 Operation and Maintenance
Operation and Maintenance Windows Operation and Maintenance
Windows Operation and Maintenance How to close ports 135, 139, 445, 593, 1025, etc.
How to close ports 135, 139, 445, 593, 1025, etc.Operation essentials: Close the ports and prevent network viruses from accessing these ports to ensure computer security and reduce the impact of viruses on Internet speed.
Recently, it was discovered that some people are infected with a new network worm virus. This virus cannot be killed using the shock wave virus killing tool. Please upgrade the anti-virus software virus database on your computer as soon as possible and scan the hard disk while disconnecting the computer network. , check and kill viruses. Users who have installed firewall software, please
Block TCP 135, 139, 445, 593, 1025 ports and UDP 135, 137, 138, 445
In addition, you can also block the backdoor ports of some popular viruses, such as TCP 2745, 3127, 6129
ports, so you can also temporarily block incoming connections to those ports.
At present, many viruses will guess the username and password of computer users and brute force crack them. For the security of your computer, please set a secure password for your computer that is not easy to guess.
Operation steps
Open the "Control Panel" (the connection to open the "Control Panel" can be found in the "Settings" menu of "My Computer" or the "Start Menu")
In the "Control Panel" Find "Administrative Tools".
Double-click to open "Administrative Tools" and find "Local Security Policy".
Double-click to open "Local Security Policy" and find "IP Security Policy", as shown in Figure 1. 
Figure 1: Find "IP Security Policy" in "Local Security Policy"
Right-click the blank space in the right pane, and select "Create IP Security" in the pop-up shortcut menu Policy" 
Figure 2: Create a new policy
Click the "Next" button in the wizard, go to the second page to name the new security policy, or directly Click "Next" again. When you reach the "Secure Communication Request", "Activate Default Corresponding Rules" is selected by default. Please click this option box with the mouse to change the selected
status to the unselected state, as shown in Figure 3, and then Click "Next".  Figure 3: Do not activate the default selected state
Figure 3: Do not activate the default selected state
Click the "Finish" button and "Edit
Properties", as shown in Figure 4.  Figure 4: Complete the new strategy addition
Figure 4: Complete the new strategy addition
In the "Properties" dialog box, check whether "Use the Add Wizard" is selected. If it is selected, please click it with the mouse to make it become unselected and click the "Add" button. As shown in Figure 5.  Figure 5: Click the "Add" button to add a new connection rule
Figure 5: Click the "Add" button to add a new connection rule
In the "New Rule Properties" dialog box, click the "Add" button, as shown in Figure 6.  Figure 6: Add new rule
Figure 6: Add new rule
In the IP policy list, first uncheck "Use Add Wizard", and then click the "Add" button. As shown in Figure 7.  Figure 7: Add a new filter
Figure 7: Add a new filter
Come to the "Filter Properties" dialog box. The first thing you see is addressing. Select "Any IP Address" for the source address and select "Any IP Address" for the destination address. "My IP address", as shown in Figure 8.  Figure 8: Filter Properties
Figure 8: Filter Properties
Click the "Protocol" tab, first select "TCP" in the
drop-down list under "Select Protocol Type", and then The gray "Set Protocol Port" will turn colored, then enter "135" in the text box under "To this port" and click the "OK" button. As shown in Figure 9.  Figure 9: Add a filter to block TCP 135 (RPC) port
Figure 9: Add a filter to block TCP 135 (RPC) port
Return to the filter list dialog box, you can see that a policy has been added, repeat steps 11, 12, 13. Continue to add TCP 137, 139, 445, 593 ports and UDP
135, 139, 445 ports. Because some worms currently scan your computer for TCP 1025, 2745, 3127, 6129
ports, so you can also temporarily add blocking policies for these ports, discard data packets accessing these ports, and do not respond, thereby reducing the impact on your Internet access. Click the Close button. As shown in Figure 10. 
Figure 10: Repeat the steps to add each port filter
In the "New Rule Properties" dialog box, click "New IP Filter List", a dot will be added to the circle on the left, indicating Already activated, then click the "Filter Operations" tab, as shown in Figure 11. 
Figure 11: Activate "New IP Filter List"
In the "Filter Action" tab, first leave "Use Add Wizard" unchecked, and then click "Add" button. As shown in Figure 12. 
Figure 12: Add filter operation
In the "Security Measures" tab of "New Filter Operation Properties", select "Block", and then click the "OK" button. As shown in Figure 13. 
Figure 13: Add the "Block" operation
In the "New Rule Properties" dialog box, you can see that there is a new "Filter Operation", click this "New Filter" "Operation", a dot will be added to the circle to the left of it, indicating that it has been activated, and then you can click the "Close" button to close the dialog box. As shown in Figure 14. 
Figure 14: Activate "New Filter Action"
Return to the "New IP Security Policy Properties" dialog box and press the "Close" button to close the dialog box. As shown in Figure 15. 
Figure 15: Close the "New IP Security Policy Properties" dialog box
Finally, return to the "Local Security Policy" window, right-click the newly added IP security policy, and then select "Assign", as shown in Figure 16. 
Figure 16: Assign a new IP security policy
At this time, your computer already has the ability to temporarily protect against RPC worms.
Finally, please visit the RPC vulnerability and MS04-011 security vulnerability notice patch download webpage provided here to download the patch suitable for your computer, and then go to the Windows Update website to download it for your computer Latest updatepatch for Windows.
The above is the detailed content of How to close ports 135, 139, 445, 593, 1025, etc.. For more information, please follow other related articles on the PHP Chinese website!
![在Windows PC上检测到Soundbar作为显示器屏幕[修复]](https://img.php.cn/upload/article/000/465/014/170835733166289.jpg) 在Windows PC上检测到Soundbar作为显示器屏幕[修复]Feb 19, 2024 pm 11:42 PM
在Windows PC上检测到Soundbar作为显示器屏幕[修复]Feb 19, 2024 pm 11:42 PM在WindowsPC上,有用户发现将Soundbar连接到HDMI端口时会被识别为显示器的问题。这可能会导致一些困扰,但解决方案并非唯一。Soundbar如何通过HDMI连接到PC大多数音棒使用HDMI、光学或3.5mm音频连接。如果您的音棒只支持HDMI连接,那么必须将其连接到带有HDMIARC标签的HDMI端口。许多电视或显示器通常配备多个HDMI端口,其中一个端口应该支持符合HDMI标准的ARC协议。换句话说,HDMI是用于传输音频和视频的接口,如果设备没有HDMI端口,可以考虑使用显示器
 linux 怎么查看远程服务器端口是否开放Mar 21, 2023 am 09:50 AM
linux 怎么查看远程服务器端口是否开放Mar 21, 2023 am 09:50 AMlinux查看远程服务器端口是否开放的方法:1、通过“nmap ip -p port”命令检测端口是否打开,具体命令如“nmap 172.17.193.18 -p 5902”;2、通过“nc -v ip port”命令检测端口是否打开,具体命令如“如nc -v 172.17.193.18 5902”。
 com1和com2是什么端口Aug 25, 2022 am 10:53 AM
com1和com2是什么端口Aug 25, 2022 am 10:53 AMcom1和com2是串行通讯端口,简称串口;一块主板一般带有两个com串行接口,通常用于连接鼠标即通讯设备,串行接口是指数据一位一位的顺序传送,特点是通信线路简单,只要一对传输线就可以实现双向通信。
 Win11怎样关闭445端口Jul 04, 2023 pm 12:17 PM
Win11怎样关闭445端口Jul 04, 2023 pm 12:17 PMWin11怎样关闭445端口?445号端口是一个TCP端口,是一个共享文件夹和打印机端口,在局域网内提供文件或打印机共享服务。近期有部分Win11用户想要关闭445端口,那么应该如何操作呢?很多小伙伴不知道怎么详细操作,小编下面整理了Win11关闭445端口的详细操作,如果你感兴趣的话,跟着小编一起往下看看吧! Win11关闭445端口的详细操作 1、首先,按Win+S组合键,或点击底部任务栏上的搜索图标,打开的Windows搜索窗口,顶部输入Windows防火墙,然后点击系统给出的最佳
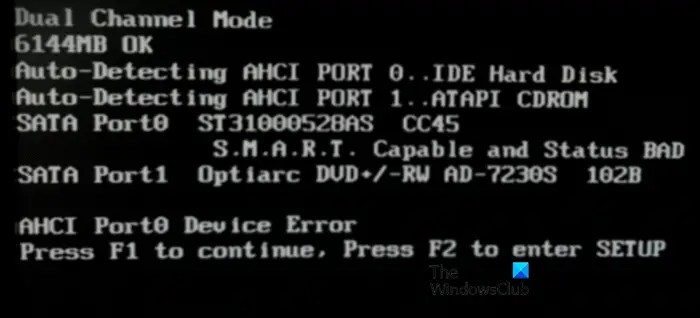 修复Windows计算机上的AHCI端口0设备错误Feb 19, 2024 pm 12:45 PM
修复Windows计算机上的AHCI端口0设备错误Feb 19, 2024 pm 12:45 PM如果你每次启动电脑时遇到AHCI端口0设备错误,需要按照本文提供的方法解决该问题。什么是AHCI端口0设备错误?AHCI设备错误是由BIOS报告的。SMART已指示端口0上的硬盘驱动器存在故障,可能无法访问。硬盘有可能随时出现问题。如果是台式机,建议尝试更换硬盘连接端口。若问题仍然存在,则可能是硬盘本身的问题。您可以运行磁盘检查工具,禁用故障硬盘并检查端口以解决此问题。修复Windows计算机上的AHCI端口0设备错误通常情况下,AHCIPort0设备错误并非源自操作系统问题,而是硬盘在端口0出
 iOS 17 更新后,您的 iPhone 无法充电?这是你可以做的Sep 21, 2023 pm 11:41 PM
iOS 17 更新后,您的 iPhone 无法充电?这是你可以做的Sep 21, 2023 pm 11:41 PMiOS17充电问题的原因是什么?更新到iOS17后,您的iPhone可能无法充电有几个可能的原因。一种可能性是软件更新中存在错误。Apple通常会快速修复iOS更新中的错误,因此,如果您遇到充电问题,则值得检查是否有新的更新。另一种可能性是充电电缆或适配器有问题。如果您使用的是第三方充电连接线或适配器,请确保它已通过Apple认证。如何修复iPhone不充电问题以下是有关如何修复iOS17更新后iPhone无法充电问题的一些提示:重启你的苹果手机这通常可以解决可能是iOS17充电问题根本原因的小
 如何关闭端口Jan 17, 2024 pm 02:07 PM
如何关闭端口Jan 17, 2024 pm 02:07 PM关闭端口的方法:1、使用防火墙关闭端口;2、使用系统配置关闭端口;3、使用第三方软件关闭端口;4、修改注册表关闭端口;5、使用路由器关闭端口;6、手动停止服务关闭端口;7、使用命令行关闭端口;8、使用安全软件关闭端口;9、修改应用程序配置关闭端口;10、使用网络设备关闭端口。详细介绍:1、使用防火墙关闭端口,打开“控制面板”,选择“Windows Defender防火墙”等等。
 如何使用LSOF实时监控端口Mar 20, 2024 pm 02:07 PM
如何使用LSOF实时监控端口Mar 20, 2024 pm 02:07 PMLSOF(ListOpenFiles)是一个命令行工具,主要用于监控类似Linux/Unix操作系统的系统资源。通过LSOF命令,用户可以获取有关系统中活动文件以及正在访问这些文件的进程的详细信息。LSOF能够帮助用户识别当前占用文件资源的进程,从而更好地管理系统资源和排除可能的问题。LSOF的功能强大且灵活,可以帮助系统管理员快速定位文件相关的问题,如文件泄漏、未关闭的文件描述符等。通过LSOF命令LSOF命令行工具允许系统管理员和开发人员:确定当前正在使用特定文件或端口的进程,在端口冲突的情


Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

EditPlus Chinese cracked version
Small size, syntax highlighting, does not support code prompt function

SecLists
SecLists is the ultimate security tester's companion. It is a collection of various types of lists that are frequently used during security assessments, all in one place. SecLists helps make security testing more efficient and productive by conveniently providing all the lists a security tester might need. List types include usernames, passwords, URLs, fuzzing payloads, sensitive data patterns, web shells, and more. The tester can simply pull this repository onto a new test machine and he will have access to every type of list he needs.

Zend Studio 13.0.1
Powerful PHP integrated development environment

Atom editor mac version download
The most popular open source editor

SublimeText3 Chinese version
Chinese version, very easy to use




