 Technology peripherals
Technology peripherals AI
AI How artificial intelligence will help enterprises fight ransomware and prevent cloud security breaches
How artificial intelligence will help enterprises fight ransomware and prevent cloud security breachesHow artificial intelligence will help enterprises fight ransomware and prevent cloud security breaches
Every year, the cybersecurity world faces new challenges and obstacles that businesses need to deal with, and we’re seeing, for example, how 2021 is shaping up to be an incredibly dangerous year. Most notably, ransomware has been a hot topic in the industry following a series of high-profile incidents involving organizations such as Kaseya and the Irish Health Service falling victim.
Additionally, the ransomware attack against JBS Corporation clearly demonstrates the potential severity of supply chain attacks. More broadly, the ongoing shift to hybrid working and rapid adoption of cloud computing also means businesses must re-evaluate their security infrastructure to ensure remote workers are adequately protected.

So, how will the lessons of 2021 shape the cybersecurity landscape in the years to come? Here are five aspects of cybersecurity that will evolve in the near future.
1. Cloud security will face increasing pressure
First, ransomware will turn to stealing and encrypting cloud data. Although this sometimes occurs through attacks on third-party data processors (as we saw Labor Party members' data being held to ransom). Next, we will see that under the "shared responsibility" model, client data will increasingly be directly attacked by ransomware gangs.
2. Take proactive steps to minimize ransomware attacks
In terms of protecting against ransomware, we will increasingly see There will be a public crackdown on ransomware gangs, and formal oversight of information security will increase due to the prevalence of ransomware attacks. However, we will also see that many public sectors are ill-prepared to deal with this threat. Finally, we will see that the consequences of ransomware relative to data loss or breach will be relatively reduced, because human-operated ransomware is detected and stopped before it can successfully explode.
It will become increasingly important for enterprises to have a defense-in-depth security architecture that covers the network and endpoints and can quickly detect and stop these attacks. The focus is on prevention rather than performing time-consuming recovery operations from backups or, worse, having to pay a ransom. Business continuity plans must be constantly adjusted to properly account for the heightened risk ransomware poses to individual businesses, while investing appropriately to prevent and minimize downtime caused by attacks.
3. Enterprises have growing demand for managed detection and response services and automation
In addition to ransomware, although The number of managed security services will continue to grow, but key subsidiaries of organizations will face a shortage of talent in the areas of automation, orchestration, and analyst-augmented artificial intelligence. Businesses will recognize that outsourcing a business environment to an external entity can be difficult and that a few well-equipped and supported internal resources can be more effective than a large number of external resources.
4. More use of artificial intelligence to combat malicious use of multi-factor authentication (MFA)
Another area of concern is around multi-factor authentication Factor Authentication (MFA). Some major tech giants like Microsoft and Google are implementing MFA. This is largely because attackers continue to successfully steal credentials and bypass basic authentication processes. However, while MFA is a step that every company should take - criminals continue to prove that it is not enough to keep them at bay. outside the door. In some cases, criminals are even using bots to help them deal with MFA issues, which will continue to be an uphill battle for businesses. As a result, we will see more enterprises turn to AI-powered security tools to help stop attacks that bypass MFA.
5. Governments and regulators pay more attention to cybersecurity
After multiple attacks on the nation’s critical infrastructure, President Biden The executive order on improving cybersecurity issued in May 2021 aims to significantly improve cybersecurity standards. We expect to see other governments taking an increasingly robust approach to meaningful and effective cybersecurity controls, aiming to be more resilient in the face of serious cyberattacks. Initiatives by UK regulators, such as the Penetration Stress Testing Mechanism (CBEST) in financial services and the TBEST regime in telecoms, which will promote a security threat intelligence-led approach to objectively assess vulnerability to attack, will almost certainly Expand to other key departments.
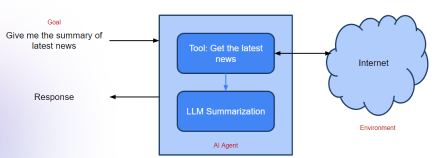
Always Be Prepared Prepare to ensure you have the best protection against potential threats. To achieve this, organizations should look to implement a detection and response strategy. This often involves using a combination of artificial intelligence and machine learning (ML) techniques to look for these intersectional operations that are authorized but exhibit suspicious behavior, as well as certain behaviors that an adversary will exhibit in launching an attack.
If businesses believe they have been compromised and actively look for signs, they will be in a better position to detect attacks and then stop them before they cause damage.
The above is the detailed content of How artificial intelligence will help enterprises fight ransomware and prevent cloud security breaches. For more information, please follow other related articles on the PHP Chinese website!
 What is Graph of Thought in Prompt EngineeringApr 13, 2025 am 11:53 AM
What is Graph of Thought in Prompt EngineeringApr 13, 2025 am 11:53 AMIntroduction In prompt engineering, “Graph of Thought” refers to a novel approach that uses graph theory to structure and guide AI’s reasoning process. Unlike traditional methods, which often involve linear s
 Optimize Your Organisation's Email Marketing with GenAI AgentsApr 13, 2025 am 11:44 AM
Optimize Your Organisation's Email Marketing with GenAI AgentsApr 13, 2025 am 11:44 AMIntroduction Congratulations! You run a successful business. Through your web pages, social media campaigns, webinars, conferences, free resources, and other sources, you collect 5000 email IDs daily. The next obvious step is
 Real-Time App Performance Monitoring with Apache PinotApr 13, 2025 am 11:40 AM
Real-Time App Performance Monitoring with Apache PinotApr 13, 2025 am 11:40 AMIntroduction In today’s fast-paced software development environment, ensuring optimal application performance is crucial. Monitoring real-time metrics such as response times, error rates, and resource utilization can help main
 ChatGPT Hits 1 Billion Users? 'Doubled In Just Weeks' Says OpenAI CEOApr 13, 2025 am 11:23 AM
ChatGPT Hits 1 Billion Users? 'Doubled In Just Weeks' Says OpenAI CEOApr 13, 2025 am 11:23 AM“How many users do you have?” he prodded. “I think the last time we said was 500 million weekly actives, and it is growing very rapidly,” replied Altman. “You told me that it like doubled in just a few weeks,” Anderson continued. “I said that priv
 Pixtral-12B: Mistral AI's First Multimodal Model - Analytics VidhyaApr 13, 2025 am 11:20 AM
Pixtral-12B: Mistral AI's First Multimodal Model - Analytics VidhyaApr 13, 2025 am 11:20 AMIntroduction Mistral has released its very first multimodal model, namely the Pixtral-12B-2409. This model is built upon Mistral’s 12 Billion parameter, Nemo 12B. What sets this model apart? It can now take both images and tex
 Agentic Frameworks for Generative AI Applications - Analytics VidhyaApr 13, 2025 am 11:13 AM
Agentic Frameworks for Generative AI Applications - Analytics VidhyaApr 13, 2025 am 11:13 AMImagine having an AI-powered assistant that not only responds to your queries but also autonomously gathers information, executes tasks, and even handles multiple types of data—text, images, and code. Sounds futuristic? In this a
 Applications of Generative AI in the Financial SectorApr 13, 2025 am 11:12 AM
Applications of Generative AI in the Financial SectorApr 13, 2025 am 11:12 AMIntroduction The finance industry is the cornerstone of any country’s development, as it drives economic growth by facilitating efficient transactions and credit availability. The ease with which transactions occur and credit
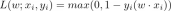 Guide to Online Learning and Passive-Aggressive AlgorithmsApr 13, 2025 am 11:09 AM
Guide to Online Learning and Passive-Aggressive AlgorithmsApr 13, 2025 am 11:09 AMIntroduction Data is being generated at an unprecedented rate from sources such as social media, financial transactions, and e-commerce platforms. Handling this continuous stream of information is a challenge, but it offers an


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

SublimeText3 Linux new version
SublimeText3 Linux latest version

SublimeText3 Chinese version
Chinese version, very easy to use





