 Technology peripherals
Technology peripherals AI
AI Three ways artificial intelligence is changing cybersecurity and user experience
Three ways artificial intelligence is changing cybersecurity and user experienceThree ways artificial intelligence is changing cybersecurity and user experience
Currently, we are at a critical moment of major change. Artificial intelligence (AI) and machine learning (ML) are revolutionizing the way people work, communicate and get business done. These innovations will help organizations become more agile, better serve their customers, and help them respond to unprecedented threats.
Artificial intelligence continues to proliferate in our industry—the global AI in cybersecurity market is expected to reach nearly $47 billion by 2027, according to Statista. Interest in this technology will only continue to grow as we see new innovations emerge.
As organizations around the world adopt solutions that best leverage artificial intelligence, fundamentally changing the way they approach security, the key question that arises is how to achieve this artificial intelligence Driven state of nirvana. This means increasingly moving away from fragmented and siled tools to unlock the true potential of data.
The “3Cs” of data underpin powerful artificial intelligence and machine learning
In addition to the obvious benefits of simplified management, the integration of tools Another feature is the ability to leverage AI and ML in security, network and user experience management, all from the same data lake. However, for an organization to reach its full potential, it must adhere to three data principles:
• Complete data. All the data you need to solve the problem. Data elements from security, network and operations must be collected into a central location.
•Consistent data. The format, structure, and labeling of data should remain constant across all collected elements. Any discrepancies may negatively impact data quality and results.
•Correct data. You should have unwavering trust in the data so that any output is also trustworthy. The way data is collected and aggregated must be the same across all data sources that provide a data lake.
The solid foundation for artificial intelligence to fundamentally change cybersecurity is these key data principles. Organizations can see this impact in three different ways:
1) Reinventing IT Operations
As we all know, today’s core IT Operations teams, including security operations centers (SOCs) and network operations centers (NOCs), are overworked and understaffed. Every day, operations teams receive tens of thousands of alerts and events, only a few of which are meaningful, and most of the others are just noise. However, for the vast majority of enterprises, operational analysts currently need to manually review these alerts to ensure that no real threats are missed. Although this activity is time-consuming and requires a significant investment of time from security and network professionals, the results are rare.
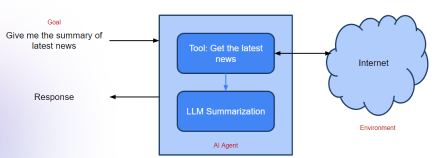
By introducing AIOps, deep visibility and automation across the network can be automated, covering all users, branches and applications. With this new AI-driven environment, alerts or events can be connected to larger data points for more effective solutions—all within minutes. This means that instead of someone sifting through thousands of meaningless alerts, AIOps can help extract the most relevant alerts so teams can focus on solving real problems.
2) Uncover Unknown Threats
#As technology advances, cybersecurity tools develop and the tools available to threat actors evolve. Synchronization. The power of artificial intelligence can help identify signs of malicious behavior or operations introduced by “unknown” or unseen variants, unlike anything humans do. Machines are very good at sifting through large volumes of alerts by scanning thousands of data points to pinpoint anomalies, constantly learning hyper-specific details about an organization to better position the technology to flag new anomalies as they arise. Once threats are identified, organizations can proactively classify and contain them before they become a real problem.
3) Improve user experience
The application of artificial intelligence can relieve the pressure on security and network teams and help end users easily overcome the frustrating problems Frustrating question. Troubleshooting access and performance issues has always been a tedious and time-consuming task. When user experience is hindered by this security process, it often results in them becoming frustrated and choosing to bypass security in order to quickly resolve the issue. In this case, organizations are vulnerable to attacks because actors may exploit user error to bypass security measures. By proactively solving problems faced by users, AI has the ability to autonomously manage the end-user’s digital experience. Ultimately, doing so gives users a clean and positive experience while keeping security intact.
Artificial intelligence has the ability to impact every aspect of our lives, such as assisting in creation, driving and predicting disease risks. And, as we begin to implement this new innovation into our organizations, we are starting to see that AI will have an equally profound impact on security and network operations, and ultimately the experience an individual or business team has with the technology.
The above is the detailed content of Three ways artificial intelligence is changing cybersecurity and user experience. For more information, please follow other related articles on the PHP Chinese website!
 What is Graph of Thought in Prompt EngineeringApr 13, 2025 am 11:53 AM
What is Graph of Thought in Prompt EngineeringApr 13, 2025 am 11:53 AMIntroduction In prompt engineering, “Graph of Thought” refers to a novel approach that uses graph theory to structure and guide AI’s reasoning process. Unlike traditional methods, which often involve linear s
 Optimize Your Organisation's Email Marketing with GenAI AgentsApr 13, 2025 am 11:44 AM
Optimize Your Organisation's Email Marketing with GenAI AgentsApr 13, 2025 am 11:44 AMIntroduction Congratulations! You run a successful business. Through your web pages, social media campaigns, webinars, conferences, free resources, and other sources, you collect 5000 email IDs daily. The next obvious step is
 Real-Time App Performance Monitoring with Apache PinotApr 13, 2025 am 11:40 AM
Real-Time App Performance Monitoring with Apache PinotApr 13, 2025 am 11:40 AMIntroduction In today’s fast-paced software development environment, ensuring optimal application performance is crucial. Monitoring real-time metrics such as response times, error rates, and resource utilization can help main
 ChatGPT Hits 1 Billion Users? 'Doubled In Just Weeks' Says OpenAI CEOApr 13, 2025 am 11:23 AM
ChatGPT Hits 1 Billion Users? 'Doubled In Just Weeks' Says OpenAI CEOApr 13, 2025 am 11:23 AM“How many users do you have?” he prodded. “I think the last time we said was 500 million weekly actives, and it is growing very rapidly,” replied Altman. “You told me that it like doubled in just a few weeks,” Anderson continued. “I said that priv
 Pixtral-12B: Mistral AI's First Multimodal Model - Analytics VidhyaApr 13, 2025 am 11:20 AM
Pixtral-12B: Mistral AI's First Multimodal Model - Analytics VidhyaApr 13, 2025 am 11:20 AMIntroduction Mistral has released its very first multimodal model, namely the Pixtral-12B-2409. This model is built upon Mistral’s 12 Billion parameter, Nemo 12B. What sets this model apart? It can now take both images and tex
 Agentic Frameworks for Generative AI Applications - Analytics VidhyaApr 13, 2025 am 11:13 AM
Agentic Frameworks for Generative AI Applications - Analytics VidhyaApr 13, 2025 am 11:13 AMImagine having an AI-powered assistant that not only responds to your queries but also autonomously gathers information, executes tasks, and even handles multiple types of data—text, images, and code. Sounds futuristic? In this a
 Applications of Generative AI in the Financial SectorApr 13, 2025 am 11:12 AM
Applications of Generative AI in the Financial SectorApr 13, 2025 am 11:12 AMIntroduction The finance industry is the cornerstone of any country’s development, as it drives economic growth by facilitating efficient transactions and credit availability. The ease with which transactions occur and credit
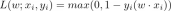 Guide to Online Learning and Passive-Aggressive AlgorithmsApr 13, 2025 am 11:09 AM
Guide to Online Learning and Passive-Aggressive AlgorithmsApr 13, 2025 am 11:09 AMIntroduction Data is being generated at an unprecedented rate from sources such as social media, financial transactions, and e-commerce platforms. Handling this continuous stream of information is a challenge, but it offers an


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Chinese version
Chinese version, very easy to use

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

Dreamweaver Mac version
Visual web development tools

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.





