How is the hotspot key generated in Redis? How to solve?
- 青灯夜游forward
- 2021-09-22 20:18:195183browse
The following article will take you to understand the hotspot keys in Redis, introduce the reasons for the generation of hotspot keys, ways to discover hotspot keys, and solutions to hotspot keys. I hope it will be helpful to everyone!

Causes of Hot Key
1. The data consumed by users is much greater than the data produced
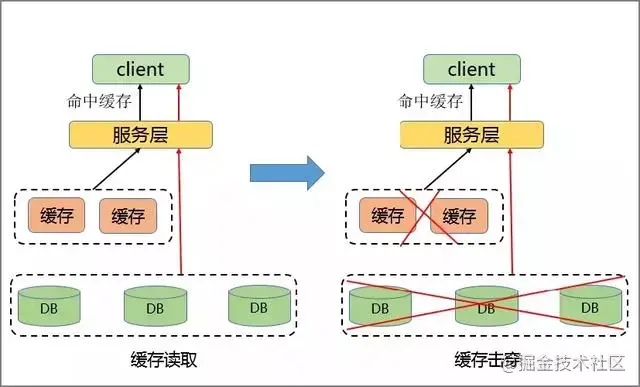
The hot key problem is that there are a large number of requests to access a fixed key on redis at a certain moment, causing cache breakdown, and the requests are all hit to the DB, overwhelming the cache service and DB service, thus affecting the availability of application services. [Related recommendations: Redis video tutorial]
The most common ones are hot searches on Weibo, such as XX celebrity marriage/cheating. Then the Key about XX star will increase instantly, and hot data problems will occur. Weibo also crashes from time to time.
Similarly, hot news, hot comments, celebrity live broadcasts, etc. that are widely published and viewed. These typical scenarios of reading more and writing less will also cause hot issues.
2. Requests for sharding are concentrated and exceed the performance limit of a single server
When reading data on the server side for access, the data is often Perform Sharding During this process, the corresponding Key will be accessed on a certain host server. When the access exceeds the server limit, it will cause hot key problems.
The dangers of hot key issues
##1. The traffic is concentrated and reaches the upper limit of the physical network card.
When the request for a certain hotspot Key exceeds the upper limit of the host's network card on a certain host, other services in the server will be unable to proceed due to excessive concentration of traffic.2. There are too many requests and the cache sharding service is defeated.
If hotspots are too concentrated and the cache of hotspot keys is too large and exceeds the current cache capacity, the cache sharding service will be overwhelmed.3. DB breakdown, causing a business avalanche.
When the cache service crashes and another request is generated at this time, it will be cached on the background DB. Since the performance of the DB itself is weak, request penetration is easy to occur when facing large requests. phenomenon, which will further lead to avalanche phenomena and seriously affect the performance of the equipment.Discovery of hot keys
1. Use business experience to estimate which keys are hot
In fact, this method is quite feasible. For example, if a product is on flash sale, the key of this product can be judged to be a hot key. The disadvantage is obvious. Not all businesses can estimate which keys are hot keys.2. Collect on the client side
#This method is to add a line of code for data statistics before operating redis. There are many ways to collect data, and it can also be to send a notification message to an external communication system. The disadvantage is that it causes intrusion into the client code.3. Collection at the Proxy layer
, which is a unified entrance. Collection and reporting can be done at the Proxy layer, but the disadvantage is obvious. Not all redis cluster architectures have proxies.
4. Use redis’ built-in command
- monitor command
- : This command can be captured in real time The redis server receives the command and then writes code to count the hot keys. Of course, there are also ready-made analysis tools that you can use, such as redis-faina. However, under high concurrency conditions, this command has the hidden danger of sudden increase in memory and will also reduce the performance of redis.
- : redis 4.0.3 provides the hotkey discovery function of redis-cli. Just add the –hotkeys option when executing redis-cli. However, when this parameter is executed, if there are many keys, the execution will be slower.
5. Self-capture packet evaluationThe Redis client uses the TCP protocol to interact with the server. The communication protocol uses
RESP. Write your own program to monitor the port, parse the data according to RESP protocol rules, and conduct analysis. The disadvantages are high development costs, difficult maintenance, and the possibility of packet loss. The above five options each have their own advantages and disadvantages. Just make a decision based on your business scenario.
1. Use the second-level cacheFor example, use
ehcache, spring cache, or even a HashMap will work. After you discover the hot key, load the hot key into the system's JVM. For this kind of hot key request, it will be fetched directly from the jvm without going to the redis layer.
Assume that there are 100,000 requests for the same key at this time. If there is no local cache, these 100,000 requests will be directly sent to the same redis.
Now assume that your application layer has 50 machines. OK, you also have jvm cache. These 100,000 requests are evenly distributed, and each machine has 2,000 requests. The value will be obtained from the JVM and then the data will be returned. This avoids the situation where hundreds of thousands of requests are sent to the same redis.2. Read and write separationRead and write separation is to send requests that are
Write to Within the Master module, the request for Read is sent to the ReadOnly module. The read-only nodes in the module can be further expanded, and this key can be stored in multiple redis. When a hot key request comes in, we randomly select a redis server with backup, access the value, and return the data. This effectively solves the problem of hot reading.
The separation of reading and writing also has the advantages of flexible expansion of read hotspot capabilities, the ability to store a large number of hotspot keys, and client-friendliness.
For more programming related knowledge, please visit:
Programming VideoThe above is the detailed content of How is the hotspot key generated in Redis? How to solve?. For more information, please follow other related articles on the PHP Chinese website!

