How to protect Java applications from session hijacking attacks
With the continuous development of technology, the Internet has become an indispensable part of people's lives. More and more applications interact with users through the Internet, and many of them are developed using the Java language. However, the problem that comes with it is that Java applications are also facing a variety of security threats, one of which is session hijacking attacks. This article will describe how to protect Java applications from session hijacking attacks.
Session hijacking attack is a common network attack method. The attacker obtains the user's session token through some means, and then uses the session token to perform malicious operations. For Java applications, it is very important to protect the security of user sessions. Here are some methods that can be used to protect Java applications from session hijacking attacks:
- Use HTTPS: Using the HTTPS protocol can encrypt user data transmitted over the network, preventing attackers from transmitting it Stealing user session tokens during the process. By configuring the application's web server to upgrade the HTTP protocol to the HTTPS protocol, a more secure communication channel can be provided.
- Update session token regularly: When a user logs in, a unique session token should be generated and stored on the server side. The validity of this token should be verified every time the user interacts with the server. To enhance security, session tokens should be updated regularly and old tokens disabled.
- Perform signature verification on session tokens: In order to prevent attackers from forging session tokens for attacks, you can perform signature verification on session tokens. Signature verification ensures the integrity and authenticity of the token.
- Use two-factor authentication: Two-factor authentication is a method that uses two or more pieces of information to verify a user's identity during the login process. In addition to traditional usernames and passwords, other factors such as mobile phone verification codes, physical tokens, or biometrics can be used for verification. By using two-factor authentication, even if an attacker obtains a session token, it will be difficult to verify identity through other factors.
- Limit session validity time and activity time: In order to reduce the risk of session hijacking, the session validity time and activity time should be limited. If the user takes no action for a period of time, the session should automatically expire and require a new login.
- Prevent cross-site scripting attacks: Cross-site scripting attacks are another common network attack method. The attacker injects malicious scripts into the application. When the user accesses the page, the malicious script will execute and obtain The user's session token. In order to prevent cross-site scripting attacks, the input data should be strictly verified and filtered to ensure that the data entered by the user will not be interpreted as a script.
- Regular auditing and monitoring: Regular auditing and monitoring of the security of Java applications is very important. By using technical means such as security logging and exception monitoring, potential threats can be discovered and responded to in a timely manner.
To summarize, protecting Java applications from session hijacking attacks is a complex task that requires the comprehensive use of various technologies and methods to improve security. The methods introduced in this article are only part of it, and there are many other techniques and measures that can be adopted. Therefore, when developing Java applications, you should always pay attention to security, and learn and apply new security technologies in a timely manner to protect user privacy and data security.
The above is the detailed content of Protect Java applications from hijacking attacks. For more information, please follow other related articles on the PHP Chinese website!
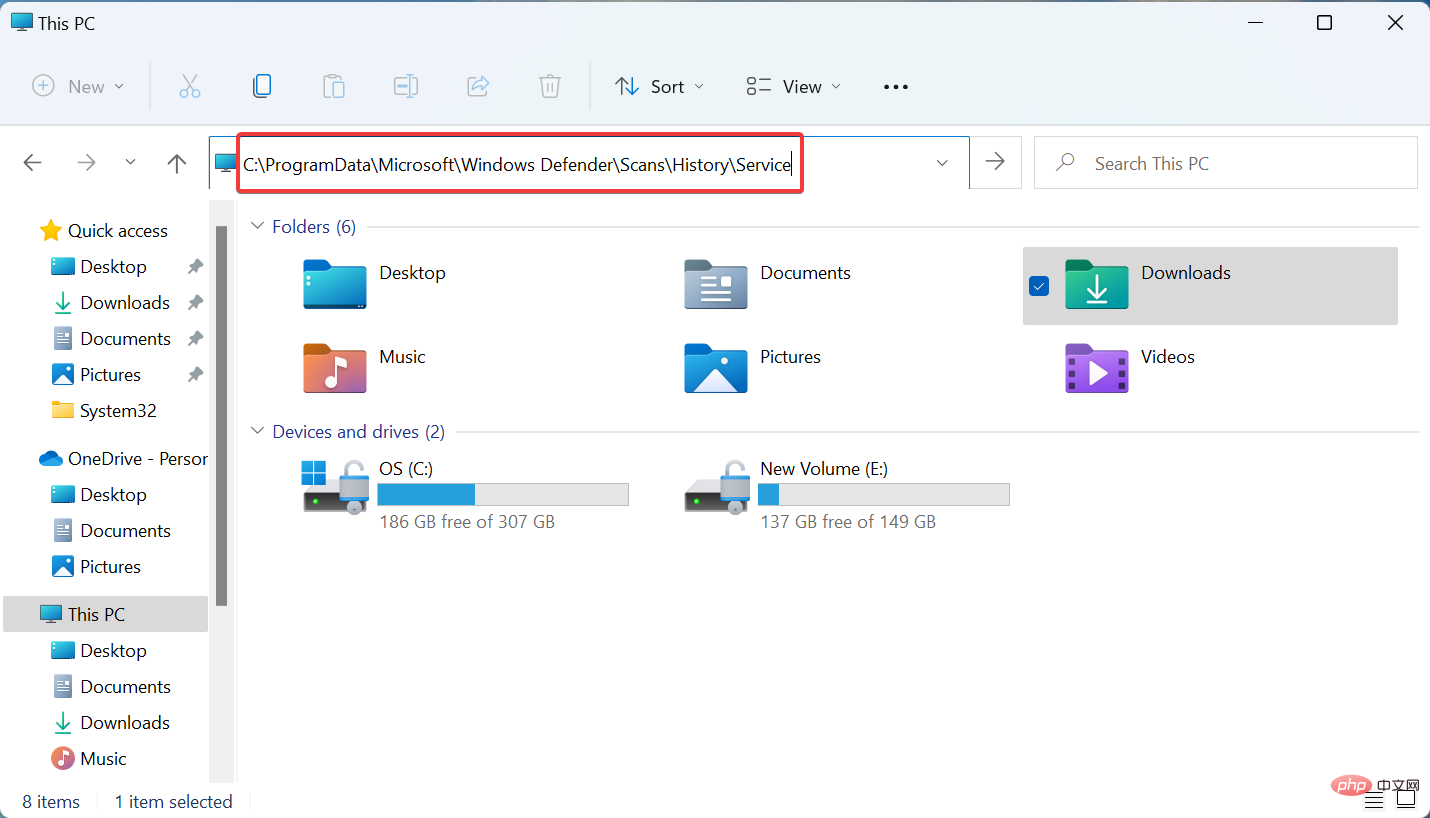 如何在 Windows 11 中清除保护历史记录:2种方法Apr 23, 2023 am 08:04 AM
如何在 Windows 11 中清除保护历史记录:2种方法Apr 23, 2023 am 08:04 AM当您的PC存储空间不足时,您可以立即查看许多文件夹以释放空间。其中一个消耗很大一部分的是WindowsDefender保护历史记录,但你可以在Windows11中清除它吗?尽管并非完全必要,但删除保护历史记录实际上有助于清除系统上的一些存储空间。对于某些用户来说,这些文件占用了20-25GB的空间,如果您的计算机存储空间不足,这可能会令人生畏。那么,让我们找出什么是保护历史记录,在Windows11中清除它的所有方式,以及如何将其配置为在设置的时间后自动清除。什么是保护历史?M
 Python在软件源码保护中的应用实践Jun 29, 2023 am 11:20 AM
Python在软件源码保护中的应用实践Jun 29, 2023 am 11:20 AMPython语言作为一种高级编程语言,具有简单易学、易读易写等特点,在软件开发领域中得到了广泛的应用。然而,由于Python的开源特性,源代码很容易被他人轻易获取,这就给软件源码保护带来了一些挑战。因此,在实际应用中,我们常常需要采取一些方法来保护Python源代码,确保其安全性。在软件源码保护中,有多种针对Python的应用实践可供选择。下面将介绍几种常见
 Java职责与工作范围简介Jan 30, 2024 am 08:31 AM
Java职责与工作范围简介Jan 30, 2024 am 08:31 AMJava是一种常用的编程语言,广泛应用于软件开发和互联网应用领域。作为一名Java开发者,了解Java的职责和工作范围对于提高自己的技能和实施工作任务非常重要。首先,Java开发者的主要职责是设计和编写高质量的Java代码。他们要根据项目需求和规格书设计、开发和测试Java应用程序。这包括编写清晰、可读性强的代码,使用Java语法和规范。Java开发者还需要
 Java技能掌握后,有哪些职业选择?Jan 30, 2024 am 09:01 AM
Java技能掌握后,有哪些职业选择?Jan 30, 2024 am 09:01 AM随着信息技术的迅速发展,Java作为一门广泛应用的编程语言,已经成为了许多企业和开发者的首选。掌握Java技能不仅可以为个人增添竞争力,而且还能够打开许多职业的门道。那么,掌握Java技能后,究竟可以选择哪些职业路径呢?Java开发工程师:毫无疑问,Java开发工程师是目前最受市场欢迎的职业之一。Java开发工程师负责开发和维护Java应用程序,并且在企业的
 如何使用PHP和Vue.js开发防御会话劫持的最佳实践Jul 06, 2023 pm 03:06 PM
如何使用PHP和Vue.js开发防御会话劫持的最佳实践Jul 06, 2023 pm 03:06 PM如何使用PHP和Vue.js开发防御会话劫持的最佳实践会话劫持是一种攻击方式,攻击者通过获取用户的会话ID或令牌,并在未经授权的情况下访问用户的会话信息。这种攻击可能导致用户隐私泄露,身份伪造等严重后果。为了防止会话劫持,我们可以使用PHP和Vue.js开发一些最佳实践。强化后端安全首先,我们需要在后端对会话进行加固和保护。以下是一些常见的防御措施:使用安全
 如何使用Vue保护数据安全性Jun 11, 2023 am 10:11 AM
如何使用Vue保护数据安全性Jun 11, 2023 am 10:11 AM随着互联网的普及和应用程序的开发,数据安全性变得越来越重要。Vue作为一种流行的JavaScript框架,可以帮助开发人员保护数据的安全性。在本文中,将介绍一些使用Vue保护数据安全性的技术和建议。1.使用VuexVuex是一种Vue.js的状态管理模式。使用Vuex,您可以通过将状态(数据)存储在中央存储库中来实现应用程序的数据安全性。因此,您可以通过各种
 如何进行代码授权和加密保护?Jun 12, 2023 am 09:33 AM
如何进行代码授权和加密保护?Jun 12, 2023 am 09:33 AM在当前信息化时代,网络上存在着大量的软件、程序和代码文件,其中有不少代码是需要被保护的,以避免被盗版或恶意利用,同时也有些代码需要进行授权以获得经济收益。那么,问题就来了:如何进行代码授权和加密保护呢?一、代码授权代码授权是指在一定的条件下,授予使用或修改、发布软件或程序源代码的权利。此时,程序开发者作为版权人,需要明确在何种情况下允许其他人使用代码、以何
 Windows安全中心实时保护关闭技巧分享Mar 27, 2024 pm 10:09 PM
Windows安全中心实时保护关闭技巧分享Mar 27, 2024 pm 10:09 PM在今天的数字化社会中,计算机已经成为我们生活中不可或缺的一部分。而作为最为普及的操作系统之一,Windows系统在全球范围内被广泛使用。然而,随着网络攻击手段的不断升级,保护个人计算机安全变得尤为重要。Windows操作系统提供了一系列的安全功能,其中“Windows安全中心”是其重要组成部分之一。在Windows系统中,“Windows安全中心”可帮助我们


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

Notepad++7.3.1
Easy-to-use and free code editor

Atom editor mac version download
The most popular open source editor






