 Backend Development
Backend Development PHP Tutorial
PHP Tutorial Strengthening strategies and measures for PHP communication security
Strengthening strategies and measures for PHP communication securityStrategies and measures for strengthening PHP communication security
In today's information age, network communication has become an indispensable part of people's lives and work. However, due to the openness and convenience of the network, communication security issues have become increasingly prominent. For developers who use PHP for network communication, strategies and measures to strengthen communication security are crucial.
- Use HTTPS for data transmission
Using HTTPS protocol for data transmission is the basis for strengthening communication security. HTTPS can effectively prevent data from being eavesdropped and tampered by encrypting the transport layer on top of HTTP. In PHP, we can use cURL library to send HTTPS requests. The following is a sample code that uses cURL to send HTTPS requests:
// 创建一个cURL资源 $ch = curl_init(); // 设置请求的URL curl_setopt($ch, CURLOPT_URL, "https://example.com/api"); // 设置SSL相关配置 curl_setopt($ch, CURLOPT_SSL_VERIFYPEER, true); curl_setopt($ch, CURLOPT_SSL_VERIFYHOST, 2); curl_setopt($ch, CURLOPT_CAINFO, '/path/to/ca_cert.pem'); // 执行请求并获取响应 $response = curl_exec($ch); // 关闭cURL资源 curl_close($ch);
In the above example, we used the curl_setopt function to set cURL related parameters. The CURLOPT_SSL_VERIFYPEER parameter is used to verify the server certificate, the CURLOPT_SSL_VERIFYHOST parameter is used to verify the consistency of the host name and certificate, and the CURLOPT_CAINFO parameter specifies the path to the CA certificate.
- Data Encryption and Decryption
In addition to using HTTPS for transmission, we can also encrypt sensitive data. PHP provides a variety of encryption algorithms, such as RSA, AES, etc. Below is a sample code for encryption and decryption using AES:
// 加密数据
function encrypt($data, $key) {
$iv = openssl_random_pseudo_bytes(openssl_cipher_iv_length('aes-256-cbc'));
$encrypted = openssl_encrypt($data, 'aes-256-cbc', $key, 0, $iv);
return base64_encode($iv . $encrypted);
}
// 解密数据
function decrypt($data, $key) {
$data = base64_decode($data);
$iv = substr($data, 0, openssl_cipher_iv_length('aes-256-cbc'));
$decrypted = openssl_decrypt(substr($data, openssl_cipher_iv_length('aes-256-cbc')), 'aes-256-cbc', $key, 0, $iv);
return $decrypted;
}
// 使用示例
$data = "Hello, world!";
$key = "mySecretKey";
$encryptedData = encrypt($data, $key);
$decryptedData = decrypt($encryptedData, $key);
echo "加密后的数据:{$encryptedData}
";
echo "解密后的数据:{$decryptedData}
"; In the above example, we use the openssl_encrypt function and the openssl_decrypt function for AES Encryption and decryption. The encryption function accepts the data to be encrypted, encryption key and other parameters, and returns the encrypted data. The decryption function accepts the data to be decrypted, the decryption key and other parameters, and returns the decrypted data.
- Preventing SQL Injection Attacks
SQL injection attacks refer to attackers obtaining illegal access rights or obtaining sensitive data by constructing malicious SQL statements. In PHP development, you can use prepared statements and bind parameters to prevent SQL injection attacks. The following is a sample code using prepared statements and bound parameters:
// 连接数据库
$dsn = "mysql:host=localhost;dbname=mydatabase";
$username = "myuser";
$password = "mypassword";
try {
$dbh = new PDO($dsn, $username, $password);
} catch (PDOException $e) {
die("连接数据库失败:" . $e->getMessage());
}
// 执行查询
$sql = "SELECT * FROM users WHERE username = :username AND password = :password";
$stmt = $dbh->prepare($sql);
$username = $_POST['username'];
$password = $_POST['password'];
$stmt->bindParam(':username', $username);
$stmt->bindParam(':password', $password);
$stmt->execute();
// 获取结果
$result = $stmt->fetch(PDO::FETCH_ASSOC);
// 处理结果
if ($result) {
// 登录成功
} else {
// 登录失败
}In the above example, we used PDO (PHP Data Objects) to connect to the database and execute queries. Prepared statements avoid directly splicing SQL statements by binding parameters with placeholders, thus effectively preventing SQL injection attacks.
Summary:
The above are several commonly used strategies and measures to enhance PHP communication security. By using HTTPS for data transmission, data encryption and decryption, and preventing SQL injection attacks, we can effectively protect data security during the communication process. In actual development, we should choose appropriate strategies and measures to strengthen communication security based on specific needs and situations, thereby protecting user privacy and system security.
The above is the detailed content of Strengthening strategies and measures for PHP communication security. For more information, please follow other related articles on the PHP Chinese website!
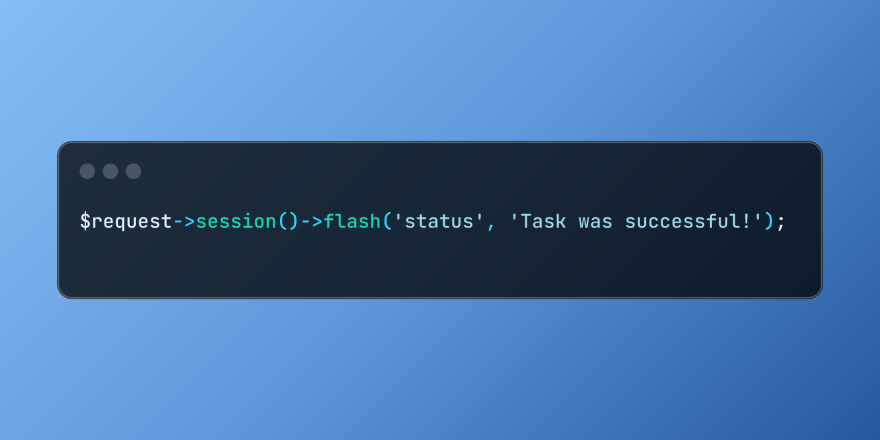 Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PM
Working with Flash Session Data in LaravelMar 12, 2025 pm 05:08 PMLaravel simplifies handling temporary session data using its intuitive flash methods. This is perfect for displaying brief messages, alerts, or notifications within your application. Data persists only for the subsequent request by default: $request-
 cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AM
cURL in PHP: How to Use the PHP cURL Extension in REST APIsMar 14, 2025 am 11:42 AMThe PHP Client URL (cURL) extension is a powerful tool for developers, enabling seamless interaction with remote servers and REST APIs. By leveraging libcurl, a well-respected multi-protocol file transfer library, PHP cURL facilitates efficient execution of various network protocols, including HTTP, HTTPS, and FTP. This extension offers granular control over HTTP requests, supports multiple concurrent operations, and provides built-in security features.
 Build a React App With a Laravel Back End: Part 2, ReactMar 04, 2025 am 09:33 AM
Build a React App With a Laravel Back End: Part 2, ReactMar 04, 2025 am 09:33 AMThis is the second and final part of the series on building a React application with a Laravel back-end. In the first part of the series, we created a RESTful API using Laravel for a basic product-listing application. In this tutorial, we will be dev
 Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PM
Simplified HTTP Response Mocking in Laravel TestsMar 12, 2025 pm 05:09 PMLaravel provides concise HTTP response simulation syntax, simplifying HTTP interaction testing. This approach significantly reduces code redundancy while making your test simulation more intuitive. The basic implementation provides a variety of response type shortcuts: use Illuminate\Support\Facades\Http; Http::fake([ 'google.com' => 'Hello World', 'github.com' => ['foo' => 'bar'], 'forge.laravel.com' =>
 12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PM
12 Best PHP Chat Scripts on CodeCanyonMar 13, 2025 pm 12:08 PMDo you want to provide real-time, instant solutions to your customers' most pressing problems? Live chat lets you have real-time conversations with customers and resolve their problems instantly. It allows you to provide faster service to your custom
 Notifications in LaravelMar 04, 2025 am 09:22 AM
Notifications in LaravelMar 04, 2025 am 09:22 AMIn this article, we're going to explore the notification system in the Laravel web framework. The notification system in Laravel allows you to send notifications to users over different channels. Today, we'll discuss how you can send notifications ov
 Explain the concept of late static binding in PHP.Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.Mar 21, 2025 pm 01:33 PMArticle discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 PHP Logging: Best Practices for PHP Log AnalysisMar 10, 2025 pm 02:32 PM
PHP Logging: Best Practices for PHP Log AnalysisMar 10, 2025 pm 02:32 PMPHP logging is essential for monitoring and debugging web applications, as well as capturing critical events, errors, and runtime behavior. It provides valuable insights into system performance, helps identify issues, and supports faster troubleshoot


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 English version
Recommended: Win version, supports code prompts!

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

Zend Studio 13.0.1
Powerful PHP integrated development environment

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),





