 Operation and Maintenance
Operation and Maintenance Linux Operation and Maintenance
Linux Operation and Maintenance How to implement strong web interface defense on Linux servers?
How to implement strong web interface defense on Linux servers?
How to implement powerful web interface defense on Linux server?
With the rapid development of the Internet, Web interfaces have become an important bridge for data exchange between systems, and have also become one of the main targets for attackers to attack servers. In order to protect the security of the server, we need to implement a powerful web interface defense solution on the Linux server. This article will introduce some commonly used defense technologies and methods, and provide some implementation example codes.
- Using a Web Firewall
A Web Application Firewall (WAF) is a tool that can monitor and filter HTTP and HTTPS traffic entering your server. It can detect and block various attacks such as SQL injection, cross-site scripting (XSS) and cross-site request forgery (CSRF). Commonly used web firewall software includes ModSecurity, NAXSI and Django Defend, etc.
The following is a sample code for web firewall configuration using ModSecurity:
# 安装ModSecurity模块 sudo apt-get install libapache2-modsecurity # 启用ModSecurity模块 sudo a2enmod mod_security # 配置ModSecurity规则 sudo nano /etc/modsecurity/modsecurity.conf # 在配置文件中添加以下规则 SecRuleEngine On SecAuditLog /var/log/apache2/modsec_audit.log SecAuditEngine On # 重启Apache服务器使配置生效 sudo service apache2 restart
- Implementing an access control list (ACL)
ACL is a method used to restrict the network A traffic mechanism used to control who can access the web interface on the server and under what circumstances. ACLs allow us to define access rules based on IP address, user authentication, and other factors. Commonly used tools include iptables and Nginx.
The following is a sample code that uses iptables to implement access control lists:
# 添加允许访问Web接口的IP地址 sudo iptables -A INPUT -s 192.168.0.1/32 -p tcp --dport 80 -j ACCEPT # 屏蔽来自指定IP地址的请求 sudo iptables -A INPUT -s 192.168.0.2/32 -j DROP # 查看已添加的iptables规则 sudo iptables -L
- Protect the transmission of sensitive data
When transmitting sensitive data in the web interface, use Encryption protocols are very important. HTTPS (Secure HTTP) is a way of providing encryption and authentication for data transmission via the SSL/TLS protocol. We can enable HTTPS using an SSL certificate on the server. Commonly used tools include OpenSSL and Apache’s mod_ssl module.
The following is a sample code that uses OpenSSL to generate a self-signed SSL certificate:
# 安装OpenSSL软件包 sudo apt-get install openssl # 生成私钥 sudo openssl genrsa -out private.key 2048 # 生成自签名证书请求(CSR) sudo openssl req -new -key private.key -out csr.csr # 生成自签名证书 sudo openssl x509 -req -days 365 -in csr.csr -signkey private.key -out certificate.crt # 配置Apache服务器使用SSL证书 sudo nano /etc/apache2/sites-available/default-ssl.conf # 将以下配置项添加到配置文件中 SSLEngine on SSLCertificateFile /path/to/certificate.crt SSLCertificateKeyFile /path/to/private.key # 启用SSL模块 sudo a2enmod ssl # 重新启动Apache服务器使配置生效 sudo service apache2 restart
In summary, establishing strong web interface defense is a necessary step to protect server security. By using web firewalls, implementing access control lists and protecting the transmission of sensitive data, we can minimize the risk of potential attacks and data breaches. At the same time, we can make corresponding adjustments and optimizations according to specific needs and environments to ensure the security of the server.
Statement: The above sample code is for reference only. Please modify and configure it appropriately according to your actual needs and environment. When implementing any security measures, always exercise caution and back up relevant files.
The above is the detailed content of How to implement strong web interface defense on Linux servers?. For more information, please follow other related articles on the PHP Chinese website!
 如何解决Linux服务器上的SSH连接中断和拒绝问题Jun 29, 2023 am 09:02 AM
如何解决Linux服务器上的SSH连接中断和拒绝问题Jun 29, 2023 am 09:02 AM如何解决Linux服务器上的SSH连接中断和拒绝问题在日常的运维工作中,使用SSH(SecureShell)进行远程连接是非常常见的操作。尽管SSH是一种安全可靠的协议,但有时仍然会遇到连接中断和拒绝的问题。这些问题可能由于各种原因引起,本文将介绍一些常见的解决方法。检查网络连接首先,确认服务器和本地机器之间的网络连接是否正常。可以通过ping命令来测试服
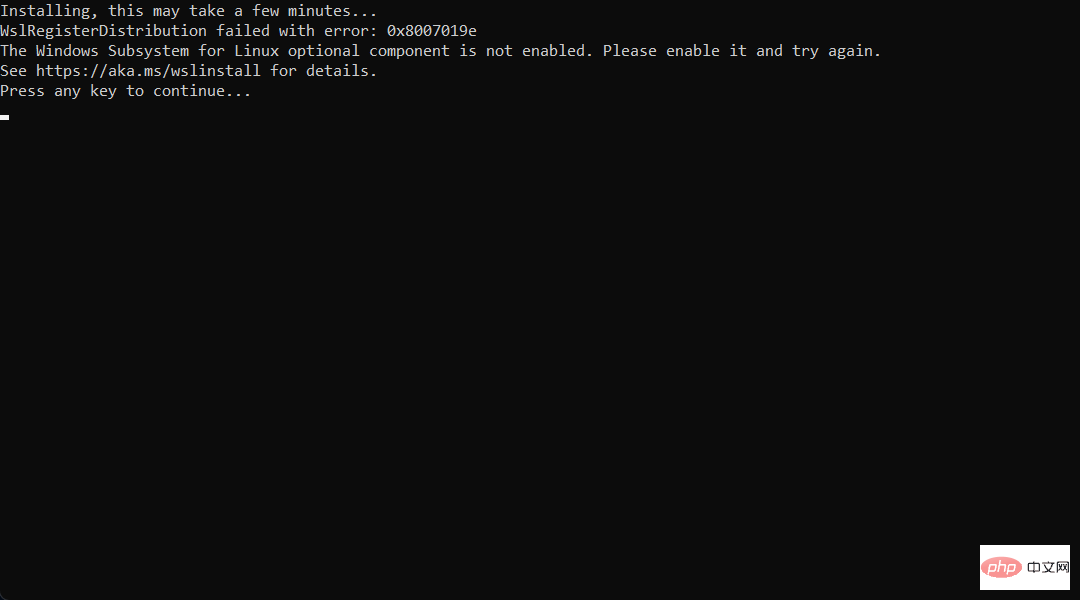 想在 Windows 11 上安装 AlmaLinux?这是怎么做的Apr 30, 2023 pm 08:13 PM
想在 Windows 11 上安装 AlmaLinux?这是怎么做的Apr 30, 2023 pm 08:13 PM在MicrosoftStore中,现在有一个版本的AlmaLinux与适用于Linux的Windows子系统兼容。这为用户提供了一系列令人印象深刻的新选项,因此我们将向您展示如何在Windows11上安装AlmaLinux。它于2021年3月发布,提供了第一个稳定的生产版本,此后该非营利基金会增加了许多新成员。最近的AMD是上个月加入的,时间是2022年3月。借助适用于Linux的Windows子系统,在Windows和Linux世界中工作的开
 PHP如何防止SSTI攻击?Jun 30, 2023 am 09:36 AM
PHP如何防止SSTI攻击?Jun 30, 2023 am 09:36 AM如何使用PHP防御Server-SideTemplateInjection(SSTI)攻击引言:Server-SideTemplateInjection(SSTI)是一种常见的Web应用程序安全漏洞,攻击者通过在模板引擎中注入恶意代码,可以导致服务器执行任意代码,从而造成严重的安全隐患。在PHP应用程序中,当不正确地处理用户输入时,可能会暴露出SST
 如何使用PHP防御跨站脚本(XSS)攻击Jun 29, 2023 am 10:46 AM
如何使用PHP防御跨站脚本(XSS)攻击Jun 29, 2023 am 10:46 AM如何使用PHP防御跨站脚本(XSS)攻击随着互联网的快速发展,跨站脚本(Cross-SiteScripting,简称XSS)攻击是最常见的网络安全威胁之一。XSS攻击主要是通过在网页中注入恶意脚本,从而实现获取用户敏感信息、盗取用户账号等目的。为了保护用户数据的安全,开发人员应该采取适当的措施来防御XSS攻击。本文将介绍一些常用的PHP防御XSS攻击的技术
 如何使用PHP和Vue.js开发防御敏感数据泄露的应用程序Jul 06, 2023 am 11:01 AM
如何使用PHP和Vue.js开发防御敏感数据泄露的应用程序Jul 06, 2023 am 11:01 AM如何使用PHP和Vue.js开发防御敏感数据泄露的应用程序在当今信息时代,个人和机构的隐私和敏感数据面临许多安全威胁,其中最常见的威胁之一就是数据泄露。为了防范这种风险,我们需要在开发应用程序时注重数据的安全性。本文将介绍如何使用PHP和Vue.js开发一个防御敏感数据泄露的应用程序,并提供相应的代码示例。使用安全的连接在进行数据传输时,确保使用安全的连接是
 如何使用PHP防御HTTP响应拆分与HTTP参数污染攻击Jun 29, 2023 am 10:01 AM
如何使用PHP防御HTTP响应拆分与HTTP参数污染攻击Jun 29, 2023 am 10:01 AM如何使用PHP防御HTTP响应拆分与HTTP参数污染攻击随着互联网的不断发展,网络安全问题也变得越来越重要。HTTP响应拆分与HTTP参数污染攻击是常见的网络安全漏洞,会导致服务器受到攻击和数据泄露的风险。本文将介绍如何使用PHP来防御这两种攻击形式。一、HTTP响应拆分攻击HTTP响应拆分攻击是指攻击者通过发送特制的请求,使服务器返回多个独立的HTTP响应
 如何使用PHP防止SQL注入攻击Jun 24, 2023 am 10:31 AM
如何使用PHP防止SQL注入攻击Jun 24, 2023 am 10:31 AM在网络安全领域里,SQL注入攻击是一种常见的攻击方式。它利用恶意用户提交的恶意代码来改变应用程序的行为以执行不安全的操作。常见的SQL注入攻击包括查询操作、插入操作和删除操作。其中,查询操作是最常被攻击的一种,而防止SQL注入攻击的一个常用的方法是使用PHP。PHP是一种常用的服务器端脚本语言,它在web应用程序中的使用非常广泛。PHP可以与MySQL等关系
 PHP防御XSS与远程代码执行攻击的方法Jun 30, 2023 am 08:04 AM
PHP防御XSS与远程代码执行攻击的方法Jun 30, 2023 am 08:04 AM如何使用PHP防御跨站脚本(XSS)与远程代码执行攻击引言:在当今互联网世界中,安全性成为了一个至关重要的问题。XSS(跨站脚本攻击)和远程代码执行攻击是两种最常见的安全漏洞之一。本文将探讨如何使用PHP语言来防御这两种攻击,并提供几种方法和技巧来保护网站免受这些攻击的威胁。一、了解XSS攻击XSS攻击是指攻击者通过在网站上注入恶意脚本来获取用户的个人信息、


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.





