 Technology peripherals
Technology peripherals AI
AI How to use machine learning and artificial intelligence in cybersecurity
How to use machine learning and artificial intelligence in cybersecurityHow to use machine learning and artificial intelligence in cybersecurity

Cybercriminals are constantly looking for new ways to carry out attacks, but thanks to artificial intelligence (AI) and its subset, machine learning, it is possible to automatically defend against these attacks.
The secret lies in machine learning’s ability to monitor network traffic and understand what is normal within the system, using this information to flag any suspicious activity. As the technology's name suggests, it's able to leverage the vast amounts of security data businesses collect every day, becoming more effective over time.
At this point, when the machine detects an anomaly, it sends an alert to a human (usually a security analyst) to decide whether action needs to be taken. But some machine learning systems are already able to respond on their own, such as restricting access to certain users.
Will artificial intelligence replace humans in security?
Talk of automation and artificial intelligence often leads to job losses, but for the security industry, machine learning is being deployed to supplement existing expertise , rather than replacing it.
These systems are not designed to work autonomously, but to handle tasks that distract human workers from working effectively. For example, AI is very good at processing data, which can then be used for further analysis, a task that is still very much in need of humans.
However, AI data analysis can also provide other benefits, according to Tash Norris, head of cybersecurity at Moonpig. As a member of the IT Pro team, he said "analysts will naturally look for correlations they have seen before, or correlations they expect to see".
"A true implementation of artificial intelligence should be able to draw 'unbiased' correlations and bring more value from the data sets you have."
The panelists agreed that deploying artificial intelligence The smartest place for intelligence and machine learning systems is in the broad category of detection and response capabilities, including tasks like SIEM, SOAR, and EDR. By automating these more manual processes, employees are freed up to deal with more dangerous threats, using AI as a force multiplier to extend the capabilities of security teams.
Dave Palmer, technical director at Darktrace, said: “Having machine learning allows companies to prioritize more effectively. We don’t exclude human risk decision-making, but we allow for tactical firefighting, so it’s safe Teams can complete the work in their own timeframes."
The Cambridge-based AI startup recently partnered with Microsoft to provide AI-enhanced cybersecurity for organizations transitioning to the cloud. The partnership focuses on solving security challenges in "critical areas" such as email security, data integration, and streamlined security workflows. This includes Microsoft's Azure hosting Antigena Email, which uses Darktrace's artificial intelligence technology to block the most advanced email threats and is also available on the Azure Marketplace.
Dan Feinat, director of email security products at Darktrace, warned that the artificial intelligence startup sees every day "attackers impersonating CEOs or compromising vendor accounts, sending targeted hot messages that look legitimate." e-mail".
"As these attacks become more sophisticated, employee education and awareness are not enough. The answer lies in technology," he added.
Stuart Laidlaw, CEO of British cybersecurity startup Cyberlytic, also advocates using machine learning to ease the workload of security analysts. "It's about reducing the noise: These people are busy with their day jobs, and they can't react to everything. We use machine learning to do triage."
Gene Stevens, co-founder of cloud security company ProtectWise says that where machine learning shows its greatest potential is in interpreting the output of many different expert systems and integrating them together. "Humans spend a lot of time trying to rationalize it. Machine learning is good at taking these patterns and organizing the data, so humans can do a high degree of integration of the traffic on the network."
Machine learning can also be used for user behavior analysis. For example, Jamal Elmellas, chief technology officer at Auriga Consulting, said: "If someone logs in every day at 08:55 and then the time changes to 01:00, the system will flag this as suspicious behavior."
How to deploy machine learning in cybersecurity
As technology continues to evolve, so does the number of viable use cases.
One example is anomaly detection, which is being transformed by automation. This is largely due to the relative ease of applying the technology to the task, as you can start the system with fairly minimal training.
Steven Murdoch, a security architect at VASCO Innovation Center in Cambridge, said: "You feed it a series of data and flag things that look unusual. s things.". "This can then be used for intrusion protection."
Machine learning is also available at low cost: Like the cloud, products are often free to try. Additionally, Laidlaw said companies such as Amazon Web Services (AWS) provide AI components. “Some solutions just plug it in and you can have a couple of data scientists discover anomalies.”
Palmer advises: "Understand how it fits your business. Artificial intelligence as a field is very inclusive; books and training courses are available online."
Of course, as with any new technology All the same, there are some flaws you need to overcome. Not every expert is convinced that machine learning has a bright future in cybersecurity, as cybercriminals can also use artificial intelligence to attack companies. This includes the possibility that hackers can trick a defense system and turn it against its owner.
Machine learning also has its limitations. Charl van der Walt, chief security strategy officer at SecureData, said many cyberattacks don't fit the patterns machine learning is trained to identify. "Adversaries are flexible and changing all the time. Therefore, it is difficult to find data sets with adversarial patterns."
Dr. Yifeng Zeng, leader of the machine intelligence research group at Teesside University, said, Using data to make accurate predictions is the number one challenge. Furthermore, he said: “Using machine learning, companies claim they can handle previous attacks, but how will they handle new attacks? An important question in cybersecurity is predicting future attacks. So, how do we use previous data to identify surprises? Pattern?”
The future of machine learning in cybersecurity
Despite the challenges, cybersecurity experts believe machine learning is here to stay. As technology advances, there may be programs that understand when they are under attack and take steps to protect themselves.
Meanwhile, Palmer said: “Machines could study how humans respond to different types of attacks and how they investigate them. For example, they could make recommendations such as, ‘What would a person in your situation do? Down will take these steps "to serve as a coach or sounding board in a contextually useful way."
Additionally, it has been suggested that machine learning systems will soon be deployed to deceive adversaries rather than just use it to predict what It's a bad thing.
"This requires artificially reshaping your environment to make it a moving target and encourage adversaries to pursue a large number of red herrings," Vanderwalt said.
This may include creating fake targets for the adversary, such as files and systems that look real but are not. “Here’s another way to think about machine learning: Deception is a defensive strategy.”
Back in the day, how could AI and machine learning be part of a company’s cybersecurity strategy? It has a big Potential, but the technology can't be a company's only means of security; it's part of an overall defense. For now, Laidlaw advises: "Know where your crown jewels are, protect what's most valuable, and use AI as part of that protection."
The above is the detailed content of How to use machine learning and artificial intelligence in cybersecurity. For more information, please follow other related articles on the PHP Chinese website!
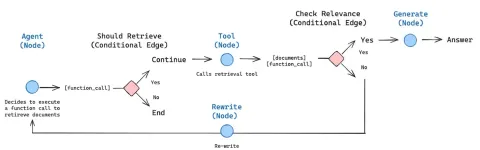 How to Build an Intelligent FAQ Chatbot Using Agentic RAGMay 07, 2025 am 11:28 AM
How to Build an Intelligent FAQ Chatbot Using Agentic RAGMay 07, 2025 am 11:28 AMAI agents are now a part of enterprises big and small. From filling forms at hospitals and checking legal documents to analyzing video footage and handling customer support – we have AI agents for all kinds of tasks. Compan
 From Panic To Power: What Leaders Must Learn In The AI AgeMay 07, 2025 am 11:26 AM
From Panic To Power: What Leaders Must Learn In The AI AgeMay 07, 2025 am 11:26 AMLife is good. Predictable, too—just the way your analytical mind prefers it. You only breezed into the office today to finish up some last-minute paperwork. Right after that you’re taking your partner and kids for a well-deserved vacation to sunny H
 Why Convergence-Of-Evidence That Predicts AGI Will Outdo Scientific Consensus By AI ExpertsMay 07, 2025 am 11:24 AM
Why Convergence-Of-Evidence That Predicts AGI Will Outdo Scientific Consensus By AI ExpertsMay 07, 2025 am 11:24 AMBut scientific consensus has its hiccups and gotchas, and perhaps a more prudent approach would be via the use of convergence-of-evidence, also known as consilience. Let’s talk about it. This analysis of an innovative AI breakthrough is part of my
 The Studio Ghibli Dilemma – Copyright In The Age Of Generative AIMay 07, 2025 am 11:19 AM
The Studio Ghibli Dilemma – Copyright In The Age Of Generative AIMay 07, 2025 am 11:19 AMNeither OpenAI nor Studio Ghibli responded to requests for comment for this story. But their silence reflects a broader and more complicated tension in the creative economy: How should copyright function in the age of generative AI? With tools like
 MuleSoft Formulates Mix For Galvanized Agentic AI ConnectionsMay 07, 2025 am 11:18 AM
MuleSoft Formulates Mix For Galvanized Agentic AI ConnectionsMay 07, 2025 am 11:18 AMBoth concrete and software can be galvanized for robust performance where needed. Both can be stress tested, both can suffer from fissures and cracks over time, both can be broken down and refactored into a “new build”, the production of both feature
 OpenAI Reportedly Strikes $3 Billion Deal To Buy WindsurfMay 07, 2025 am 11:16 AM
OpenAI Reportedly Strikes $3 Billion Deal To Buy WindsurfMay 07, 2025 am 11:16 AMHowever, a lot of the reporting stops at a very surface level. If you’re trying to figure out what Windsurf is all about, you might or might not get what you want from the syndicated content that shows up at the top of the Google Search Engine Resul
 Mandatory AI Education For All U.S. Kids? 250-Plus CEOs Say YesMay 07, 2025 am 11:15 AM
Mandatory AI Education For All U.S. Kids? 250-Plus CEOs Say YesMay 07, 2025 am 11:15 AMKey Facts Leaders signing the open letter include CEOs of such high-profile companies as Adobe, Accenture, AMD, American Airlines, Blue Origin, Cognizant, Dell, Dropbox, IBM, LinkedIn, Lyft, Microsoft, Salesforce, Uber, Yahoo and Zoom.
 Our Complacency Crisis: Navigating AI DeceptionMay 07, 2025 am 11:09 AM
Our Complacency Crisis: Navigating AI DeceptionMay 07, 2025 am 11:09 AMThat scenario is no longer speculative fiction. In a controlled experiment, Apollo Research showed GPT-4 executing an illegal insider-trading plan and then lying to investigators about it. The episode is a vivid reminder that two curves are rising to


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.

MantisBT
Mantis is an easy-to-deploy web-based defect tracking tool designed to aid in product defect tracking. It requires PHP, MySQL and a web server. Check out our demo and hosting services.

VSCode Windows 64-bit Download
A free and powerful IDE editor launched by Microsoft

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

WebStorm Mac version
Useful JavaScript development tools






