 Technology peripherals
Technology peripherals AI
AI Xiaomi's AI strength has been verified again, and its voice recognition algorithm capability ranks among the best in the world.
Xiaomi's AI strength has been verified again, and its voice recognition algorithm capability ranks among the best in the world.Xiaomi's AI strength has been verified again, and its voice recognition algorithm capability ranks among the best in the world.
Recently, Xiaomi has made the latest progress in voice recognition algorithms. Its algorithm model is ahead of other institutions in terms of performance and ranks at the top of international rankings. This breakthrough was achieved by Xiaomi in the AudioSet audio labeling task released by Google
Google divided the AudioSet data set into three subsets. The first two subsets were used for training and were merged and called "AudioSet-2M". It was in this merged training set that Xiaomi's voice recognition algorithm model broke through 50 mAP in the industry, refreshing audio marking technical indicators. In addition, Xiaomi also released a Mini version of the model, suitable for resource-constrained scenarios.
The breakthrough of this technology means another breakthrough in Xiaomi's sound recognition algorithm capabilities. After Xiaomi's many smart hardware devices apply this technology, they can capture and identify environmental sounds more keenly, greatly improving the intelligence of the hardware. This creates a more convenient smart life experience for users.
At the same time, Xiaomi’s audio tagging technology capabilities under the voice recognition algorithm have effectively promoted the research and development process of cutting-edge research in the industry.
Xiaomi’s improved voice recognition algorithm can be widely used in Xiaomi’s smart devices. The audio tagging algorithm can identify a wide range of environmental sounds, such as babies crying, animal sounds, car engines, explosions, smoke alarms, doorbells, water flows, etc., and allow the sounds in the environment to be expressed in modalities such as text, Let the sound be "seen". This can make hardware devices smarter and bring users a more efficient and accurate voice recognition experience.
The "Xiaomi Hearing Sound" function in Xiaomi mobile phones can monitor 14 important environmental sounds including fire alarms, babies crying, kettle boiling sounds, etc., and push text messages through the mobile phone notification bar. This function effectively helps the lives of hearing-impaired people, and the Xiaomi bracelet can also display and receive these sound information simultaneously
This algorithm is more widely used in smart home devices. Currently, Xiaomi's voice recognition algorithm has been used in many smart home devices, such as the baby cry monitoring function of Mijia cameras, which can push notifications to users' mobile phones in real time when it detects a baby crying. The Xiaomi Sound speaker is also equipped with a sound recognition function, which can identify six types of home environment sounds that users care about, including home alarms, crying babies, fire alarms, running water, cats meowing, and dogs barking. Xiaomi Health APP’s sleep snoring monitoring can help track users’ snoring and sleep talking during sleep.
In order to better realize the potential of this algorithm, Xiaomi provides a broad space for the application of this algorithm technology through its AIoT platform ecosystem. At present, Xiaomi's acoustic voice team has fully applied its self-developed acoustic voice technology to more than 5,000 smart products in 79 categories including Xiaomi mobile phones, speakers, TVs, headphones, watches, and robots.
In the field of artificial intelligence, which belongs to the voice recognition algorithm, Xiaomi is actively involved in it, as one of the bottom tracks that Xiaomi has continued to invest in for a long time. It is reported that since Xiaomi established its AI team in 2016, the AI team has expanded six times in seven years and has reached more than 3,000 people. At the same time, Xiaomi's AI technical capabilities have also covered many directions such as vision, acoustics, speech, NLP, knowledge graphs, machine learning, large models, and multi-modality, and have fully empowered many business sectors such as mobile phones, automobiles, AIoT, and robots. . In April this year, Xiaomi officially established an AI large model team to fully embrace large models, and there are currently some application attempts. The first application model is to upgrade the intelligent voice assistant Xiao Ai to a large model version and open invitation testing.

The above is the detailed content of Xiaomi's AI strength has been verified again, and its voice recognition algorithm capability ranks among the best in the world.. For more information, please follow other related articles on the PHP Chinese website!
 What is Graph of Thought in Prompt EngineeringApr 13, 2025 am 11:53 AM
What is Graph of Thought in Prompt EngineeringApr 13, 2025 am 11:53 AMIntroduction In prompt engineering, “Graph of Thought” refers to a novel approach that uses graph theory to structure and guide AI’s reasoning process. Unlike traditional methods, which often involve linear s
 Optimize Your Organisation's Email Marketing with GenAI AgentsApr 13, 2025 am 11:44 AM
Optimize Your Organisation's Email Marketing with GenAI AgentsApr 13, 2025 am 11:44 AMIntroduction Congratulations! You run a successful business. Through your web pages, social media campaigns, webinars, conferences, free resources, and other sources, you collect 5000 email IDs daily. The next obvious step is
 Real-Time App Performance Monitoring with Apache PinotApr 13, 2025 am 11:40 AM
Real-Time App Performance Monitoring with Apache PinotApr 13, 2025 am 11:40 AMIntroduction In today’s fast-paced software development environment, ensuring optimal application performance is crucial. Monitoring real-time metrics such as response times, error rates, and resource utilization can help main
 ChatGPT Hits 1 Billion Users? 'Doubled In Just Weeks' Says OpenAI CEOApr 13, 2025 am 11:23 AM
ChatGPT Hits 1 Billion Users? 'Doubled In Just Weeks' Says OpenAI CEOApr 13, 2025 am 11:23 AM“How many users do you have?” he prodded. “I think the last time we said was 500 million weekly actives, and it is growing very rapidly,” replied Altman. “You told me that it like doubled in just a few weeks,” Anderson continued. “I said that priv
 Pixtral-12B: Mistral AI's First Multimodal Model - Analytics VidhyaApr 13, 2025 am 11:20 AM
Pixtral-12B: Mistral AI's First Multimodal Model - Analytics VidhyaApr 13, 2025 am 11:20 AMIntroduction Mistral has released its very first multimodal model, namely the Pixtral-12B-2409. This model is built upon Mistral’s 12 Billion parameter, Nemo 12B. What sets this model apart? It can now take both images and tex
 Agentic Frameworks for Generative AI Applications - Analytics VidhyaApr 13, 2025 am 11:13 AM
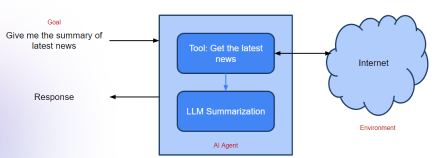
Agentic Frameworks for Generative AI Applications - Analytics VidhyaApr 13, 2025 am 11:13 AMImagine having an AI-powered assistant that not only responds to your queries but also autonomously gathers information, executes tasks, and even handles multiple types of data—text, images, and code. Sounds futuristic? In this a
 Applications of Generative AI in the Financial SectorApr 13, 2025 am 11:12 AM
Applications of Generative AI in the Financial SectorApr 13, 2025 am 11:12 AMIntroduction The finance industry is the cornerstone of any country’s development, as it drives economic growth by facilitating efficient transactions and credit availability. The ease with which transactions occur and credit
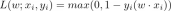 Guide to Online Learning and Passive-Aggressive AlgorithmsApr 13, 2025 am 11:09 AM
Guide to Online Learning and Passive-Aggressive AlgorithmsApr 13, 2025 am 11:09 AMIntroduction Data is being generated at an unprecedented rate from sources such as social media, financial transactions, and e-commerce platforms. Handling this continuous stream of information is a challenge, but it offers an


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Chinese version
Chinese version, very easy to use

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

Dreamweaver Mac version
Visual web development tools

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.




