 Backend Development
Backend Development PHP Tutorial
PHP Tutorial Nginx load scheduler + dual Tomcat load and session sharing + MySQL back-end database
Nginx load scheduler + dual Tomcat load and session sharing + MySQL back-end databaseThis article mainly introduces the Nginx load scheduler dual Tomcat load and session sharing MySQL back-end database. It has a certain reference value. Now I share it with you. Friends in need can refer to it
Nginx Load scheduler dual Tomcat load and session replication MySQL backend database
Environment:
| Function | |
|---|---|
| nginx | |
| tomcat1 | |
| tomcat2 | |
| mysql |
Steps:
①Close the firewall or open ports 80, 8080, 3306, close selinux
②Install nginx
从nginx官网下载最新版 wget http://nginx.org/download/nginx-1.13.9.tar.gz
[root@192 ~]# yum -y install pcre-devel zlib-devel gcc gcc-c make
[root@192 ~]# useradd -M -s /sbin/nologin nginx
[root@192 ~]# tar zxf nginx-1.13.9.tar.gz -C /usr/src
[root@192 ~]# cd /usr/src/nginx-1.13 .9/
[root@192 nginx-1.13.9]# ./configure --prefix=/usr/local/nginx --user=nginx --group=nginx --with-http_stub_status_module && make && make install
[root@192 ~]# ln -s /usr/local/nginx/sbin/nginx /usr/local/sbin
Do not start nginx③Two tomcat hosts for installation
jdk从官网下载需要许可,允许之后下载至本地,导入主机 tomcat从官网downloads找到tomcat7.0或者更高版本 wget http://mirror.bit.edu.cn/apache/tomcat/tomcat-7/v7.0.86/bin/apache-tomcat-7.0.86.tar.gz
[root@192 ~]# tar zxf jdk-7u65-linux-x64.gz -C /usr/src
[root@192 ~]# tar zxf apache-tomcat-7.0.54.tar.gz -C /usr/src
[root@192 ~]# mv jdk1.7.0_65/ /usr/local/ java
[root@192 ~]# mv apache-tomcat-7.0.54/ /usr/local/tomcat7
[root@192 ~]# vim /etc/profile
export JAVA_HOME=/usr/local/java export CATALINA_HOME=/usr/local/tomcat7 export PATH=$JAVA_HOME/bin:$CATALINA_HOME/bin:$PATH
[root@192 ~]# source /etc/profile
[root@192 ~]# java -version
java version "1.8.0_171" Java(TM) SE Runtime Environment (build 1.8.0_171-b11) Java HotSpot(TM) 64-Bit Server VM (build 25.171-b11, mixed mode)
[root@192 ~]# catalina.sh version
Using CATALINA_BASE: /usr/local/tomcat7 Using CATALINA_HOME: /usr/local/tomcat7 Using CATALINA_TMPDIR: /usr/local/tomcat7/temp Using JRE_HOME: /usr/local/java Using CLASSPATH: /usr/local/tomcat7/bin/bootstrap.jar:/usr/local/tomcat7/bin/tomcat-juli.jar Server version: Apache Tomcat/7.0. Server built: May 19 2014 10:26:15 Server number: 7.0.86.0 OS Name: Linux OS Version: 3.10.0-327.el7.x86_64 Architecture: amd64 JVM Version: 1.7.0_65-b17 JVM Vendor: Oracle Corporation
Start tomcat
[root@192 ~]# /usr/local/tomcat7/bin/startup.shUsing CATALINA_BASE: /usr/local/tomcat7 Using CATALINA_HOME: /usr/local/tomcat7 Using CATALINA_TMPDIR: /usr/local/tomcat7/temp Using JRE_HOME: /usr/local/java Using CLASSPATH: /usr/local/tomcat7/bin/bootstrap.jar:/usr/local/tomcat7/bin/tomcat-juli.jar Tomcat started.
Test access
http:// 192.168.2.6:8080
http://192.168.2.7:8080[root@192 ~]#cd /usr/local/tomcat7/conf
④Two hosts modify the tomcat configuration file
[root@192 ~]#cp server.xml server.xml.bak
[root@192 ~]#vim server.xml
....... <engine> <host> <context></context></host></engine>
[root@192 ~]#mkdir -p /web/webapp1
[root@192 ~]#vim /web/webapp1/index.jsp
<title>tomcat-1</title> <h1 id="font-Session-serviced-by-tomcat-font"><font>Session serviced by tomcat</font></h1>
| Session ID | |
| Create on |
Restart tomcat
[root@192 ~] #shutdown.sh[root@192 ~]#startup.sh
Test access in jsp shows that the session IDs of the two tomcat hosts are different, and the preparations are completed
http://192.168.2.6 :8080
http://192.168.2.7:8008
2. Session sharing configuration
Steps:
①Configure session sharing cluster on two hosts
[root@192 ~]#vim /usr/local/tomcat7/conf/server.xml.......
<engine>
<!--For clustering, please take a look at documentation at:
/docs/cluster-howto.html (simple how to)
/docs/config/cluster.html (reference documentation) -->
<!--
<Cluster className="org.apache.catalina.ha.tcp.SimpleTcpCluster"/>
-->
<cluster>
<manager></manager>
<channel ina.tribes.group.groupchannel>
<membership></membership>
<receiver></receiver>
<sender>
<transport></transport>
</sender>
<interceptor></interceptor>
<interceptor></interceptor>
</channel>
<valve></valve>
<valve></valve>
<deployer></deployer>
<clusterlistener></clusterlistener>
<clusterlistener></clusterlistener>
</cluster>
<!-- Use the LockOutRealm to prevent attempts to guess user passwords
via a brute-force attack -->
<realm>
<!-- This Realm uses the UserDatabase configured in the global JNDI
resources under the key "UserDatabase". Any edits
that are performed against this UserDatabase are immediately
available for use by the Realm. -->
<realm></realm>
</realm>
<host>
<context></context></host></engine>
[root@192 ~]#mkdir /web/webapp1/WEB-INF
[ root@192 ~]#cp /usr/local/tomcat7/conf/web.xml WEB-INF/
[root@192 ~]#vim WEB-INF/web.xml
<web-app> <distributable></distributable> #添加这个单词,必须有这一步,否则用户的session没法使用</web-app>If the firewall is enabled, enable the following
[root@192 ~]#firewall-cmd --add-port=45564/udp --permanent
[root@192 ~]#firewall-cmd --add-port=4000/tcp --permanent
[root@192 ~]#firewall-cmd --reload
Restart tomcat
[root@192 ~]#startup.sh
②Configure nginx
[root@192 ~]#vim /usr/local/nginx/conf/nginx.conf
.......
http {
.......
upstream tomcat_server {
server 192.168.2.6:8080 weight=1;
server 192.168.2.7:8080 weight=1;
}
#gzip on;
server {
listen 80;
server_name localhost;
#charset koi8-r;
#access_log logs/host.access.log main;
location / {
root html;
index index.html index.htm;
proxy_pass http://tomcat_server;
}
Start nginx, visit the nginx address and refresh the page to test access
[root@192 ~]#nginx
http://192.168.2.5
3. Connection mysql database
Steps:
①The mysql container in 192.168.2.8 serves as the database server, configure mysql:
mysql>grant all privileges on.
to javauser @'192.168.2.%' identified by '123.com';mysql> create database javatest
mysql>use javatest
mysql>create table testdata(id int not null auto_increment primary key,foo varchar(25),bar varchar(10));
mysql>insert into testdata(foo,bar) values('hello','123.com');
mysql>select * from testdata;
| foo | bar | |
|---|---|---|
| hello | 123.com |
The above is the detailed content of Nginx load scheduler + dual Tomcat load and session sharing + MySQL back-end database. For more information, please follow other related articles on the PHP Chinese website!
 内存飙升!记一次nginx拦截爬虫Mar 30, 2023 pm 04:35 PM
内存飙升!记一次nginx拦截爬虫Mar 30, 2023 pm 04:35 PM本篇文章给大家带来了关于nginx的相关知识,其中主要介绍了nginx拦截爬虫相关的,感兴趣的朋友下面一起来看一下吧,希望对大家有帮助。
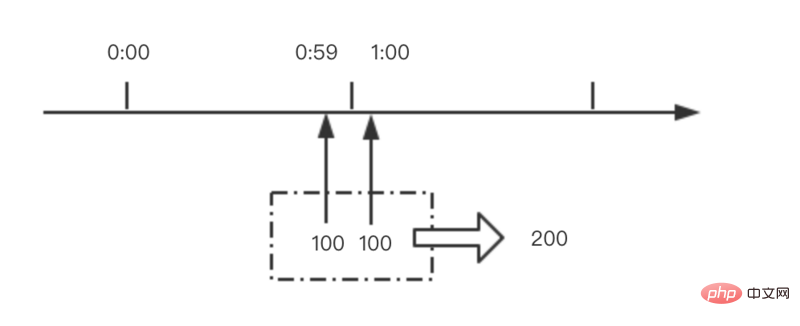 nginx限流模块源码分析May 11, 2023 pm 06:16 PM
nginx限流模块源码分析May 11, 2023 pm 06:16 PM高并发系统有三把利器:缓存、降级和限流;限流的目的是通过对并发访问/请求进行限速来保护系统,一旦达到限制速率则可以拒绝服务(定向到错误页)、排队等待(秒杀)、降级(返回兜底数据或默认数据);高并发系统常见的限流有:限制总并发数(数据库连接池)、限制瞬时并发数(如nginx的limit_conn模块,用来限制瞬时并发连接数)、限制时间窗口内的平均速率(nginx的limit_req模块,用来限制每秒的平均速率);另外还可以根据网络连接数、网络流量、cpu或内存负载等来限流。1.限流算法最简单粗暴的
 nginx+rsync+inotify怎么配置实现负载均衡May 11, 2023 pm 03:37 PM
nginx+rsync+inotify怎么配置实现负载均衡May 11, 2023 pm 03:37 PM实验环境前端nginx:ip192.168.6.242,对后端的wordpress网站做反向代理实现复杂均衡后端nginx:ip192.168.6.36,192.168.6.205都部署wordpress,并使用相同的数据库1、在后端的两个wordpress上配置rsync+inotify,两服务器都开启rsync服务,并且通过inotify分别向对方同步数据下面配置192.168.6.205这台服务器vim/etc/rsyncd.confuid=nginxgid=nginxport=873ho
 nginx php403错误怎么解决Nov 23, 2022 am 09:59 AM
nginx php403错误怎么解决Nov 23, 2022 am 09:59 AMnginx php403错误的解决办法:1、修改文件权限或开启selinux;2、修改php-fpm.conf,加入需要的文件扩展名;3、修改php.ini内容为“cgi.fix_pathinfo = 0”;4、重启php-fpm即可。
 如何解决跨域?常见解决方案浅析Apr 25, 2023 pm 07:57 PM
如何解决跨域?常见解决方案浅析Apr 25, 2023 pm 07:57 PM跨域是开发中经常会遇到的一个场景,也是面试中经常会讨论的一个问题。掌握常见的跨域解决方案及其背后的原理,不仅可以提高我们的开发效率,还能在面试中表现的更加
 nginx部署react刷新404怎么办Jan 03, 2023 pm 01:41 PM
nginx部署react刷新404怎么办Jan 03, 2023 pm 01:41 PMnginx部署react刷新404的解决办法:1、修改Nginx配置为“server {listen 80;server_name https://www.xxx.com;location / {root xxx;index index.html index.htm;...}”;2、刷新路由,按当前路径去nginx加载页面即可。
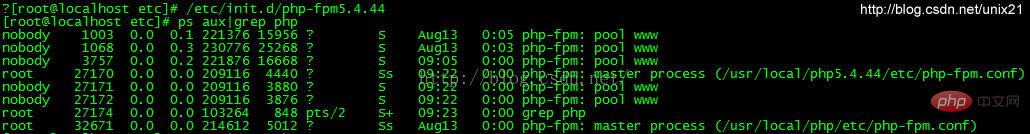 Linux系统下如何为Nginx安装多版本PHPMay 11, 2023 pm 07:34 PM
Linux系统下如何为Nginx安装多版本PHPMay 11, 2023 pm 07:34 PMlinux版本:64位centos6.4nginx版本:nginx1.8.0php版本:php5.5.28&php5.4.44注意假如php5.5是主版本已经安装在/usr/local/php目录下,那么再安装其他版本的php再指定不同安装目录即可。安装php#wgethttp://cn2.php.net/get/php-5.4.44.tar.gz/from/this/mirror#tarzxvfphp-5.4.44.tar.gz#cdphp-5.4.44#./configure--pr
 nginx怎么禁止访问phpNov 22, 2022 am 09:52 AM
nginx怎么禁止访问phpNov 22, 2022 am 09:52 AMnginx禁止访问php的方法:1、配置nginx,禁止解析指定目录下的指定程序;2、将“location ~^/images/.*\.(php|php5|sh|pl|py)${deny all...}”语句放置在server标签内即可。


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

SublimeText3 Chinese version
Chinese version, very easy to use

mPDF
mPDF is a PHP library that can generate PDF files from UTF-8 encoded HTML. The original author, Ian Back, wrote mPDF to output PDF files "on the fly" from his website and handle different languages. It is slower than original scripts like HTML2FPDF and produces larger files when using Unicode fonts, but supports CSS styles etc. and has a lot of enhancements. Supports almost all languages, including RTL (Arabic and Hebrew) and CJK (Chinese, Japanese and Korean). Supports nested block-level elements (such as P, DIV),

Notepad++7.3.1
Easy-to-use and free code editor

DVWA
Damn Vulnerable Web App (DVWA) is a PHP/MySQL web application that is very vulnerable. Its main goals are to be an aid for security professionals to test their skills and tools in a legal environment, to help web developers better understand the process of securing web applications, and to help teachers/students teach/learn in a classroom environment Web application security. The goal of DVWA is to practice some of the most common web vulnerabilities through a simple and straightforward interface, with varying degrees of difficulty. Please note that this software

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.






