Maison >Opération et maintenance >exploitation et maintenance Linux >Qu'est-ce que Linux Openssl
Qu'est-ce que Linux Openssl
- 青灯夜游original
- 2023-04-18 11:06:433555parcourir
Sous Linux, openssl est un outil de ligne de commande extrêmement puissant qui peut être utilisé pour effectuer de nombreuses tâches liées au système de clé publique et à HTTPS. openssl a deux modes de fonctionnement : le mode interactif et le mode batch ; entrez directement openssl et appuyez sur Entrée pour entrer en mode interactif, entrez openssl avec les options de commande pour entrer en mode batch.
L'environnement d'exploitation de ce tutoriel : système linux7.3, ordinateur Dell G3.
1. Introduction à la commande openssl
openssl est un outil de ligne de commande extrêmement puissant qui peut être utilisé pour effectuer de nombreuses tâches liées à l'infrastructure à clé publique (infrastructure à clé publique) et HTTPS. openssl est une puissante bibliothèque cryptographique Secure Sockets Layer, comprenant les principaux algorithmes cryptographiques, les fonctions de gestion d'encapsulation de clés et de certificats couramment utilisées et les protocoles SSL, et fournit une multitude d'applications à des fins de test ou à d'autres fins.
openssl dispose de deux modes de fonctionnement : le mode interactif et le mode batch. Entrez directement openssl et appuyez sur Entrée pour passer en mode interactif, entrez openssl avec les options de commande pour passer en mode batch.
L'ensemble du progiciel openssl peut être grossièrement divisé en trois parties fonctionnelles principales : bibliothèque d'algorithmes cryptographiques, bibliothèque de protocoles SSL et applications. La structure des répertoires d'openssl est naturellement planifiée autour de ces trois parties fonctionnelles. Ce que fait la commande openssl :
- Création et gestion des clés privées, des clés publiques et des paramètres
- Opérations de chiffrement par clé publique
- Création de certificats X.509, CSR et CRL
- Calcul des résumés de messages
- Utilisation de mots de passe pour le chiffrement et décryptage
- Tests client et serveur SSL/TLS
- Traitement des e-mails signés ou cryptés S/MIME
- Demande d'horodatage, génération et vérification
Exemples d'utilisation
1. Obtenez de l'aide sur les commandes en mode
OpenSSL> help Standard commands asn1parse ca ciphers cms crl crl2pkcs7 dgst dhparam dsa dsaparam ec ecparam enc engine errstr gendsa genpkey genrsa help list nseq ocsp passwd pkcs12 pkcs7 pkcs8 pkey pkeyparam pkeyutl prime rand rehash req rsa rsautl s_client s_server s_time sess_id smime speed spkac srp storeutl ts verify version x509 Message Digest commands (see the `dgst’ command for more details) blake2b512 blake2s256 gost md4 md5 mdc2 rmd160 sha1 sha224 sha256 sha3-224 sha3-256 sha3-384 sha3-512 sha384 sha512 sha512-224 sha512-256 shake128 shake256 sm3 Cipher commands (see the `enc’ command for more details) aes-128-cbc aes-128-ecb aes-192-cbc aes-192-ecb aes-256-cbc aes-256-ecb aria-128-cbc aria-128-cfb aria-128-cfb1 aria-128-cfb8 aria-128-ctr aria-128-ecb aria-128-ofb aria-192-cbc aria-192-cfb aria-192-cfb1 aria-192-cfb8 aria-192-ctr aria-192-ecb aria-192-ofb aria-256-cbc aria-256-cfb aria-256-cfb1 aria-256-cfb8 aria-256-ctr aria-256-ecb aria-256-ofb base64 bf bf-cbc bf-cfb bf-ecb bf-ofb camellia-128-cbc camellia-128-ecb camellia-192-cbc camellia-192-ecb camellia-256-cbc camellia-256-ecb cast cast-cbc cast5-cbc cast5-cfb cast5-ecb cast5-ofb des des-cbc des-cfb des-ecb des-ede des-ede-cbc des-ede-cfb des-ede-ofb des-ede3 des-ede3-cbc des-ede3-cfb des-ede3-ofb des-ofb des3 desx idea idea-cbc idea-cfb idea-ecb idea-ofb rc2 rc2-40-cbc rc2-64-cbc rc2-cbc rc2-cfb rc2-ecb rc2-ofb rc4 rc4-40 seed seed-cbc seed-cfb seed-ecb seed-ofb sm4-cbc sm4-cfb sm4-ctr sm4-ecb sm4-ofb
2. Affichez la version de la commande
OpenSSL> version OpenSSL 1.1.1h 22 Sep 2020
3. Utilisez les commandes openssl pour effectuer l'encodage et le décodage base64
- encodage base64
(base) [root@sun-site certs]# echo “wuhs” |openssl base64 d3Vocwo= (base) [root@sun-site certs]# echo “wuhs” > 1.txt (base) [root@sun-site certs]# openssl base64 -in 1.txt d3Vocwo=.
- décodage base64
(base) [root@sun-site certs]# echo “d3Vocwo=” | openssl base64 -d wuhs (base) [root@sun-site certs]# openssl base64 -d -in 1.base64 wuhs
4. Utilisez openssl pour générer un mot de passe aléatoire
- Générez un mot de passe aléatoire à 12 chiffres
(base) [root@sun-site certs]# openssl rand -base64 10 |cut -c 1-12 PGznlV5Og0Us
5. Utilisez la commande openssl pour générer un résumé
- .
- Effectuer md5 calcul de résumé sur la chaîne "wuhs"
(base) [root@sun-site certs]# echo wuhs | openssl md5 (stdin)= 4cdb1fbd6a34ff27dc8c10913fab3e7e (base) [root@sun-site certs]# openssl md5 1.txt MD5(1.txt)= 4cdb1fbd6a34ff27dc8c10913fab3e7e
- Effectuez le calcul de résumé sha1 sur la chaîne "wuhs"
(base) [root@sun-site certs]# openssl sha1 1.txt SHA1(1.txt)= bd8f0b20de17d623608218d05e8741502cf42302 (base) [root@sun-site certs]# echo wuhs | openssl sha1 (stdin)= bd8f0b20de17d623608218d05e8741502cf42302
6. Utilisez la commande openssl pour effectuer le cryptage et le déchiffrement AES
- Cryptez la chaîne ". wuhs" avec aes, en utilisant la clé 123, le résultat de sortie est donné au format d'encodage base64
(base) [root@sun-site certs]# openssl aes-128-cbc -in 1.txt -k 123 -base64 *** WARNING : deprecated key derivation used. Using -iter or -pbkdf2 would be better. U2FsdGVkX194Z8P5c7C8vmXbA39omlqU/ET8xaehVFk=
- Déchiffrer les données du fichier crypté aes, clé 123
(base) [root@sun-site certs]# openssl aes-128-cbc -d -k 123 -base64 -in 2.txt *** WARNING : deprecated key derivation used. Using -iter or -pbkdf2 would be better. wuhs
7. Génération et vérification de clé
- Créer une clé privée cryptée
(base) [root@sun-site tmp]# openssl genrsa -des3 -out sunsite.key 2048 Generating RSA private key, 2048 bit long modulus (2 primes) …+++++ …+++++ e is 65537 (0x010001) Enter pass phrase for sunsite.key: Verifying - Enter pass phrase for sunsite.key: (base) [root@sun-site tmp]# ll total 16 -rw------- 1 root root 1751 Oct 25 14:43 sunsite.key
- Vérifiez la clé privée
(base) [root@sun-site tmp]# openssl rsa -check -in sunsite.key Enter pass phrase for sunsite.key: RSA key ok writing RSA key -----BEGIN RSA PRIVATE KEY----- MIIEpAIBAAKCAQEA1jDreCAjX5kpNmnyNayQB/GUvyIRvZZM2WoKAIjne91JupgP OKmBdYSWeWsf0h0XU9ubhCHpgCss2hdRKxLN3rJLlFD98TUKpb9S2XkfrT9s3cLN PQyCELK60zrs1sE52I4pDj4nTZPZCL9mykzqwNa5rcGuHN/lLnvJxFPJOJwVWbVE Bvh+jGioJbi+Ar0rs37/8naGBYz5k4BFn5sCKrhssoMEpDWjMz4yJMpycTlEFITa …
- Cryptez la clé privée, entrez le mot de passe et le fichier de clé privée est crypté
(base) [root@sun-site tmp]# openssl rsa -des3 -in sunsite.key -out sunsite.key writing RSA key Enter PEM pass phrase: Verifying - Enter PEM pass phrase:
- Déchiffrez la clé privée, entrez le mot de passe et la clé privée le fichier est déchiffré
(base) [root@sun-site tmp]# openssl rsa -in sunsite.key -out sunsite2.key Enter pass phrase for sunsite.key: writing RSA key
8. Générer la signature du certificat
- Utilisez le fichier de clé privée spécifié pour générer le fichier csr
(base) [root@sun-site tmp]# openssl req \ -key sunsite.key \ -new -out sunsite.csr You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:CN State or Province Name (full name) [Some-State]:HuNan Locality Name (eg, city) []:changsha Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:524627027@qq.com Please enter the following ‘extra’ attributes to be sent with your certificate request A challenge password []:123456 An optional company name []:123456
- Générez la clé privée et le CSR
(base) [root@sun-site tmp]# openssl req \ -newkey rsa:2048 -nodes -keyout s.key \ -out s.csr Generating a RSA private key …+++++ .+++++ writing new private key to ‘s.key’ ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:cn State or Province Name (full name) [Some-State]:hunan Locality Name (eg, city) []:changsha Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:524627027@qq.com Please enter the following ‘extra’ attributes to be sent with your certificate request A challenge password []:123456 An optional company name []:123456 (base) [root@sun-site tmp]# ll total 28 -rw-r–r-- 1 root root 1102 Oct 25 15:37 s.csr -rw------- 1 root root 1708 Oct 25 15:37 s.key
- Utilisez le certificat existant et une clé privée pour générer le CSR
openssl x509 \ -in domain.crt \ -signkey domain.key -x509toreq -out domain.csr
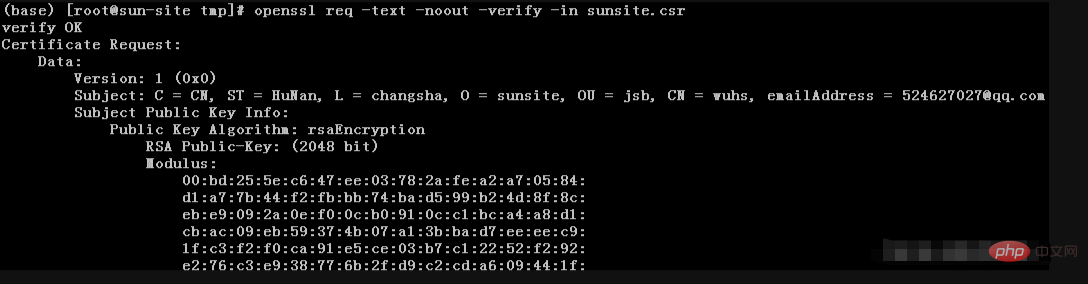
- Afficher le fichier CSR
(base) [root@sun-site tmp]# openssl req -text -noout -verify -in sunsite.csr
9. Créer et afficher des certificats SSL
- Générer un certificat auto-signé
(base) [root@sun-site tmp]# openssl req \ -newkey rsa:2048 -nodes -keyout sunsite.key \ -x509 -days 365 -out sunsite.crt Generating a RSA private key …+++++ …+++++ writing new private key to ‘sunsite.key’ ----- You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:cn State or Province Name (full name) [Some-State]:hn Locality Name (eg, city) []:cs Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:524627027@qq.com (base) [root@sun-site tmp]# ll -rw-r–r-- 1 root root 1383 Oct 25 16:03 sunsite.crt -rw-r–r-- 1 root root 1102 Oct 25 15:05 sunsite.csr -rw------- 1 root root 1708 Oct 25 16:03 sunsite.key
- Utilisez une clé privée existante pour générer un certificat auto-signé
(base) [root@sun-site tmp]# openssl req \ -key sunsite.key -new \ -x509 -days 365 -out sunsite.crt You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter ‘.’, the field will be left blank. ----- Country Name (2 letter code) [AU]:cn State or Province Name (full name) [Some-State]:hn Locality Name (eg, city) []:cs Organization Name (eg, company) [Internet Widgits Pty Ltd]:sunsite Organizational Unit Name (eg, section) []:jsb Common Name (e.g. server FQDN or YOUR name) []:wuhs Email Address []:wuhs@qq.com
- Utilisez une clé privée existante et CSR Générez un certificat auto-signé
(base) [root@sun-site tmp]# openssl x509 \ -signkey sunsite.key \ -in sunsite.csr \ -req -days 365 -out sunsite.crt Signature ok subject=C = CN, ST = HuNan, L = changsha, O = sunsite, OU = jsb, CN = wuhs, emailAddress = 524627027@qq.com Getting Private key
- Afficher le certificat
(base) [root@sun-site tmp] # openssl x509 -text -noout -in sunsite.crt
- Vérifiez si le certificat est émis par ca
(base) [root@sun-site tmp]# openssl verify -verbose -CAfile ca.crt sunsite.crt Error loading file ca.crt #需要ca证书
- Vérifiez si la clé privée, le certificat et le CSR correspondent
(base) [root@sun-site tmp]# openssl x509 -noout -modulus -in sunsite.crt |openssl md5 (stdin)= e26905e973af69aed4e4d707f882de61 (base) [root@sun-site tmp]# openssl rsa -noout -modulus -in sunsite.key |openssl md5 (stdin)= e26905e973af69aed4e4d707f882de61 (base) [root@sun-site tmp]# openssl req -noout -modulus -in sunsite.csr |openssl md5 (stdin)= e26905e973af69aed4e4d707f882de61 #md5校验和一致说明,三者匹配
10. Conversion du format de certificat
- PEM en DER
(base) [root@sun-site tmp]# openssl x509 -in sunsite.crt -outform der -out sunsite.der
- DER en PEM
(base) [root@sun-site tmp]# openssl x509 -in sunsite.der -inform der -out sunsite.crt
- P EM en PKCS7
(base) [root@sun-site tmp]# openssl crl2pkcs7 -nocrl -certfile sunsite.crt -certfile ca-chain.crt -out sunsite.p7b
- PKCS7 en PEM
#openssl pkcs7 -in domain.p7b -print_certs -out domain.crt
- PEM à PKCS12
openssl pkcs12 -inkey domain.key -in domain.crt -export -out domain.pfx
- PKCS12 à PEM
openssl pkcs12 -in domain.pfx -nodes -out domain.combined.crt
11, révocation de certificat
- Le client obtient le numéro de série du certificat à révoquer (en exécution hôte à l'aide du certificat)
(base) [root@sun-site tmp]# openssl x509 -in sunsite.crt -noout -serial -subject serial=2DA086B4B14ECE63535734049A4BCF70290446C9 subject=C = CN, ST = HuNan, L = changsha, O = sunsite, OU = jsb, CN = wuhs, emailAddress = 524627027@qq.com
Obtenir l'aide de la commande12.
- Prenons la commande openssl x509 comme exemple
(base) [root@sun-site tmp]# openssl x509 --help
三、使用语法及命令介绍
openssl command [ command_opts ] [ command_args ]
2、标准命令
| 命令 | 命令介绍 |
|---|---|
| asn1parse | 解析ASN.1序列。 |
| ca | 证书颁发机构(ca)管理。 |
| ciphers | 密码套件描述确定。 |
| cms | cms(加密消息语法)实用程序 |
| crl | 证书撤销列表(crl)管理。 |
| crl2pkcs7 | CRL到PKCS#7的转换。 |
| dgst | 消息摘要计算。 |
| dh | Diffie-Hellman参数管理。被dhparam淘汰。 |
| dhparam | Diffie-Hellman参数的生成和管理。由genpkey和pkeyparam取代 |
| dsa | dsa数据管理。 |
| dsaparam | DSA参数生成和管理。由genpkey和pkeyparam取代 |
| ec | ec(椭圆曲线)密钥处理 |
| ecparam | EC参数操作和生成 |
| enc | 使用密码进行编码。 |
| engine | 引擎(可加载模块)信息和操作。 |
| errstr | 错误编号到错误字符串的转换。 |
| gendh | Diffie-Hellman参数的生成。被dhparam淘汰。 |
| gendsa | 根据参数生成DSA私钥。由genpkey和pkey取代 |
| genpkey | 生成私钥或参数。 |
| genrsa | 生成RSA私钥。由根普基取代。 |
| nseq | 创建或检查netscape证书序列 |
| ocsp | 在线证书状态协议实用程序。 |
| passwd | 生成哈希密码。 |
| pkcs12 | PKCS#12数据管理。 |
| pkcs7 | PKCS#7数据管理。 |
| pkey | 公钥和私钥管理。 |
| pkeyparam | 公钥算法参数管理。 |
| pkeyutl | 公钥算法加密操作实用程序。 |
| rand | 生成伪随机字节。 |
| req | PKCS#10 X.509证书签名请求(CSR)管理。 |
| rsa | rsa密钥管理。 |
| rsautl | RSA实用程序,用于签名、验证、加密和解密。被pkeyutl取代 |
| s_client | 这实现了一个通用的SSL/TLS客户端,它可以与使用SSL/TLS的远程服务器建立透明连接。它仅用于测试目的,只提供基本的接口功能,但在内部主要使用OpenSSL库的所有功能。 |
| s_server | |
| s_time | SSL连接计时器。 |
| sess_id | SSL会话数据管理。 |
| smime | S/MIME邮件处理。 |
| speed | 算法速度测量。 |
| spkac | spkac打印和生成实用程序 |
| ts | 时间戳授权工具(客户端/服务器) |
| verify | X.509证书验证。 |
| version | OpenSSL版本信息。 |
| x509 | X.509证书数据管理。 |
3. Commande de résumé de message
| Commande | Introduction à la commande |
|---|---|
| md2 | MD2 Digest |
| md5 | MD5 Digest |
| mdc2 | MDC2 Digest |
| rmd160 | RMD-160 Digest |
| sha | SHA Digest |
| sha1 | SHA-1 Digest |
| sha224 | SHA-224 Digest |
| sha256 | 4. Commandes d'encodage et de mot de passe |
| Command | |
encodage base64bf bf-cbc bf-cfb cb bf-ofbMot de passe Blowfish
| Force password conversion | |
|---|---|
| des des-cbc des-cfb des-ecb des-ede des-ede-cbc des-ede-cfb des-ede-ofb des-ofb | |
| des3 desx des-ede3 des-ede3-cbc des-ede3-cfb des-ede3-ofb | |
| idée idée-cbc idée-cfb idée-ecb idée-ofb | |
| rc2 rc2-cbc rc2-cfb rc2-ecb rc2-ofb | |
| rc4 | |
| rc5 rc5- cbc rc5-cfb rc5- ecb rc5-ofb | |
| " |
Ce qui précède est le contenu détaillé de. pour plus d'informations, suivez d'autres articles connexes sur le site Web de PHP en chinois!



