 web3.0
web3.0 What are the cross-chain infrastructure projects? Cross-chain infrastructure projects and currency inventory
What are the cross-chain infrastructure projects? Cross-chain infrastructure projects and currency inventoryWhat are the cross-chain infrastructure projects? Cross-chain infrastructure projects and currency inventory

As a network, blockchain is almost equivalent to the Internet in the 1980s. Because the ecology is extremely fragmented, applications, users and funds are all separated in different network systems.
Cross-chain bridges are of course a very important solution, but they should not become the norm. Real large-scale adoption of blockchain requires core protocols and APIs.
Vitalik, the founder of Ethereum, once summarized three cross-chain solutions - hash time lock (HTLC), notary and side chain/relay.
Hash time lock uses cryptography to realize cross-chain transfers. The principle can be simply understood as Alipay, but the implementation method is decentralized.
The notary mechanism means that the notary establishes an intermediate account, and the user transfers assets to the intermediate account. The principle is almost the same as Alipay's inter-bank transfer, which requires the notary to issue a vToken across the chain.
Since the notary acts as a bridge between blockchain networks, the handling fee will be very low or even free. The only risk is whether the notary is trustworthy - not only whether there is a motive for evil, but also Also vulnerable to attack.
The third is the side chain/relay solution, which can also be called the bridge chain solution, because the relay chain is essentially a common side chain for multiple chains, and then the interaction between the side chains is realized. Operability.
This common side chain still acts as an intermediate account, but it is more secure than the notary mechanism just mentioned. Both Cosmos and Polkadot are more complete in terms of technology and mechanism.
The above is the detailed content of What are the cross-chain infrastructure projects? Cross-chain infrastructure projects and currency inventory. For more information, please follow other related articles on the PHP Chinese website!
 Tether CEO Paolo Ardoino Completes Visit to the United States, Meeting with Lawmakers in Washington, D.C. to Discuss Stablecoin RegulationApr 15, 2025 am 11:24 AM
Tether CEO Paolo Ardoino Completes Visit to the United States, Meeting with Lawmakers in Washington, D.C. to Discuss Stablecoin RegulationApr 15, 2025 am 11:24 AMHis visit comes as the U.S. Congress moves closer to introducing legislation regulating stablecoins, which Ardoino believes is necessary for financial inclusion and preserving U.S. dollar dominance.
 Why XRP Price May Not 'Go Parabolic' Post-SEC SettlementApr 15, 2025 am 11:22 AM
Why XRP Price May Not 'Go Parabolic' Post-SEC SettlementApr 15, 2025 am 11:22 AMThe XRP price holds still in the $2.10-2.20 range for the past few days, but this is not stopping Ripple's community from continuing to post various content about XRP
 Metaplanet Expands Its Bitcoin Treasury Holdings by Another 319 BTCApr 15, 2025 am 11:20 AM
Metaplanet Expands Its Bitcoin Treasury Holdings by Another 319 BTCApr 15, 2025 am 11:20 AMIn an announcement made earlier today, Japanese firm Metaplanet revealed it has acquired another 319 Bitcoin (BTC), pushing its total corporate holdings beyond 4,500 BTC.
 Metaplanet Scoops Another 319 Bitcoin, Pushing Its Total Corporate Holdings Beyond 4500Apr 15, 2025 am 11:18 AM
Metaplanet Scoops Another 319 Bitcoin, Pushing Its Total Corporate Holdings Beyond 4500Apr 15, 2025 am 11:18 AMIn an announcement made earlier today, Japanese firm Metaplanet revealed it has acquired another 319 Bitcoin (BTC), pushing its total corporate holdings beyond 4,500 BTC.
 Ripple (XRP) price rallied through a weekend riseApr 15, 2025 am 11:16 AM
Ripple (XRP) price rallied through a weekend riseApr 15, 2025 am 11:16 AMRipple (XRP) price rallied through a weekend rise from its $2.00 critical support mark to reach $2.23.
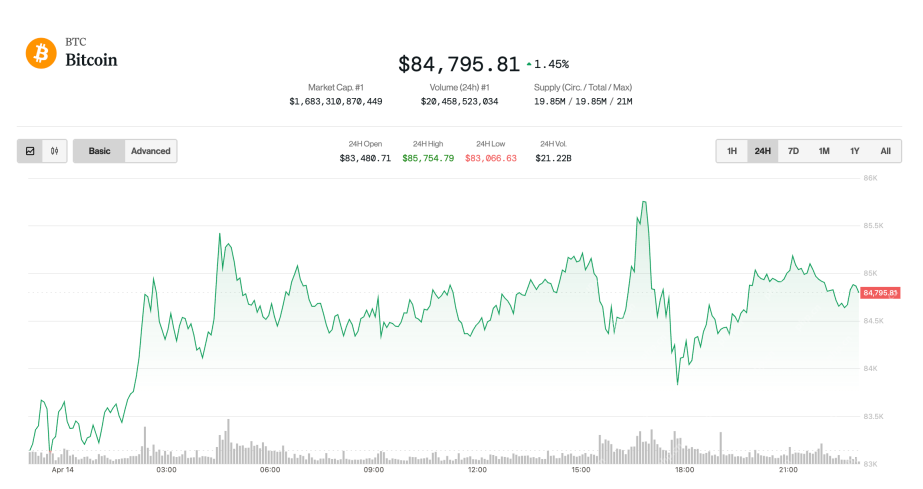 Bitcoin (BTC) drifts upwards as the broader market adjusts favorably to trade-related newsApr 15, 2025 am 11:14 AM
Bitcoin (BTC) drifts upwards as the broader market adjusts favorably to trade-related newsApr 15, 2025 am 11:14 AMThe largest cryptocurrency was up 1.6% in the last 24 hours and is now trading just shy of $85,000. Ether (ETH), meanwhile, rose 2.7%
 Is ADA the Sleeper Pick for the Next Bull Run? Hoskinson's $250K BTC Forecast Says YesApr 15, 2025 am 11:12 AM
Is ADA the Sleeper Pick for the Next Bull Run? Hoskinson's $250K BTC Forecast Says YesApr 15, 2025 am 11:12 AMADA has risen by 1.5% in the past 24 hours, with its move to $0.644 coming as the crypto market suffers a 2% loss today.
 Solana Leads Market Recovery After Brief Dip Below $100Apr 15, 2025 am 11:10 AM
Solana Leads Market Recovery After Brief Dip Below $100Apr 15, 2025 am 11:10 AMJimmy has nearly 10 years of experience as a journalist and writer in the blockchain industry. He has worked with well-known publications such as Bitcoin Magazine, CCN, and Blockonomi, covering news...

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

Zend Studio 13.0.1
Powerful PHP integrated development environment

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.




