 Operation and Maintenance
Operation and Maintenance Linux Operation and Maintenance
Linux Operation and Maintenance The Ultimate Guide to Linux Server Security: Use These Commands
The Ultimate Guide to Linux Server Security: Use These Commands
Linux server is a very common server operating system in a network environment. Due to its open source code and high customizability, it is favored by many enterprises and individual users. However, because of its widespread use, Linux servers have also become the target of hacker attacks and security threats. In order to protect the security of Linux servers, it is very important to use some commands. This article will introduce some commonly used commands to help you improve the security of your Linux server.
The first thing is to update and upgrade the software. To prevent known vulnerabilities and security vulnerabilities from being exploited, it is crucial to keep the software on your server updated and upgraded. Fortunately, Linux provides some commands to upgrade and update software. The most commonly used commands are the following:
-
apt-get update- This command will update the software source list to include the latest software package information. -
apt-get upgrade- This command will upgrade installed packages on the server. -
apt-get dist-upgrade- This command will upgrade installed packages on the server and resolve all dependencies.
In addition to updating and upgrading software, you also need to monitor your server’s network connections and activity. Here are some commonly used commands to monitor a server's network connections and related activities:
-
netstat- This command will display the current network connections. -
nmap- This command scans open ports on the server. -
tcpdump- This command captures network traffic packets on the server.
Next, let’s talk about access control and permission management. To ensure that only authorized users can access the server, we need to set up appropriate access control and permission management. Here are some commonly used commands:
-
chmod- This command is used to change the permissions of a file or directory. -
chown- This command is used to change the owner of a file or directory. -
chgrp- This command is used to change the group of a file or directory.
Setting strong passwords on Linux servers is also a core task. Here are some useful commands to set and manage user passwords:
-
passwd- This command is used to change user passwords. -
chpasswd- This command can batch change user passwords by inputting files.
In addition, there are some additional commands that can help you further improve the security of your Linux server. For example:
-
sudo- This command allows a specific user to run commands with root privileges. -
ufw- This command is used to configure firewall rules. -
fail2ban- This command automatically detects and blocks brute force attempts.
Last but not least, back up your server data regularly. Backups are key to recovering your data and systems, whether data is lost due to a security threat, hardware failure, or other reasons. Here are some commonly used commands to backup server data:
-
rsync- This command can synchronize and backup files between remote servers. -
tar- This command can package files and directories into .tar files.
In short, by using these commands correctly, you can help improve the security of your Linux server. However, it should be noted that these commands only provide some basic security strategies and methods and cannot guarantee 100% security. Therefore, it is crucial to continually learn and understand the latest security technologies and best practices.
The above is the detailed content of The Ultimate Guide to Linux Server Security: Use These Commands. For more information, please follow other related articles on the PHP Chinese website!
 如何配置Nginx代理服务器以保护Web服务的用户身份验证信息?Sep 05, 2023 pm 12:40 PM
如何配置Nginx代理服务器以保护Web服务的用户身份验证信息?Sep 05, 2023 pm 12:40 PM如何配置Nginx代理服务器以保护Web服务的用户身份验证信息?导语:在当今的互联网世界中,保护用户的身份验证信息至关重要。Nginx是一个功能强大的代理服务器,它可以帮助我们实现身份验证信息的保护。本文将介绍如何配置Nginx代理服务器以保护Web服务的用户身份验证信息,并提供一些代码示例。一、安装Nginx首先,我们需要安装Nginx。在大多数Linux
 Golang开发:实现基于JWT的用户身份验证Sep 20, 2023 am 08:31 AM
Golang开发:实现基于JWT的用户身份验证Sep 20, 2023 am 08:31 AMGolang开发:实现基于JWT的用户身份验证随着互联网的快速发展,用户身份验证成为了Web应用中至关重要的一部分。传统的基于Cookie的身份验证方式已经逐渐被基于JWT(JSONWebToken)的身份验证方式所取代。JWT是一种轻量级的身份验证标准,它允许服务端生成一个加密的令牌,并将该令牌发送给客户端,客户端发送请求的时候将令牌放入Authori
 win7系统防火墙设置方法流程Mar 26, 2024 pm 07:40 PM
win7系统防火墙设置方法流程Mar 26, 2024 pm 07:40 PM1、打开设备,选取【控制面板】选项;如图所示:2、在网络和Internet一览中找到【查看网络状态和任务】,并将之打开;如图所示:3、接着,点击左下角的【防火墙】;如图所示:4、最后,依次点击左侧边栏中的选项完成调整即可。如图所示:
 微博评论防火墙怎么设置_微博评论防火墙设置方法Mar 29, 2024 pm 06:57 PM
微博评论防火墙怎么设置_微博评论防火墙设置方法Mar 29, 2024 pm 06:57 PM1、首先登录手机新浪微博,点击右上角的设置。2、然后进入设置页面,点击隐私设置。3、最后进入隐私设置页面,找到评论防火墙,点击开启即可。
 Win10怎样禁止cdr联网Win10完全禁止cdr联网教程Jul 14, 2023 pm 01:25 PM
Win10怎样禁止cdr联网Win10完全禁止cdr联网教程Jul 14, 2023 pm 01:25 PMWin10怎样禁止cdr联网?我们在应用cdr软件时,有时必须在操控的历程中完全禁止cdr联网,碰到这种的状况该怎么操作设定呢?今日咱们以Win10系统软件为例子为我们介绍一下完全禁止cdr联网的操作流程!Win10完全禁止cdr联网教程1、最先大家打开电脑=按win+PauseBreak键盘快捷键,寻找系统属性对话框,点击操作面板。2、如下图所示,开启赶到操作面板网页页面,鼠标点击“系统软件和安全性”。3、如下图所示,大家开启“系统软件和安全性”的选择项,然后电脑鼠标选择“WindowsDef
 win10系统不能连接steam的处理方法Jul 13, 2023 pm 03:01 PM
win10系统不能连接steam的处理方法Jul 13, 2023 pm 03:01 PM最近,win10系统用户显示使用计算机下载游戏,但发现系统不能连接到steam,用户尝试了很多方法来解决这个问题,所以win10系统不能连接steam怎么办?以下作者将分享win10系统不能连接steam的解决方案教程。win10系统不能连接steam的处理方法:1.点击开始菜单栏的steam。如图所示:2.选择更多,打开文件的位置。如图所示:3.找到steam快捷方式文件夹,右键单击快捷方式选择属性。如图所示:4.在属性界面找到目标路径。如图所示:5.在路径结束时输入空间,然后输入-TCP,然
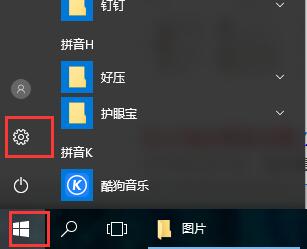 如何设置win10防火墙Dec 29, 2023 pm 05:55 PM
如何设置win10防火墙Dec 29, 2023 pm 05:55 PM很多的用户们使用电脑的时候,电脑中的防火墙是个很烦的东西,但是这个防火墙怎么设置呢,今天本站就为广大用户们介绍下详细的步骤吧~win10防火墙在哪里设置:1、首先在桌面右下的菜单中,点击“设置”。2、然后在打开的窗口中,选择“网络和Internet”。3、然后在该窗口中,点击“以太网”选项。4、然后在以太网中,点击“Windows防火墙”。5、然后在选项中,选择“启用或关闭Windows防火墙”。6、然后就能够进行防火墙的关闭和开启等,然后点击确定。
 win7系统怎么添加防火墙设备Jun 29, 2023 pm 12:48 PM
win7系统怎么添加防火墙设备Jun 29, 2023 pm 12:48 PMwin7系统怎么添加防火墙设备?在使用带电脑的时候,为了使用起来更加的安全,我们可以去设置一个防火墙。这样在遇到危险程序的时候,电脑就会自动进行防御了。那么这个防火墙要怎么去设置,很多小伙伴不知道怎么详细操作,小编下面整理了win7系统防火墙设置方法,如果你感兴趣的话,跟着小编一起往下看看吧! win7系统防火墙设置方法 1、打开控制面板,点击网络和Internet下的查看网络状态和任务。 2、点击下方的windowsdefender防火墙。 3、选择你需要设置的内容。 4、打开允


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

Atom editor mac version download
The most popular open source editor

Dreamweaver Mac version
Visual web development tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 English version
Recommended: Win version, supports code prompts!





