 Operation and Maintenance
Operation and Maintenance Linux Operation and Maintenance
Linux Operation and Maintenance Hardening Linux Servers: Configuring Security with Command Line Tools
Hardening Linux Servers: Configuring Security with Command Line Tools
In today’s digital era, servers are one of the core infrastructures of companies and organizations. In order to ensure the security and stability of the server, we need to take a series of protective measures. One of the important protective measures is to harden the security of Linux servers. This article will introduce how to configure and harden the security of Linux servers through command line tools.
- Disable unnecessary services and ports: First, we need to check the services and open ports running on the server, and disable unnecessary services and ports. You can use the command "netstat -tuln" to view the currently listening port. Then, use the command "systemctl stop
" to stop unnecessary services, and use the command "systemctl disable " to disable automatic startup at boot. - Update operating system and software packages: Timely updating of operating systems and software packages is an important step in keeping your server secure. We can use the commands "sudo apt update" and "sudo apt upgrade" to update the Ubuntu system and software packages. For other Linux distributions, updates can be made according to the corresponding package manager.
- Configure the firewall: Use a firewall to limit access to the server and protect the server from network attacks. On Linux, you can use iptables or ufw to configure firewall rules. For specific operations, please refer to the corresponding documents or tutorials.
- Use key to log in: Using key to log in can increase the security of the login process. First, we need to generate a public and private key pair locally. Then, copy the public key to the "~/.ssh/authorized_keys" file on the server. Finally, disable password login and enable key login by modifying the "/etc/ssh/sshd_config" file.
- Manage users and access permissions: Restricting user permissions is one of the key measures to protect the server. We can use the command "sudo adduser
" to create a new user and add it to the sudo group through the command "sudo usermod -aG sudo ". In addition, by editing the sudoers file with the command "sudo visudo", you can perform more fine-grained permission management for different users or user groups. - Logs and monitoring: By monitoring log files, we can detect abnormal behaviors and security events in a timely manner. You can use the command "tail -f
" to view log file updates in real time. In addition, you can use tools such as fail2ban to automatically analyze and block malicious behavior. - Regular backup: No matter how powerful the security measures are, they cannot guarantee the absolute security of the server. Regular backups are an important way to avoid data loss and restore your system. You can use tools such as rsync or backup software to regularly back up critical data.
- Encrypted transmission: In order to protect the security of data during transmission, we should use encryption protocols such as SSH, TLS/SSL, etc. for remote connection and data transmission.
- Update passwords and keys regularly: Updating passwords and keys regularly is an essential step in keeping your server secure. It is recommended to change passwords regularly and generate new key pairs regularly.
- Security audit and penetration testing: By conducting security audits and penetration testing, we can discover security risks in the server and take timely measures to repair them.
To summarize, various security configurations and reinforcement measures can be performed on Linux servers through command line tools. During operation, you need to remain vigilant and cautious, and keep an eye on the latest security vulnerabilities and threats. Only by continuously strengthening the security of the server can the stable operation of the server and the security of the data be ensured.
The above is the detailed content of Hardening Linux Servers: Configuring Security with Command Line Tools. For more information, please follow other related articles on the PHP Chinese website!
 Linux服务器的SSH连接断开问题如何解决?Jun 30, 2023 pm 08:27 PM
Linux服务器的SSH连接断开问题如何解决?Jun 30, 2023 pm 08:27 PM如何解决Linux服务器上的SSH连接中断问题随着云计算和远程工作的普及,远程连接到Linux服务器成为了日常工作中不可或缺的一部分。然而,有时SSH连接可能会出现中断的情况,给我们带来不便和困扰。本文将分享一些解决Linux服务器上SSH连接中断问题的方法,帮助您更好地管理和维护服务器。一、网络问题首先,我们需要排除网络问题。网络稳定与否直接影响到SSH连
 如何解决Linux服务器上的SSH连接中断和拒绝问题Jun 29, 2023 am 09:02 AM
如何解决Linux服务器上的SSH连接中断和拒绝问题Jun 29, 2023 am 09:02 AM如何解决Linux服务器上的SSH连接中断和拒绝问题在日常的运维工作中,使用SSH(SecureShell)进行远程连接是非常常见的操作。尽管SSH是一种安全可靠的协议,但有时仍然会遇到连接中断和拒绝的问题。这些问题可能由于各种原因引起,本文将介绍一些常见的解决方法。检查网络连接首先,确认服务器和本地机器之间的网络连接是否正常。可以通过ping命令来测试服
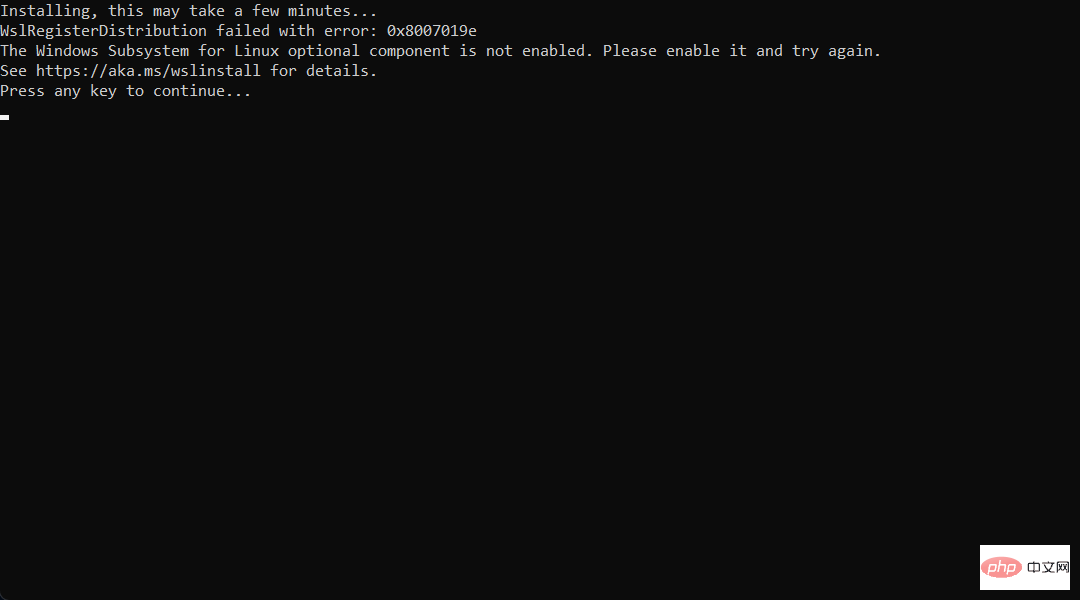 想在 Windows 11 上安装 AlmaLinux?这是怎么做的Apr 30, 2023 pm 08:13 PM
想在 Windows 11 上安装 AlmaLinux?这是怎么做的Apr 30, 2023 pm 08:13 PM在MicrosoftStore中,现在有一个版本的AlmaLinux与适用于Linux的Windows子系统兼容。这为用户提供了一系列令人印象深刻的新选项,因此我们将向您展示如何在Windows11上安装AlmaLinux。它于2021年3月发布,提供了第一个稳定的生产版本,此后该非营利基金会增加了许多新成员。最近的AMD是上个月加入的,时间是2022年3月。借助适用于Linux的Windows子系统,在Windows和Linux世界中工作的开
 Linux服务器安全:使用命令检查系统漏洞Sep 08, 2023 pm 03:39 PM
Linux服务器安全:使用命令检查系统漏洞Sep 08, 2023 pm 03:39 PMLinux服务器安全:使用命令检查系统漏洞概述:在当今的数字化环境中,服务器安全性是至关重要的。针对已知漏洞进行及时的检测和修复,能够有效地保护服务器免受潜在的攻击威胁。本文将介绍一些常用的命令,可用于在Linux服务器上检查系统漏洞,并提供相关的代码示例。通过正确使用这些命令,您将能够增强服务器的安全性。检查系统更新:在开始进行漏洞检查之前,确保您的系统已
 提供更强大的Web接口安全性:Linux服务器的关键实践。Sep 08, 2023 pm 12:51 PM
提供更强大的Web接口安全性:Linux服务器的关键实践。Sep 08, 2023 pm 12:51 PM提供更强大的Web接口安全性:Linux服务器的关键实践在当今的数字时代,Web接口安全性变得越来越重要。随着越来越多的应用和服务转移到云端,服务器安全保护也日益成为关键问题。Linux作为最常用的服务器操作系统之一,其安全性的保护至关重要。本文将介绍一些关键实践,帮助您提供更强大的Web接口安全性。更新和维护操作系统和软件及时进行操作系统和软件的更新是服务
 Linux服务器上常见的日志文件损坏问题及其修复方法Jun 29, 2023 pm 06:00 PM
Linux服务器上常见的日志文件损坏问题及其修复方法Jun 29, 2023 pm 06:00 PMLinux服务器上常见的日志文件损坏问题及其修复方法摘要:日志文件是Linux服务器中非常重要的组成部分,它记录了系统运行过程中的各种操作和事件。然而,由于各种原因,日志文件有时会出现损坏问题,导致服务器无法正常分析和调试。本文将探讨一些常见的日志文件损坏问题,并提供相应的解决方法。引言:在Linux服务器运行过程中,日志文件扮演着至关重要的角色。它们记录了
 Linux服务器防御:保护Web接口免受恶意文件上传攻击。Sep 09, 2023 am 09:06 AM
Linux服务器防御:保护Web接口免受恶意文件上传攻击。Sep 09, 2023 am 09:06 AMLinux服务器防御:保护Web接口免受恶意文件上传攻击近年来,随着网络的普及和发展,Web应用程序的使用越来越广泛。然而,与之伴随而来的是各种安全威胁,其中之一就是恶意文件上传攻击。恶意文件上传攻击是指攻击者向服务器上传包含恶意代码的文件,从而获取服务器权限或者传播恶意内容。为了保护Web接口免受恶意文件上传攻击,我们可以采取一些有效的防御措施。下面将介绍
 Linux服务器安全加固:配置和优化您的系统Sep 08, 2023 pm 03:19 PM
Linux服务器安全加固:配置和优化您的系统Sep 08, 2023 pm 03:19 PMLinux服务器安全加固:配置和优化您的系统引言:在当今信息安全威胁日益增加的环境中,保护您的Linux服务器免受恶意攻击和未经授权的访问变得至关重要。为了加固系统安全,您需要采取一系列的安全措施,以保护您的服务器和其中存储的敏感数据。本文将介绍一些关键的配置和优化步骤,以提高您的Linux服务器的安全性。一、更新和管理软件包安装最新的软件包和更新对于保持系


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

Dreamweaver Mac version
Visual web development tools

Notepad++7.3.1
Easy-to-use and free code editor

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft





