 Technology peripherals
Technology peripherals AI
AI Is AI fraud a 100% success rate? Du Xiaoman's anti-deep fake model 'defeats magic with magic”
Is AI fraud a 100% success rate? Du Xiaoman's anti-deep fake model 'defeats magic with magic”2023-05-26 10:22:19 Author: Song Junyi
A few days ago, a topic #AIFraud Success Rate is Close to 100%# became a hot search topic on Weibo. The legal representative of a technology company in Fujian was defrauded of 4.3 million yuan by a face-changing AI video. The incident took only 10 minutes.
An AI-related scam also occurred abroad. An email with a video of Google CEO attached caused many YouTube bloggers to download files containing dangerous viruses.
Both of these fraud incidents involved deepfake technology. This is a face-changing method that has been around for 6 years. Nowadays, the explosion of AIGC technology has made it easier and easier to create hard-to-identify deepfake videos. For the financial industry where facial recognition is widely used, preventing deep fake attacks is also particularly important.
In the financial industry, the fraud caused by deepfake is mainly identity fraud, that is, using deep fake images and videos to impersonate the identity of others, deceiving the identity verification system in the financial credit process, and then committing fraud and malicious registration. . At present, the financial industry has relatively mature technical methods and solutions for dealing with deepfake, and Du Xiaoman has accumulated rich experience in dealing with deepfake.
Du Xiaoman introduced that in recent years, the trend of using deep fake technology to bypass the face recognition process has increased, posing a certain threat to the real-name authentication system of financial institutions. The best way to identify and confirm whether content is fake is to develop AI “anti-deepfake” detection algorithms. Starting from three dimensions, Du Xiaoman's anti-counterfeiting deep detection model algorithm strategy successfully cracked the forged video.
The first is to generate defects. Specifically, due to the lack of relevant training data, the deepfake model may not be able to correctly render some human facial features, ranging from abnormal blinking frequency to inconsistency between mouth shape and voice, etc. By designing specific analysis algorithms, the detection model can extract these "basically visible" features for further analysis and judgment.

The second is the inherent attribute. Since different cameras have different device fingerprints, models like GAN will also leave unique fingerprints for identifying the generator when generating faces, so clues can be found through comparison.

The third detail is high-level semantics. It refers to issues such as detecting the coordination of facial action units (muscle groups), the orientation consistency of various facial areas, and the microscopic continuity of videos. Because these details are difficult to model and copy, it is easy to get caught.

Of course, since a single feature is difficult to adapt to complex deepfake content, the overall framework of the detection model uses multi-feature fusion to ensure the robustness of decision-making.
In addition to the advantages of data samples, Du Xiaoman also incorporates his own originality, including neural network search and optimization algorithms, micro-expression analysis and graph convolution (GCN) technology, and self-supervised pre-training methods based on reconstruction, allowing The model realizes the transformation from "counterfeiting" to "authenticity".
It is precisely for this reason that Xiaoman’s anti-deep fake detection model successfully passed the special face recognition security evaluation of the Academy of Information and Communications Technology in September last year, and obtained the excellent certification for live detection security protection capabilities. In terms of specific effects, it can cover various forms of deep fakes, including static portrait picture activation, AI face changing, false face synthesis, etc., achieving a recall of more than 90% with a false alarm rate of one thousandth, which is an accuracy of 99% .
As new deepfake tools continue to emerge, the financial industry will need to face more deepfake attacks. Du Xiaoman believes that more counterfeiting detection technologies in the future should focus on mining semantic features, cross-modal features, etc., so that the model can use high-level semantics with strong interpretability to detect counterfeiting. As an innovative financial technology company, Du Xiaoman will also provide more technological support for the steady development of the financial industry.
The above is the detailed content of Is AI fraud a 100% success rate? Du Xiaoman's anti-deep fake model 'defeats magic with magic”. For more information, please follow other related articles on the PHP Chinese website!
 I Tried Vibe Coding with Cursor AI and It's Amazing!Mar 20, 2025 pm 03:34 PM
I Tried Vibe Coding with Cursor AI and It's Amazing!Mar 20, 2025 pm 03:34 PMVibe coding is reshaping the world of software development by letting us create applications using natural language instead of endless lines of code. Inspired by visionaries like Andrej Karpathy, this innovative approach lets dev
 Replit Agent: A Guide With Practical ExamplesMar 04, 2025 am 10:52 AM
Replit Agent: A Guide With Practical ExamplesMar 04, 2025 am 10:52 AMRevolutionizing App Development: A Deep Dive into Replit Agent Tired of wrestling with complex development environments and obscure configuration files? Replit Agent aims to simplify the process of transforming ideas into functional apps. This AI-p
 Top 5 GenAI Launches of February 2025: GPT-4.5, Grok-3 & More!Mar 22, 2025 am 10:58 AM
Top 5 GenAI Launches of February 2025: GPT-4.5, Grok-3 & More!Mar 22, 2025 am 10:58 AMFebruary 2025 has been yet another game-changing month for generative AI, bringing us some of the most anticipated model upgrades and groundbreaking new features. From xAI’s Grok 3 and Anthropic’s Claude 3.7 Sonnet, to OpenAI’s G
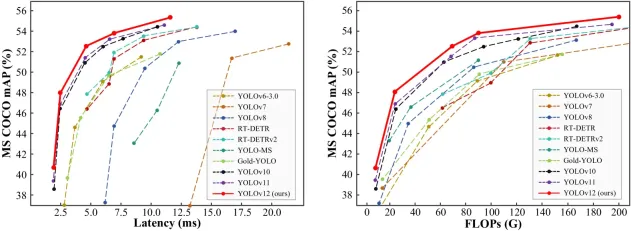 How to Use YOLO v12 for Object Detection?Mar 22, 2025 am 11:07 AM
How to Use YOLO v12 for Object Detection?Mar 22, 2025 am 11:07 AMYOLO (You Only Look Once) has been a leading real-time object detection framework, with each iteration improving upon the previous versions. The latest version YOLO v12 introduces advancements that significantly enhance accuracy
 How to Use DALL-E 3: Tips, Examples, and FeaturesMar 09, 2025 pm 01:00 PM
How to Use DALL-E 3: Tips, Examples, and FeaturesMar 09, 2025 pm 01:00 PMDALL-E 3: A Generative AI Image Creation Tool Generative AI is revolutionizing content creation, and DALL-E 3, OpenAI's latest image generation model, is at the forefront. Released in October 2023, it builds upon its predecessors, DALL-E and DALL-E 2
 Elon Musk & Sam Altman Clash over $500 Billion Stargate ProjectMar 08, 2025 am 11:15 AM
Elon Musk & Sam Altman Clash over $500 Billion Stargate ProjectMar 08, 2025 am 11:15 AMThe $500 billion Stargate AI project, backed by tech giants like OpenAI, SoftBank, Oracle, and Nvidia, and supported by the U.S. government, aims to solidify American AI leadership. This ambitious undertaking promises a future shaped by AI advanceme
 5 Grok 3 Prompts that Can Make Your Work EasyMar 04, 2025 am 10:54 AM
5 Grok 3 Prompts that Can Make Your Work EasyMar 04, 2025 am 10:54 AMGrok 3 – Elon Musk and xAi’s latest AI model is the talk of the town these days. From Andrej Karpathy to tech influencers, everyone is talking about the capabilities of this new model. Initially, access was limited to
 Google's GenCast: Weather Forecasting With GenCast Mini DemoMar 16, 2025 pm 01:46 PM
Google's GenCast: Weather Forecasting With GenCast Mini DemoMar 16, 2025 pm 01:46 PMGoogle DeepMind's GenCast: A Revolutionary AI for Weather Forecasting Weather forecasting has undergone a dramatic transformation, moving from rudimentary observations to sophisticated AI-powered predictions. Google DeepMind's GenCast, a groundbreak


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.

Atom editor mac version download
The most popular open source editor

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.





