Operation and Maintenance
Operation and Maintenance Linux Operation and Maintenance
Linux Operation and Maintenance Five different ways to group user IDs in Linux
Five different ways to group user IDs in Linux
"Five different grouping methods of user IDs in Linux"
In the Linux operating system, user ID (User ID) is a number used to identify different users. . The user ID determines the user's permissions and access level in the system. In addition to ordinary users, system administrators can also group users to better manage and control user permissions. In Linux, there are many ways to group user IDs. Five common grouping methods will be introduced below, with specific code examples.
1. Basic User ID grouping method (Primary User ID):
In the Linux system, each user has a basic user ID, also called Primary User ID. This ID is the user's main identification in the system and determines the user's access rights and resource control. You can use the following command to view the basic user ID of the current user:
$ id -u
2. Additional User ID grouping method (Additional User ID):
In addition to the basic user ID, the Linux system also allows users to have Multiple additional user IDs, also known as Additional User IDs. By setting additional user IDs, users can access different resources in different environments. You can use the following command to view all user IDs of the current user (including basic user IDs and additional user IDs):
$ id
3. User group ID grouping method (Group ID):
User group ID (Group ID) is used to divide different users into different user groups to better manage and control user permissions. You can use the following command to view the user groups to which the current user belongs:
$ groups
4. Additional Group ID grouping method (Additional Group ID):
In addition to user group IDs, Linux also allows users to have multiple additional group ID, also known as Additional Group ID. By setting additional group IDs, users can have different permissions in different user groups. You can use the following command to view all group IDs of the current user (including user group IDs and additional group IDs):
$ id -G
5. Special User ID grouping method (Special User ID):
Special User ID (Special User ID) is a user ID that has special permissions when the user accesses the system. Among them, the super user (root) is the most special user and has the highest authority in the system. You can use the following command to check whether the current user is a super user:
$ sudo id
Summary:
The above are five different grouping methods of user IDs in Linux. Each method has its specific role and Applicable scene. By properly setting the grouping method of user IDs, users' permissions and resource access in the system can be better managed and controlled. I hope readers can learn more about Linux user IDs through this article and use them flexibly in practical applications.
The above is the detailed content of Five different ways to group user IDs in Linux. For more information, please follow other related articles on the PHP Chinese website!
 如何进行企业微信实名认证?Feb 18, 2024 pm 03:06 PM
如何进行企业微信实名认证?Feb 18, 2024 pm 03:06 PM企业微信实名认证在哪里随着互联网技术的普及,企业微信作为一种专门为企业提供内部沟通和办公协作的工具越来越受到企业的青睐。为了确保企业微信的安全性和信任度,企业微信实名认证成为了必要的环节。那么,企业微信实名认证在哪里呢?企业微信实名认证是指企业在使用企业微信前,需要进行的身份验证过程,以确保企业的真实性和合法性。这对于提高企业微信的安全性和用户的信任度非常重
 linux系统下svn安装有几种方式Jun 14, 2023 am 10:50 AM
linux系统下svn安装有几种方式Jun 14, 2023 am 10:50 AMlinux系统下svn安装方式常见有3种:1、使用操作系统预编译的软件包工具,如在“Ubuntu/Debian”上使用“sudo apt-get update”“sudo apt-get install subversion”进行安装;2、从源代码编译安装,官网下载源代码然后在Linux终端执行命令进行编译和安装;3、使用第三方包管理器如“Yum”进行安装,注意依赖项问题即可。
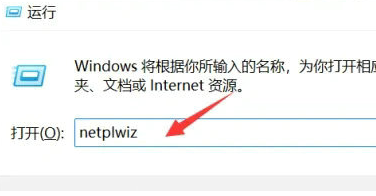 Win11用户权限设置教程:如何配置Win11的用户权限Jan 29, 2024 pm 08:33 PM
Win11用户权限设置教程:如何配置Win11的用户权限Jan 29, 2024 pm 08:33 PM有些用户们在使用电脑的时候会创建多个账户,不过也有一些用户们的账户没有权限,这就导致一些操作不能直接的进行操作?那Win11怎么设置用户权限?不清楚的用户们可以来本站看看相关的攻略吧。Win11设置用户权限的方法1、直接通过组合快捷键【win+R】打造运行功能,然后在搜索框中输入【netplwiz】点击确定。3、在打开的属性窗口中,点击上方菜单栏中的组成员。5、会出现一个窗口提示,直接点击【是】进行账户的注销重启即可完成设置。
 如何实现PHP的用户登录和权限控制?Jun 29, 2023 pm 02:28 PM
如何实现PHP的用户登录和权限控制?Jun 29, 2023 pm 02:28 PM如何实现PHP的用户登录和权限控制?在开发Web应用程序时,用户登录和权限控制是非常重要的功能之一。通过用户登录,我们可以对用户进行身份验证,并且基于用户的权限进行一系列的操作控制。本文将介绍如何使用PHP实现用户登录和权限控制功能。一、用户登录功能实现用户登录功能是用户验证的第一步,只有通过验证的用户才能进一步进行操作。下面是一个基本的用户登录实现过程:创
 如何在文件管理器中隐藏文件和文件夹Jan 12, 2024 am 08:51 AM
如何在文件管理器中隐藏文件和文件夹Jan 12, 2024 am 08:51 AM如果一个系统被多个用户使用,你或许出于个人原因想在文件管理器中隐藏一些文件或文件夹不让其他人看到(绝大多数用户不会对Linux系统进行深入了解,所以他们只会看到文件管理器列出的文件和文件夹),我们有三种方法可以来做这件事。此外,(除了隐藏)你还可以使用密码保护文件或文件夹。在这个教程中,我们将讨论如何用非重命名的方法在文件管理器中隐藏文件和文件夹。我们都知道,通过以点(“.”)前缀重命名一个文件或文件夹的方式,可以在Linux中将该文件或文件夹隐藏。但这不是隐藏文件或文件夹的正确/高效方式。一些
 linux操作系统包有哪些Jun 14, 2023 am 10:41 AM
linux操作系统包有哪些Jun 14, 2023 am 10:41 AMlinux常用操作系统包有:1、Debian,稳定、通用、开放源代码的操作系统,全球使用最广泛的 Linux 发行版之一;2、Ubuntu,基于Debian的开放源代码操作系统,在桌面和笔记本电脑领域得到了广泛的应用;3、CentOS,基于Red Hat Enterprise Linux源码重新编译而来的社区发布版本,在企业服务器主机环境中非常流行等等。
 Node.js开发:如何实现用户权限管理功能Nov 08, 2023 am 09:17 AM
Node.js开发:如何实现用户权限管理功能Nov 08, 2023 am 09:17 AM标题:Node.js开发:用户权限管理功能实现及代码示例摘要:随着Web应用程序和系统的复杂性不断增加,用户权限管理成为一个不可忽视的重要功能。本文将介绍在Node.js开发中如何实现用户权限管理功能,并给出具体的代码示例。引言:Node.js作为一个高效且轻量级的开发平台,拥有广泛的应用场景。在众多Node.js应用开发中,用户权限管理往往是必不可少的功能


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

SublimeText3 Linux new version
SublimeText3 Linux latest version

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function