What does the stolen device protection function do and how to turn it on
In iOS 17.3 Beta1, Apple has added a new feature called "Stolen Device Protection". The "Stolen Device Protection" feature allows users to effectively lock stolen devices by combining factors such as location, biometric scans, and time delays. devices, and protect your data and privacy.
When Stolen Device Protection is enabled, users will need to verify their identity via Face ID or Touch ID to execute iPhone operations if the phone is in a location that is not normally associated with the owner. certain operations.
Simply put, if the Stolen Device Protection feature is not turned on, an iPhone thief who has your password can use it to change your Apple ID password, thus You are permanently locked out of the device. This allows thieves to easily turn off the Find My feature, which is necessary to wipe the original user data from the device. The thief can then sell the device at full usage value, rather than lowballing it as an iCloud-locked useless brick.
If the "Stolen Device Protection" feature is turned on, when the user is away from a familiar location such as home or work, the phone will ask for Face ID or Touch ID scan. Additionally, there is a one-hour delay before changing the Apple ID password on your device. After an hour, it will still ask for a Face ID or Touch ID scan before changing the Apple ID password from your iPhone. This greatly increases the difficulty and risk for thieves, while also giving users enough time to report a stolen iPhone and preventing criminals from further infringing on their rights.
How to turn on the "Stolen Device Protection" function?
Conditions: Currently, Apple has only introduced the "Stolen Device Protection" function in the first Beta version update of iOS/iPadOS 17.3. Therefore, users who want to use this feature need to upgrade their device systems to iOS 17.3 Beta1. (iOS 17.3 Beta1 is still a beta version, please be cautious!)
Steps to enable the "Stolen Device Protection" function:
Open your iPhone and enter [ Settings], find [Privacy and Security], and in the security check, activate [Device Theft Protection].

After this function is turned on, if the phone is in an infrequently used location, the following operations are required User additionally authenticates via Face ID or Touch ID:
#View/use password or passkey stored in iCloud Keychain
Apply for a new Apple Card
View Apple Card virtual card
Turn off Lost Mode
Delete all content and settings
Perform certain Apple Cash and Savings actions in Wallet
-
Use payment methods stored in Safari
Set up your iPhone as a new device
For particularly sensitive operations , in addition to verifying identity through Face ID or Touch ID, you must also wait for one hour, and then use Face ID or Touch ID to authenticate again, such as:
Change Apple ID password
Update some Apple ID account security settings, including adding or removing trusted devices, trusted phone numbers, recovery keys, or recovery contacts
Change iPhone Password
Add or Remove Face ID or Touch ID
-
Turn off “Find My”
Turn off the "Device Theft Protection" feature
When the iPhone is in a commonly used location, it will not appear these restrictions.
The above is the detailed content of What does the stolen device protection function do and how to turn it on. For more information, please follow other related articles on the PHP Chinese website!
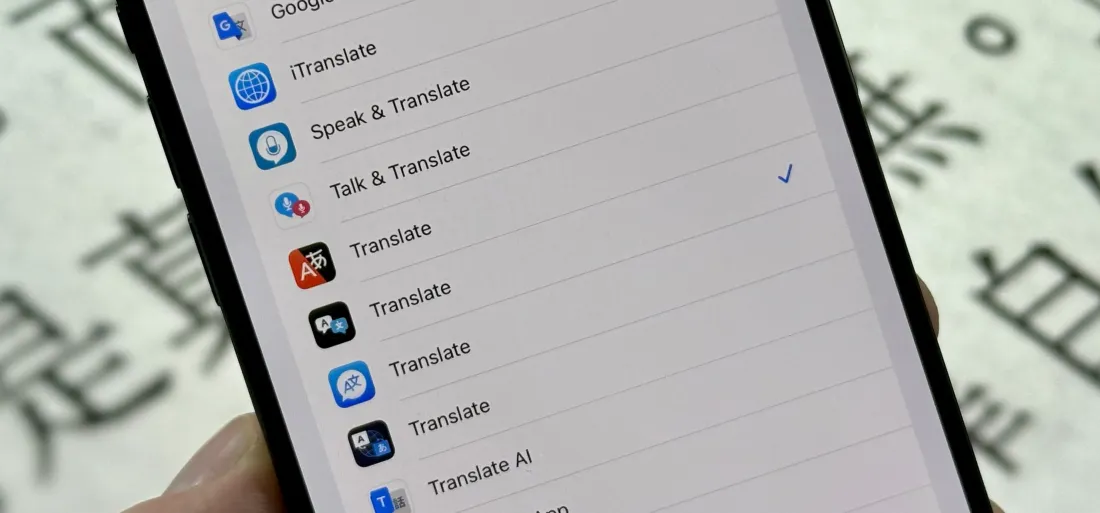 Change Your Default Translation App on iPhone and iPadMay 09, 2025 am 11:21 AM
Change Your Default Translation App on iPhone and iPadMay 09, 2025 am 11:21 AMiOS 18.4 and iPadOS 18.4 introduce the ability to customize your default translation app on iPhone and iPad. Previously, Apple's Translate app was the sole option, but now you can select third-party alternatives like Google Translate or Microsoft Tr
 Notes Disappeared from iPhone or iPad? Here’s How to Fix Missing iCloud NotesMay 09, 2025 am 11:14 AM
Notes Disappeared from iPhone or iPad? Here’s How to Fix Missing iCloud NotesMay 09, 2025 am 11:14 AMRecently, some iPhone and iPad users have reported the loss of iCloud memos, which has attracted widespread attention. Apple has officially confirmed and provided the solution. Many users found that the memo on the device disappeared after updating the iOS/iPadOS system or agreeing to the new iCloud Terms of Service. Given the importance of memorandum applications in storing important information, this issue is undoubtedly worrying. Although some users have found some solutions, the solutions provided by Apple are basically consistent with these methods. How to Recover Lost iCloud Memos on iPhone and iPad If your memo has recently disappeared from your iPhone or iPad, please follow the official Apple recommendations below
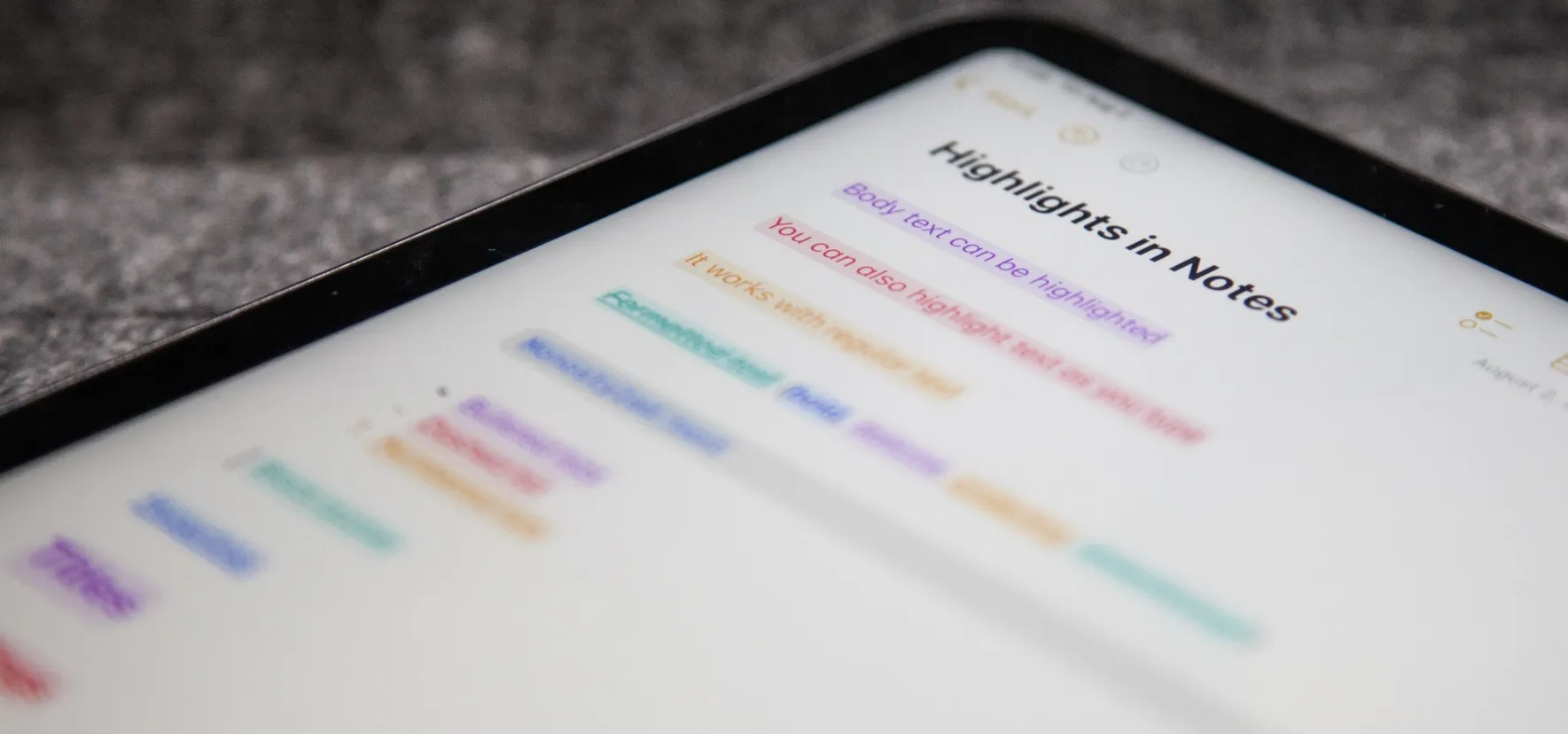 How to Change Text Color and Background Highlights in Apple Notes on iPhone, iPad, and Mac — The Official Way May 09, 2025 am 10:51 AM
How to Change Text Color and Background Highlights in Apple Notes on iPhone, iPad, and Mac — The Official Way May 09, 2025 am 10:51 AMApple Notes upgrade: Text highlighting and color features detailed explanation While Apple Notes isn't as comprehensive as powerful word processors like Apple Pages, this simple text editor keeps adding utility new features, making it much more than a basic note-taking app. The latest updates finally bring text highlighting and font color change features, providing more options for highlighting important details. The new feature is included in iOS 18, iPadOS 18 and macOS Sequoia 15, and will be released on September 16. It should be noted that Notes' highlighting function does not currently support iCloud.com version
 How to Find a Lost Apple PencilMay 09, 2025 am 10:42 AM
How to Find a Lost Apple PencilMay 09, 2025 am 10:42 AMLooking for the Lost Apple Pencil: A Practical Tips Guide Lost Apple Pencil? don’t worry! This article provides several ways to help you get it back, no matter which generation of Apple Pencil you are using. Let's start looking! Method 1: Easily find Apple Pencil Pro (Pro models only) If you are using Apple Pencil Pro, finding it is very easy because it supports the Find app. Open the Find app on the iPad connected to Apple Pencil Pro and go to the Devices tab. Select your Apple Pencil Pro and its location will be displayed on the map. Help
 Why is Wi-Fi Turning On By Itself on iPhone?May 09, 2025 am 09:45 AM
Why is Wi-Fi Turning On By Itself on iPhone?May 09, 2025 am 09:45 AMMany iPhone users find that their iPhone Wi-Fi will automatically turn on, usually after the system software is updated to iOS, restart the iPhone, or restart the iPhone. This frustrates many iPhone users because not everyone wants to enable Wi-Fi for a variety of reasons, especially when bringing their personal iPhone to areas with public, corporate, medical or government networks, such as workplaces, companies, or other public places (such as medical institutions or government agencies), they do not want to connect to those networks. A common solution is to keep Wi-Fi off (or forgetting the network), but many users find that iPhones turn on Wi-Fi on by themselves. Let's explore why iP
 iOS 18.1.1 & iPadOS 18.1.1 Security Updates ReleasedMay 09, 2025 am 09:42 AM
iOS 18.1.1 & iPadOS 18.1.1 Security Updates ReleasedMay 09, 2025 am 09:42 AMApple has launched iOS 18.1.1, iPadOS 18.1.1, iOS 17.2.2 and iPadOS 17.2.2 updates, bringing important security fixes to iPhone and iPad users. These update packages are relatively small in size but contain important security patches and are recommended for all eligible users to install. In addition, Apple has released macOS Sequoia 15.1.1 and visionOS 2.1.1, which also contain the same security patches. These security updates are not expected to bring any new features or other changes, which may be followed by beta testing in iOS 18.2 next month
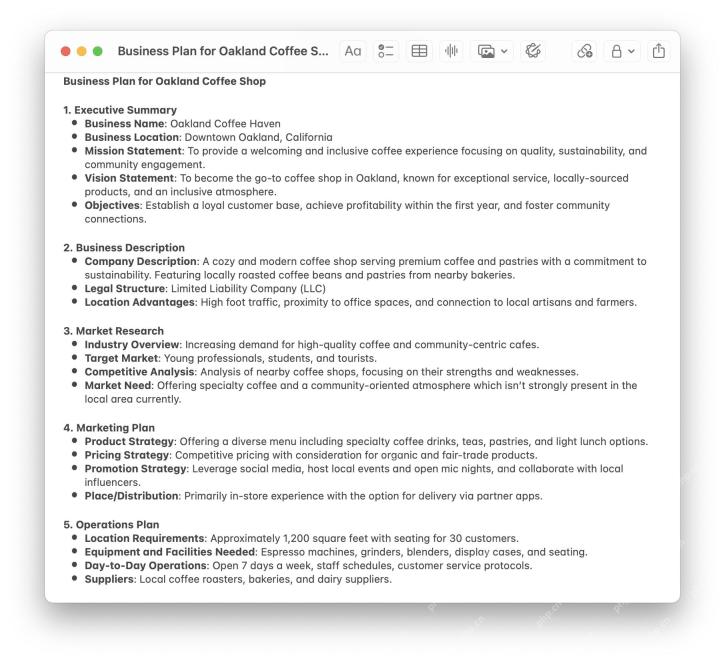 How to Instantly Write a Business Plan with AI on Mac, iPhone, iPadMay 09, 2025 am 09:41 AM
How to Instantly Write a Business Plan with AI on Mac, iPhone, iPadMay 09, 2025 am 09:41 AMCreate a business plan quickly with Apple's smart features and ChatGPT! iPhone, iPad and Mac users can easily own it without paid software or consulting. Whether it is starting a business plan, improving existing business, applying for a loan or academic assignment, high-quality business plans can be generated in seconds. How to create a business plan now on your Mac, iPhone, or iPad? Here is the fastest way to create a business plan: Open the Memo app on your Mac, iPhone, or iPad. Create a new memo and click the Apple Smart Button. Select Compose. Enter a letter such as "Business Plan for the Fashion Coffee Shop on Venice Beach"
 How to Check Battery Cycle Count on iPhoneMay 09, 2025 am 09:03 AM
How to Check Battery Cycle Count on iPhoneMay 09, 2025 am 09:03 AMWant to know how many iPhone battery cycles? The number of battery cycles represents the number of charge and discharge of the battery, which helps evaluate battery usage, health and life. In the past, it was cumbersome to view iPhone battery cycles, and you needed to view iPhone analysis data, use third-party apps, or even connect to a Mac computer. But if you're using an iPhone 15 or newer model, you can now easily view the number of battery cycles directly on the device. How to view the number of iPhone battery cycles If you are using an iPhone 15 or newer, you can easily check the number of battery cycles: Open the Settings app on your iPhone. Go to "Battery". Click "Battery Health". View "Check"


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

SublimeText3 Mac version
God-level code editing software (SublimeText3)

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

Notepad++7.3.1
Easy-to-use and free code editor

WebStorm Mac version
Useful JavaScript development tools






