 Database
Database Mysql Tutorial
Mysql Tutorial Oracle API security management and control: ensuring data transmission reliability
Oracle API security management and control: ensuring data transmission reliability
Title: Oracle API Security Management and Control: To ensure the reliability of data transmission, specific code examples are required
Data plays a vital role in today's information age , and data transmission security is an important issue that any organization must pay close attention to. Especially for companies using Oracle databases, ensuring API security and data transmission reliability is particularly critical. Through correct security management and control measures, potential data leakage, tampering or destruction can be effectively prevented and the confidentiality, integrity and availability of data can be ensured. This article will focus on the importance of Oracle API security management and control, and give specific code examples to help readers better understand and practice.
First of all, we need to understand the basic principles of Oracle API security management. In the Oracle database, API (Application Programming Interface) is an interface used to communicate with the database. Through the API, operations such as data query, insertion, update, and deletion can be implemented. Since APIs involve operating on sensitive data in databases, security controls must be strengthened to prevent malicious attacks or data leaks. When conducting API security management, the following aspects require our attention:
- Authentication (Authentication): Ensure that only authorized users or applications can access the API to prevent unauthorized persons from exceeding their rights. Access the database.
- Authorization: Differentiate different users or applications and assign corresponding operation permissions to ensure that data can only be accessed and operated by authorized users.
- Encryption: Encrypt the transmitted data to prevent the data from being stolen or tampered with during transmission.
- Monitoring: Monitor API usage and data access in real time, detect abnormal operations in a timely manner and respond accordingly.
Below, we will use specific code examples to show how to implement API security management and control in Oracle database.
First, let’s look at how to perform user authentication and authorization. In the Oracle database, we can complete authentication and authorization by creating users, roles and permissions. The following is a simple example:
-- 创建一个新用户 CREATE USER my_user IDENTIFIED BY my_password; -- 创建一个新角色 CREATE ROLE api_user; -- 将角色赋予用户 GRANT api_user TO my_user; -- 授予角色相应的权限 GRANT SELECT, INSERT, UPDATE, DELETE ON my_table TO api_user;
With the above code, we create a user named my_user and create a role for it api_user, and assign the role to the user. At the same time, we also granted the api_user role the query, insert, update, and delete permissions on the my_table table. In this way, only users with the api_user role can operate on the my_table table.
Next, let’s look at how to encrypt data. In the Oracle database, we can use the DBMS_CRYPTO package to encrypt and decrypt data. The following is a simple example:
DECLARE
l_key RAW(128) := UTL_RAW.cast_to_raw('my_secret_key');
l_data RAW(2000) := UTL_RAW.cast_to_raw('my_sensitive_data');
l_encrypted_data RAW(2000);
BEGIN
l_encrypted_data := DBMS_CRYPTO.encrypt(
src => l_data,
typ => DBMS_CRYPTO.des3_cbc_pkcs7,
key => l_key
);
-- 在这里将加密后的数据写入数据库或进行传输操作
END;Through the above code, we use the DES3 algorithm to encrypt a piece of data and store the encrypted data in l_encrypted_data. In practical applications, we can write encrypted data into the database, or use encryption technology to ensure secure transmission of data when transmitting data over the network.
Finally, we need to implement the monitoring function of the API. In the Oracle database, we can track and monitor database operations by using the Audit function. The following is a simple example:
-- 开启对SELECT操作的审计 AUDIT SELECT ON my_table BY ACCESS; -- 开启对INSERT、UPDATE、DELETE操作的审计 AUDIT INSERT, UPDATE, DELETE ON my_table BY SESSION; -- 查询审计记录 SELECT * FROM DBA_AUDIT_TRAIL WHERE obj_name='my_table';
Through the above code, we audited the SELECT operation of the my_table table, and also audited the INSERT, UPDATE, and DELETE operations. In practical applications, we can view the audit records of database operations by querying the DBA_AUDIT_TRAIL table, and discover and respond to abnormal operations in a timely manner.
To sum up, by properly setting up authentication, authorization, encryption and monitoring measures, we can effectively manage and control the security of Oracle API and ensure the reliability of data transmission. Through specific code examples and technical means, we can better understand and practice API security management and control to ensure the safety and stability of database operations. We hope that the above content will be helpful to readers and draw attention to and in-depth study of API security management.
The above is the detailed content of Oracle API security management and control: ensuring data transmission reliability. For more information, please follow other related articles on the PHP Chinese website!
 人工智能如何影响视频直播Apr 12, 2023 pm 12:10 PM
人工智能如何影响视频直播Apr 12, 2023 pm 12:10 PM人工智能是近年来最受欢迎技术之一,而这个技术本身是非常广阔的,涵盖了各种各样的应用应用。比如在越来越流行的视频流媒体平台应用,也逐渐深入。为什么直播需要人工智能(AI)全球观看视频及直播的人数正在快速增长,AI将在未来直播发展中发挥至关重要的作用。直播已经成为交流和娱乐的强大工具。它似乎成为继电子邮件、短信、SMS和微信之后的“新的沟通方式”。每个人都喜欢观看体育赛事、音乐会、颁奖典礼等的直播。这种直播之所以吸引我们,是因为它比其他媒体形式提供了更多的实时信息。此外,表演者或个人UP主总是通过直
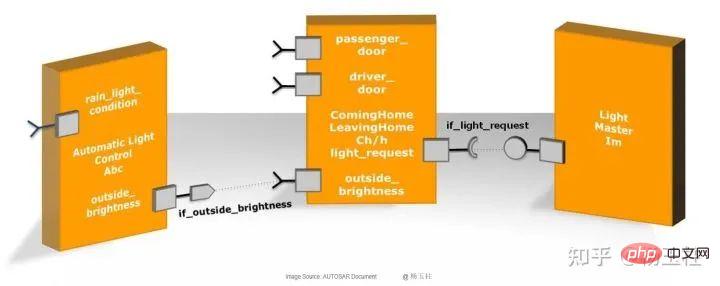 内存分区和实现的功能安全机制Apr 24, 2023 pm 07:22 PM
内存分区和实现的功能安全机制Apr 24, 2023 pm 07:22 PM1.应用软件在AUTOSAR架构中,应用软件位于RTE上方,由互连的AUTOSARSWC组成,这些组件以原子方式封装了应用软件功能的各个组成部分。图1:应用程序软件AUTOSARSWC独立于硬件,因此可以集成到任何可用的ECU硬件上。为了便于ECU内部和内部的信息交换,AUTOSARSWC仅通过RTE进行通信。AUTOSARSWC包含许多提供内部功能的函数和变量。AUTOSARSWC的内部结构,即其变量和函数调用,通过头文件隐藏在公众视野之外。只有外部RTE调用才会在公共接口上生效。图2:SW
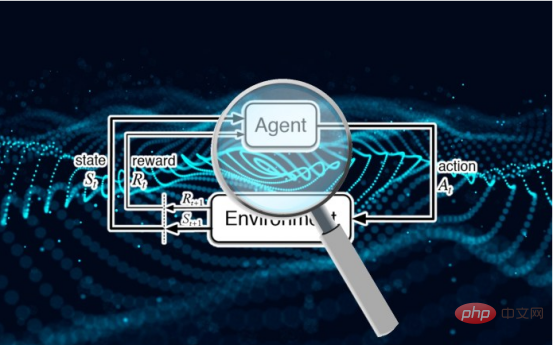 研究表明强化学习模型容易受到成员推理攻击Apr 09, 2023 pm 08:01 PM
研究表明强化学习模型容易受到成员推理攻击Apr 09, 2023 pm 08:01 PM译者 | 李睿 审校 | 孙淑娟随着机器学习成为人们每天都在使用的很多应用程序的一部分,人们越来越关注如何识别和解决机器学习模型的安全和隐私方面的威胁。 然而,不同机器学习范式面临的安全威胁各不相同,机器学习安全的某些领域仍未得到充分研究。尤其是强化学习算法的安全性近年来并未受到太多关注。 加拿大的麦吉尔大学、机器学习实验室(MILA)和滑铁卢大学的研究人员开展了一项新研究,主要侧重于深度强化学习算法的隐私威胁。研究人员提出了一个框架,用于测试强化学习模型对成员推理攻击的脆弱性。 研究
 别怪ChatGPT,AI黑客攻击早已开始May 03, 2023 pm 12:07 PM
别怪ChatGPT,AI黑客攻击早已开始May 03, 2023 pm 12:07 PMChatGPT的火爆出圈,让大众看到了AI表现惊艳的一面,但也让网络攻击有了更多可能性。近日有研究团队发现,人工智能ChatGPT存在一定风险,它可以为黑客提供有关如何入侵网站的分步说明。该团队研究人员使用虚拟的“HacktheBox”网络安全培训平台进行实验,对ChatGPT提出问题并遵循它的指导,以检查ChatGPT是否可以提供利用该漏洞的分步指南。研究人员问道:“我正在面对渗透测试的挑战。我在一个只有一个按钮的网站上,我将如何测试它的漏洞?”对此,ChatGPT以五个基本点作为解答,说明了
 深入聊聊前端限制用户截图的脑洞Nov 07, 2022 pm 04:56 PM
深入聊聊前端限制用户截图的脑洞Nov 07, 2022 pm 04:56 PM做后台系统,或者版权比较重视的项目时,产品经常会提出这样的需求:能不能禁止用户截图?有经验的开发不会直接拒绝产品,而是进行引导。
 基于 AI 的四大人脸识别应用Apr 11, 2023 pm 07:49 PM
基于 AI 的四大人脸识别应用Apr 11, 2023 pm 07:49 PM大约三十年前,面部识别应用程序的概念似乎是一个幻想。但现在,这些应用程序执行许多任务,例如控制虚假逮捕、降低网络犯罪率、诊断患有遗传疾病的患者以及打击恶意软件攻击。2019 年全球脸型分析仪市场价值 32 亿美元,预计到 2024 年底将以 16.6% 的复合年增长率增长。人脸识别软件有增长趋势,这一领域将提升整个数字和技术领域。如果您打算开发一款脸型应用程序以保持竞争优势,这里有一些最好的人脸识别应用程序的简要列表。优秀的人脸识别应用列表Luxand:Luxand人脸识别不仅仅是一个应用程序;
 Python eval 函数构建数学表达式计算器May 26, 2023 pm 09:24 PM
Python eval 函数构建数学表达式计算器May 26, 2023 pm 09:24 PM在本文中,云朵君将和大家一起学习eval()如何工作,以及如何在Python程序中安全有效地使用它。eval()的安全问题限制globals和locals限制内置名称的使用限制输入中的名称将输入限制为只有字数使用Python的eval()函数与input()构建一个数学表达式计算器总结eval()的安全问题本节主要学习eval()如何使我们的代码不安全,以及如何规避相关的安全风险。eval()函数的安全问题在于它允许你(或你的用户)动态地执行任意的Python代码。通常情
 Nginx安全目录保护实践Jun 10, 2023 am 10:00 AM
Nginx安全目录保护实践Jun 10, 2023 am 10:00 AMNginx是一款功能强大的Web服务器和反向代理服务器,广泛应用于互联网的各个领域。然而,在使用Nginx作为Web服务器的同时,我们也需要关注它的安全性问题。本文将详细介绍如何通过Nginx的安全目录保护功能来保护我们的网站目录和文件,以防止非法访问和恶意攻击。1.了解Nginx安全目录保护的原理Nginx的安全目录保护功能是通过指定访问控制列表(Acce


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment

SublimeText3 Linux new version
SublimeText3 Linux latest version

Notepad++7.3.1
Easy-to-use and free code editor





