Home >Web Front-end >HTML Tutorial >The https era is here, but you still don't know anything about it?
The https era is here, but you still don't know anything about it?
- 阿神Original
- 2017-01-23 15:22:091310browse
Now when you open major well-known websites, have you noticed that a small green lock has been added to the address bar?

Yes, this is https, this is the era of https.
However, do you know https?
Simply put, https is http wrapped in SSL/TLS, which is secure http. What is safety? A secure network communication environment must solve three problems:
1. Confidentiality of communication content
2. True identity of both communicating parties
3. Integrity of communication content
And https was born to solve these three major problems (to be precise, it should be ssl). Let’s take a look at the solutions to these three problems respectively.
Confidentiality of communication content
Confidentiality of communication content needs to be achieved through encryption. Our Internet environment is very transparent, and communications need to go through many transits before reaching the recipient. This situation is a bit like handing a note to Xiaohong in the first row during class. On the note, you would definitely not directly write "see you at the playground at midnight tonight", but cleverly write "see you at the same place." Only you and Xiaohong know about this old place, so even if Xiaoming and Xiaoli see the note, they don't know whether the old place is the library or the English corner. This is encryption, and the old place is the so-called key.
Of course, this example is not very accurate. Simply put, encryption and decryption are a function, and the key is the parameter of this function. For example, we define a simple encryption function, f(x)=x+b, x is the input plaintext, and b is the key; the decryption function is the inverse function of the encryption function, that is, g(x)=x-b. When you don't know b, you can't guess the real content even if you see the ciphertext, so encryption is achieved. This kind of encryption and decryption uses the same key, which is called symmetric encryption
But there is a problem here. How is the parameter b here negotiated?
You and Xiaohong can spend time and money to make an appointment on the b value, but in a real network environment, there is no possibility of direct communication between you and Xiaohong. All communication If you have to rely on Xiao Ming and Xiao Li to pass the note, how can you avoid them? Here you need to use an asymmetric encryption algorithm. This algorithm has a pair of public keys and private keys. The public key is a key that everyone can obtain, and the private key is a key that the server keeps privately. In the asymmetric encryption algorithm, the content encrypted by the public key can only be decrypted by the private key, and the content encrypted by the private key can only be decrypted by the public key. So when you use Xiaohong’s public key to encrypt your note, Xiaoming, Xiaoli and others who help you deliver the note will not be able to read the content when they see the note. Only Xiaohong who has the private key can read your information. .
The symmetric encryption algorithm uses the same secret key for encryption and decryption; the asymmetric encryption algorithm requires two keys for encryption and decryption, and these two secret keys are public keys. (public key, referred to as public key) and private key (private key, referred to as private key). You may be curious about the principles of asymmetric encryption algorithms, but I will not go into details about the algorithms here. Interested students can search for them by themselves.
#Then the question is, what should I do if Xiaohong also wants to encrypt the response to you?
If Xiaohong uses her private key to encrypt, everyone in the class knows the public key, and the public key can decrypt the private key, which also means that everyone can decrypt Xiaohong’s Respond to messages. If you are smart, you must have thought of a solution: Use an asymmetric encryption algorithm to encrypt a symmetric key to Xiaohong. Xiaohong uses her private key to read the symmetric key, and then you use this symmetric key to perform symmetric encryption. Then you can have a pleasant date.
Of course, https does the same thing.
The true identity of the communicating parties
After encryption, the communication process seems to be perfect? Wait a minute, how does Xiaohong’s public key become known to the world?
You must know that all information exchanges in the network environment are carried out by passing notes, and Xiaohong’s public key is no exception. What if it is switched when it passes through Xiaoming’s hands? ? How to ensure that the Xiaohong public key in your hand is the real Xiaohong public key? Seeing that the notes about the crazy men and women in the class were being exchanged in various ways, Sister Feng, the entertainment committee member, decided to come forward. Sister Feng came up with a way to carry a certificate with her in all encrypted communications to prove her identity. This certificate was specially made by Sister Feng for all the singles in the class. The public key is placed in the certificate and returned to the sender of the note. In addition to the public key, the certificate also contains various information such as student number, name, and even zodiac sign, height and measurements. . There is a large identification seal stamped on the certificate. This is Sister Feng's unique seal, which means that the authenticity of the information on the certificate is guaranteed by Sister Feng. When you see this seal, you can think that the other party is a real single.
Through this information, you can know whether the other party is Xiaohong or Ruhua. This is the certificate mechanism.
Obviously you will suspect that Sister Feng’s official seal on the certificate may have been forged, and your suspicion is justified! Therefore, the official seal on the certificate is also asymmetrically encrypted. The encryption method is just the opposite of what is mentioned above: encrypted with Sister Feng’s private key, and decrypted with Sister Feng’s public key, so that the authenticity of the certificate can be verified. This official seal is the digital signature of the certificate. Specifically, it is the process of extracting the digest of the certificate using a hash algorithm and then encrypting the digest. In addition, you can also go directly to Sister Feng with the certificate, and Sister Feng will help you verify the validity of the certificate. (Certificates have an expiration date, so even real certificates may expire, so you need to pay attention)
This mechanism seems to be quite complete, but we have to build a security mechanism with a skeptical attitude, something that Sister Feng guarantees It's trustworthy.
But, is Sister Feng really Sister Feng? ? ?
Therefore, Sister Feng herself must be guaranteed by a certificate. Sister Feng’s certificate is issued by the head teacher, and the class teacher’s certificate is issued by the principal... This chain goes all the way to the most authoritative few Institutions, these institutions are the so-called root CAs in the https system. Roots are unquestionable authorities, they bring salt to themselves and prove themselves to be who they are. In the https certificate system, the root certificate comes with the operating system/browser. We can trust the certificates certified by these organizations, and then derive them layer by layer to the level of Fengjie.
In addition, because the certificate is actually very easy to obtain, it costs 10 yuan per copy at the subway entrance, and it costs 10 yuan for both Harvard and Stanford! Therefore, some companies will make their own certificates without going to the root CA organization at all, such as the famous 12306. You can also make your own certificate and put it online for users to download and import into their browsers, but because you don’t have Sister Feng’s influence, no one will believe you. Of course, some people don’t even believe Sister Feng...
The complete communication content
The password has also been added, and Sister Feng’s official seal has also been stamped. Is this mechanism sufficient? Is it perfect?
NoNoNo, think about it, Xiao Ming, who has a crush on you, will definitely feel unhappy when he sees you sending a note to Xiao Hong. Although he can’t understand it, he can still change the cipher text. Originally, you were going to ask Xiaohong to meet on the playground at midnight, but Xiaoming deleted the first half of the cipher text, and after decryption it happened to be "Meet on the playground." Then Xiaohong ran to the playground immediately after class, but you ran back to the dormitory to take a good shower. A bath. . . Then, Xiaohong ran away with Xiaoming~~
I believe everyone has a deep understanding of this scenario of tampering with communication content. When we visit some sites, advertisements from operators appear for no reason. This is all It was added by the operator! ! Therefore, the integrity of the content also needs to be guaranteed. This is relatively simple: first use a hash algorithm to extract the content summary, and then encrypt the summary to generate a digital signature. By verifying the digital signature, you can determine the integrity of the communication content.
The above is a simplified version of the technology used in https. An http communication process is as follows:
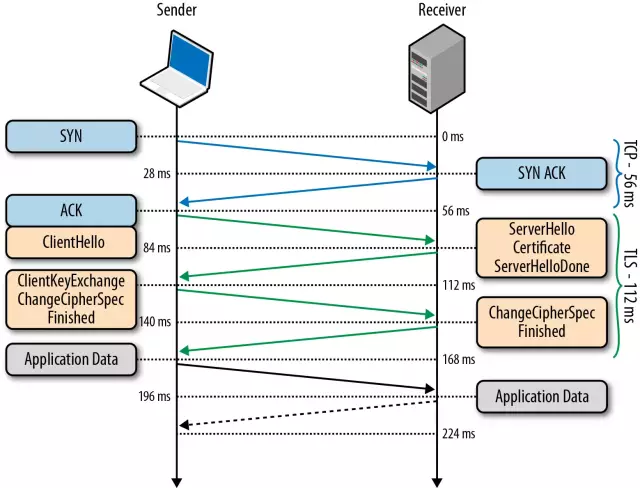
General steps:
1. The client sends a Client Hello message to start SSL communication. The message contains the SSL version, available algorithm list, key length, etc.
2. When the server supports SSL communication, it will respond with a Server Hello message. The message also includes the SSL version and encryption algorithm configuration, that is, the negotiated encryption and decryption algorithm.
3. Then the server will send a Certificate message, that is, the certificate will be sent to the client.
4. The client sends a Client Key Exchange message, uses the certificate public key in 3 to encrypt the Pre-master secret random password string, and subsequently uses this password for symmetric encryption for communication.
5. After the server successfully decrypts using the private key, it returns a response indicating that the SSL communication environment has been set up.
6. Then there is the regular http c/s communication.
As mentioned above, digest and signature algorithms will be used in steps 3 and 6 to ensure that the passed certificate and communication content are not tampered with. It can be seen from this process that the core of https lies in encryption, especially the asymmetric encryption algorithm that is used many times to transmit key information.
After understanding encryption, realizing the transparency of the network, and being skeptical of everything, it becomes simple to understand the https system.
Conclusion
Recently in the system To review things related to http, this article first introduces the basic principles of https. I have little knowledge and knowledge. There are some inappropriate things in the article. I hope you can correct them! Later, we will introduce practical applications, static server configuration, etc.~
##Appendix
httpsHow to avoid man-in-the-middle hijacking?
If someone hijacks your DNS server and resolves http://wwe.icbc.com to his illegal website, or the proxy server directs you to his illegal website, this is a man-in-the-middle attack. If there is no https, then the attack occurs. So how does https avoid such attacks?
The answer is through certificate authentication.
1. When applying for a certificate, the CA will perform control certification on the domain name to be applied for, so it is impossible for you to use Lao Wang’s website next door to apply for a certificate. Even if you hack his site, Lao Wang can find out as long as he applies for a certificate.
2. If you forge a certificate that is not issued by an authoritative CA, then the browser will alert you when checking that the certificate is illegal. Of course, users can still continue to operate, such as grabbing train tickets or something. .
3. If you download the certificate of the real site, the domain name on the certificate remains unchanged, and you just replace the public key, then the browser will find that it is not correct when comparing the digital signature of the certificate. Without saying a word, call the police.
4. If the middleman directly uses the real certificate of ICBC Home, then although he can receive the client's message, he cannot decrypt it, so he cannot respond to the client's request, and the attack is invalid!
Digital signature of the certificate
Before the hash algorithm and number I don’t know much about signatures, but after understanding it, I found that the principle is actually quite simple. The hash algorithm can convert a large amount of data into a fixed-length summary, and the summary corresponds to the input. The summary will also change when the input changes. Therefore, a hash algorithm is applied to the data to obtain a summary. By comparing the summary, you can determine whether the data has been tampered with. The certificate uses the private key to encrypt the digest, and then the client can use the public key to decrypt it to obtain the digest. By comparing the digest calculated by the hash algorithm, it can determine whether the certificate has been tampered with. On the other hand, because the public and private keys are in pairs, although the digest of the tampered certificate can be obtained, the signature cannot be encrypted, so the combination of digest and encryption can ensure the authenticity of the certificate. The private key here is the private key of the issuing authority of the certificate, that is, the CA on the CA chain encrypts the user server certificate, and the superior CA encrypts the certificate of the subordinate CA, thus forming a trust ring.

