
The operating environment of this tutorial: Windows 10 system, Dell G3 computer.
The current network attack model is multi-faceted and multi-method, making it difficult to guard against. Generally speaking, they are divided into four categories: denial of service attacks, exploitation attacks, information collection attacks, and fake news attacks.
1. Denial of service attack
Denial of service attack attempts to prevent you from providing services by crashing your service computer or overwhelming it. Denial of service attack is the most common Easily implemented attacks:
teardrop
Overview: Teardrop attacks exploit information contained in the headers of packets in IP fragments that are trusted by the TCP/IP stack implementation to implement your own attack. IP fragments contain information indicating which part of the original packet the fragment contains. Some TCP/IP (including NT before servicepack 4) will crash when receiving forged fragments containing overlapping offsets.
Defense: The server applies the latest service pack, or reassembles segments when setting up a firewall instead of forwarding them.
2. Exploitation attack
Exploitation attack is a type of attack that attempts to directly control your machine:
Trojan horse
Overview: A Trojan horse is a program that is secretly installed on a target system either directly by a hacker or by an unsuspecting user. Once the installation is successful and administrator rights are obtained, the person who installed the program can directly control the target system remotely.
The most effective one is called backdoor program. Malicious programs include: NetBus, BackOrifice and BO2k, and benign programs used to control the system such as: netcat, VNC, pcAnywhere. The ideal backdoor operates transparently.
Defense: Avoid downloading suspicious programs and refusing to execute them, and use network scanning software to regularly monitor the listening TCP service on the internal host.
3. Information collection attacks
Information collection attacks do not cause harm to the target itself. As the name suggests, this type of attack is used to provide useful information for further intrusions. Information. Mainly include: scanning technology, architecture probing, and use of information services
(1) Address scanning
Overview: Use programs such as ping to detect target addresses, and responses to this indicate its existence.
Defense: Filter out ICMP reply messages on the firewall.
(2) Architecture detection
Overview: Hackers use automated tools with a database of known response types to examine responses from the target host to bad packet transmissions . Since each operating system has its own unique response method (for example, the specific implementation of the TCP/IP stack is different between NT and Solaris), by comparing this unique response with known responses in the database, hackers can often determine The operating system that the target host is running.
Defense: Remove or modify various banners, including those of the operating system and various application services, and block ports used for identification to disrupt the opponent's attack plan.
(3) Utilize information services
DNS domain conversion
Overview: The DNS protocol does not authenticate conversions or informational updates, which makes the protocol regarded as Utilize it in different ways. If you maintain a public DNS server, a hacker can obtain the names and internal IP addresses of all your hosts by performing a domain translation operation.
Defense: Filter out domain conversion requests at the firewall.
4. Fake message attack
is used to attack messages with incorrect target configuration, mainly including: DNS cache pollution and fake emails.
DNS Cache Pollution
Overview: Because DNS servers exchange information with other name servers without authentication, this allows hackers to incorporate incorrect information and compromise users. Directed to the hacker's own host.
Defense: Filter inbound DNS updates on the firewall. External DNS servers should not be able to change what your internal servers know about internal machines.
Fake Email
Overview: Since SMTP does not authenticate the sender of an email, a hacker can forge an email to your internal customers, claiming to be from someone they know and know. Believers, and come with an installable Trojan horse, or a link to a malicious website.
Defense: Use security tools like PGP and install email certificates.
The above is the detailed content of What are the 4 main types of cyber attacks?. For more information, please follow other related articles on the PHP Chinese website!
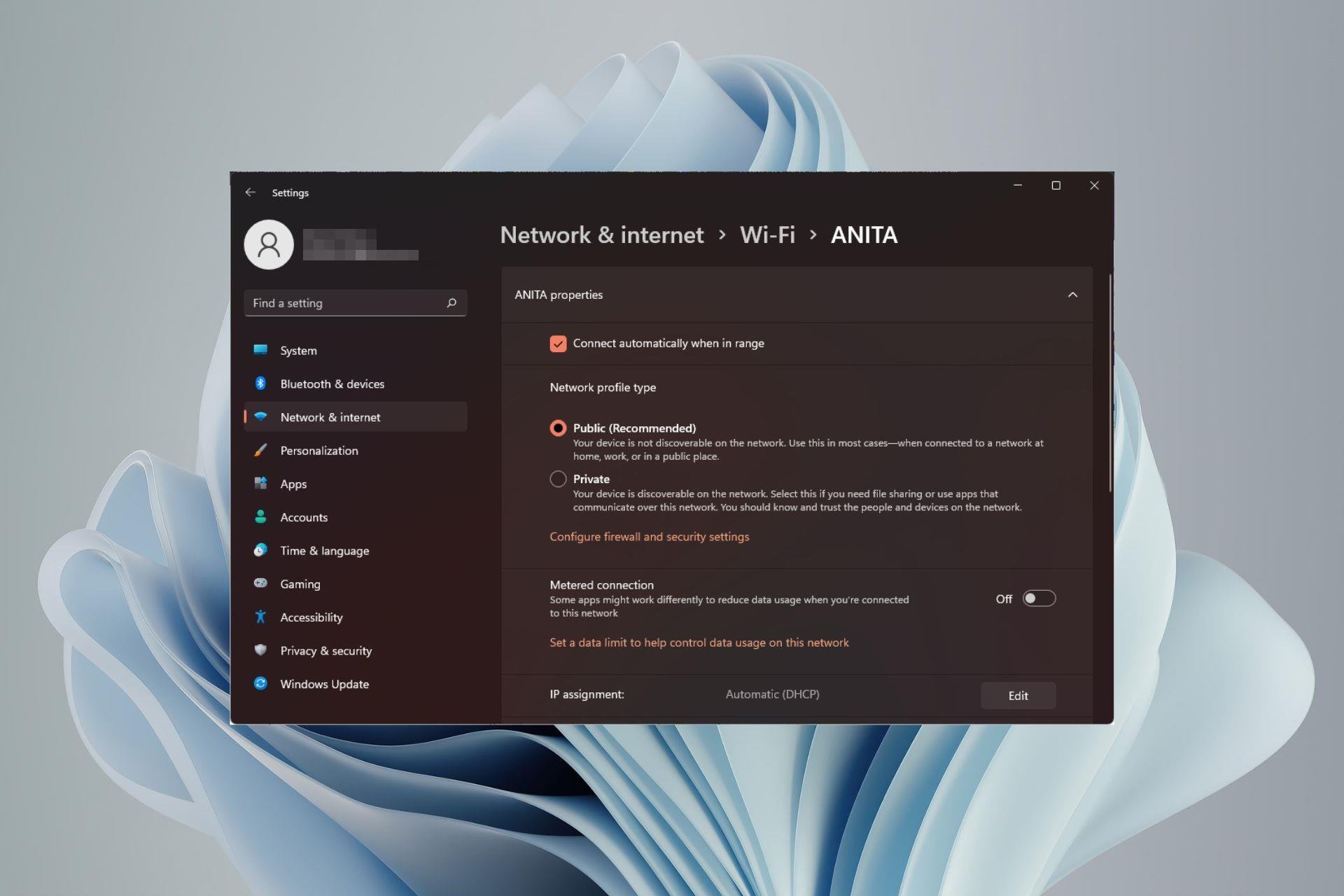 如何在 Windows 11 中更改网络类型为专用或公共Aug 24, 2023 pm 12:37 PM
如何在 Windows 11 中更改网络类型为专用或公共Aug 24, 2023 pm 12:37 PM设置无线网络很常见,但选择或更改网络类型可能会令人困惑,尤其是在您不知道后果的情况下。如果您正在寻找有关如何在Windows11中将网络类型从公共更改为私有或反之亦然的建议,请继续阅读以获取一些有用的信息。Windows11中有哪些不同的网络配置文件?Windows11附带了许多网络配置文件,这些配置文件本质上是可用于配置各种网络连接的设置集。如果您在家中或办公室有多个连接,这将非常有用,因此您不必每次连接到新网络时都进行所有设置。专用和公用网络配置文件是Windows11中的两种常见类型,但通
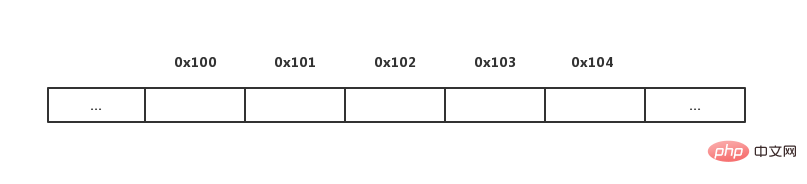 用Python实现动态数组:从入门到精通Apr 21, 2023 pm 12:04 PM
用Python实现动态数组:从入门到精通Apr 21, 2023 pm 12:04 PMPart1聊聊Python序列类型的本质在本博客中,我们来聊聊探讨Python的各种“序列”类,内置的三大常用数据结构——列表类(list)、元组类(tuple)和字符串类(str)的本质。不知道你发现没有,这些类都有一个很明显的共性,都可以用来保存多个数据元素,最主要的功能是:每个类都支持下标(索引)访问该序列的元素,比如使用语法Seq[i]。其实上面每个类都是使用数组这种简单的数据结构表示。但是熟悉Python的读者可能知道这3种数据结构又有一些不同:比如元组和字符串是不能修改的,列表可以
 日本 JAXA 道歉,因遭遇网络攻击而导致合作伙伴信息泄露Jul 10, 2024 pm 02:57 PM
日本 JAXA 道歉,因遭遇网络攻击而导致合作伙伴信息泄露Jul 10, 2024 pm 02:57 PM本站7月5日消息,日本宇宙航空研究开发机构(JAXA)今日发布公告,证实去年遭受的网络攻击导致了信息外泄,并就此向相关单位道歉。JAXA表示,此次泄露的信息不仅包括该机构内部信息,而且还有与外部组织联合行动相关的信息和个人信息,JAXA认为“此事可能损害信赖关系”,但由于与对方的关系将不提供详细信息。对此,JAXA已向泄露信息的个人和相关方表示歉意,并逐一通知。截至目前,JAXA尚未收到有关相关人员的业务活动受到任何重大影响的报告,但他们对由此造成的任何不便深表歉意,并再次致歉。本站注意到,JA
 视频矩阵账号怎么做?它的矩阵账号都有哪些类型呢?Mar 21, 2024 pm 04:57 PM
视频矩阵账号怎么做?它的矩阵账号都有哪些类型呢?Mar 21, 2024 pm 04:57 PM随着短视频平台的盛行,视频矩阵账号营销已成为一种新兴营销方式。通过在不同平台上创建和管理多个账号,企业和个人能够实现品牌推广、粉丝增长和产品销售等目标。本文将为您探讨如何有效运用视频矩阵账号,并介绍不同类型的视频矩阵账号。一、视频矩阵账号怎么做?要想做好视频矩阵账号,需要遵循以下几个步骤:首先要明确你的视频矩阵账号的目标是什么,是为了品牌传播、粉丝增长还是产品销售。明确目标有助于制定相应的策略。2.选择平台:根据你的目标受众,选择合适的短视频平台。目前主流的短视频平台有抖音、快手、火山小视频等。
 Golang 函数返回值的类型是什么?Apr 13, 2024 pm 05:42 PM
Golang 函数返回值的类型是什么?Apr 13, 2024 pm 05:42 PMGo函数可以返回多个不同类型的值,返回值类型在函数签名中指定,并通过return语句返回。例如,函数可以返回一个整数和一个字符串:funcgetDetails()(int,string)。实战中,一个计算圆面积的函数可以返回面积和一个可选错误:funccircleArea(radiusfloat64)(float64,error)。注意事项:如果函数签名未指定类型,则返回空值;建议使用显式类型声明的return语句以提高可读性。
 Python中类型提示的最佳实践Apr 23, 2023 am 09:28 AM
Python中类型提示的最佳实践Apr 23, 2023 am 09:28 AM使用动态语言一时爽,代码重构火葬场。相信你一定听过这句话,和单元测试一样,虽然写代码的时候花费你少量的时间,但是从长远来看,这是非常值得的。本文分享如何更好的理解和使用Python的类型提示。1、类型提示仅在语法层面有效类型提示(自PEP3107开始引入)用于向变量、参数、函数参数以及它们的返回值、类属性和方法添加类型。Python的变量类型是动态的,可以在运行时修改,为代码添加类型提示,仅在语法层面支持,对代码的运行没有任何影响,Python解释器在运行代码的时候会忽略类型提示。因此类型提
 C++ 函数的类型和特性Apr 11, 2024 pm 03:30 PM
C++ 函数的类型和特性Apr 11, 2024 pm 03:30 PMC++函数有以下类型:简单函数、const函数、静态函数、虚函数;特性包括:inline函数、默认参数、引用返回、重载函数。例如,calculateArea函数使用π计算给定半径圆的面积,并将其作为输出返回。
 主要的自媒体平台有哪些?自媒体平台的类型有哪些呢?Mar 21, 2024 pm 06:36 PM
主要的自媒体平台有哪些?自媒体平台的类型有哪些呢?Mar 21, 2024 pm 06:36 PM随着互联网的快速发展,自媒体已经成为了信息传播的重要渠道。自媒体平台为个人和企业提供了一个展示自己、传播信息的舞台。目前,市场上主要的自媒体平台有微信公众号、今日头条、一点资讯、企鹅媒体平台等。这些平台各有特色,为广大自媒体从业者提供了丰富的创作空间。接下来,我们将对这些平台进行详细介绍,并探讨自媒体平台的类型。一、主要的自媒体平台有哪些?微信公众号是腾讯推出的自媒体平台,为个人和企业用户提供信息发布和传播服务。它分为服务号和订阅号两种类型,服务号主要为企业提供服务,而订阅号则侧重于资讯传播。由

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Safe Exam Browser
Safe Exam Browser is a secure browser environment for taking online exams securely. This software turns any computer into a secure workstation. It controls access to any utility and prevents students from using unauthorized resources.

PhpStorm Mac version
The latest (2018.2.1) professional PHP integrated development tool

MinGW - Minimalist GNU for Windows
This project is in the process of being migrated to osdn.net/projects/mingw, you can continue to follow us there. MinGW: A native Windows port of the GNU Compiler Collection (GCC), freely distributable import libraries and header files for building native Windows applications; includes extensions to the MSVC runtime to support C99 functionality. All MinGW software can run on 64-bit Windows platforms.

WebStorm Mac version
Useful JavaScript development tools

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),






