 Tutorial sistem
Tutorial sistem LINUX
LINUX Cara Menghadkan Pengguna Sudo Untuk Menjalankan Perintah Dibenarkan Di Linux
Cara Menghadkan Pengguna Sudo Untuk Menjalankan Perintah Dibenarkan Di LinuxCara Menghadkan Pengguna Sudo Untuk Menjalankan Perintah Dibenarkan Di Linux
The sudo command allows users to run commands with root privileges. This can be a powerful tool, but it can also be a security risk if not used carefully. One way to mitigate this risk is to allow sudo users to run particular authorized commands. In this guide, we will show you how to restrict sudo users to run specific commands with sudo privileges in Linux. We will also show you how to revert sudoers file back to the original configuration.
Table of Contents
Restrict Sudo Users to Run Authorized Commands
To restrict sudo users to ONLY run authorized commands, you can use the sudoers configuration file. On most Linux distributions, the sudoers file is located at /etc/sudoers file or /etc/sudoers.d/ directory.
Heads Up: Before making changes to the sudoers file, it's crucial to use caution, as incorrect configurations can lead to system issues. Always use the visudo command to edit the sudoers file, as it performs syntax checks before saving changes.
Here's how you can restrict sudo users to run specific commands:
1. It's highly recommended to backup the sudoers file before making any changes or edits to it. To backup sudoers file, run:
$ sudo cp /etc/sudoers /etc/sudoers.bak
By backing up the sudoers file, you can easily revert to a known-working configuration if errors occur during editing or in case of security incidents.
2. Open the sudoers file for editing using visudo command:
$ sudo visudo
3. Scroll down to the line where it says:
# Allow members of group sudo to execute any command %sudo ALL=(ALL:ALL) ALL
The above line means that members of the "sudo" group are allowed to execute any command with sudo privileges on any host and as any user or group. Essentially, it grants full sudo access to the users in the "sudo" group.
4. To allow the sudo users to execute only a specific command, for example apt, modify the line as shown below.
%sudo ALL=(ALL:ALL) /bin/apt

You can also specify multiple allowed commands for a user by separating them with commas:
%sudo ALL=(ALL:ALL) /path/to/allowed/command1,/path/to/allowed/command2
5. If you want to allow the user to run the allowed commands without entering a password, you can append NOPASSWD: before the command path. However, be cautious when using this option, as it might reduce the security of your system.
%sudo ALL=(ALL) NOPASSWD: /path/to/allowed/command
6. Once you've made the necessary changes, save and close the sudoers file.
7. Verify the syntax of your sudoers file before exiting visudo. If there are any syntax errors, visudo will prompt you to correct them.
After following these steps, all the members of the sudo group will only be able to execute the allowed commands with sudo privileges. Running all other commands with sudo privilege will be denied, even if the user is a member of sudo group.
Let us verify it by running the cat command with sudo privilege.
$ sudo cat /etc/sudoers
Sample Output:
[sudo] password for ostechnix: Sorry, user ostechnix is not allowed to execute '/usr/bin/cat /etc/sudoers' as root on debian12.ostechnix.lan.

Even though, the user 'ostechnix' is a member of sudo group, he can't run sudo cat /etc/sudoers command. Because, we restricted him to run only the apt command with sudo privilege.
Let us list all of the commands that the user ostechnix is allowed to run with sudo privileges.
$ sudo -lU ostechnix
[sudo] password for ostechnix:
Matching Defaults entries for ostechnix on debian12:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, use_pty
User ostechnix may run the following commands on debian12:
<strong><mark>(ALL : ALL) /bin/apt</mark></strong>

As you can see in the above output, the user ostechnix can run only apt command with sudo privilege.
Let us check if he can able to the apt command with sudo privilege.
$ sudo apt update

Yes, he has no problem on running the allowed command, which is apt in this case, with sudo rights. The user can also run all the sub-commands of apt, for example apt upgrade, apt full-upgrade etc.
Please note that this is applicable only for the commands run with sudo privilege. Executing any other commands without sudo will normally work.
Restoring Original sudoers File Configuration
If you want to revert the sudoers file back to the original configuration, you need to change it to the correct syntax that was originally present in the file. To do that, follow these steps:
1. Login as root user or switch to another sudo user who has full sudo privilege.
2. If you already have the backup, restore the sudoers file from the backup using the following command (assuming the backup file is in /etc directory).
$ sudo cp /etc/sudoers.bak /etc/sudoers
If you don't have backup, follow the subsequent steps.
3. Open the sudoers file for editing using visudo command. Make sure you're logged in as root or other sudo user.
$ sudo visudo
4. Locate the line that you want to modify. In our case, it's the line that grants sudo privileges to the sudo group and allows them to run /bin/apt.
5. Replace the current line with the original configuration that you want to restore. For example, if the current line is:
%sudo ALL=(ALL:ALL) /bin/apt
and you want to revert it back to the default configuration that grants full sudo privileges to the sudo group, it should be:
%sudo ALL=(ALL:ALL) ALL
6. Save and close the sudoers file.
7. Verify the syntax of your sudoers file before exiting visudo. If there are no syntax errors, the changes will be applied.
After making these changes, the sudo configuration will be modified back to the original settings, and the users will have the sudo privileges as they had before the changes were made.
Remember to be careful when modifying the sudoers file, as incorrect configurations can lead to issues with sudo access on your system. Always use visudo to edit the file to avoid syntax errors.
Conclusion
Restricting sudo users to run specific commands is a good way to improve the security of your Linux system. By limiting the commands that sudo users can run, you can reduce the risk of unauthorized access and system damage.
Related Read:
- How To Run Particular Commands Without Sudo Password In Linux
- How To Allow Or Deny Sudo Access To A Group In Linux
- How To Restrict Su Command To Authorized Users In Linux
- Run Commands As Another User Via Sudo In Linux
- How To Prevent Command Arguments With Sudo In Linux
- How To Run All Programs In A Directory Via Sudo In Linux
- How To Restore Sudo Privileges To A User
Atas ialah kandungan terperinci Cara Menghadkan Pengguna Sudo Untuk Menjalankan Perintah Dibenarkan Di Linux. Untuk maklumat lanjut, sila ikut artikel berkaitan lain di laman web China PHP!
 Bagaimanakah proses boot berbeza antara Linux dan Windows?Apr 29, 2025 am 12:12 AM
Bagaimanakah proses boot berbeza antara Linux dan Windows?Apr 29, 2025 am 12:12 AMProses permulaan Linux termasuk: 1. Proses permulaan Windows termasuk: 1. Mula Bios/UEFI, 2. Beban WindowsBootManager, 3. Beban winload.exe, 4. Beban tonskrnl.exe dan Hal, 5. Linux menyediakan lebih banyak pilihan penyesuaian, sementara Windows memberi perhatian lebih kepada pengalaman dan kestabilan pengguna.
 Cara memulakan semula perkhidmatan gagal secara automatik di LinuxApr 28, 2025 am 09:39 AM
Cara memulakan semula perkhidmatan gagal secara automatik di LinuxApr 28, 2025 am 09:39 AMPanduan ini memperincikan bagaimana untuk mengkonfigurasi perkhidmatan automatik dimulakan semula di Linux menggunakan SystemD, meningkatkan kebolehpercayaan sistem dan meminimumkan downtime. Pentadbir sistem sering bergantung pada fungsi ini untuk memastikan perkhidmatan kritikal, seperti pelayan web (APA
 10 Hidden Linux Commands Every Sysadmin Should KnowApr 28, 2025 am 09:35 AM
10 Hidden Linux Commands Every Sysadmin Should KnowApr 28, 2025 am 09:35 AM作为Linux用户,我们经常依赖常用的命令ls、grep、awk、sed和find来完成工作。但Linux拥有大量鲜为人知的命令,可以节省时间、自动化任务并简化工作流程。 本文将探讨一些被低估但却功能强大的Linux命令,它们值得更多关注。 rename – 高效批量重命名文件 当您需要一次重命名多个文件时,rename命令是救星。无需使用包含mv的循环,rename允许您轻松应用复杂的重命名模式。 将所有.txt文件更改为.log。 rename 's/\.txt$/\.log/' *
 Cara Menyenaraikan Semua Perkhidmatan Berjalan Di Bawah Systemd di LinuxApr 28, 2025 am 09:29 AM
Cara Menyenaraikan Semua Perkhidmatan Berjalan Di Bawah Systemd di LinuxApr 28, 2025 am 09:29 AMSistem Linux menyediakan pelbagai perkhidmatan sistem (seperti pengurusan proses, log masuk, syslog, cron, dll) dan perkhidmatan rangkaian (seperti log masuk jauh, e -mel, pencetak, hosting web, penyimpanan data, pemindahan fail, resolusi nama domain (menggunakan DNS), peruntukan alamat IP dinamik (menggunakan DHCP), dan sebagainya). Secara teknikal, perkhidmatan adalah proses atau kumpulan proses (biasanya dikenali sebagai daemon) yang berjalan secara berterusan di latar belakang, menunggu permintaan masuk (terutama dari pelanggan). Linux menyokong cara yang berbeza untuk menguruskan perkhidmatan (mula, berhenti, memulakan semula, membolehkan permulaan automatik pada permulaan sistem, dll.), Biasanya melalui proses atau pengurus perkhidmatan. Hampir semua pengagihan Linux moden kini menggunakannya
 Crossover 25: Jalankan perisian dan permainan Windows di LinuxApr 28, 2025 am 09:27 AM
Crossover 25: Jalankan perisian dan permainan Windows di LinuxApr 28, 2025 am 09:27 AMJalankan perisian dan permainan Windows di Linux dengan Crossover 25 Running Windows Applications and Games di Linux kini lebih mudah dari sebelumnya, terima kasih kepada Crossover 25 dari CodeWeavers. Penyelesaian perisian komersial ini membolehkan pengguna Linux menjalankan pelbagai jenis angin
![PCLOUD - Penyimpanan awan yang paling selamat [tawaran off 50%]](https://img.php.cn/upload/article/001/242/473/174580357418126.jpg?x-oss-process=image/resize,p_40) PCLOUD - Penyimpanan awan yang paling selamat [tawaran off 50%]Apr 28, 2025 am 09:26 AM
PCLOUD - Penyimpanan awan yang paling selamat [tawaran off 50%]Apr 28, 2025 am 09:26 AMSelamatkan data anda dengan pcloud: panduan komprehensif untuk pemasangan linux Pcloud, perkhidmatan penyimpanan awan yang selamat, menyediakan platform yang mantap untuk menguruskan fail dan data anda. Panduan ini memperincikan proses pemasangan pada sistem Linux. Mengenai
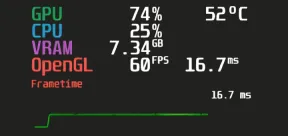 Mangohud - Monitor FPS, CPU & GPU penggunaan dalam permainan LinuxApr 28, 2025 am 09:25 AM
Mangohud - Monitor FPS, CPU & GPU penggunaan dalam permainan LinuxApr 28, 2025 am 09:25 AMMangohud: Alat yang berkuasa untuk pemantauan masa nyata prestasi permainan Linux Mangohud adalah alat yang kuat dan ringan yang direka untuk pemain, pemaju, dan sesiapa sahaja yang ingin memantau prestasi sistem dalam masa nyata. Ia bertindak sebagai overlay untuk aplikasi Vulkan dan OpenGL, memaparkan maklumat penting seperti FPS, CPU dan penggunaan GPU, suhu, dan lain-lain. Artikel ini akan meneroka fungsi, prinsip kerja dan penggunaan Mangohud, dan memberikan arahan langkah demi langkah untuk memasang dan mengkonfigurasi mangoS pada sistem linux. Apa itu mangohud? Mangohud adalah projek sumber terbuka yang tersedia di GitHub dan bertujuan untuk menyediakan cara yang mudah dan disesuaikan untuk memantau
 5 Mesti-tahu Alat Arkib Barisan Perintah Linux-Bahagian 1Apr 28, 2025 am 09:23 AM
5 Mesti-tahu Alat Arkib Barisan Perintah Linux-Bahagian 1Apr 28, 2025 am 09:23 AMMenguruskan fail yang diarkibkan adalah tugas biasa di Linux. Artikel ini, yang pertama dalam siri dua bahagian, meneroka lima alat arkib baris arahan yang kuat, memperincikan ciri dan penggunaannya dengan contoh. 1. Perintah tar: utiliti pengarkiban serba boleh t


Alat AI Hot

Undresser.AI Undress
Apl berkuasa AI untuk mencipta foto bogel yang realistik

AI Clothes Remover
Alat AI dalam talian untuk mengeluarkan pakaian daripada foto.

Undress AI Tool
Gambar buka pakaian secara percuma

Clothoff.io
Penyingkiran pakaian AI

Video Face Swap
Tukar muka dalam mana-mana video dengan mudah menggunakan alat tukar muka AI percuma kami!

Artikel Panas

Alat panas

SecLists
SecLists ialah rakan penguji keselamatan muktamad. Ia ialah koleksi pelbagai jenis senarai yang kerap digunakan semasa penilaian keselamatan, semuanya di satu tempat. SecLists membantu menjadikan ujian keselamatan lebih cekap dan produktif dengan menyediakan semua senarai yang mungkin diperlukan oleh penguji keselamatan dengan mudah. Jenis senarai termasuk nama pengguna, kata laluan, URL, muatan kabur, corak data sensitif, cangkerang web dan banyak lagi. Penguji hanya boleh menarik repositori ini ke mesin ujian baharu dan dia akan mempunyai akses kepada setiap jenis senarai yang dia perlukan.

Versi Mac WebStorm
Alat pembangunan JavaScript yang berguna

SublimeText3 versi Mac
Perisian penyuntingan kod peringkat Tuhan (SublimeText3)

Dreamweaver Mac版
Alat pembangunan web visual

Muat turun versi mac editor Atom
Editor sumber terbuka yang paling popular






