 Mobile Tutorial
Mobile Tutorial Android Phone
Android Phone How to copy the access card on Xiaomi 11_Tutorial on copying the access card on Xiaomi 11
How to copy the access card on Xiaomi 11_Tutorial on copying the access card on Xiaomi 11How to copy the access card on Xiaomi 11_Tutorial on copying the access card on Xiaomi 11
In recent years, with the continuous upgrading of smart phone functions, more and more users have begun to try to use mobile phones to simulate the functions of access control cards. For Xiaomi 11 users, how to copy access cards on their mobile phones has become a hot topic. In this article, PHP editor Xigua will give you a detailed tutorial on copying access cards on Xiaomi Mi 11, so that you can easily master this technique.
1. First, we need to open the phone, and then click on the desktop to open the [Xiaomi Wallet] software of the Xiaomi phone. In the software, the user can see the cards that can be simulated and added, and click on the access card option that you want to simulate. ,click to enter.

2. In the interface for adding access cards, click the yellow plus sign add button in the lower right corner, click Add, and copy and add an access card to the back of the phone according to the phone operation prompts to successfully simulate .

3. Select the physical access card simulation, click [Start Detection], and place the access card near the NFC function area on the back of the phone. Do not remove it. The phone will detect and copy the access card at this time. The information in the card is transferred to the mobile phone.


#5. After completion, you only need to call up the card swiping interface on your phone each time, and then bring the back of your phone's head close to the card swiping sensing area to complete the sensing operation, which is very convenient. .

The above is the detailed content of How to copy the access card on Xiaomi 11_Tutorial on copying the access card on Xiaomi 11. For more information, please follow other related articles on the PHP Chinese website!
 You Can Get the Galaxy Watch FE for As Low As $150 TodayMay 14, 2025 am 05:15 AM
You Can Get the Galaxy Watch FE for As Low As $150 TodayMay 14, 2025 am 05:15 AMSamsung Galaxy Watch FE Bluetooth
 5 Reasons Why I'm Excited About The Galaxy Z Flip 7 FE: Samsung's Affordable FoldableMay 14, 2025 am 05:14 AM
5 Reasons Why I'm Excited About The Galaxy Z Flip 7 FE: Samsung's Affordable FoldableMay 14, 2025 am 05:14 AMSummary The Galaxy Z Flip 7 FE is said to borrow its specifications from Samsung's 2024 flip-style flagship, the Galaxy Z Flip 6, including the scre
 Nextcloud Says Google Is Hurting Its Android AppMay 14, 2025 am 05:10 AM
Nextcloud Says Google Is Hurting Its Android AppMay 14, 2025 am 05:10 AMGoogle is reportedly blocking Nextcloud, the open-source cloud storage service, from full file access on Android devices. Nextcloud is accusing Google of anti-competitive behavior, while a fully functional version remains available through the F-Droi
 Google Says RCS Messaging Just Hit a Big MilestoneMay 14, 2025 am 04:55 AM
Google Says RCS Messaging Just Hit a Big MilestoneMay 14, 2025 am 04:55 AMSummary Google's efforts in promoting RCS as an SMS replacement have paid off, with a billion RCS messages sent daily in the US.
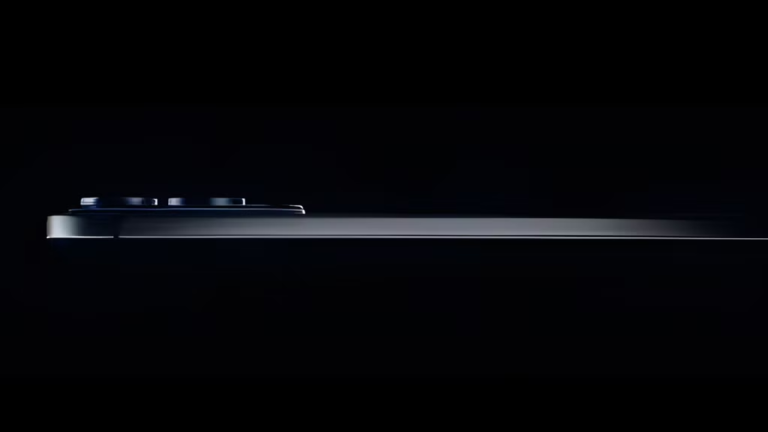 Galaxy S25 Edge: What to Expect From Samsung's Super-Thin SmartphoneMay 14, 2025 am 04:42 AM
Galaxy S25 Edge: What to Expect From Samsung's Super-Thin SmartphoneMay 14, 2025 am 04:42 AMSamsung is about to reveal its thinnest smartphone to date: the Galaxy S25 Edge. Despite having a slim profile, the phone will maintain a flagship stature with top-tier hardware and software. Ahead of its official launch, here's everything we know ab
 Google's Find My Device Network Is Now a Hub for People, TooMay 14, 2025 am 04:33 AM
Google's Find My Device Network Is Now a Hub for People, TooMay 14, 2025 am 04:33 AMIt’s barely been a year since Google flipped the switch on Android's Find My Device network, but it’s already getting a rebrand and an upgrade to help you keep track of everything and everyone that matters. Find My Device launched as an expansion
 The Super-Thin Galaxy S25 Edge Has ArrivedMay 14, 2025 am 04:05 AM
The Super-Thin Galaxy S25 Edge Has ArrivedMay 14, 2025 am 04:05 AMSamsung has officially revealed its super-thin flagship phone for 2025: the Galaxy S25 Edge. It’s available to order starting today, but as you might expect, Samsung had to make a few compromises to achieve the super-slim design. Following a tease
 Moto Razr Ultra (2025) vs. Samsung Galaxy Z Flip 6May 14, 2025 am 04:02 AM
Moto Razr Ultra (2025) vs. Samsung Galaxy Z Flip 6May 14, 2025 am 04:02 AMThere's a new clamshell foldable in town — the Moto Razr Ultra (2025) — ready to take on the best from the competition. Here's how the flip-style foldable compares with Samsung's Galaxy Z Flip 6, and which is better. Price


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

SublimeText3 Linux new version
SublimeText3 Linux latest version

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

Notepad++7.3.1
Easy-to-use and free code editor





