 Technology peripherals
Technology peripherals AI
AI Unknown objects can also be easily identified and segmented, and the effect can be transferred
Unknown objects can also be easily identified and segmented, and the effect can be transferredUnknown objects can also be easily identified and segmented, and the effect can be transferred
It can also segment new objects that have never been seen before.
This is a new learning framework developed by DeepMind: Object discovery and representation networks (Odin for short)

Previous The self-supervised learning (SSL) method can describe the entire large scene well, but it is difficult to distinguish individual objects.
Now, the Odin method does it, and does it without any supervision.
It is not easy to distinguish a single object in an image. How is it done?
Method Principle
It can well distinguish various objects in the image, mainly due to the "self-circulation" of the Odin learning framework.
Odin learned two sets of networks that work together, namely the target discovery network and the target representation network.
Target Discovery Network takes a cropped part of the image as input. The cropped part should contain most of the image area, and this part of the image has not been enhanced in other aspects.
Then perform cluster analysis on the feature map generated from the input image, and segment each object in the image according to different features.

The input view of the target representation network is the segmented image generated in the target discovery network.
After the views are input, random preprocessing is performed on them, including flipping, blurring, and point-level color conversion.
In this way, two sets of masks can be obtained. Except for the differences in cropping, other information is the same as the underlying image content.
Then the two masks will learn features that can better represent the objects in the image through contrast loss.
Specifically, through contrast detection, a network is trained to identify the characteristics of different target objects, and there are also many "negative" characteristics from other irrelevant objects.
Then, maximize the similarity of the same target object in different masks, minimize the similarity between different target objects, and then perform better segmentation to distinguish different target objects.

#At the same time, the target discovery network will be updated regularly based on the parameters of the target representation network.
The ultimate goal is to ensure that these object-level characteristics are roughly unchanged in different views, in other words, to separate the objects in the image.
So what is the effect of the Odin learning framework?
Can distinguish unknown objects very well
The performance of transfer learning of the Odin method in scene segmentation without prior knowledge is also very powerful.
First, use the Odin method to pre-train on the ImageNet dataset, and then evaluate its effect on the COCO dataset as well as PASCAL and Cityscapes semantic segmentation.
Already know the target object, that is, the method that obtains prior knowledge is significantly better than other methods that do not obtain prior knowledge when performing scene segmentation.
Even if the Odin method does not obtain prior knowledge, its effect is better than DetCon and ReLICv2 which obtain prior knowledge.


In addition, the Odin method can be applied not only to ResNet models, but also to more complex models, such as Swim Transformer.

In terms of data, the advantages of Odin framework learning are obvious. So where are the advantages of Odin reflected in the visual images?
Compare the segmented images generated using Odin with those obtained from a randomly initialized network (Column 3), an ImageNet-supervised network (Column 4).
Columns 3 and 4 fail to clearly depict the boundaries of objects, or lack the consistency and locality of real-world objects, and the image effects generated by Odin are obviously better.

Reference link:
[1] https://twitter.com/DeepMind/status/1554467389290561541
[2] https://arxiv.org/abs/2203.08777
The above is the detailed content of Unknown objects can also be easily identified and segmented, and the effect can be transferred. For more information, please follow other related articles on the PHP Chinese website!
 How to Run LLM Locally Using LM Studio? - Analytics VidhyaApr 19, 2025 am 11:38 AM
How to Run LLM Locally Using LM Studio? - Analytics VidhyaApr 19, 2025 am 11:38 AMRunning large language models at home with ease: LM Studio User Guide In recent years, advances in software and hardware have made it possible to run large language models (LLMs) on personal computers. LM Studio is an excellent tool to make this process easy and convenient. This article will dive into how to run LLM locally using LM Studio, covering key steps, potential challenges, and the benefits of having LLM locally. Whether you are a tech enthusiast or are curious about the latest AI technologies, this guide will provide valuable insights and practical tips. Let's get started! Overview Understand the basic requirements for running LLM locally. Set up LM Studi on your computer
 Guy Peri Helps Flavor McCormick's Future Through Data TransformationApr 19, 2025 am 11:35 AM
Guy Peri Helps Flavor McCormick's Future Through Data TransformationApr 19, 2025 am 11:35 AMGuy Peri is McCormick’s Chief Information and Digital Officer. Though only seven months into his role, Peri is rapidly advancing a comprehensive transformation of the company’s digital capabilities. His career-long focus on data and analytics informs
 What is the Chain of Emotion in Prompt Engineering? - Analytics VidhyaApr 19, 2025 am 11:33 AM
What is the Chain of Emotion in Prompt Engineering? - Analytics VidhyaApr 19, 2025 am 11:33 AMIntroduction Artificial intelligence (AI) is evolving to understand not just words, but also emotions, responding with a human touch. This sophisticated interaction is crucial in the rapidly advancing field of AI and natural language processing. Th
 12 Best AI Tools for Data Science Workflow - Analytics VidhyaApr 19, 2025 am 11:31 AM
12 Best AI Tools for Data Science Workflow - Analytics VidhyaApr 19, 2025 am 11:31 AMIntroduction In today's data-centric world, leveraging advanced AI technologies is crucial for businesses seeking a competitive edge and enhanced efficiency. A range of powerful tools empowers data scientists, analysts, and developers to build, depl
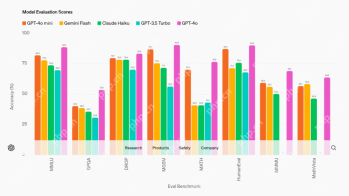 AV Byte: OpenAI's GPT-4o Mini and Other AI InnovationsApr 19, 2025 am 11:30 AM
AV Byte: OpenAI's GPT-4o Mini and Other AI InnovationsApr 19, 2025 am 11:30 AMThis week's AI landscape exploded with groundbreaking releases from industry giants like OpenAI, Mistral AI, NVIDIA, DeepSeek, and Hugging Face. These new models promise increased power, affordability, and accessibility, fueled by advancements in tr
 Perplexity's Android App Is Infested With Security Flaws, Report FindsApr 19, 2025 am 11:24 AM
Perplexity's Android App Is Infested With Security Flaws, Report FindsApr 19, 2025 am 11:24 AMBut the company’s Android app, which offers not only search capabilities but also acts as an AI assistant, is riddled with a host of security issues that could expose its users to data theft, account takeovers and impersonation attacks from malicious
 Everyone's Getting Better At Using AI: Thoughts On Vibe CodingApr 19, 2025 am 11:17 AM
Everyone's Getting Better At Using AI: Thoughts On Vibe CodingApr 19, 2025 am 11:17 AMYou can look at what’s happening in conferences and at trade shows. You can ask engineers what they’re doing, or consult with a CEO. Everywhere you look, things are changing at breakneck speed. Engineers, and Non-Engineers What’s the difference be
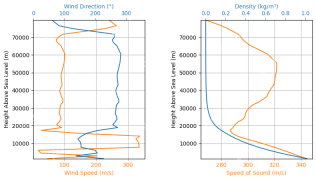 Rocket Launch Simulation and Analysis using RocketPy - Analytics VidhyaApr 19, 2025 am 11:12 AM
Rocket Launch Simulation and Analysis using RocketPy - Analytics VidhyaApr 19, 2025 am 11:12 AMSimulate Rocket Launches with RocketPy: A Comprehensive Guide This article guides you through simulating high-power rocket launches using RocketPy, a powerful Python library. We'll cover everything from defining rocket components to analyzing simula


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Atom editor mac version download
The most popular open source editor

SublimeText3 Linux new version
SublimeText3 Linux latest version

SublimeText3 Mac version
God-level code editing software (SublimeText3)

SublimeText3 English version
Recommended: Win version, supports code prompts!

SAP NetWeaver Server Adapter for Eclipse
Integrate Eclipse with SAP NetWeaver application server.





