 Technology peripherals
Technology peripherals AI
AI Demand for AI cyber defense highlights, advanced ransomware campaigns increase pressure
Demand for AI cyber defense highlights, advanced ransomware campaigns increase pressureDemand for AI cyber defense highlights, advanced ransomware campaigns increase pressure
Deep Instinct’s chief information officer Carl Frogit mentioned in an interview that a key focus of the 2024 budget will shift to ransomware protection technology. He expects artificial intelligence, especially deep learning, to be integrated into business processes to a greater extent, automating workflows and improving the workplace experience

Ransomware attacks What are the new trends, and how can enterprises use AI technology to prepare for them?
The latest data comes from Deep Instinct, which finds that the total number of ransomware victims will increase rapidly by 2023, and surprisingly, by 2023 There were more victims of ransomware attacks in the first half of the year than in all of 2022. In addition to media coverage of this rising trend, well-respected non-profit organizations like FS-ISAC have acknowledged the problems with this trend, which demonstrates the inadequacy of our current approach to combating evolving threats. The pattern has failed. The emergence of ransomware has changed our original “detect and respond” approach, which has been unable to keep up with the development of new variants. As a result, we are seeing an increasing number of victims. To meet this challenge, we need to shift our tactics again
Attacker techniques have changed and ransomware attacks are being carried out as large-scale campaigns affecting a significant number of victims simultaneously, just like our This year saw the same Zimbra and MOVEit exploits. With the rapid adoption of AI by bad actors, we will see the continued evolution of malware that is more sophisticated than ever before.
The advanced capabilities of AI enable us to now avoid ransomware and other cyberattacks, not just detect and respond to them. Existing evidence shows that response is no longer good enough and we need to return to a prevention-first philosophy, leveraging AI to embed prevention capabilities in infrastructure, storage and business applications. This is where enterprises can truly protect themselves from advanced forms of The only way to combat ransomware and threats, especially by leveraging more sophisticated forms of AI, such as deep learning
How deep learning differs from standard machine learning models in identifying and mitigating ransomware threats ?
Not all AI is created equal, and this is especially true when comparing deep learning and machine learning-based solutions. Most cybersecurity tools leverage machine learning models, but these models have some shortcomings in preventing threats. For example, these products only use a limited subset of available data for training (usually 2%-5%), can only provide 50%-70% accuracy for unknown threats, and produce many false positives. Machine learning solutions also require significant human intervention and are only trained on small data sets, which exposes them to human bias and error
Digital libraries are built on neural networks, relatively Compared with other methods, its "brain" can continuously train itself through raw data. Because deep learning models understand the building blocks of malicious files, predictive prevention-based security programs can be implemented and deployed to predict future malicious behavior and detect and prevent unknown threats, ransomware, and zero-day attacks
There are significant advantages to using a digital library-based solution for a business and its cybersecurity operations. First, compared to machine learning-based solutions, the solution’s continuous detection of known and unknown malware is extremely efficient, with an extremely low false positive rate. Deep Learning only needs to be updated once or twice a year to maintain this effect, and is fast and privacy-friendly because it runs independently without the need for ongoing cloud searches or intel sharing, without the need for any cloud analysis
How can deep learning technology reduce false positives, and what is the potential impact on enterprise cost savings?
Security operations center (SOC) teams are inundated with alerts and potential security threats that need to be investigated using traditional machines Learning tools, such as traditional anti-virus solutions, make it difficult for teams to determine which alerts are truly worth investigating as opposed to noise. There are many reasons for this, but the "detect and respond" philosophy means you have to collect a lot of data, which is expensive to store and maintain, and as any SOC member will say, the false positive rate is very high. .
This affects the effectiveness of the SOC - they cannot protect the enterprise, and it also has other impacts on the ability to sustain the SOC team. The volume and time-intensive nature of dealing with false positive alerts is taking a toll on the mental health of security teams, with more than half of SOC teams saying their stress levels have increased in the past 12 months due to "staff and resource constraints." Without the right technology, SOC teams, already struggling with talent constraints, are forced to focus on mundane monitoring tasks.
A solution powered by deep learning successfully solves this problem with very high accuracy and extremely low false alarm rates, which frees up the SOC team to focus on truly actionable alerts and Locate threats faster and more efficiently. By spending time on real threats, they can optimize their threat posture and engage in more proactive threat hunting, significantly improving their organization's risk posture
As enterprises begin budgeting for 2024, they should Is investing in ransomware prevention technology a priority? With 62% of CEOs confirming ransomware was their top concern over the past year, businesses are expected to adjust their budgets to increase their focus on Investment in prevention technologies to protect against ransomware, known and unknown threats, and other malware
The industry has relied on outdated and reactive solutions, such as Endpoint Detection and Response (EDR), to deliver Protect. While EDR tools are still useful from a follow-up perspective, if companies only invest in these tools, they are "assuming a breach" and hoping that remediation efforts will be successful. Clearly, this approach is failing rapidly every year due to changes in the threat landscape. Just like the Signature solution eventually failed and we moved to EDR, EDR is at the same breaking point. As a result, the industry as a whole needs to take a more advanced, proactive approach to security
In fact, IDC recently predicted that endpoint protection will There is some form of rebirth. We are in the post-EDR honeymoon period, with predictive prevention in full effect, stopping attacks before they enter your network.
The only way to combat increasingly sophisticated AI threats is to move from a “what if breach” mentality to a proactive, preventive approach to cybersecurity. Security teams cannot rely solely on outdated tools to meet the challenges of AI. Instead, enterprises should adopt native cybersecurity solutions based on deep learning models to slow the volume and velocity of evolving AI threats. By 2024, we will see enterprises making room in their budgets to integrate advanced AI technologies into their cybersecurity strategies to increase security resiliency and reduce the likelihood of successful attacks
you How do you predict that AI, especially deep learning models, will become more integrated into business processes in the coming year?
In 2023, we see AI popping up, and in 2024, AI will become a factor in business planning, processes, and decision-making As part of this, for example, this includes automating workflows, optimizing processes, and prioritizing alerts that we see in the AI assistant, these additional features do not prevent, but only help in the moment.
Additionally, as AI becomes fully integrated, younger generations will not have the same hands-on experience with workplace tasks such as troubleshooting, outages, and security incidents, as much of these tasks will be automated by AI . For leaders, the question will become: How do we continue to develop and shape people’s skills and careers when the opportunity to learn the basics of the workforce is taken away? I expect this question will be answered by the end of next year.
The above is the detailed content of Demand for AI cyber defense highlights, advanced ransomware campaigns increase pressure. For more information, please follow other related articles on the PHP Chinese website!
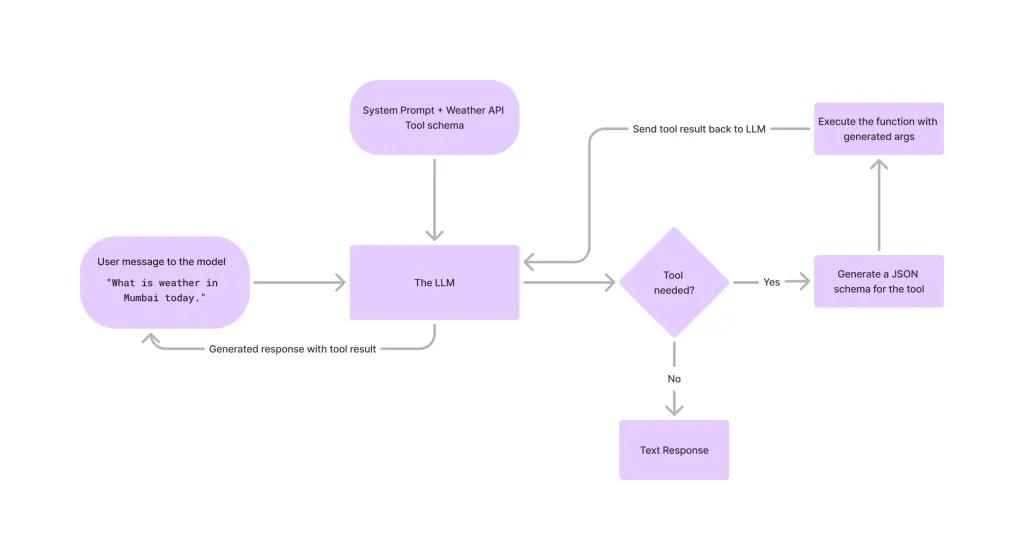 Tool Calling in LLMsApr 14, 2025 am 11:28 AM
Tool Calling in LLMsApr 14, 2025 am 11:28 AMLarge language models (LLMs) have surged in popularity, with the tool-calling feature dramatically expanding their capabilities beyond simple text generation. Now, LLMs can handle complex automation tasks such as dynamic UI creation and autonomous a
 How ADHD Games, Health Tools & AI Chatbots Are Transforming Global HealthApr 14, 2025 am 11:27 AM
How ADHD Games, Health Tools & AI Chatbots Are Transforming Global HealthApr 14, 2025 am 11:27 AMCan a video game ease anxiety, build focus, or support a child with ADHD? As healthcare challenges surge globally — especially among youth — innovators are turning to an unlikely tool: video games. Now one of the world’s largest entertainment indus
 UN Input On AI: Winners, Losers, And OpportunitiesApr 14, 2025 am 11:25 AM
UN Input On AI: Winners, Losers, And OpportunitiesApr 14, 2025 am 11:25 AM“History has shown that while technological progress drives economic growth, it does not on its own ensure equitable income distribution or promote inclusive human development,” writes Rebeca Grynspan, Secretary-General of UNCTAD, in the preamble.
 Learning Negotiation Skills Via Generative AIApr 14, 2025 am 11:23 AM
Learning Negotiation Skills Via Generative AIApr 14, 2025 am 11:23 AMEasy-peasy, use generative AI as your negotiation tutor and sparring partner. Let’s talk about it. This analysis of an innovative AI breakthrough is part of my ongoing Forbes column coverage on the latest in AI, including identifying and explaining
 TED Reveals From OpenAI, Google, Meta Heads To Court, Selfie With MyselfApr 14, 2025 am 11:22 AM
TED Reveals From OpenAI, Google, Meta Heads To Court, Selfie With MyselfApr 14, 2025 am 11:22 AMThe TED2025 Conference, held in Vancouver, wrapped its 36th edition yesterday, April 11. It featured 80 speakers from more than 60 countries, including Sam Altman, Eric Schmidt, and Palmer Luckey. TED’s theme, “humanity reimagined,” was tailor made
 Joseph Stiglitz Warns Of The Looming Inequality Amid AI Monopoly PowerApr 14, 2025 am 11:21 AM
Joseph Stiglitz Warns Of The Looming Inequality Amid AI Monopoly PowerApr 14, 2025 am 11:21 AMJoseph Stiglitz is renowned economist and recipient of the Nobel Prize in Economics in 2001. Stiglitz posits that AI can worsen existing inequalities and consolidated power in the hands of a few dominant corporations, ultimately undermining economic
 What is Graph Database?Apr 14, 2025 am 11:19 AM
What is Graph Database?Apr 14, 2025 am 11:19 AMGraph Databases: Revolutionizing Data Management Through Relationships As data expands and its characteristics evolve across various fields, graph databases are emerging as transformative solutions for managing interconnected data. Unlike traditional
 LLM Routing: Strategies, Techniques, and Python ImplementationApr 14, 2025 am 11:14 AM
LLM Routing: Strategies, Techniques, and Python ImplementationApr 14, 2025 am 11:14 AMLarge Language Model (LLM) Routing: Optimizing Performance Through Intelligent Task Distribution The rapidly evolving landscape of LLMs presents a diverse range of models, each with unique strengths and weaknesses. Some excel at creative content gen


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

ZendStudio 13.5.1 Mac
Powerful PHP integrated development environment





