
1. Characters:
Characters include letters, numbers, arithmetic symbols, punctuation marks and others symbols, as well as some functional symbols. When characters are stored in the computer, the corresponding binary code representing the character should be specified. The selection of codes should be consistent with the specifications of the relevant peripheral devices. These peripheral devices include keyboard console input and output, printer output, and so on. When
characters are input, they are automatically converted into binary codes and stored in the machine; when output, the binary codes in the computer are automatically converted into characters. The conversion of both is achieved by peripheral devices. The
character is the smallest data access unit in the data structure. A character is usually represented by 8 binary bits (one byte), but there are also a few computer systems that use 6 binary character representations. The size of the character set in a system is completely determined by the system itself. The number of characters available for computers is generally 128 to 256 (excluding Chinese characters). After each character enters the computer, it will be converted into an 8-bit binary number. Different computer systems and different languages have different character ranges.
In ASCII encoding, one English alphabetic character requires 1 byte to store.
In GB 2312 encoding or GBK encoding, one Chinese character storage requires 2 bytes. In UTF-8 encoding, the storage of an English alphabetic character requires 1 byte, and the storage of a Chinese character requires 3 to 4 bytes. In UTF-16 encoding, the storage of an English alphabetic character or a Chinese character requires 2 bytes (some Chinese characters in the Unicode extension area require 4 bytes to store). In UTF-32 encoding, the storage of any character in the world requires 4 bytes.
2. String:
A string or string (String) is a string of characters composed of numbers, letters, and underscores. Generally recorded as s=“a1a2···an” (n>=0). It is a data type that represents text in programming languages. In programming, a string is a continuous sequence of symbols or values, such as a symbol string (a string of characters) or a binary digit string (a string of binary digits).
Usually the entire string is used as the operation object, such as: finding a substring in the string, obtaining a substring, inserting a substring at a certain position in the string, deleting a substring, etc. The necessary and sufficient conditions for two strings to be equal are: the lengths are equal, and the characters at each corresponding position are equal. Assume that p and q are two strings. The operation of finding the position where q first appears in p is called pattern matching. The two most basic storage methods of strings are sequential storage and linked storage.
The above is the detailed content of What do characters and strings mean?. For more information, please follow other related articles on the PHP Chinese website!
 php怎么将16进制字符串转为数字Oct 26, 2021 pm 06:36 PM
php怎么将16进制字符串转为数字Oct 26, 2021 pm 06:36 PMphp将16进制字符串转为数字的方法:1、使用hexdec()函数,语法“hexdec(十六进制字符串)”;2、使用base_convert()函数,语法“bindec(十六进制字符串, 16, 10)”。
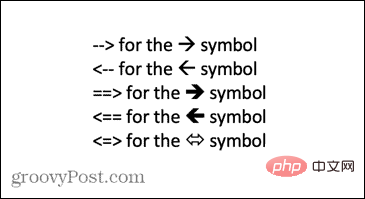 如何在 Word 中键入箭头Apr 16, 2023 pm 11:37 PM
如何在 Word 中键入箭头Apr 16, 2023 pm 11:37 PM如何使用自动更正在 Word 中键入箭头在 Word 中键入箭头的最快方法之一是使用预定义的自动更正快捷方式。如果您键入特定的字符序列,Word 会自动将这些字符转换为箭头符号。您可以使用此方法绘制多种不同的箭头样式。要使用自动更正在 Word 中键入箭头:将光标移动到文档中要显示箭头的位置。键入以下字符组合之一:如果您不希望将您键入的内容更正为箭头符号,请按键盘上的退格键会将
 如何在 Microsoft Excel 中应用上标和下标格式选项Apr 14, 2023 pm 12:07 PM
如何在 Microsoft Excel 中应用上标和下标格式选项Apr 14, 2023 pm 12:07 PM上标是一个字符或多个字符,可以是字母或数字,您需要将其设置为略高于正常文本行。例如,如果您需要写1st,则字母st需要略高于字符1。同样,下标是一组字符或单个字符,需要设置为略低于正常文本级别。例如,当你写化学式时,你需要把数字放在正常字符行的下方。以下屏幕截图显示了上标和下标格式的一些示例。尽管这似乎是一项艰巨的任务,但实际上将上标和下标格式应用于您的文本非常简单。在本文中,我们将通过一些简单的步骤说明如何轻松地使用上标或下标格式设置文本。希望你喜欢阅读这篇文章。如何在 Excel 中应用上标
 golang怎么检测变量是否为字符串Jan 06, 2023 pm 12:41 PM
golang怎么检测变量是否为字符串Jan 06, 2023 pm 12:41 PM检测变量是否为字符串的方法:1、利用“%T”格式化标识,语法“fmt.Printf("variable count=%v is of type %T \n", count, count)”;2、利用reflect.TypeOf(),语法“reflect.TypeOf(变量)”;3、利用reflect.ValueOf().Kind()检测;4、使用类型断言,可以对类型进行分组。
 如何在 iPhone 和 Mac 上输入扩展字符,例如度数符号?Apr 22, 2023 pm 02:01 PM
如何在 iPhone 和 Mac 上输入扩展字符,例如度数符号?Apr 22, 2023 pm 02:01 PM您的物理或数字键盘在表面上提供有限数量的字符选项。但是,有几种方法可以在iPhone、iPad和Mac上访问重音字母、特殊字符等。标准iOS键盘可让您快速访问大写和小写字母、标准数字、标点符号和字符。当然,还有很多其他角色。您可以从带有变音符号的字母到倒置的问号中进行选择。您可能无意中发现了隐藏的特殊字符。如果没有,以下是在iPhone、iPad和Mac上访问它们的方法。如何在iPhone和iPad上访问扩展字符在iPhone或iPad上获取扩展字符非常简单。在“信息”、“
 使用java的Character.isDigit()函数判断字符是否为数字Jul 27, 2023 am 09:32 AM
使用java的Character.isDigit()函数判断字符是否为数字Jul 27, 2023 am 09:32 AM使用Java的Character.isDigit()函数判断字符是否为数字字符在计算机内部以ASCII码的形式表示,每个字符都有一个对应的ASCII码。其中,数字字符0到9分别对应的ASCII码值为48到57。要判断一个字符是否为数字,可以使用Java中的Character类提供的isDigit()方法进行判断。isDigit()方法是Character类的
 正确在matplotlib中显示中文字符的方法Jan 13, 2024 am 11:03 AM
正确在matplotlib中显示中文字符的方法Jan 13, 2024 am 11:03 AM在matplotlib中正确地显示中文字符,是很多中文用户常常遇到的问题。默认情况下,matplotlib使用的是英文字体,无法正确显示中文字符。为了解决这个问题,我们需要设置正确的中文字体,并将其应用到matplotlib中。下面是一些具体的代码示例,帮助你正确地在matplotlib中显示中文字符。首先,我们需要导入需要的库:importmatplot
 php怎么将字符串转为布尔类型Jul 01, 2021 pm 06:36 PM
php怎么将字符串转为布尔类型Jul 01, 2021 pm 06:36 PM转换方法:1、在转换变量前加上用括号括起来的目标类型“(bool)”或“(boolean)”;2、用boolval()函数,语法“boolval(字符串)”;3、用settype()函数,语法“settype(变量,"boolean")”。

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Chinese version
Chinese version, very easy to use

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

Notepad++7.3.1
Easy-to-use and free code editor

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.






