet下載和共享文件。最新版本Qbittorrent 5.0最近發行了,並帶有新功能和改進。 本文將
 ARCH Linux上的設置NGINX虛擬主機,PhpMyAdmin和SSLMay 13, 2025 am 10:03 AM
ARCH Linux上的設置NGINX虛擬主機,PhpMyAdmin和SSLMay 13, 2025 am 10:03 AM以前的Arch Linux LEMP文章僅涵蓋了基本內容,從安裝網絡服務(NGINX,PHP,MYSQL和PHPMYADMIN)以及配置MySQL Server和PhpMyAdmin所需的最低安全性。 這個主題與形式嚴格有關
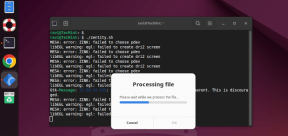 Zenity:在外殼腳本中構建GTK對話框May 13, 2025 am 09:38 AM
Zenity:在外殼腳本中構建GTK對話框May 13, 2025 am 09:38 AMZenity是一種工具,可讓您使用命令行在Linux中創建圖形對話框。它使用GTK,這是一種用於創建圖形用戶界面(GUI)的工具包,使您可以輕鬆地將視覺元素添加到您的腳本中。 Zenity可能非常


熱AI工具

Undresser.AI Undress
人工智慧驅動的應用程序,用於創建逼真的裸體照片

AI Clothes Remover
用於從照片中去除衣服的線上人工智慧工具。

Undress AI Tool
免費脫衣圖片

Clothoff.io
AI脫衣器

Video Face Swap
使用我們完全免費的人工智慧換臉工具,輕鬆在任何影片中換臉!

熱門文章

熱工具

SublimeText3 Linux新版
SublimeText3 Linux最新版

SecLists
SecLists是最終安全測試人員的伙伴。它是一個包含各種類型清單的集合,這些清單在安全評估過程中經常使用,而且都在一個地方。 SecLists透過方便地提供安全測試人員可能需要的所有列表,幫助提高安全測試的效率和生產力。清單類型包括使用者名稱、密碼、URL、模糊測試有效載荷、敏感資料模式、Web shell等等。測試人員只需將此儲存庫拉到新的測試機上,他就可以存取所需的每種類型的清單。

ZendStudio 13.5.1 Mac
強大的PHP整合開發環境

DVWA
Damn Vulnerable Web App (DVWA) 是一個PHP/MySQL的Web應用程序,非常容易受到攻擊。它的主要目標是成為安全專業人員在合法環境中測試自己的技能和工具的輔助工具,幫助Web開發人員更好地理解保護網路應用程式的過程,並幫助教師/學生在課堂環境中教授/學習Web應用程式安全性。 DVWA的目標是透過簡單直接的介面練習一些最常見的Web漏洞,難度各不相同。請注意,該軟體中

記事本++7.3.1
好用且免費的程式碼編輯器






