With the rapid development of Web applications, network security problems are becoming increasingly serious. Attackers can easily exploit vulnerabilities in web applications to compromise and steal personal information, corporate secrets, and more. To protect web applications, developers and administrators alike must take steps to combat a variety of attacks. Nginx's HTTP filter is a very effective tool that can play an important role in Web security.
HTTP filter is a core module of Nginx, used to filter and inspect HTTP requests. It can detect and block malicious requests, SQL injection, cross-site scripting (XSS) and other attacks, effectively protecting the security of web applications. The following will introduce the application method of Nginx HTTP filter in web security.
First, HTTP filters can detect and prevent malicious requests. Attackers will send a large number of malicious requests in an attempt to exploit vulnerabilities in web applications. For example, an attacker may inject SQL statements into the URL in an attempt to spoof the database. HTTP filters can identify these requests, intercept them and prevent the attacker from further actions.
Secondly, HTTP filters can detect and block XSS attacks. XSS attacks refer to attackers injecting JavaScript code into web applications to obtain users' sensitive information or perform other malicious operations. HTTP filters can detect these attacks and intercept them on the server side, protecting users' personal information.
Again, HTTP filters can detect and block CSRF attacks. A CSRF attack occurs when an attacker tricks a user into performing a specific action without authorization, such as clicking a link or submitting a form. HTTP filters can detect these attacks and prevent more malicious operations from happening.
Finally, HTTP filters are also very effective in dealing with DDoS attacks. A DDoS attack occurs when an attacker sends a large number of requests to a server to bring it down. HTTP filters can identify and intercept these requests, effectively mitigating the impact of DDoS attacks on web applications.
To sum up, Nginx’s HTTP filter plays an important role in web security. HTTP filters can effectively protect the security of web applications by detecting and blocking malicious requests, XSS attacks, CSRF attacks, and DDoS attacks. At the same time, developers and administrators can also use some tools and technologies to further enhance the security of web applications, such as SSL certificates, firewalls, network IDS/IPS, etc.
Although HTTP filters can handle most web security issues, attackers' techniques are constantly evolving, and new attack methods are constantly emerging. Therefore, in order to maintain the security of web applications, we still need to continuously improve our security awareness, learn new security technologies and update our protective measures in a timely manner.
The above is the detailed content of Application of Nginx HTTP filter in web security. For more information, please follow other related articles on the PHP Chinese website!
 内存飙升!记一次nginx拦截爬虫Mar 30, 2023 pm 04:35 PM
内存飙升!记一次nginx拦截爬虫Mar 30, 2023 pm 04:35 PM本篇文章给大家带来了关于nginx的相关知识,其中主要介绍了nginx拦截爬虫相关的,感兴趣的朋友下面一起来看一下吧,希望对大家有帮助。
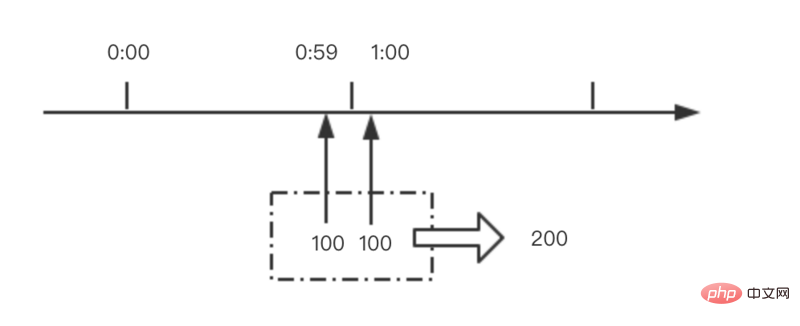 nginx限流模块源码分析May 11, 2023 pm 06:16 PM
nginx限流模块源码分析May 11, 2023 pm 06:16 PM高并发系统有三把利器:缓存、降级和限流;限流的目的是通过对并发访问/请求进行限速来保护系统,一旦达到限制速率则可以拒绝服务(定向到错误页)、排队等待(秒杀)、降级(返回兜底数据或默认数据);高并发系统常见的限流有:限制总并发数(数据库连接池)、限制瞬时并发数(如nginx的limit_conn模块,用来限制瞬时并发连接数)、限制时间窗口内的平均速率(nginx的limit_req模块,用来限制每秒的平均速率);另外还可以根据网络连接数、网络流量、cpu或内存负载等来限流。1.限流算法最简单粗暴的
 nginx php403错误怎么解决Nov 23, 2022 am 09:59 AM
nginx php403错误怎么解决Nov 23, 2022 am 09:59 AMnginx php403错误的解决办法:1、修改文件权限或开启selinux;2、修改php-fpm.conf,加入需要的文件扩展名;3、修改php.ini内容为“cgi.fix_pathinfo = 0”;4、重启php-fpm即可。
 nginx+rsync+inotify怎么配置实现负载均衡May 11, 2023 pm 03:37 PM
nginx+rsync+inotify怎么配置实现负载均衡May 11, 2023 pm 03:37 PM实验环境前端nginx:ip192.168.6.242,对后端的wordpress网站做反向代理实现复杂均衡后端nginx:ip192.168.6.36,192.168.6.205都部署wordpress,并使用相同的数据库1、在后端的两个wordpress上配置rsync+inotify,两服务器都开启rsync服务,并且通过inotify分别向对方同步数据下面配置192.168.6.205这台服务器vim/etc/rsyncd.confuid=nginxgid=nginxport=873ho
 如何解决跨域?常见解决方案浅析Apr 25, 2023 pm 07:57 PM
如何解决跨域?常见解决方案浅析Apr 25, 2023 pm 07:57 PM跨域是开发中经常会遇到的一个场景,也是面试中经常会讨论的一个问题。掌握常见的跨域解决方案及其背后的原理,不仅可以提高我们的开发效率,还能在面试中表现的更加
 nginx部署react刷新404怎么办Jan 03, 2023 pm 01:41 PM
nginx部署react刷新404怎么办Jan 03, 2023 pm 01:41 PMnginx部署react刷新404的解决办法:1、修改Nginx配置为“server {listen 80;server_name https://www.xxx.com;location / {root xxx;index index.html index.htm;...}”;2、刷新路由,按当前路径去nginx加载页面即可。
 nginx怎么禁止访问phpNov 22, 2022 am 09:52 AM
nginx怎么禁止访问phpNov 22, 2022 am 09:52 AMnginx禁止访问php的方法:1、配置nginx,禁止解析指定目录下的指定程序;2、将“location ~^/images/.*\.(php|php5|sh|pl|py)${deny all...}”语句放置在server标签内即可。
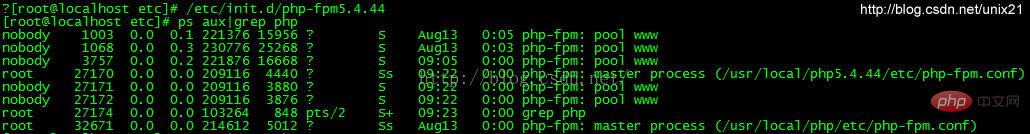 Linux系统下如何为Nginx安装多版本PHPMay 11, 2023 pm 07:34 PM
Linux系统下如何为Nginx安装多版本PHPMay 11, 2023 pm 07:34 PMlinux版本:64位centos6.4nginx版本:nginx1.8.0php版本:php5.5.28&php5.4.44注意假如php5.5是主版本已经安装在/usr/local/php目录下,那么再安装其他版本的php再指定不同安装目录即可。安装php#wgethttp://cn2.php.net/get/php-5.4.44.tar.gz/from/this/mirror#tarzxvfphp-5.4.44.tar.gz#cdphp-5.4.44#./configure--pr


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

SublimeText3 Chinese version
Chinese version, very easy to use






